Weak passwords and lack of AV a major issue in social network security
Twitter, Facebook and Microsoft warn of dangers
That many people simply don't run anti-virus software is another major headache, adds Manohar.
"Many people don't have anti-virus software on their computer - that is the biggest vector, that's affecting us quite a bit. About 60% of legitimate websites have had some security vulnerability in the last year. And these vulnerabilities are used to spread malware to your computer.
"So my first suggestion is: get anti-virus on your computer and that will help solve the problem. Because once they get malware on your computer, they can log every keystroke; they can change the websites that you visit; they can change the DNS entry in your computer and they send all this data to arbitrary people and there's an underground market which buys and sells this information.
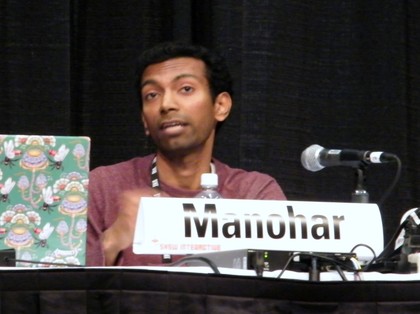
ACCOUNTS FOR SALE: Microsoft's Deepak Manohar
"You can buy Facebook accounts, you can buy Twitter accounts, and you can buy Windows Live accounts, and this is the vector that they use. It is more because of a lack of anti-virus on computers which is leading to people being affected rather than vulnerabilities in the website itself."
Getting your phished account back
So how do you restore access to a compromised account? That's difficult, says Harvey. "If you reset a password and your users don't have a login other than their username and password with no email address connected to it, what are they going to do?"
Sign up for breaking news, reviews, opinion, top tech deals, and more.
McGeehan continues: "If you have a single webmail account and it gets phished, usually a good response would be to block out anyone from accessing that account. But then how do you notify that person that they need to reset their password? Because you've just locked out their email.
"And if the user has malware that is attacking your website – if you terminate the session of the attacker there is a piece of malware on that user's machine that is going to bring it right back so you have to communicate to that user and say 'hey, you have to manually remove malware from your machine and then we'll do the rest of the process, which will include resetting your password'."
"And that's really hard," adds Harvey. "Telling someone 'hey, your computer is infected - trust us, we are a site on the internet!' It's not very convincing to a lot of people.
"We have a lot of users who will write in and say 'you suspended my account, what's up?' and we say 'you're super-infected, actually' and they will say 'no, I downloaded five torrents last week, and they were .EXEs, but I am not infected.'
"Telling a user in a non-aggressive but factual way is really hard. This is their Facebook account, their Twitter account, their email account, their online identity of some form and you are telling them that it is jacked up and they cannot touch it right now. Nobody wants to hear that.
"So telling them that in a way that doesn't come across as us being aggressive or over-protective or 'we just made an error on our end'… We get a lot of 'no, you must be wrong'. And we're like, 'actually you posted malware. Seven times. In 18 seconds. You are."
-------------------------------------------------------------------------------------------------------
Liked this? Then check out 10 easy ways to boost your online security
Sign up for TechRadar's free Weird Week in Tech newsletter
Get the oddest tech stories of the week, plus the most popular news and reviews delivered straight to your inbox. Sign up at http://www.techradar.com/register
- 1
- 2
Current page: Lack of anti-virus protection causes headaches
Prev Page Weak passwords on social network sitesAfter watching War Games and Tron more times that is healthy, Paul (Twitter, Google+) took his first steps online via a BBC Micro and acoustic coupler back in 1985, and has been finding excuses to spend the day online ever since. This includes roles editing .net magazine, launching the Official Windows Magazine, and now as Global EiC of TechRadar.

 Become a TechRadar Insider
Become a TechRadar Insider







