Best Antivirus Software of 2026: Expert Reviews, Testing, and Rankings
We've ranked and reviewed the best antivirus software available in 2026

- Today's top deals
- Quick List
- Best overall
- Best for families
- Best for mobile
- Best for Wi-Fi security
- Best for ad blocking
- Best for gamers
- Best for malware removal
- Best for Mac
- Best for banking
- Best for customization
- Antivirus rankings
- How to pick an antivirus software
- How we test antivirus
- Antivirus FAQs
Antivirus software is a digital shield the intercepts malicious files before they can run. If left unchecked, these files could steal your files, encrypt them, or delete them entirely - sometimes leaving you with a device that no longer works.
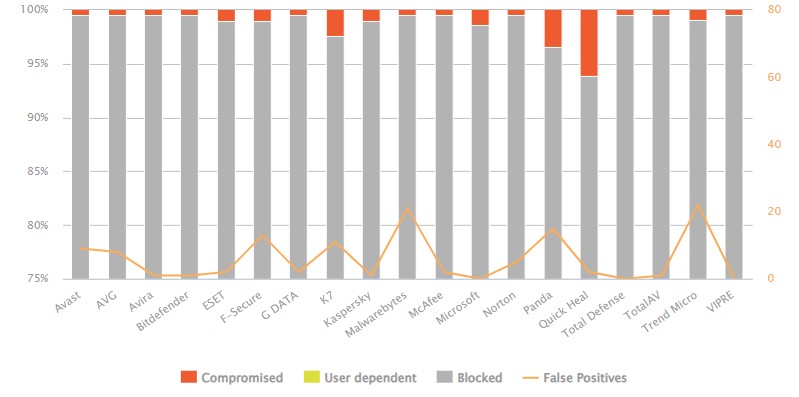
Our team of experts test all the best antivirus software hands on, using both industry standard and our own bespoke EICAR files to test antivirus detection rates. We then compare our findings to the testing performed by third party labs such as AV-TEST and AV-Comparatives.
Bitdefender is the best antivirus in 2026 for most people, and has consistently outperformed other software in testing. Norton and McAfee also score very highly.
There is also free antivirus software for those who do not have the budget for a premium options, and we have also rounded up Mac antivirus software and Android antivirus apps for device specific protection.
Today's Best Antivirus Deal
Reader Offer: Norton 360 Deluxe - Up to 58% Off (First Year)
Norton 360 Deluxe provides comprehensive protection against malware and viruses, secures your internet traffic with a Secure VPN, and even scans for leaked credentials using Dark Web Monitoring. Plus, you also get a Parental Control app and a 50GB Cloud Backup to store all your sensitive files and precious memories.
Techradar Pro Approved Sponsored Offer
Reader Offer: Norton 360 Deluxe - Up to 58% Off (First Year)
Norton 360 Deluxe provides comprehensive protection against malware and viruses, secures your internet traffic with a Secure VPN, and even scans for leaked credentials using Dark Web Monitoring. Plus, you also get a Parental Control app and a 50GB Cloud Backup to store all your sensitive files and precious memories.
Techradar Pro Approved Sponsored Offer

Benedict has spent over 7 years writing about security issues, covering everything from major data breaches and cyber attacks, to the malware and credentials thefts that threaten livelihoods and personal security. He has a passion for security products that keep people safe, and the knowledge to help them make the right decision.
January 2026 Update - While the rankings remain unchanged, this update included price checking, navigation optimizations, and fact checking to ensure all the information on this page is correct in 2026.
Quick List

Bitdefender is the best antivirus software available today. It offers protection against existing and new threats with unbeatable detection rates. Plus, you also get a password manager, secure browser, VPN, and ransomware protection included.

Norton is the best antivirus software for families, providing you with malware protection, firewall, and online backup with cloud storage. Plus, the included password manager, parental control app, and secure VPN make it perfect for household protection.

McAfee is the perfect option for those looking to protect their mobile device. This antivirus software runs on iOS and Android, giving you access to an unlimited VPN, spam filter and an intelligent firewall - along with identity theft protection tools.
Load more products ↓

F-Secure antivirus is perfect for protecting your Wi-Fi network and smart devices with its specialized network protection tools. F-Secure also has exceptional remote and live customer support options to help keep your network secure.

Get rid of those invasive adverts with Avira - the best antivirus for ad blocking. Advertisements are everywhere and some can harbor malicious files and infostealers. Avira can block malware, phishing attempts and ransomware as well.

Avast provides the best antivirus software for gamers, with protection that switches to gaming mode so you get performance and protection. Avast also include a VPN, firewall, malicious URL blocker, and Ransomware Shield for added security.

