The basics of home networking
A guide to the fundamentals of home networking

The basics of home networking
In this article we're going to look at how your home networking technologies actually function. We'll look at the basic technologies that drive it and how they work together. It may be a little dry – but we guarantee that just a little understanding of the fundamentals will help you a lot when it comes to setting up your own home network.

Ethernet
Although it's now almost synonymous with wired local area networking (LAN), that wasn't always the case for Ethernet. There were once a variety of LAN technologies available, but Ethernet has become absolutely dominant thanks largely to its flexibility. It's very easy to add and remove devices from the network: you pretty much just plug them in and the Ethernet standard itself takes care of the rest.
It works over a variety of different media – coaxial, copper, optical fibre – but most home users will only ever use copper, in the form of "twisted pairs," which are copper wires intertwined with each other.
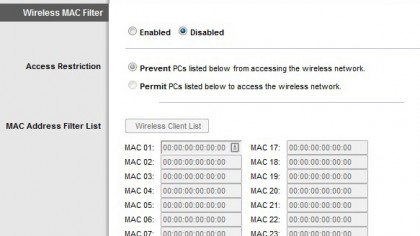
Each Ethernet device has a unique identifier, known as its MAC (media access control) address. It's a string of six groups of two characters, like something like 01:23:45:67:89:ab. You'll often see the MAC address of a network device on a sticker attached to it.
The funny thing about MAC addresses is that they don't tell data how to get from point A to point B. It's like writing a letter with a name but no delivery address. But that's where Ethernet switches come in.
Back in the olden days, we used passive hubs, which simply broadcasted every bit of data on the network to every device, which is how they guaranteed that data got to its destination. As you can imagine, that's pretty inefficient, which is why we now use switches.
A switch remembers which MAC address is attached to which physical port, so it only sends the data to the device that it's intended for. And if it gets a chunk of data that's supposed to go to a MAC address that it has no record for? Then it just broadcasts it on every port and waits for the reply, at which point it will make a note and send future packets of data directly to the device.
One of the clever things about Ethernet is that a switch can associate more than one MAC address with a given physical port. That's why you can daisy chain switches. It's OK to plug a switch into another switch.
All the devices attached to each should be able to communicate with each other seamlessly – although there is a caveat in that the link between the two switches may end up having a lot of traffic carried over it, which may reduce performance.

Ethernet: Cables
Ethernet twisted pair cables come in a variety of flavours. Different categories of cable were designed for different speeds. Cat 5 and 5e cables were designed for 100mbit (but 5e will work for gigabit); Cat 6 for gigabit and Cat 6a for 10-gigabit.
There are also shielded/foiled twisted pair (S/FTP) and unshielded (UTP) cables. The former are used in instances where there might be interference – if you're running cables near electrical lines or in bundles, use S/FTP.
Finally, there are crossover cables. It's possible to connect Ethernet devices directly to each other, without a switch in between, but if you do that the upstream and downstream cables in the pair will be backwards. That's where you need a crossover cable, which reverses them and lets you connect devices directly.
Wireless
The thing to understand about Wi-Fi is that it's really just a version of Ethernet that uses the airwaves as the physical medium. It deals with the same issues: how to share the medium between multiple devices and how to specify the target (it also uses MAC addresses).
Of course, Wi-Fi has a few things layered on top. First of all, the airwaves are a much messier medium than physical cables, so it has to deal a lot more with error correction, contention (multiple users competing for airtime) and noise reduction.
It also has to deal with security issues -- when something transmits over Wi-Fi it's really just throwing data out into the ether, hoping that it gets to its destination. Anybody nearby could also grab that data, which is why Wi-Fi data needs to be encrypted and password protected using Wi-Fi Protected Access (WPA) so that only authorised devices can understand the data.
Wi-Fi devices can talk directly to each other, but more commonly use a hub called a Wi-Fi access point, that operates very much like a switch, relaying data between devices.

Routers
MAC addresses work pretty well for local networks, but they're no good for the internet. Switches can't remember the MAC address of every single device on the internet. That's why the Internet Protocol (IP) was invented.
Where a MAC address is like an envelope with a name but no delivery address, an IP address includes information on how to get to the destination. It may look like just a series of four 8-bit numbers (like 123.123.123.123), but the way it breaks down is actually a template for understanding the hierarchy of networks of the internet. You could look at it like a physical address: the first number is the country, the second the postcode, the third the street name and the fourth the street number.
Of course, it doesn't actually break down geographically, but by network. The first number might be your ISP, the second is the city, the third the exchange, the fourth your number on that exchange. (Obviously that's a big simplification of how the address breaks down, but we'll spare you a dissertation on IP address classes and subnet masks).
While the IP address contains the information on where the target is, you still need devices that figure out how to cross the collection of connected networks that is the internet. That's what a router does – it's the postman of the internet. As the name says, it figures out a route to get the data from point a to point b.

TCP
You may also be wondering about the "TCP" that always seems to be attached to "IP". TCP stands for Transmission Control Protocol, and it's a system for managing sessions and ensuring that data reaches its destination intact.
Connecting to another computer is like making a phone call, and TCP manages the pick-up and hang-up, and checks to see whether anything was lost on the way (which is called "packet loss") and, if so, asks for it to be sent again.
There's a counterpart to TCP called User Datagram Protocol (UDP) which is also known as "send-and-pray" networking – instead of a managed connection with retransmission like TCP, UDP just sends data across the internet and hopes it gets there. It's most commonly used in instances like streaming media or voice where, even if something is lost, it's not worth going back and waiting for it to be resent.
Sign up for breaking news, reviews, opinion, top tech deals, and more.
You are now subscribed
Your newsletter sign-up was successful