‘I can think of a couple Pretti Good reasons!’: Hacktivists may have just cracked open ICE and exposed over 6,000 companies working with the DHS
DHS and ICE apparently suffer cyberattacks

- A hacktivist group has hacked into the US Department of Homeland Security
- The group allegedly stole document containing contracts between ICE and private companies
- The stolen data has been posted online
A hacktivist group has claimed to have broken into systems belonging to the US Department of Homeland Security (DHS) and exposed sensitive files online.
The group, with the self-awarded name “The Department of Peace”, stole data from the Office of Industry Partnership that contained contracts between DHS, Immigration and Customs Enforcement (ICE), and over 6,000 private companies.
Among the companies contracted to work alongside DHS and ICE were Anduril, L3Harris, Raytheon, Palantir, Microsoft, and Oracle.
The Department of Peace
The files stolen by the Department of Peace have been posted online by nonprofit transparency collective, DDoSecrets. The site states that the documents include:
- Company names
- Company URLs
- Names of various employees and sometimes their titles
- Business and potentially personal addresses
- Employee phone numbers
- Employee email addresses
- Tax identification numbers, including employer identification numbers and potentially SSNs
- Other government contractor IDs, such as UEI numbers and CAGE codes
- Some internal comments by DHS staff regarding things like updates to the information above
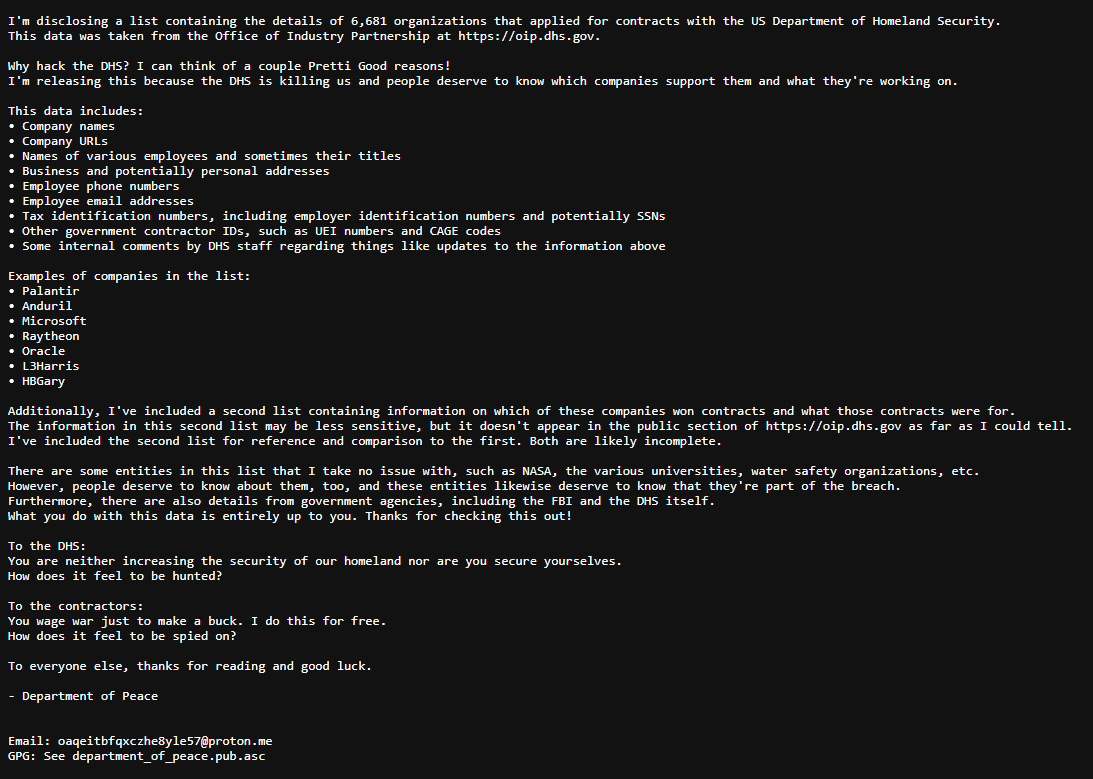
The justification for the hack relates to the killing of two US Citizens, Alex Pretti and Renée Good, by federal agents in Minneapolis. A statement from the hackers accompanying the data states, “Why hack the DHS? I can think of a couple Pretti Good reasons! I'm releasing this because the DHS is killing us and people deserve to know which companies support them and what they're working on.”
The hackers included an additional statement, “To the DHS: You are neither increasing the security of our homeland nor are you secure yourselves. How does it feel to be hunted? To the contractors: You wage war just to make a buck. I do this for free. How does it feel to be spied on?”
