Sponsored by Norton VPN
How do I know if I can trust my VPN provider with my privacy?
Look out for these signs of a trustworthy VPN
It might seem like a silly question to ask how to know whether your chosen VPN provider can be trusted with your privacy. After all, isn't that the whole purpose of a VPN in the first place: to be a protective barrier against all the virtual nasties of the online world? It's also right there in the name: Virtual Private Network.
Sadly, that is not enough of a guarantee and you'll definitely need to delve a little deeper when researching which is the best VPN to ensure that your data is kept under lock and key.
Here are a few key factors to look out for to ensure you're justifiably placing your trust in a VPN company.
Sign up to Norton VPN with TechRadar's exclusive offer
Our lucky readers in North America, the UK and Australia can take advantage of discounts on Norton VPN's feature-packed Plus and Ultimate plans thanks to this exclusive offer. All carry a generous 60-day money-back guarantee, meaning you can give Norton VPN a try risk-free!
– Get Norton VPN with our exclusive deal
Robust no-logging policy
Many VPN providers will claim to be 'no-logs' and have a no-logs policy outlining the information it does and doesn't keep a record of. This means that, should a provider be requested to hand over data by an authority, it'll have nothing meaningful to share about its users and their online activity.
Generally, this means a provider won't retain information like your IP address, browsing history, or connection times.
It's rare for VPNs to be truly no logs, as they genuinely require at least some data in order to run their service as safely and smoothly as possible. Norton VPN, for instance, is incredibly transparent about the data it does and doesn't collect from you and why.
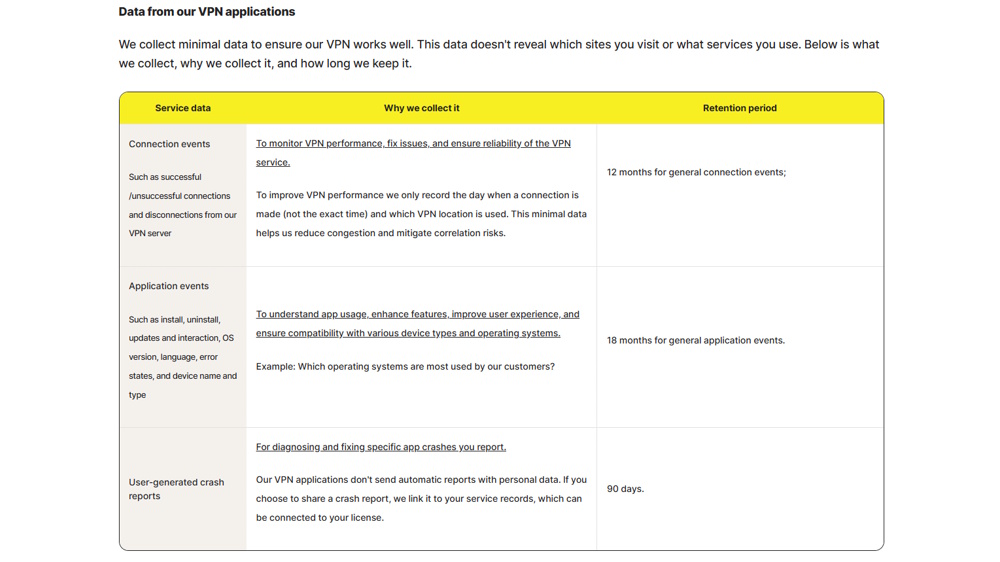
Norton VPN's no logs policy outlines that it retains information such as day of connections (not specific times), application details like installation and update times, type of device, as well as crash reports filed by users.
On the whole, that is a scant set of data taken for the purpose of allowing software to run smoothly, identifying any needed fixes, and avoiding server congestion. Norton's policy also states this data will be deleted after a specific period of time.
Regular independent audits
A no-logs policy is all well and good, but does a VPN provider actually practice what it preaches?
As well as delving headfirst into a provider's no-logs policy and ensuring you're happy with what data it does and doesn't collect, you should next ensure it backs up these claims. You can do this by checking whether or not it has had any independent audits carried out, both on its no-logs policy and other aspects of its apps and the features it provides.
Independent audits are carried out by third-party cybersecurity of auditing firms that will delve into different elements of a VPN, and give a report on its security claims and the performance of its features.
Not only is it important that these audits exist and that they back the provider's claims, but that they are carried out regularly. The landscape of online threats is constantly evolving, and a VPN needs to meet these ever-changing demands.
Reputable name in cybersecurity

