'We will be taking action to protect American innovation': White House accuses China of 'systematically' extracting American AI technologies
China is allegedly stealing US AI models

- The US has accused China of stealing American AI models
- Chinese actors allegedly used a proxy network and jailbreaking techniques
- The accusation will likely strain US-China relations after a period of recompense
The White House has accused China of orchestrating a campaign to steal AI models from American developers on an ‘industrial-scale’.
In a memo, Michael Kratsios, director of the White House Office of Science and Technology Policy, said, “The US government has information indicating that foreign entities, principally based in China, are engaged in deliberate, industrial-scale campaigns to distil US frontier AI systems.”
The accusations come ahead of a meeting between US President Donald Trump and Chinese President Xi Jinping in Beijing next month.
‘Tens of thousands of proxies and jailbreaking techniques’
"Leveraging tens of thousands of proxy accounts to evade detection and using jailbreaking techniques to expose proprietary information, these coordinated campaigns systematically extract capabilities from American AI models, exploiting American expertise and innovation," the White House memo continued.
This isn’t the first time China has been accused of stealing US technology, with the superpower previously in the crosshair for stealing aerospace secrets and industrial technology.
The memo strikes a different tone to previous accusations, with the White House stating, “There is nothing innovative about systemically extracting and copying the innovations of American industry, and there is nothing about supposedly open models that are derived from acts of malicious exploitation.”
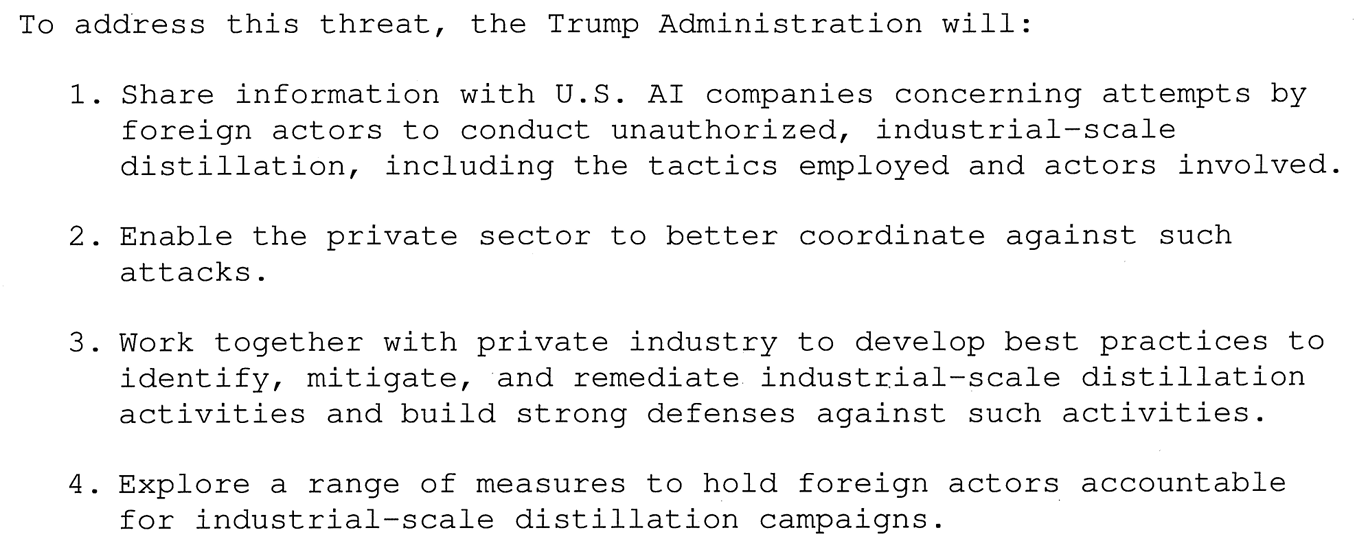
Washington says it will take the following steps:
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
In response, the Chinese Embassy in Washington issued a statement saying that it rejects “the baseless allegations,” and that Beijing “attaches great importance to the protection of intellectual property rights.”
The accusation is likely to strain US-China relations ahead of next month's meeting. Tensions are also likely to rise as the US Congress passes its “largest significant export control mark-up in the history of Congress” that seeks to prevent China from accessing US tech - especially high-powered chips.
Restrictions on the sale of powerful chips to China were eased in January, with the possibility of some of Nvidia’s most powerful chips being sold on a case-by-case basis. But these exports have been thrown into question by the latest restrictions from Congress.
Nonetheless, China has proven itself capable of developing and training powerful AI models such as Deepseek and OpenClaw - both of which have rattled American AI developers as China was believed to be years behind the US.

Follow TechRadar on Google News and add us as a preferred source to get our expert news, reviews, and opinion in your feeds.

Benedict is a Senior Security Writer at TechRadar Pro, where he has specialized in covering the intersection of geopolitics, cyber-warfare, and business security.
Benedict provides detailed analysis on state-sponsored threat actors, APT groups, and the protection of critical national infrastructure, with his reporting bridging the gap between technical threat intelligence and B2B security strategy.
Benedict holds an MA (Distinction) in Security, Intelligence, and Diplomacy from the University of Buckingham Centre for Security and Intelligence Studies (BUCSIS), with his specialization providing him with a robust academic framework for deconstructing complex international conflicts and intelligence operations, and the ability to translate intricate security data into actionable insights.
You must confirm your public display name before commenting
Please logout and then login again, you will then be prompted to enter your display name.

 Become a TechRadar Insider
Become a TechRadar Insider