Malwarebytes is renown for being a first choice in malware removal, and I've always relied on it in a pinch! Malwarebytes antivirus provides real-time security reports for your devices, and if you do get infected, you know you'll be back online in no time.

Macs used to be more secure by default, but not any more. Intego is the choice for Mac users looking to add an extra layer of antivirus protection. It also offers a great MacOS system cleaner to keep your device in tip-top shape, as well as some handy parental controls.

Trend Micro antivirus is the best for frequent bankers with a dedicated top-of-the-range PayGuard secure banking tool. With Trend Micro, you can also benefit from reliable malware protection and a very capable malicious URL blocker.

If you are looking to customize your antivirus protection, look no further than ESET. ESET antivirus software is highly configurable and easy to install, allowing you to customize the level of protection you receive at the application level.
The Best Antivirus Software in 2026:
Why you can trust TechRadar
Best overall

Specifications
Reasons to buy
Reasons to avoid
Use if:
✔️ You want a full antivirus toolkit: Bitdefender's features hunt down malware and protect against ransomware without disrupting your browsing.
✔️ You don't want to sacrifice too many resources: Bitdefender doesn't take up a lot of storage space, so you don't need to worry about sacrificing system speed for security.
✔️ You're new to antivirus solutions: Bitdefender is easy to install and use. Its real-time protection is even enabled from the get-go.
Don't use if:
❌ You want quick scans: initial and deep scans take almost an hour to complete (five times longer than other antivirus on average). Thankfully, you'll still be able to work, play, and browse when they're running.
❌ You need identity theft monitoring: Bitdefender has some monitoring tools to track online identities, but doesn't offer round-the-clock protection from identity theft.
❌ You're already infected with malware: Bitdefender isn't as effective when it comes to removing threats already attacking your system. For current infections, try Malwarebytes.
Our thoughts:
Bitdefender is more than just antivirus software - it can be a life security suite depending on the plan you choose. It consistently impresses with its ability to identify threats and stop them in their tracks and has scored very highly in our own testing and testing done by third-party laboratories.
Bitdefender Total Security includes parental controls, a VPN, vulnerability scanner, and a dedicated browser. The software is remarkably easy to use and runs on most major operating systems. Most of the features will come enabled by default making it a hassle-free installation process - just click and go.
▶ Try Bitdefender Total Security free for 30 days
Bottom line: ⭐⭐⭐⭐½
🔒 Bitdefender is the best antivirus package on the market—and has been for a few years. It combines watertight security tools with straightforward apps and, best of all, offers fantastic value for money.
Features | Notes | Rating |
|---|---|---|
Protection | Consistently earns high marks from third-party security test labs | ⭐⭐⭐⭐⭐ |
Performance | Won't impact your speed or create noticeable slowdown | ⭐⭐⭐⭐⭐ |
Ease of use | Most key features are automatically enabled and apps are intuitive | ⭐⭐⭐⭐ |
Advanced tools | Safe banking features, webcam monitoring, and parental controls to name a few | ⭐⭐⭐⭐⭐ |
Customer support | Bitdefender lacks live support but has a library of video tutorials, how-to articles, and a helpful user community | ⭐⭐⭐⭐ |
Value | There are cheaper solutions out there, but you're getting a lot of functionality and value with Bitdefender | ⭐⭐⭐⭐ |
Read our full Bitdefender review here.
Best for families

Specifications
Reasons to buy
Reasons to avoid
Use if:
✔️ You need family protection: the 5 device coverage with the inclusion of a password manager, parental control app, and 50GB secure cloud backup makes it a great option for families.
✔️ You want multi-device protection: keep your mobile phones and tablets secure with sleek apps that include Wi-Fi security.
✔️ You need to secure your browser: Norton hides your IP with a VPN, and your browsing history, so you can surf the web without leaving an identifiable trail.
Don't use if:
❌ You're on a budget: Norton is hardly a budget option—even with its new-user deals—and only gets pricier on renewal.
❌ You want a stellar VPN: while solid, Norton Secure VPN doesn't top our best VPN list.
Our thoughts:
Norton is a household name in the antivirus industry with very strong testing results. In our testing it detected all our sample files, and has consistent high sores across independent testing labs.
Norton 360 Deluxe goes beyond Norton's award winning malware protection and includes a range of tools for family security. Deluxe is perfect if you are looking for family protection as you can protect up to 5 devices, store precious memories in the generous cloud backup, and use parental controls to ensure your children are safe online.
▶ Try Norton 360 Deluxe and get a 60-day money-back guarantee
Bottom line: ⭐⭐⭐⭐
🔒 Norton excels when it comes to basic malware protection and offers some awesome tools for families—like its parental control app, VPN, and password manager. These extras make it an expensive option, however.
Features | Notes | Rating |
|---|---|---|
Protection | Excellent at detecting known malware, malicious URLs, and leaked credentials | ⭐⭐⭐⭐⭐ |
Performance | Slight lag when running, placing it right in the middle of the pack | ⭐⭐⭐⭐ |
Ease of use | Its dual dashboards can be tricky to navigate | ⭐⭐⭐ |
Advanced tools | An impressive tool set, including a solid VPN, password manager, and cloud backup | ⭐⭐⭐⭐⭐ |
Customer support | No problems reaching out to Norton via email, live chat, and even telephone | ⭐⭐⭐⭐⭐ |
Value | An undeniabley pricey product, but a plethora of tools ensure you're getting your money's worth | ⭐⭐⭐ |
Read our full Norton review here.
Best for mobile

