What you need to know about Friday's massive web outage
Twitter, Netflix, Spotify and more downed by cyber attack
Update 3:47pm PT: It appears the waves of DDoS attacks against Dyn are over and websites should be back to full operation as a result - fingers crossed.
"This incident has been resolved," the firm's status page read as of 22:17 UTC. This comes after a day full of strikes that rendered some of the internet's top sites inaccessible.
We'll continue to monitor for any updates, but you can learn more about Friday's web outage below.
Trouble getting onto your favorite website on Friday? You weren't alone as a massive distributed denial of service (DDoS) attack struck down some of the web's biggest sites, including Twitter, Spotify, Netflix and Reddit.
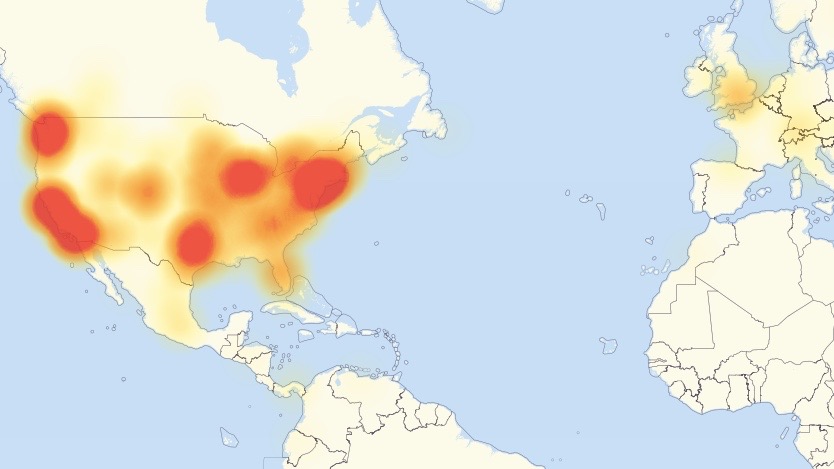
The first wave began at 11:10 UTC, though more continued throughout the day. The outage first most affected users on the US East Coast, however it soon became apparent that folks across the country as well as abroad were being met with blank web pages.
While most sites appear back to normal now, domain name system (DNS) provider Dyn, the target of the attack, reported attacks and mitigation efforts into late Friday afternoon Pacific time.
Dyn is calling the attacks "very smart", as reported by TechCrunch , saying that as the company responds, the attackers react, pointing to a sophisticated and complicated assault.
Sign up for breaking news, reviews, opinion, top tech deals, and more.
Here are key details to know about the attack:
What is a DDoS attack?
A distributed denial of service attack, or DDoS attack, is a form of cyber-sabotage where the perpetrator overloads a machine or system with requests, slowing it down or completely rendering it unable to work.
DDoS strikes have been on the rise, almost doubling in frequency in the past year, with targets ranging from internet routers to Xbox Live.
What makes a DDoS attack on a DNS provider particularly potent is that it only needs to overload one system to affect many sites, versus having to attack those sites one-by-one. As we saw today, this can lead to widespread disruptions across the web.
Which sites were affected?
As first reported by Hacker News, impacted sites included Twitter, Etsy, Github, SoundCloud, Spotify, Heroku, PagerDuty, Shopify and the Intercom app.
Other sites experienced outages as well, including Netflix, Reddit, The New York Times, PayPal and Pinterest.
Basically, some of the most popular and largest sites on the internet were taken offline, disrupting access for countless users.
Were IoT devices really behind the attack?
Though no person or persons have been fingered for the attack, security firm Flashpoint has confirmed that some of the infrastructure responsible is Internet of Things devices infected with the Mirai botnet.
Mirai infiltrates devices such as routers, DVRs, webcams and security cameras, and a bad actor can turn these devices on a target to send traffic requests its way. In today's case, Flashpoint confirmed that at least some of the devices used to flood Dyn with requests were DVRs.

If that concerns you about connected home devices, know that Mirai has been used in attacks before against a blog called Krebs On Security and OVH, an internet service provider.
What's more, Mirai's source code is available online, meaning anyone can create their own botnets to launch a DDoS attack.
Today's attack serves as a reminder that web security can be tenuous, especially as more of our devices connect to the internet and one another.
Law involved
White House Press Secretary Josh Earnest said that the situation caught the attention of the US Department of Homeland Security, and it is closely monitoring the situation, according to USA Today.
However, according to Reuters, US officials have begun investigating the attack to gauge whether it is was a criminal act.
BREAKING: U.S. government probing whether east coast internet attack was a 'criminal act' - officialOctober 21, 2016
Flashpoint says it is monitoring the situation and working with vendors and law enforcement to track down infected devices that form the botnet.
We'll stay on top of any further developments, but for now, the crisis seems to be over. Resume your internet wanderings as you would.

Michelle was previously a news editor at TechRadar, leading consumer tech news and reviews. Michelle is now a Content Strategist at Facebook. A versatile, highly effective content writer and skilled editor with a keen eye for detail, Michelle is a collaborative problem solver and covered everything from smartwatches and microprocessors to VR and self-driving cars.

 Become a TechRadar Insider
Become a TechRadar Insider







