Free tools to protect your PC from attack
If someone can gain physical access to your computer, they can install a keylogger to capture passwords and usernames. This may be a worry if you share a house with strangers, and students are particularly at risk.
Luckily, discovering if someone has sneaked into your machine is easy using a keylogger detector. One such program is the award-winning Online Armor by Tall Emu Software, which is available in both a free and a commercial version. The latter also contains antivirus protection, but you should already have such a package installed, updated and actively protecting you, so the free version will do.
Installation is as simple as repeatedly clicking 'Next'. However, when you come to the step of registering your email address, you can simply untick the associated tickbox and move on. Once installation is complete, run Online Armor and select the option to run the wizard, then click 'Next'.
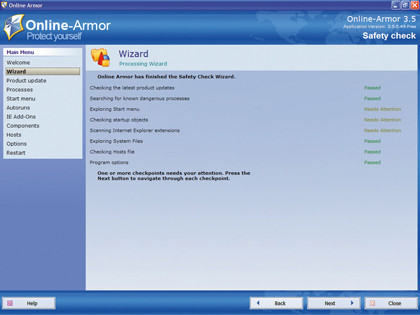
This begins a scan that includes running processes, Start menu items, start-up objects and various important files. Once complete, OnlineArmor may tell you that some scanning categories need attention. Click 'Next' to see the programs on your PC that OnlineArmor doesn't recognise.
These are usually just applications that Online Armor doesn't have in its database, but check to see if there are any you didn't install. Highlight them and click the 'Block' button to ensure that they never run. It may be that they're simply bloatware installed by the manufacturer when the computer was commissioned. You can free up some space by uninstalling them later.
Clicking 'Next' shows a list of programs that start when you boot up your computer (called Autoruns). Hover your mouse pointer over each one to get more details. If there are any that you don't recognise, then run Process Explorer and double-click on the running process. The Image tab enables you to verify them and see details of their publisher.
Use Process Explorer's 'Search Online...' facility to get extra details about these processes. After all, it's not unheard of for keyloggers and rootkits to take the names of legitimate programs. If you see something you don't like the look of and there's no publisher information, go to www.processlibrary.com and enter its name. This should give you chapter and verse on what each process is.
Sign up for breaking news, reviews, opinion, top tech deals, and more.
If you believe there's anything dodgy about something you find, block it while you find more information. When you're done, click 'Next'. OnlineArmor will then display the list of IE extensions that it's found but doesn't recognise. You can use ProcessLibrary.com to check out their legitimacy.
When you're done, click 'Next'. The next page enables you to determine how OnlineArmor checks for updates and whether it's launched automatically at startup. Finally, click 'Next' again and decide whether you want to reboot the machine now to put the decisions you made in place.
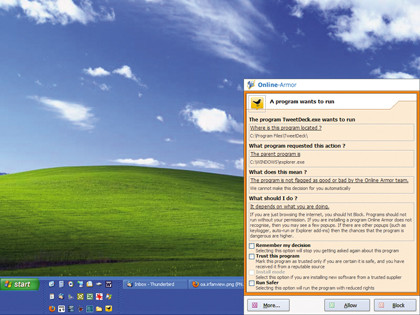
When you next reboot, Online Armor will enter Learn mode for around two minutes while it learns what services and start-up programs should be running. Once complete, when anything tries to run on the computer, Online Armor will intercept it and ask if you want it to do so.
If someone has installed a keylogger or other piece of malware, Online Armor will pick it up, even if your antivirus software misses it.
Secure your website
If you run your own web server, watch out for malicious hackers. These people deface web pages, supposedly to let the owner know that they're insecure.
Some hackers replace carefully written web pages or blog entries with a single, stark page telling the whole world that the site has been hacked. Sometimes they even include a message letting you know that they've changed your admin password to 'secure' the site.

How did this happen? It was probably your password that let the hacker in. Despite the public's perception of hackers as malicious geniuses, this is the easiest way to gain unauthorised access to an online resource, and there are password-cracking programs online that will plough through a huge list of possibilities.
If your website exists on hosted space and the hacker has changed your password as punishment for using a weak one, you'll need to contact your hosting company and have it changed to let you back in. If your hosting company can restore your site from its backups, it's time to invoke that service. Otherwise, you'll have to reload everything by hand.
If you run your own web server and it's hacked, the hacker will probably have made a mess. You shouldn't trust the server because the hacker may have installed a rootkit to get back in. The first thing to do is unplug the machine from the internet. Next, format it and reinstall the operating system from scratch.
You'll then need to reinstall your web server software and any extension packages, applications and scripts. It's been said countless times, but making nightly backups is far easier.
-------------------------------------------------------------------------------------------------------
First published in PC Plus Issue 291
Liked this? Then check out Who's hacking your PC?
Sign up for TechRadar's free Weird Week in Tech newsletter
Get the oddest tech stories of the week, plus the most popular news and reviews delivered straight to your inbox. Sign up at http://www.techradar.com/register

 Become a TechRadar Insider
Become a TechRadar Insider