Specifications
Reasons to buy
Reasons to avoid
Use if:
✔️ Mobile security is your priority: McAfee's mobile apps provide all-around protection that you can take on the go.
✔️ You want to protect your identity: check out a raft of tools and advanced features designed to safeguard against identity theft and phishing.
✔️ You need good network protection: keep hackers out of your home network system with an intelligent firewall for all of your devices.
Don't use if:
❌ You're on a budget: McAfee is a big name with a big price tag, and particularly pricey on renewal.
❌ You use a Mac: although it does run on Mac computers, the solution still feels a little clunky compared to its Windows version.
❌ You want built-in parental controls: you'll need to pay extra to access parental controls, adding extra cost to a solution that's already pretty expensive.
Our thoughts:
McAfee is another name that frequently tops the tests in our own trials and third-party testing. McAfee has a solid reputation for antivirus protection, and consistently scores top marks.
McAfee+ goes beyond simple antivirus protection and includes a firewall, password manager, file shredder and unlimited VPN all in just the basic tier. The mobile apps are well crafted and easy to use, making it a top choice for those who want protection on the go. You can also use the Online Account Cleanup tool to check if any of your online accounts are having their data hoovered up by less than reputable sites, and help you delete them.
▶ Try McAfee+ with its 30 day money back guarantee
Bottom line: ⭐⭐⭐½
🔒 McAfee is undoubtedly expensive, but earns its spot in my top picks with standout mobile apps, advanced features, and its prioritization of identity protection.
Features | Notes | Rating |
|---|---|---|
Protection | Excellent protection and plenty of extra tools to help keep you secure | ⭐⭐⭐⭐⭐ |
Performance | Infrequent lagging, but not enough to interrupt what you're working on | ⭐⭐⭐⭐ |
Ease of use | Mobile apps are pretty straightforward to use, desktop is a bit overwhelming when you first use it | ⭐⭐⭐⭐ |
Advanced tools | Many tools focus on protecting your identity including a VPN and personal data cleanup, but how well they work depends on what you're willing to pay | ⭐⭐⭐⭐ |
Customer support | Decent FAQs section on its website, and a support community, live chat is with a Virtual Assistant and not a live agent | ⭐⭐⭐⭐ |
Value | One of the most expensive antivirus programs, but you can use it on any number of devices | ⭐⭐⭐ |
Read our full McAfee review here.
Best for Wi-Fi security

Specifications
Reasons to buy
Reasons to avoid
Use if:
✔️ You have a lot of smart devices: F-Secure has one of the best network protection tools to secure every gadget connected to your home internet.
✔️ You value speed: scans balance speed with thoroughness without sacrificing either.
✔️ You need a VPN: the F-Secure VPN does have its limitations, but it's a useful tool to have in a pinch.
Don't use if:
❌ You're new to antivirus: the dashboard is very text-heavy, which can be overwhelming, and it's not the easiest tool to install.
❌ You need Chromebook protection: unfortunately, F-Secure doesn't offer a Chromebook app—meaning you'll have to look elsewhere.
❌ You don't want to be slowed down: you might experience slower load times when opening programs or browsing the web, leading to serious frustration.
Our thoughts:
I frequently write about smart devices being taken over by hackers, so F-Secure is a sight for sore eyes in this respect. While F-Secure doesn't quite rival the scores of other antivirus in testing - and occasionally throws up a few false alarms - it provides great protection for edge, IoT, and smart devices connected to your Wi-Fi network.
One of the standout features of F-Secure Total is the 24/7 live and remote support that can help you with any bugs or glitches you might experience - something very few providers offer. The network protection can even protect your on unsecured public networks while the built-in VPN keeps your traffic encrypted and private.
▶ Try F-Secure Total for 30 days free
Bottom line: ⭐⭐⭐⭐
🔒 F-secure takes some getting used to, but all of the most important security and privacy tools are there—including incredible network protection and 24/7 live support.
Features | Notes | Rating |
|---|---|---|
Protection | Excellent malware blocking and protects smart devices connected to your home network | ⭐⭐⭐⭐⭐ |
Performance | Some slowdown when launching programs or navigating the web | ⭐⭐⭐ |
Ease of use | Not the easiest to figure out, but the tutorials do help | ⭐⭐⭐⭐ |
Advanced tools | Not as many tools as other antivirus software, but the ones included are helpful | ⭐⭐⭐⭐ |
Customer support | Live support is available including remote support for difficult issues | ⭐⭐⭐⭐⭐ |
Value | First-time users get a great bargain, but the price jumps higher upon renewal | ⭐⭐⭐⭐ |
Read our full F-Secure review here.
Best for ad blocking

