Microsoft fixes 'critical' Windows flaws
New patches fix vulnerabilities in Vista and older versions
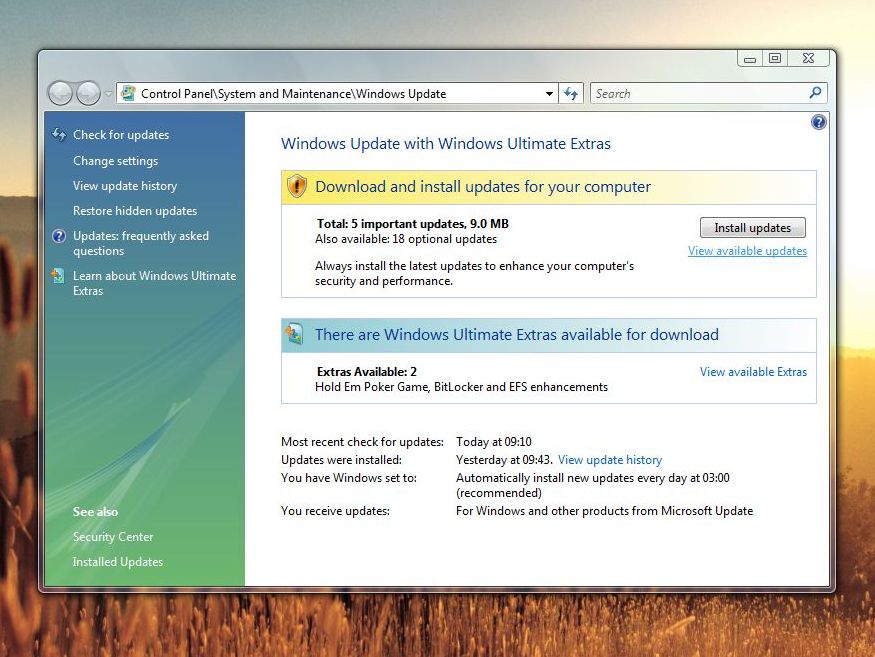
Windows has been patched again after Microsoft released three new critical updates, plus two others of lesser importance. Such fixes are classified as critical when the problem might allow a hacker to gain control of a user's PC without the user actually doing anything themselves.
This is usually through the release of a worm or "remote code execution" that can self-replicate, without the need to rely on user action.
Windows Vista is among the Windows versions affected, along with XP, 2000 and Server 2003.
Of the two non-critical patches, one was for Microsoft's Content Management Server operating system; the other for Windows. Both are classified at the lower threat level of 'important'. If you have Automatic Updates turned on, you'll get the updates dripped down to you. They can also be manually downloaded .
These latest patches follow Microsoft's monthly 'Patch Tuesday' update cycle. But last week, the corporation had to issue an extra update after the exposure of a critical flaw affecting animated cursors . Microsoft has released a further version of this patch in this latest round of updates as some users found last week's patch conflicted with apps on their system.
The reason for the extra update was that the cursor vulnerability was rapidly being exploited, so Microsoft decided to act . The weakness occurred in the way Windows handles .ani files, a format that manages animated cursors and icons. When the file opens, a memory flaw can occur. The flaw can be exploited by luring a user to a malicious website, opening a manipulated email message or a virus-infested attachment. A successful attack gives the hacker full control of the computer.
"Over this weekend attacks against this vulnerability have increased somewhat," programme manager Christopher Budd wrote on Microsoft's Security Response Center blog last week. Microsoft originally posted a warning about the security threat on 31 March.
Sign up for breaking news, reviews, opinion, top tech deals, and more.
Dan (Twitter, Google+) is TechRadar's Former Deputy Editor and is now in charge at our sister site T3.com. Covering all things computing, internet and mobile he's a seasoned regular at major tech shows such as CES, IFA and Mobile World Congress. Dan has also been a tech expert for many outlets including BBC Radio 4, 5Live and the World Service, The Sun and ITV News.

 Become a TechRadar Insider
Become a TechRadar Insider







