5 things you need to know about Apple vs the FBI
Apple's refusal to comply with a court order to provide the FBI with a backdoor into the iPhone has opened a new chapter in the debate over security vs privacy.
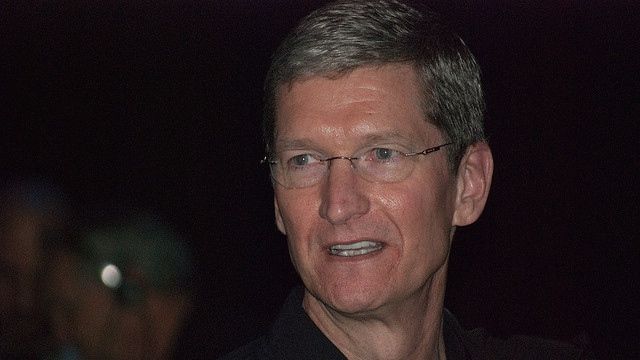
Throw in a scathing letter by Apple CEO Tim Cook, and you have the recipe for an unprecedented face-off between a tech company and the government. This is a new phase in a heated battle between Apple and the Bureau, the outcome of which will set the stage in the war over encryption for years to come.
Here are five things you need to know about Apple's fight with the FBI. For even more coverage, follow the links below:
- Critical new details emerge in Apple's encryption battle with the government
- Donald Trump calls for Apple boycott
- US Department of Justice files motion against Apple
- Here's where Facebook and Twitter stand
- Google picks a side, and it's not the FBI's
1. What the FBI wants
Essentially, the FBI wants to crack the passcode on an iPhone 5C used by one of the shooters in the 2015 San Bernardino terrorist attack. The FBI doesn't have the PIN, and after 10 failed attempts the agency fears the phone will wipe what data is on there – a standard iPhone security feature.
On Tuesday, a judge ordered Apple's "reasonable technical assistance" to do three things: bypass or disable the auto-erase function on the phone, enable the FBI to electronically input passcodes from another device hooked up to the iPhone and ensure the phone's software doesn't impose time delays between passcode attempts beyond what's incurred by Apple's hardware.
In other words, the FBI wants to unlock the iPhone by brute force by attempting many, many passcodes until it hits on the right one, without having to manually input them and without a delay after every incorrect attempt.
2. The special version of iOS
To get around the three things listed above, the FBI basically wants Apple to make a special version of iOS for the recovered iPhone.
Sign up for breaking news, reviews, opinion, top tech deals, and more.
The court order maintains the software would have an identifier for the phone coded by Apple so that it would only work on that specific device. This special version of iOS would be loaded via Device Firmware Upgrade (DFU) mode, recovery mode or "other applicable mode available to the FBI."
The FBI needs Apple to make the firmware because, before the update kicks in, the device will verify that it has a valid signature from Apple. If it doesn't have the signature, then the firmware won't take.
The court order indicates that this special operating system would be loaded onto the iPhone 5C at a government facility or at an Apple facility. If it takes place at an Apple location, the FBI would have remote access to the device so it could try passcodes on it.
3. What the FBI is asking for is possible
There has been debate about whether what the FBI is asking Apple to do is even possible, and my research indicates that it would be difficult for Apple to accomplish it on a locked phone running a more recent version of iOS.
Difficult, but not impossible. What the FBI is asking for is technically feasible due largely to the fact that the iPhone it wants to access is a 5C, according to Trail of Bits.
This device doesn't have what's called a Secure Enclave, the "single most important security feature produced by Apple," writes Trail of Bits. The Secure Enclave is a separate coprocessor within the A7 chip, found on iPhones with Touch ID. The iPhone 5C is not one of those iPhones.
When a passcode is entered on an iPhone that has a Secure Enclave, that passcode attempt is "tangled" with a key from the Secure Enclave, and not even Apple knows that key. So even if Apple created a new version of iOS to circumvent the other security features, if the device has a Secure Enclave, it would be virtually impossible to crack.
However, no Secure Enclave means that all you have to contend with is the passcode protections in the software itself, which takes us back to the FBI wanting a special version of iOS in the first place.

Michelle was previously a news editor at TechRadar, leading consumer tech news and reviews. Michelle is now a Content Strategist at Facebook. A versatile, highly effective content writer and skilled editor with a keen eye for detail, Michelle is a collaborative problem solver and covered everything from smartwatches and microprocessors to VR and self-driving cars.