Specifications
Reasons to buy
Reasons to avoid
Use if:
✔️ You want a reliable ad-blocker: Avira includes a handy ad blocker to keep your browsing fast and hassle free.
✔️ You'd like to try before buying: Avira's free plan is limited, but gives you a good taste of what to expect if you choose to upgrade.
✔️ You want configurability: Avira gives users plenty of ways to tailor their security experience.
Don't use if:
❌ You use a lot of locally saved apps: during my testing, I found that Avira causes apps to launch more slowly.
❌ You need mobile protection: most of Avira's packages aren't available for mobile devices—and those that are have a hefty price tag.
❌ You want optimal PC performance: Avira has a tendency to take a bit out of your device performance.
Our thoughts:
Avira performs really well in testing, being able to detect our own bespoke EICAR files and performing well against existing and new threats in tests done by third parties.
A standout point is the included ad blocker which significantly improves web page load times and general user experience. Avira Internet Security also includes a handy bargain hunting tool to help you get the best deals when shopping online. While it does include a system optimizer tool and PUA shield to reduce PC slowdown, it does tend to take up a few more resources than we would like - but overall it is a solid antivirus solution.
▶ Try Avira antivirus for free
Bottom line: ⭐⭐⭐⭐
🔒 Avira has a lot of handy tools that can be configured down to the last detail and a free plan you can use to try before you buy—however, it's not the best pick for mobile devices.
Features | Notes | Rating |
|---|---|---|
Protection | No problem stopping both known and new malware threats | ⭐⭐⭐⭐⭐ |
Performance | Slower at loading webpages and downloading software | ⭐⭐⭐⭐ |
Ease of use | Dark mode interface that is intuitively laid out, but most tools, including ransomware protections, have to be turned on | ⭐⭐⭐ |
Advanced tools | Includes some good advanced security tools, but not enough to be compared with other "internet security" suites | ⭐⭐⭐ |
Customer support | Some basic help articles are online, the only way to contact a live agent is through the email form | ⭐⭐⭐ |
Value | Decent price point and has a monthly subscription available | ⭐⭐⭐⭐ |
Read our full Avira review here.
Best for gamers

Specifications
Reasons to buy
Reasons to avoid
Use if:
✔️ You want the best malware protection: Avast came out on top in all of our malware-blocking tests.
✔️ Gaming is your priority: block untrustworthy incoming connections with a handy gaming mode—which is enabled by default.
✔️ You want to try before buying: Avast's free plan has its limitations, but effectively showcases the product's capabilities.
Don't use if:
❌ You don't want to delete unwanted apps: Avast will do its very best to install its own internet browser and make it your new default, which is slightly frustrating.
❌ You need better VPN access: depending on your plan, you might experience bandwidth caps and a limited choice of servers
❌ You need clear warnings: at times, unwarranted warnings can pop up with no clear way to stop them
Our thoughts:
Avast is one of the best performing antivirus software providers, scoring top marks in our testing and achieving impressive results in testing performed by the third party pros.
Avast One is designed to be a simple all-in-one app that does everything it says on the tin, and if you want it to do more, it can. The app automatically goes into gaming mode so that you can squeeze all the performance you need out of your device without your security taking a hit. Avast One comes with more features than I can list, but some notable inclusion are dark web monitoring, scam detection, and an advanced firewall to keep hackers out of your network.
Bottom line: ⭐⭐⭐⭐
🔒 Avast One is a malware-blocking powerhouse that stops threats dead in their tracks. It won't slow your device to a crawl, either, and is incredibly easy to use—a great pick for antivirus first-timers.
Features | Notes | Rating |
|---|---|---|
Protection | Top scores for malware protection from third-party test labs | ⭐⭐⭐⭐⭐ |
Performance | Doesn't create noticeable lag, and has an awesome gamer mode | ⭐⭐⭐⭐⭐ |
Ease of use | Friendly apps for all devices with a fresh design, and they're easy to use | ⭐⭐⭐⭐ |
Advanced tools | Paid users get the lion's share of features and access to an unlimited VPN | ⭐⭐⭐⭐ |
Customer support | No live chat, but you can typically get a response from support staff via email within 24 hours | ⭐⭐⭐⭐ |
Value | Subscriptions won't break the bank and come with a plethora of features, and the free plan is equally impressive | ⭐⭐⭐⭐⭐ |
Read our full Avast review here.
Best for malware removal

