Stopping the internet: how the world is trying to censor the web
And why it will never work
Sign up for breaking news, reviews, opinion, top tech deals, and more.
You are now subscribed
Your newsletter sign-up was successful
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
On March 21, Turkey's under-siege government (theoretically) cut off all access to Twitter, the social network attributed with dozens of embarrassing leaks about the ruling powers.
Before understanding why internet censorship, a staple of any totalitarian government, is failing Turkey so badly, it's key to understand the mechanisms underlying the internet, and how a government can (theoretically) go about blocking it.
In broad terms, a country's internet works like the postal system. Letters go from an individual to a local post office; from there, a letter travels up to a sorting office, from where it's routed to a sorting centre close to the letter's destination; in the case of overseas mail, it will even travel by boat or plane to get to that sorting station.
Article continues belowThe internet works in the same sort of way: your friendly postie is replaced by a copper or fibre-optic line that runs to the digital equivalent of your post office – in this case, a telephone exchange. The sorting offices are really data centres, and the boats and trains become high-speed underseas fibre-optic cables.
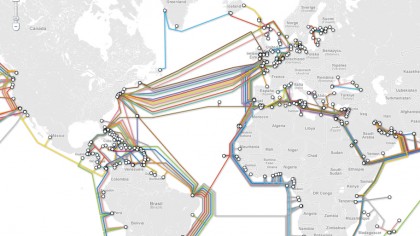
What that means for a government wanting to block websites is that all your traffic has to flow through a few choke points, owned and operated by a handful of Internet Service Providers (ISPs), like BT, Virgin or Sky. Turning off the internet wholesale is relatively simple – data centres within the borders of the country will be turned off, and the underseas cables cut, to prevent any communication with the outside world.
Pick 'n Mix censorship
Selective censoring – blocking some sites but not others – is a little more difficult. The crudest method of selective censoring, and the one initially employed by Turkey's government, is to cut the address of the website you want to block out of the Domain Name System (DNS).
The DNS is a system that matches the URL of a website (e.g. www.techradar.co.uk) with the IP address of that website (89.167.142.126, in this case). To re-use our postal system analogy, that would be like deleting someone's postal code from the register – without a postcode, the letter gets lost in the sorting centre.

However, getting around DNS blocking is pretty simple – you can either enter the raw IP address of the website you want to access into your internet browser, or fiddle with the settings of your internet browser to use a different DNS system, one that the government hasn't fiddled with.
There is a more sophisticated means of blocking the internet, of course. Blocking the actual IP addresses is easy enough for ISPs to do, and that's analogous to sifting through all of a country's mail, and removing any letters addressed to Twitter – you can't get around it with a simple DNS hack.
That said, this is still the internet, and getting around any block is still child's play.
Sticking It To The Man
The most common means to dodge ISP-level blocking is by the use of a Virtual Private Network (VPN). This can best be thought of as an encrypted tunnel that connects to a server in another country, and routes all your traffic through that server. Imagine it, for all intents and purposes, as being like a middle-man in the mail service: your parcels and letters are directed to your 'middle man' (in this case, the VPN server), and he then packages them in a giant, padlocked steel container, and ships them over to you.
This means that the ISPs have no way of seeing what's inside the giant steel box (alright, VPN), and as such, there's no way of monitoring or censoring the traffic. Because VPNs use the same Transmission Control Protocol as the rest of the internet, there's no simple way of distinguishing VPN traffic from regular 'ole web traffic, so it's not possible to just outright block VPNs, either. Moreover, VPNs are cheap (sometimes, free) and easy to set up.

As you'd expect, then, everyone and their dog seems to be using VPNs to get around internet censorship. In the specific example of Turkey, downloads of popular VPN service Hotspot Shield jumped by 3,000 per cent in the 24 hours following the implementation of the ban. Growth hasn't slowed down, either: four days after the Twitter ban, Hotspot Shield told TechRadar that it had seen 1.1 million downloads from across Turkey, as opposed to the normal average of around 10,000 per day.
The surge in users isn't just limited to Hotspot Shield, though. At the time of writing, VPN apps were in three of the top five iOS apps, and Hotspot Shield has been the number-one overall app ever since Twitter was blocked.
And, according to Twitter-monitoring website Brandwatch, Twitter usage was up by 138 per cent following the supposed wholesale blocking of the site in Turkey. Not exactly the resounding success the Prime Minister was presumably hoping for when he banned the social media site.
What's Next?
The outlook for any government looking to ban the internet is pretty bleak. Even China, which has one of the more sophisticated firewalls, hasn't managed to keep VPNs out of the country – and boy, have they tried. A few years ago, China went after the VPN providers themselves.
According to Hotspot Shield, all its download servers at the time were banned, so that no-one could get their hands on the VPN software if they didn't already have a copy on their computer. However, according to David Gorodyansky, the CEO of Hotspot Shield's parent company, "we just set up an email service, so anyone could send an email to an address, and automatically get a working download link in reply…we actually saw our install increase by four times immediately following the ban".

What blocking turns into, then, is a game of cat-and-mouse. Given the way that the internet's laid out, and the relative size of the companies involved, small VPN firms will always find it easier to change stuff compared to large companies and firms. It's a game that you can expect those who are pro-internet-freedom to be winning for the next little while.
A good example is a small Israeli firm, Hola, which has become increasingly popular thanks to offering a free, VPN-esque service that requires even less set-up that options like Hotspot Shield. They too have seen a "major surge" in traffic in Turkey; they're also ready for more sophisticated blocking, and, according to CEO Ofer Vilenski, "are ready to put Hola to the challenge".
Sign up for breaking news, reviews, opinion, top tech deals, and more.
 Become a TechRadar Insider
Become a TechRadar Insider






