Websites under attack: Monster.com
Database violated, CVs from users nicked
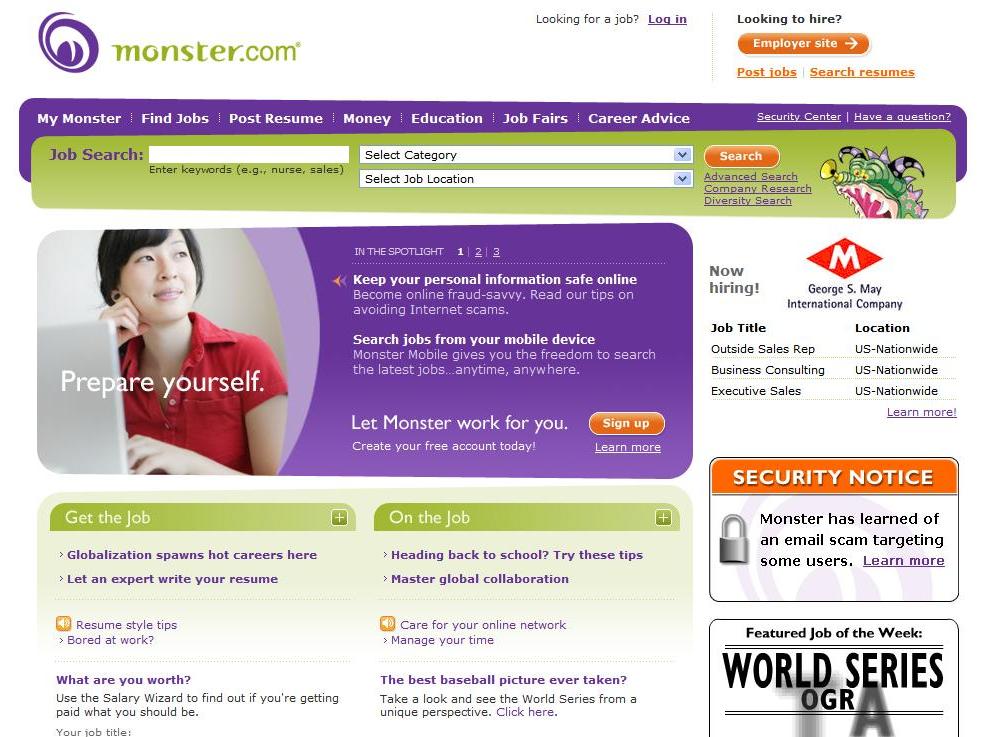
Monster.com, a popular careers website, has announced that it's under attack. The company explained that this "is not the first time Monster's database has been the target of criminal activity", and it does not yet know how many users have been affected.
After conducting an investigation into suspicious activity, Monster.com discovered that someone compromised accounts in an attempt to access CVs and résumés. Contact information was then harvested and stored on a remote server. Luckily, the server has since been located and shut down.
Data theft
On the face of it, this scraping of information is innocuous given that people don't normally put financial information on such documents.
But armed with the knowledge that a user is a Monster.com customer, hackers could easily send targeted phishing e-mails that appear to come from Monster.com. If the recipient were to follow the directions in the e-mail, important identifying information could easily be stolen.
In a public note to users, Monsters CEO Sal Iannuzzi explained that: "illegally downloaded contact information may be used to lure job seekers into opening a 'phishing' e-mail that attempts to acquire financial information or lure job seekers into fraudulent financial transactions."
According to the Associated Press, access to the résumés was gained by hacking into corporate recruiter accounts. From there, the hackers used an automated tool to copy the information to a remote database.
Monster.com is currently employing an anti-phishing initiative that aims to educate its users about the threat of phishing techniques.
Sign up for breaking news, reviews, opinion, top tech deals, and more.

 Become a TechRadar Insider
Become a TechRadar Insider