Specifications
Reasons to buy
Reasons to avoid
Use if:
✔️ You have an existing malware infection: when it comes to getting rid of threats that are already on your computer, Malwarebytes is unbeatable.
✔️ You want to see real-time security reports: check out what the antivirus is doing, at any time, with detailed insights.
✔️ You want multi-device protection: protect between two and 10 devices without spending a fortune.
Don't use if:
❌ You need flawless detection: Malwarebytes can struggle to pinpoint, and resolve, new threats.
❌ You want to protect more than Windows devices: while the solution is compatible with other operating systems, it's also more limited.
Our thoughts:
Malwarebytes has always been my choice when it comes to getting rid of a malware infection, but wouldn't be my go-to when it comes to real-time protection. In our own testing (and independent testing), it scored in the middle ground of what I would expect.
But, as I said, if you currently have malware lurking on your device then Malwarebytes is a solid tool for getting rid of it - and what Malwarebytes lacks in testing scores, it makes up for in features. The software will provide real time protection reports, scam protection, and even includes AI-powered protection. Some features are only available on the Windows app however.
▶ Get Malwarebytes free edition
Bottom line: ⭐⭐⭐½
🔒 Malwarebytes excels at removing malware already on your device, but can fall short in real-time protection.
Features | Notes | Rating |
|---|---|---|
Protection | Not as effective at blocking malware as it is at removing current infections | ⭐⭐⭐⭐ |
Performance | Fairly light on resources, so not a problem to run it in the background | ⭐⭐⭐⭐⭐ |
Ease of use | Basic use is easy to figure out, but it gets harder when you need to customize settings | ⭐⭐⭐⭐ |
Advanced tools | Doesn't have the level of advanced features we'd expect in a Pro program | ⭐⭐⭐ |
Customer support | All support links redirect you to its extensive knowledgebase rather than provide live support options right away | ⭐⭐⭐ |
Value | Monthly subscription prices are about right for what is offered | ⭐⭐⭐⭐ |
Read our full Malwarebytes review here.
Best for Mac

Specifications
Reasons to buy
Reasons to avoid
Use if:
✔️ You're a Mac user: Intego is designed specifically for Mac machines.
✔️ You need parental controls: you won't find many other antivirus solutions for Mac that include configurable parental controls.
✔️ You want to boost your Mac performance: Intego's Mac Washing Machine can spot vulnerable software and old apps and help clear them up.
Don't use if:
❌ You need mobile protection: unfortunately, this antivirus offering is only available for desktops.
❌ You're looking for powerful extras: Intego doesn't have the quantity, or quality, of advanced features as our other picks.
❌ You have a mixed device household: households with a mix of different operating systems won't all benefit from the same plan.
Our thoughts:
Intego scores well in testing across the board and is specially built to be friendly to Mac machines. In fact, it offers a Mac Washing Machine tool to keep your device free of vulnerable and outdated applications that could be a potential virus entry point.
Outside of scoring though, there is a bit of a downside. Each of the five security applications included in the Intego Mac Premium Bundle X9 has to be installed individually, and while this is great for those looking to pick and choose what parts they use, many of the other providers have a single app that includes all the various protection tools. If you don't mind taking the time to install them, Intego makes an excellent Mac protection antivirus.
Bottom line: ⭐⭐⭐½
🔒 Intego is a great pick for Mac machines, and can clean up your system to keep it running efficiently.
Features | Notes | Rating |
|---|---|---|
Protection | Misses a few threats, but does score higher than average for malware detection | ⭐⭐⭐⭐ |
Performance | We noticed a bit of lag with the app itself, but it didn't seem to affect our working and browsing too much | ⭐⭐⭐⭐ |
Ease of use | Each tool is a separate download with its own dashboard making it harder to navigate the entire package | ⭐⭐⭐ |
Advanced tools | A bit limited, but the system cleaner and parental controls are effective | ⭐⭐⭐ |
Customer support | Lots of pages to navigate through the find the support email form, live chat is sometimes available | ⭐⭐⭐ |
Value | It's expensive, other Mac antivirus is available for cheaper and with more tools | ⭐⭐⭐ |
Read our full Intego review here.
Best for banking

