Security researchers found 'critical' flaw in IPVanish Mac VPN app — here's all you need to know
IPVanish has now released an update to fix the vulnerability

- Security researchers found a critical flaw in the IPVanish Mac VPN app
- The bug can allow attackers to gain full control over a user's system
- IPVanish has now released an update to fix the vulnerability
Update: On March 6, IPVanish released an update to the IPVanish macOS Desktop software (version 4.10.3) that fixes the vulnerability with OpenVPN.
A "critical privilege escalation vulnerability" has been discovered in the IPVanish VPN application for macOS, potentially allowing malicious actors to gain full control over a user's system.
Discovered by cybersecurity researchers at SecureLayer7, the flaw exploits the VPN’s "privileged helper tool," a background component used to manage secure network connections. The researchers found that this tool only makes very limited efforts to verify who is asking to run commands. As a result, the bug "allows any unprivileged local process to execute arbitrary code as root without user interaction," experts warn.
While IPVanish is a well-known name often compared to the best VPN services, the vulnerability has been assigned a severity score of 8.8 (High) and listed as "pending."
In a statement to TechRadar, a spokesman for IPVanish said the team is aware of the vulnerability with OpenVPN in the Mac VPN app and is "working on a fix" that will be released as soon as possible.
"WireGuard is the default protocol for new installations, meaning users who have only used the standard configuration won’t be impacted," IPVanish added.
As of March 6, IPVanish released an update to the IPVanish macOS Desktop software (version 4.10.3) that fixes the vulnerability with OpenVPN.
What's IPVanish Mac vulnerability is about
The vulnerability centers on how the IPVanish app communicates with its background "helper" tool for the OpenVPN protocol (the OpenVPNPath parameter). In macOS, these helper tools act like system administrators with top-level privileges to change important settings.
According to the SecureLayer7 report, the problem is that this helper tool acts like a security guard who never checks IDs. It listens for instructions but only makes very limited efforts to verify who or what is sending them.
In practice, this leaves the door wide open. Any app or program running on your Mac can send commands to this powerful helper. Because the tool doesn't make all the necessary checks to confirm that the request is coming from a safe or trusted source, malicious software can easily use it to gain total control over the computer.
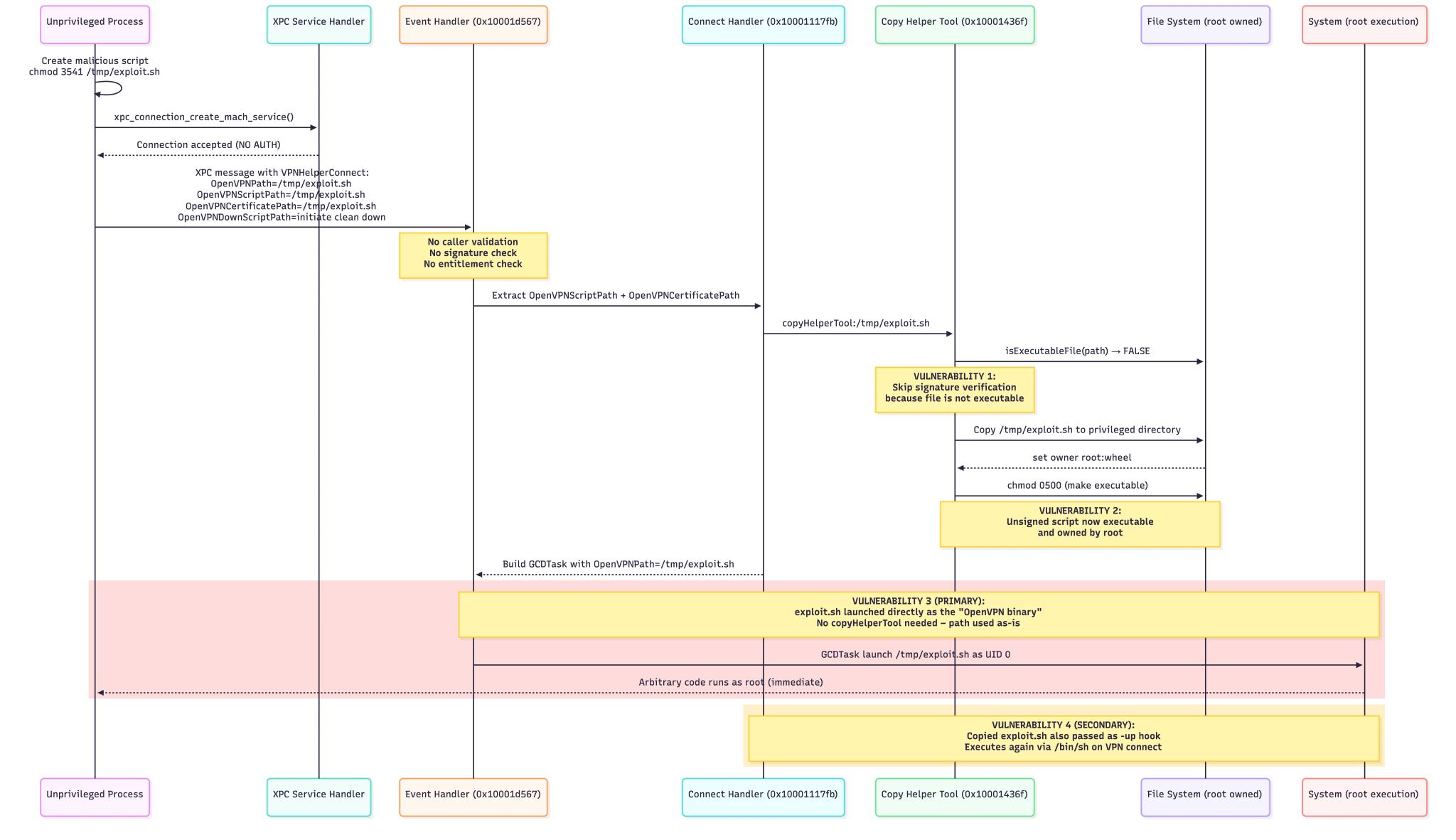
Researchers identified two main ways hackers can abuse this, both resulting "in the attacker’s script running as root," warn experts.