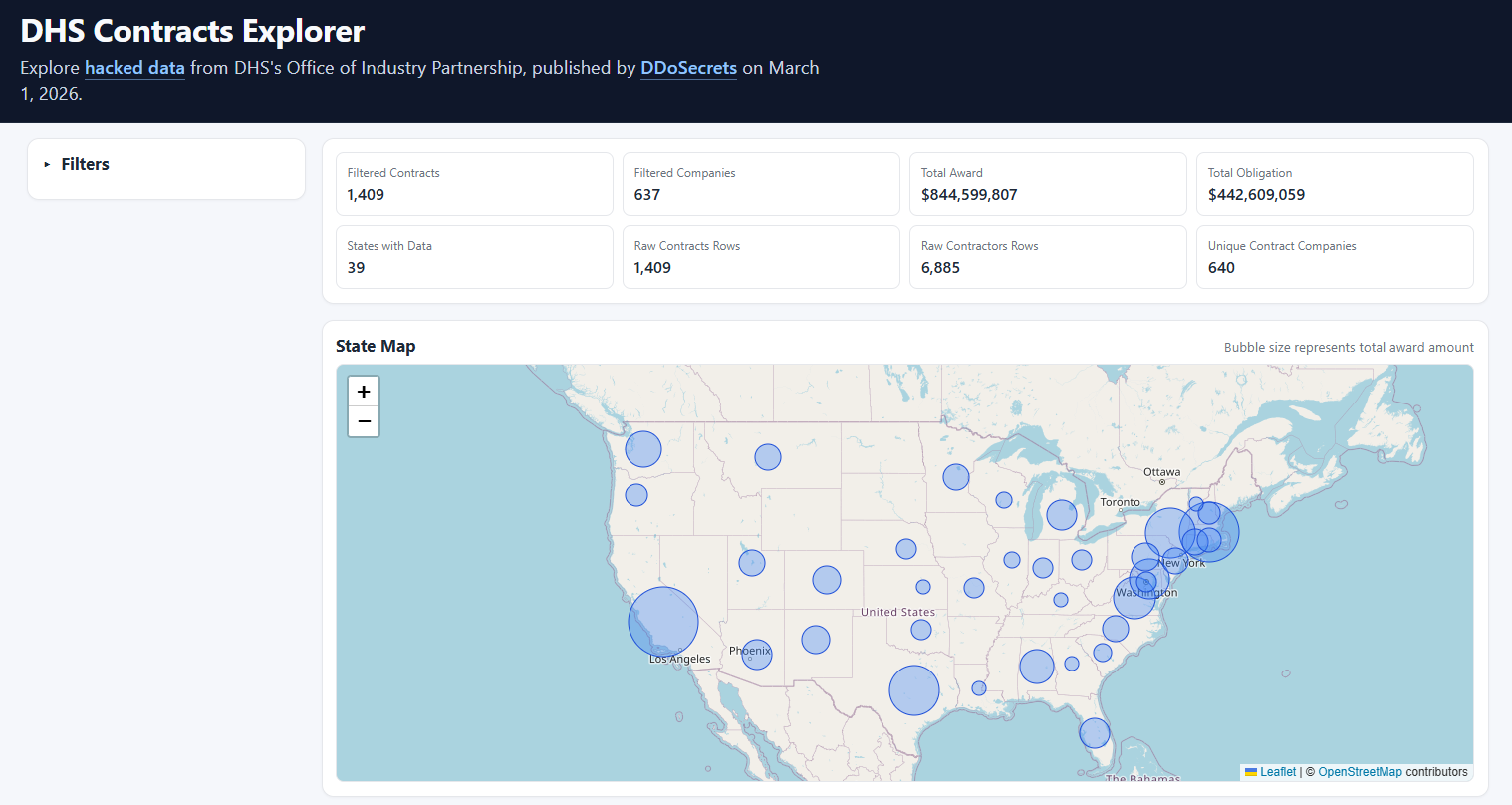
The contractual information stolen from the DHS has been hosted online by Security researcher Micah Lee, and can be filtered by contractor and monetary amount.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
Under the Trump administration, Federal agents from the DHS and ICE have launched one of the most aggressive deportation campaigns which has seen numerous US citizens illegally detained, and numerous persons deported without due process.
Detention centers on US soil have been criticized for having inhumane conditions due to overcrowding. The US has also made use of external detention centers and prisons with alleged human rights abuses including sexual abuse and torture, such as El Salvador’s Cecot prison.
The DHS and ICE did not immediately respond to a request for comment. Any update will be posted here.
Via TechCrunch

➡️ Read our full guide to the best identity theft protection
1. Best overall:
Aura
2. Best for families:
IdentityForce
3. Best for credit beginners:
Experian IdentityWorks

Benedict is a Senior Security Writer at TechRadar Pro, where he has specialized in covering the intersection of geopolitics, cyber-warfare, and business security.
Benedict provides detailed analysis on state-sponsored threat actors, APT groups, and the protection of critical national infrastructure, with his reporting bridging the gap between technical threat intelligence and B2B security strategy.
Benedict holds an MA (Distinction) in Security, Intelligence, and Diplomacy from the University of Buckingham Centre for Security and Intelligence Studies (BUCSIS), with his specialization providing him with a robust academic framework for deconstructing complex international conflicts and intelligence operations, and the ability to translate intricate security data into actionable insights.
You must confirm your public display name before commenting
Please logout and then login again, you will then be prompted to enter your display name.

 Become a TechRadar Insider
Become a TechRadar Insider