Specifications
Reasons to buy
Reasons to avoid
Use if:
✔️ You bank or shop online: PayGuard, Trend Micro's secure banking feature, is one of the best in the industry.
✔️ You want web protection: Trend Micro has a robust URL blocker that will warn you if you stumble across a dangerous site.
✔️ You don't want too many bells and whistles: Trend Micro offers a simple antivirus software without any overwhelming tools and options.
Don't use if:
❌ You're an avid gamer: Trend Micro has a noticeable impact on device performance, and can interrupt gameplay (and streaming.)
❌ You want to customize your experience: if you're looking for an antivirus solution you can customize, you're better off with Bitdefender.
❌ You are looking for more than just antivirus: Trend Micro lacks the extra features to protect more than just your device.
Our thoughts:
Trend Micro sits in the middle ground in terms of antivirus protection, both in our own testing and testing done by the independent labs, but is near-unrivaled when it comes to banking protection.
Trend Micro Antivirus+ Security offers a tool known as PayGuard, which helps keeps payments made through your browser secure and out of the clutches of any hackers that could be lurking online. Trend Micro does unfortunately hamper device performance and doesn't offer as many extra security features as its rivals - which could be a good thing for those looking for a simple and easy to use solution.
▶ Try Trend Micro Antivirus+ Security for 30 days risk-free
Bottom line: ⭐⭐⭐
🔒 Trend Micro doesn't come with a ton of added features, but if you need a boost of security for your banking and online shopping, Pay Guard is a fantastic option.
Features | Notes | Rating |
|---|---|---|
Protection | Struggles a bit to stop brand new threats not included in malware databases | ⭐⭐⭐⭐ |
Performance | Causes some slowdown when downloading programs or launching an application | ⭐⭐⭐⭐ |
Ease of use | Very simple interface with essential security tools you need already turned on | ⭐⭐⭐⭐⭐ |
Advanced tools | Not a lot is included with its basic subscription, but Pay Guard comes with all antivirus subscriptions | ⭐⭐⭐ |
Customer support | Phone, email, and chat support are all available, but there may be some delays when trying to connect | ⭐⭐⭐⭐ |
Value | Not too bad for basic protection of a single Windows device | ⭐⭐⭐⭐⭐ |
Read our full Trend Micro review here.
Best for customization

