Windows 7 is a big operating system with an efficient architecture, but its inner world of processes and services can be a confusing place if you're not used to it.
If you don't know what you're looking at, it's easy for malware to masquerade as a legitimate process and for legitimate processes to frighten you so much that you kill them, crash the system and lose data.
Then there's the problem of your anti-malware protection or Windows popping up warnings about processes needing your permission to access resources. Will accepting the request infect your machine, or worse?
Article continues belowHierarchy of processes
To work out whether a process is benign or malicious, it's useful to understand something about the structure of a running installation of Windows 7.
After you power up the PC and it passes its self-tests, the BIOS loads the master boot record from the primary hard disk partition and runs it. This in turn loads and runs the Windows 7 kernel image, which then begins unpacking the other processes it needs help it create all the processes that constitute the OS.
All modern operating systems have a hierarchy of processes. In Windows 7, there are usually three or four top-level processes. One such process is called 'wininit', the direct descendent (the process it personally starts running) of which is called 'services.exe'.
Sign up for breaking news, reviews, opinion, top tech deals, and more.
As you might expect, it's the job of this process to spawn child processes that run as independent services in the background. However, there's often a degree of confusion that creeps into the user's mind over this seemingly simple task.
The confusion is that 'services. exe' starts multiple instances of a process called 'svchost.exe'. Search for the term and you'll find many forum posts from worried users asking if their PC has been taken over by malware and asking how to kill all those multiple processes.
However, it's normal to have many instances running in parallel, and killing them can harm the running OS. If this happens, you'll need to reboot and may lose data or even corrupt your hard disk.
The reason there are so many instances of 'svchost.exe' is that it acts as a launcher for processes that run from DLLs rather than EXE files. These are apportioned between many instances of 'svchost.exe' for efficiency, speed and system resilience.
'Services.exe' also starts many other service processes that run directly from EXE files. These include the service portion of your anti-malware products, updaters for third-party products and Windows 7, and services for power management and the Windows Live Sign-in Assistant Manager.
Another process that causes confusion and fear in the minds of users is the innocent 'Search Indexer.exe'. When the hard disk light stays lit for prolonged periods of time, it's normal to worry about what's going on, but it's usually down to this benign and useful part of Windows 7.
It simply indexes all your files for use in Windows Search. Its index is used when you type in the name of a file in the Start Menu search box and when you search for files in Explorer. It's even used by Windows 7's Libraries feature.
Another vital top-level process is 'explorer.exe'. This process runs the Windows 7 desktop and is the mother process for all your running applications, including those that sit in the system tray of the task bar, ready for use.
Improving the view
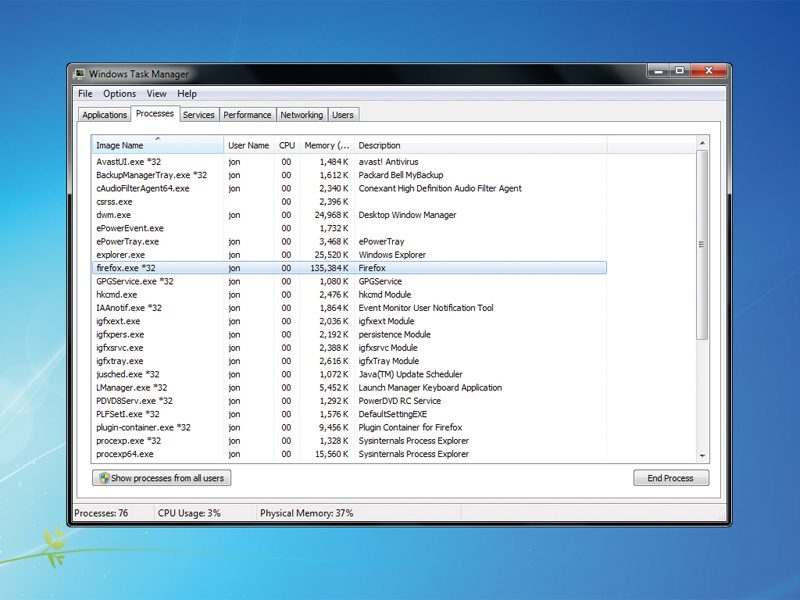
Traditionally, processes, services and applications are viewed using Task Manager. In Windows 7, it's started by pressing [Ctrl]+[Alt]+ [Del], then selecting it from the menu.
Task Manager sorts full applications, underlying system processes and services into three tabs, but it doesn't show you everything. Where are all those 'svchost.exe' processes? Task Manager hides a lot from you, and when you're investigating system activity, this limited view of what's going on is to be avoided.
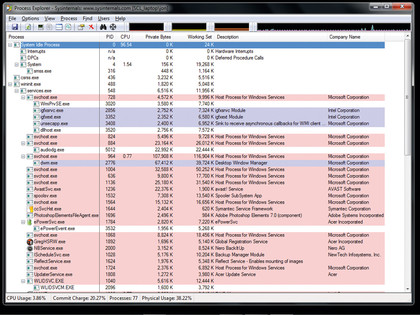
Instead, a better option is to download and run our old friend Process Explorer, available from Windows Sysinternals author Mark Russinovich. Process Explorer needs no installation. Simply unzip the archive and drag the files into a convenient directory.

 Become a TechRadar Insider
Become a TechRadar Insider






