Beginner's guide to internet security
Protect yourself from viruses, phishing emails and other scams

You wouldn't dream of leaving a brand new car unlocked and unattended in the same street as Thieving Keith the Car Thief, yet when it comes to computers, many of us do something very similar.
Unprotected computers are easy prey for viruses, malware and other online infections, and despite the very real dangers of identity theft, we'll accidentally - or in some cases, happily - share our most valuable personal information with the entire world wide web.
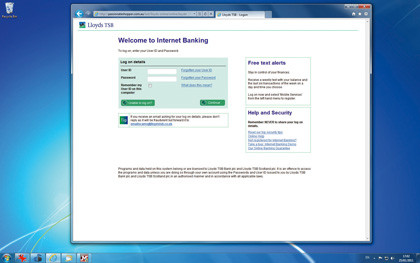
When fraudsters aren't trying to steal our identities, they're after our online banking details. Some of them are alarmingly convincing. Even the savviest computer owner has looked at an official-looking email and wondered whether it really is from the bank, or from eBay or Facebook, and legitimate-looking online shops can quickly part people from their hard-earned cash in exchange for products that never turn up.
Article continues belowThe good news is that you can fight back. In the battle against net nasties, your PC can be your most powerful ally - and the utilities that you need don't have to cost you a thing. With a few cool tools, some useful information and some simple changes to the things that you post online, you can soon be much more secure.
Viruses, spyware and rootkits
Malware - malicious software - has been around since the earliest days of the PC, and as computers have become smarter, it has too. While different kinds of malware do different things, they all have two things in common: they try to sneak on to your PC without being spotted, and they can be stopped with up-to-date security tools.
The most famous kind of malware is the virus, which works in much the same way real-life viruses do - if your PC is infected, it can infect other PCs it communicates with.
Sign up for breaking news, reviews, opinion, top tech deals, and more.
Viruses typically spread by email, but they can also turn up in infected files such as documents or downloads - and viruses called worms don't need to infect files at all, as they can spread by taking advantage of security flaws on computers.
Viruses and worms usually have a payload, and that's the scary bit. One of the nastiest kinds of payload is the rootkit, which gives someone else remote access to your computer. That access can be used to flood your computer with more malware, or it can be used to steal computing resources, for example by using your computer to relay spam emails or attack a specific website.
Another kind of payload is spyware, which sits on your PC and watches what you do, sending data to its operator. That could be something specific such as credit card information, or it could be everything you type or a list of websites you visit.
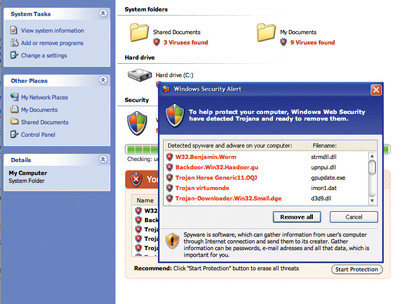
Malware can really ruin your day. It can redirect your web browser, taking you to a site of its choosing no matter what web address you type; it can plaster your screen with adverts; and it can slow your internet connection or your entire PC down to a crawl.
Spyware rarely travels alone - if a computer has one piece of spyware on it, it usually has tens or even hundreds of similar infections.
So how does it get there? It can be dropped on to your computer by a virus or a worm, or by a web page that takes advantage of unpatched web browsers - that is, browsers that haven't been updated for a long time, so don't benefit from the latest security updates.
It can be installed alongside a legitimate application - spyware is quite common in the world of free music programs, especially peer-to-peer downloading applications - or it can be tucked into a pirated version of well-known software.
The good news is that prevention couldn't be easier or cheaper.
No entry
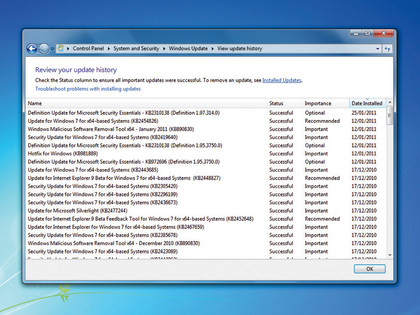
You can fight malware in a number of ways. The first thing you need to do is ensure you have the most recent Windows Updates, and that you have the most recent version of Internet Explorer (or the most recent Firefox, or Opera, or…) as lots of malware takes advantage of security holes that were closed a long time ago.
Step two is to install good security software. That needn't cost money - when we tested Microsoft's free Security Essentials, we found it as good as pricey packages - but whatever you go for, make sure it stays up-to-date. New malware is made every day, and security software that isn't up-to-date becomes useless.
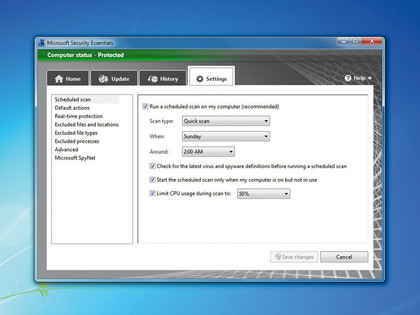
Should you splash out on a security suite? That really depends on personal preference. Many such suites offer all kinds of protection, including automated scanning, beefed-up parental controls and protection from every conceivable kind of problem, and they often offer extras such as PC tune-up utilities. In many cases, though, you can get similar protection by installing a few carefully chosen freebies.
Don't overlook the features in Windows itself: Windows Defender can help keep spyware and other nasties from infecting your system in the first place; the Malicious Software Removal Tool runs a monthly check for known worms; and Internet Explorer warns you of suspected malware and potentially dangerous websites. Download a free copy of Microsoft Security Essentials and you've got a pretty impressive collection of security software.
Don't be lulled into a false sense of security, though - you still need to practice safe surfing. Unsolicited email attachments should be approached with caution, and you should never download a file you aren't completely sure about.
Staying away from the darker corners of the internet where pirated software lives is a very good idea, too, and not just from a moral point of view - you're much more likely to encounter malware on a dodgy download site than you are on more wholesome websites.

Contributor
Writer, broadcaster, musician and kitchen gadget obsessive Carrie Marshall has been writing about tech since 1998, contributing sage advice and odd opinions to all kinds of magazines and websites as well as writing more than twenty books. Her latest, a love letter to music titled Small Town Joy, is on sale now. She is the singer in spectacularly obscure Glaswegian rock band Unquiet Mind.

 Become a TechRadar Insider
Become a TechRadar Insider