Specifications
Reasons to buy
Reasons to avoid
Use if:
✔️ You want an antivirus you can configure: plenty of low-level configurability gives you granular control over setup and features.
✔️ You need multi-device support: with ESET, you can choose how many devices to include in your subscription.
✔️ You want to protect multiple network devices: everything that you connect to your Wi-Fi network is protected, including IoT and smart devices.
Don't use if:
❌ You need a wide array of tools: ESET isn't as feature-rich as its closest competitors, though its advanced tools are still solid.
❌ You want iOS support: if you want to secure your iPhone or iPad, I'd recommend checking out Bitdefender's mobile apps.
❌ You want zero-day malware protection: ESET reserves its top level of protection for the more expensive subscriptions.
Our thoughts:
In terms of protection, ESET antivirus software sits in the big leagues with the likes of Avast and Bitdefender - but this level of protection comes at a cost, even without all the extras.
The ESET Essential plan is exactly that, just the essentials. You get antivirus protection for one device, plus a firewall, banking protection, and a network shield to protect internet connected devices. So if you're looking for a feature-rich package, you will have to opt for the highest tier subscription. If you do, you can access an unlimited VPN, identity protection, and a password manager - but keep in mind many other brands provide these without breaking the bank.
▶ Try ESET Internet Security for 30 days free
Bottom line: ⭐⭐⭐
🔒 ESET is easy to install, though a little more difficult to figure out once it's up and running. Plus, some important security features are reserved for its most expensive product.
Features | Notes | Rating |
|---|---|---|
Protection | Slightly below average of the industry average in some independent tests, doesn't include new threat detection in all programs | ⭐⭐⭐ |
Performance | Definitely can feel the lag when using this antivirus | ⭐⭐⭐ |
Ease of use | The interface feels outdated with a lot of text that gives it an overwhelming, busy look | ⭐⭐⭐⭐ |
Advanced tools | Missing some important tools like a password manager and data encryption, but the number of security features is impressive | ⭐⭐⭐⭐ |
Customer support | Not the easiest to find answers to questions and even harder to figure out how to get a hold of a live person | ⭐⭐⭐ |
Value | An overall good deal, though we wish more was included | ⭐⭐⭐⭐ |
Read our full ESET review here.
TechRadar's antivirus rankings
There are more antivirus solutions on the market than we can count—but only ten spots in our list of favorites. Below, you can check out our rankings at a glance, including some honorable mentions that just missed out on a spot in our shortlist.
Provider | Summary |
|---|---|
1. Bitdefender | Sets the standard for all antivirus to reach for |
2. Norton | Good protection and great identity theft services |
3. Avast | Easy to use, great advanced security, excellent gaming mode |
4. McAfee | Good for mobile, and decent on other devices, too, but expensive |
5. F-Secure | Protects smart devices, such as TVs and Amazon Echo connected to your network |
6. Trend Micro | Good protections for banking and shopping online |
7. AVIRA | Decent tools with a good free antivirus available |
8. ESET | Okay for basic protection, but feels outdated and falls behind better options |
9. Malwarebytes | Not the best as a first defender malware blocker, but is excellent at removing threats already on your device |
10. Intego | Specifically designed for Mac computers, does well at blocking threats, but awkward to use |
How to choose antivirus software
How do you decide on just one antivirus solution when there are dozens of viable candidates out there? The obvious answer is to consult our rankings—our shortlist is the result of pooled expert knowledge, in-house testing, third-party security labs testing, and thorough, continually updated reviews of the top antivirus players.
Perhaps more importantly, however, you need to consider your own needs and use case. Do you have a ton of devices to protect? Do you need advanced features or specific tools? Do you want a service with a built-in VPN to save money on subscription fees?
These considerations will vary from person to person and might mean that our number one pick isn't your match made in heaven. Our recommendations can point you in the direction of some stellar options, but you'll need to modify these based on your individual requirements.
For more thoughts on this, check out our article exploring how to choose the best antivirus.
How we test antivirus software - our review methodology
To get a clear, accurate, and thorough picture of each antivirus, I take a multi-faceted approach to my testing—and I make sure I get hands-on experience with each product.
Thanks to our team's background in IT, we're able to create malware files for specific use in testing environments. We keep these files on a short leash and let them wreak a little havoc—nothing that we can't control, of course—but this is an important part of the process, seeing as they're new threats that no antivirus software will be familiar with.
Lots of antivirus developers provide a test file called 'EICAR' that simulates a threat that isn't a threat. The problem with relying on this file during testing is that antivirus companies have made sure that their software recognizes it. Using our own bespoke malware helps us evaluate how well these services deal with the unknown.
We don't rely solely on our findings, however. There are all sorts of ways to test antivirus and some fantastic labs out there that do it a lot more frequently than we do. That's why we refer to results from AV-Comparatives and AV-Tests to paint a broader picture of the antivirus software's capabilities and assign a fair protection score.

Performance is a critical consideration during our testing. We need to know how much slowdown is caused by installing and running the antivirus, and how much it's going to impact your day-to-day activities. After all, an antivirus that zaps every threat known to man, but slows your machine down to a crawl, won't be much use to anyone.
We know that resources will be used, seeing as the antivirus programs are saved locally on the device, but we still measure things like how long it takes to open a browser, navigate to a website, attach a file to an email, or how long it takes a webpage to load fully.
Online speed test websites give us a hand with this process by providing the nit-picky numbers to supplement our real-time testing. That way, we can balance solid statistics with our individual experiences, to get a real feel for how the antivirus behaves outside of a lab.
As you'd expect, real-time testing involves us installing and using antivirus programs on our home devices. We'll keep track of anything out of the ordinary, the highs and lows, and how easy the software is to navigate. This is also where we'll dig into the tools and settings to see if they do everything that they're supposed to do—think password managers, file encryption, VPN add-ons, and parental controls.
Customer support is another important aspect of any review. Usually, it's easy enough to follow along with the on-screen instructions provided by the installation wizard when you download new antivirus software, but that doesn't mean there aren't times when you'll need a little extra help from an agent.
We evaluate each company's support options, ranging from the live chat support and email ticketing systems, if available, and the online library of resources. We measure how quickly agents respond to our inquries, how detailed their reply is, and how accessible the company's resources are—particularly for new users.
Tested by

Mike is a lead security reviewer at Future, where he stress-tests VPNs, antivirus and more to find out which services are sure to keep you safe, and which are best avoided.

