If you haven't already, go to www.truecrypt.org, grab the Windows install package. You'll notice that the TrueCrypt interface is surprisingly simple. You can ignore the main area, which is a list of drives. This reflects an older aim of TrueCrypt: to provide a virtual mounted drive that's just a single encrypted file on the existing file system. It's clever, as you can read and write to it and the encryption is handled on the fly.
You can still use this system, and it's a great way to carry protected data around with you on a USB drive. In fact, when you install TrueCrypt there's a portable option for exactly this. Beyond this, TrueCrypt offers encryption of the system partition with boot-time protection, standard removable and fixed-drive encryption, and the ability to encrypt the boot drive with a hidden system drive.
For the super-paranoid, this last option creates two bootable systems with different passwords. If you're ever forced to provide the password, you can give the fake one. This triggers the system to boot into the 'fake' OS, and with the encryption, the real OS looks no different to random bits. For plausible deniability you're suppose to use the 'fake' OS on a day-to-day basis, saving the hidden OS for duties you want secure.
Article continues below 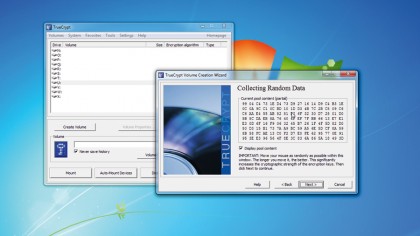
No matter what option you wish to use, click the 'Create volume' button and choose from file-base, non-system and system partition encryption. The system partition encryption is the most involved of these, but even this is straightforward. You'll be asked if you want a normal or hidden drive as detailed above. Most people, we suspect, will opt for normal.
An option to encrypt the host protected area is next. If you built the system yourself, then you're safe to choose 'Yes', but for vendor systems we'd select 'No'. It depends on whether the PC has a hidden rescue partition, so if you're unsure, don't do it. TrueCrypt supports multi-boot systems, though if you're running one you can probably figure out this yourself.
Before creating your password, you can choose your encryption and hash methods. The default AES and RIPEMD-160 hash are perfectly adequate and securely tested solutions. Finally, TrueCrypt will ask you to choose your very own password.
This is very important stage in the process. As we've said before, a long, non-trivial password is best, and TrueCrypt suggest a minimum of 20 characters. We'd point to the XKCD guidelines of using multiple words that paint a memorable pictogram, but it never hurts to top that off with a number and few bits of random punctuation. You need to remember this password, because there's no way to recover your data if you happen to forget it.
Sign up for breaking news, reviews, opinion, top tech deals, and more.
Next, TrueCrypt is going to create hashes and slats based on random data; it's already started to take 'random' data points. Computers are notoriously bad at generating truly random numbers, so it's been monitoring your key strokes, taken timing information and other elements. Next it'll ask you to move the mouse randomly too.
With this done and the encryption keys created, it's essential that you make the rescue disc. In fact, TrueCrypt will not let you proceed without one.
The last stages including an option to wipe unused data. If you're using an SSD we don't advise this, because it's better to use the PartMagic and the three passes are really overkill.
Finally, TrueCrupt will test to see if the system can in fact boot, and enable you to test the password. If all of that succeeds then it'll start the encryption, which takes place on the fly so you can carry on working.

 Become a TechRadar Insider
Become a TechRadar Insider