Does your VPN's reputation precede it... and in a good way? When it comes to choosing a VPN, it's best not to go too far off the beaten track and subscribe to a relatively unheard-of or new-on-the-scene VPN.
Norton VPN, for example, has been in the cybersecurity game for years. In fact, Symantec and Peter Norton Computing joined forces in 1990, bringing together their antivirus and utilities software to go on to create a household name in the field of cybersecurity. While its standalone VPN didn't come until 2019, that's decades of building strong foundations in the sector, and Norton VPN is continuing to make waves with its product offering.
While they don't necessarily have the same prestigious history, other reputable VPN providers include ExpressVPN, established in 2009, and NordVPN, which launched in 2012.
Both are well-known names – and for good reason – topping many of TechRadar's 'best for' lists thanks to their robust, top-performing VPN products.
Long list of privacy tools and features
In order to fully trust your VPN provider, you'll also want its settings menus to provide a long list of available privacy and security tools:
- Kill Switch: Most good VPNs offer a kill switch as a baseline. Once set up, a kill switch will do pretty much what its name describes: cut your internet connection should the line to your server drop, reducing the risk of your data being left exposed.
- Double VPN: This feature means your traffic gets routed through not one, but two servers, adding an extra encrypted barrier between your online activity and whoever might be trying to snoop. Sometimes known as 'Multi-hop'.
- Auto Connect: You can set up your VPN so that as soon as it launches on your device, it automatically connects to a local server. This means your online identity will immediately be concealed and your data encrypted.
- Ad Blocker: Ads online aren't just annoying, they can also pose more online threats, with some ads directing you to phishing sites.
- IP Rotation: While connecting to a VPN will conceal your own IP address from the get-go, IP Rotation frequently changes your IP address while connected. This makes it that bit more difficult to be tracked and helps avoid annoyances like IP throttling, scraping and DDoS attacks.
Choice of protocols
Protocols are the way in which servers transmit your data, with some protocols prioritizing privacy over speed and vice versa. Depending on what online task you're doing, then, you may wish to switch from one protocol to another.
WireGuard is worth looking out for, thanks to its high speed and security levels. OpenVPN is an open-source, trusted protocol that has been deemed very secure for years now.
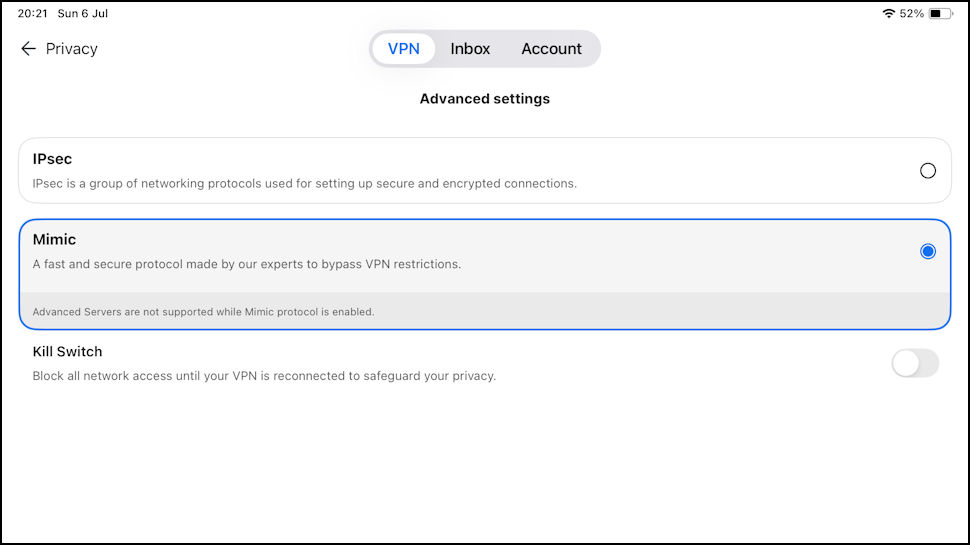
Most VPN providers will offer these protocols as standard, but some also have their own proprietary protocols. For instance, Norton VPN has its Mimic protocol, built by its own in-house experts, with a focus on stealth. Right there in the name, it's great for accessing streaming services and bypassing firewalls, disguising your connection to look like it's coming from a standard HTTPS, and so, for all intents and purposes, doesn't look like a VPN.
Proton VPN has a similar protocol called Stealth, which looks to navigate government-imposed censorship, while NordVPN's NordLynx protocol utilizes the WireGuard framework to offer its users an even faster server option.
We test and review VPN services in the context of legal recreational uses. For example: 1. Accessing a service from another country (subject to the terms and conditions of that service). 2. Protecting your online security and strengthening your online privacy when abroad. We do not support or condone the illegal or malicious use of VPN services. Consuming pirated content that is paid-for is neither endorsed nor approved by Future Publishing.

Alice formerly worked as an eCommerce Editor at Future across its portfolio of brands. Still stringing together words for a living, she writes about everything from entertainment to consumer tech to VPNs – and what they allow you to watch! She has been writing in the eCommerce space for more than five years, previously working at Trusted Reviews before joining Future.

 Become a TechRadar Insider
Become a TechRadar Insider