Sead is a seasoned freelance journalist based in Sarajevo, Bosnia and Herzegovina. He covers all things cybersecurity, including ID theft, ransomware, and data breaches, as well as laws and regulations related to the field.
The best antivirus FAQs
What is the best antivirus of 2026
I put all of today's top dogs to the test and found that Bitdefender is the best antivirus software in 2026.
It's a superb bit of kit—from its entry-level Bitdefender Antivirus Plus and its cast-iron malware defenses, excellent threat detection and genuinely value-adding extra features, right up to its all-singing, all-dancing Total Security that adds an array of maintenance tools and can be used to protect your family's computers, tablets and phones.
What does antivirus do? How does virus protection work?
An antivirus app sits on your device like a guard dog, watching over the entire system and sniffing out suspicious intruders. In short, it offers real-time defenses against viruses or other threats, which, if detected, are immediately dealt with, preventing them from carrying out their destructive payload. As well as this automated protection, you can run manual virus scans whenever you wish.
Antivirus applications use what are called virus ‘definitions’ to catch intruders. Think of these as the fingerprints of malware, and if something is spotted coming onto your system that has a matching fingerprint, the antivirus leaps into action, quarantining the offender. As another line of defense, antivirus programs also use what are called ‘heuristics’ that look for any file or process exhibiting suspicious behavior—this allows the app to potentially catch any freshly made malware that isn’t yet in its definitions database.
For more details on this topic, see our full breakdown of exactly how antivirus software works.

Do I really need antivirus in 2026?
The internet is jam-packed with threats, like ransomware, cooked up by cybercriminals willing to do whatever it takes to get what they want. Security breaches are commonplace, unfortunately, and hackers use malware to crack a company's system and make off with important files—including customer information. Unfortunately, that means that you're the ultimate victim of these attacks, seeing as they can lead to identity theft.
Today's best antivirus programs can help prevent identity theft by keeping an eye on the dark web, where all sorts of personal information is bought and sold. You'll also get protection against phishing scams, and block messages designed to trick you into handing over personal information to dodgy third parties.
More and more antivirus software includes a VPN, too, which will safeguard your browsing sessions regardless of the device you're using. You'll be able to bypass geo-restrictions and blocks, and avoid cookies, trackers, and invasive advertisements.
You may have heard arguments that if you’re prudent about where you browse on the web, and what you download or click on, you’ll be fine—and that’s true to a certain extent, but I really wouldn’t risk it. Even well-known websites might occasionally be victims of malware being peddled via their adverts (in other words, the ad networks they work with), for example, so no matter how cautious and tech-savvy you are, it’s worth having an antivirus app as a fall-back defense.
Fortunately, the best antivirus products are getting more and more affordable—and free antivirus keeps improving, too.
Is free antivirus enough?
Unfortunately, there's not a simple yes or no answer to this question.
A good free antivirus can boost your digital security, and a lot of folks will rely on Microsoft Defender to do the job. The good news is that Microsoft Defender is a decent option that'll cover all of the basics when it comes to putting a stop to viruses and malware.
You'll find that most free antivirus use the same protection engine (the central tech that monitors your device and thwarts threats) as their paid counterparts.
However, premium antivirus programs offer extra features above and beyond the fundamentals. A robust system of parental controls could be a huge win for those with kids, for example. Or, a dedicated anti-ransomware layer of protection that only comes with the paid-for product could help catch one of the most dreaded infections and halt it in its tracks.
Given how cheap some premium antivirus apps are—particularly with the various deals on offer—it’s well worth considering going this route instead to get extra features that could give you more peace of mind.
For more on this, read our full piece on whether free antivirus is enough to protect you.
Editors' note: Kaspersky Anti-Virus used to appear on this list. However, considering the current climate, and the recent ban of the sale of Kaspersky software in the US, we've made the decision to remove the provider.
Although much of the company's core processes now take place in Switzerland, the fact that its headquarters remain in Moscow, and that there are prior allegations around government coercion, it feels prudent to urge caution when considering the provider.
What's more, with so many excellent alternatives to choose from, it's impossible to wholeheartedly recommend Kaspersky at this time.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!

Benedict is a Senior Security Writer at TechRadar Pro, where he has specialized in covering the intersection of geopolitics, cyber-warfare, and business security.
Benedict provides detailed analysis on state-sponsored threat actors, APT groups, and the protection of critical national infrastructure, with his reporting bridging the gap between technical threat intelligence and B2B security strategy.
Benedict holds an MA (Distinction) in Security, Intelligence, and Diplomacy from the University of Buckingham Centre for Security and Intelligence Studies (BUCSIS), with his specialization providing him with a robust academic framework for deconstructing complex international conflicts and intelligence operations, and the ability to translate intricate security data into actionable insights.
- Mike WilliamsLead security reviewer
- River HartTech Software Editor

 Become a TechRadar Insider
Become a TechRadar Insider