First, an attacker can simply trick the OpenVPNPath parameter into launching a malicious program instead of the normal VPN software.
The second method is even more concerning because it bypasses Apple's strict, built-in security guards. Normally, your Mac stops unapproved or dangerous software from running. However, the IPVanish's OpenVPNPath appears to have a major logic flaw: it only checks a file's safety signature if the file is already labeled as a running program (an "executable").
Hackers can easily get around this by disguising their malicious code inside a harmless, non-running file. The IPVanish helper sees the harmless label, assumes it's safe, and skips the security check. Then, in a major blunder, the helper tool moves the file to a secure area and actually changes the file's settings itself, turning it into a running program and doing the hacker's job for them.
Staying safe
It is important to emphasize that this is a Local Privilege Escalation (LPE) vulnerability. This means a hacker cannot exploit this bug remotely over the internet just by knowing your IP address. The attack "requires only local access to the system where IPVanish VPN is installed," meaning a hacker must already have a foothold on your machine via malware or physical access.
SecureLayer7 states that fixing this will require significant changes to the app's architecture. "The most critical immediate mitigation is implementing caller authentication in the XPC event handler," the firm advises.
On their side, IPVanish ensures that only macOS users connecting to the OpenVPN protocol have been impacted by this vulnerability.
IPVanish has now sent notifications to all Mac users urging them to update to the latest version. Alternatively, customers can also download the latest version on the official websites here.
The team assures TechRadar that the vulnerability "did not involve any intrusion into the IPVanish VPN server network and did not affect the encryption or integrity of the VPN connection."
Follow TechRadar on Google News and add us as a preferred source to get our expert news, reviews, and opinion in your feeds. Make sure to click the Follow button!
Sign up for breaking news, reviews, opinion, top tech deals, and more.

Rene Millman is a seasoned technology journalist whose work has appeared in The Guardian, the Financial Times, Computer Weekly, and IT Pro. With over two decades of experience as a reporter and editor, he specializes in making complex topics like cybersecurity, VPNs, and enterprise software accessible and engaging.
You must confirm your public display name before commenting
Please logout and then login again, you will then be prompted to enter your display name.

 Become a TechRadar Insider
Become a TechRadar Insider






