The best Android apps of 2023
The best Android apps for your phone, both free and paid for

Sign up for breaking news, reviews, opinion, top tech deals, and more.
You are now subscribed
Your newsletter sign-up was successful
The best android apps can be tough to find, as there are millions of apps available and not all of them are good.
But we’re here to help. We’ve been using the Google Play Store for a long time now to find the best Android software, putting each promising app through its paces to make sure that it's worth the download.
There are stunning apps in all sorts of categories, from health and fitness to cameras and photo editors, to customization apps, music ones and beyond, so whatever you're looking for there should be the perfect fit available - and you're likely to find it in this article.
So whether you've recently picked up one of the best Android phones or you're just looking to add to your app library, this is the place to start.
We consistently update this guide with new Android apps to consider too, some of which are free and some paid. All of them, though, have been picked out by our experts so you know you’re getting a good one for your phone. So get stuck in, and remember to check back often for all the new additions.
- These are the world's very best Android phones
Best new Android app
Why you can trust TechRadar
This is the latest Android app we've chosen to feature, refreshed every few weeks. Our choices are usually new apps or apps that have recently received a major update, but occasionally hidden gems and other essentials will also be highlighted.
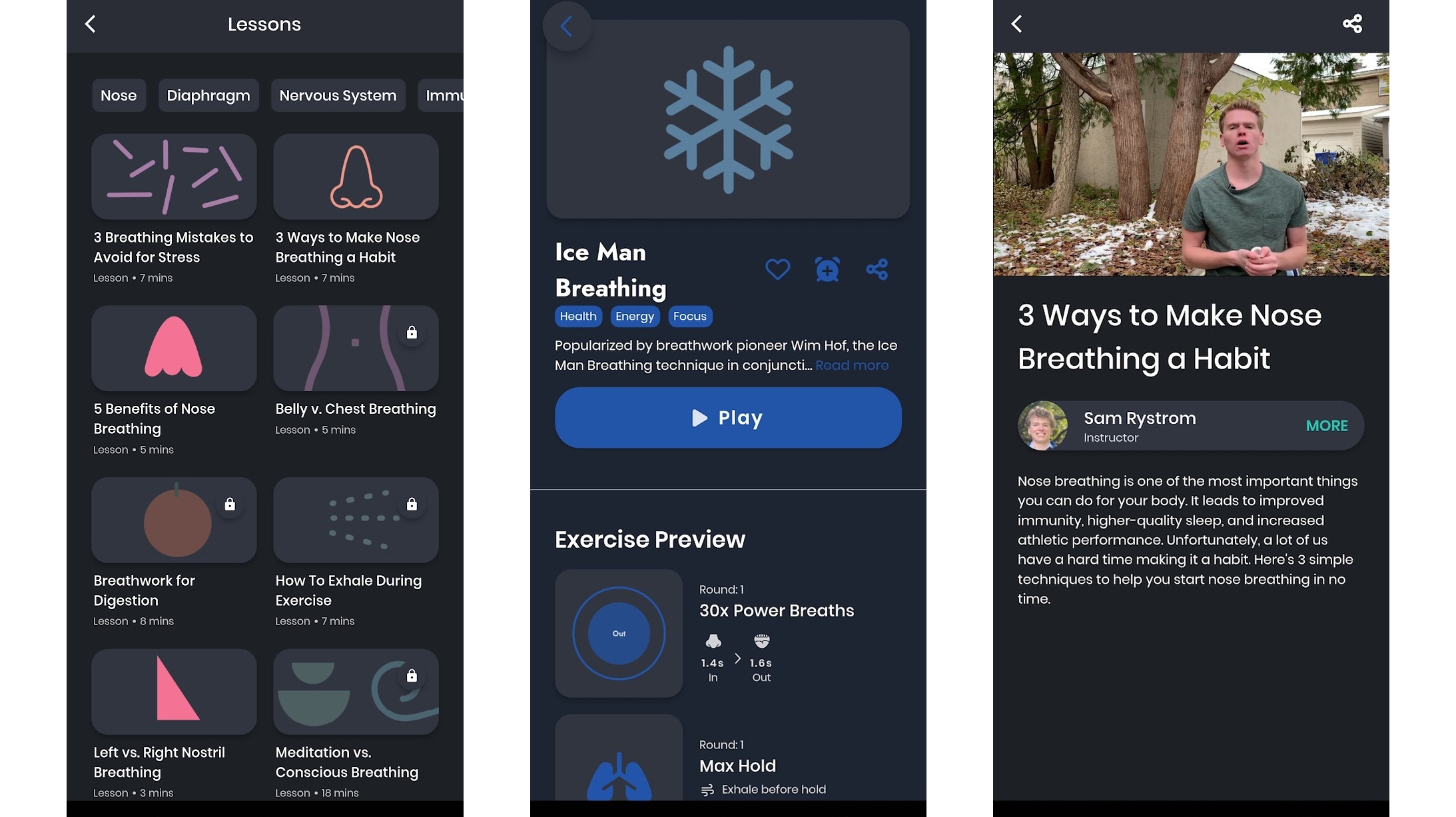
One Deep Breath: Relax & Sleep
Free or $47.99 / £45.99 yearly subscription
We’re never not breathing, yet there’s an art – and science – to breathing effectively, and few of us have mastered it. That’s what One Deep Breath: Relax & Sleep is here to help with.
Through guided breathing exercises, meditation techniques, video lessons, and even the ability to build custom breathing exercises within the app, One Deep Breath will teach you how to breathe in ways that reduce stress and anxiety, improve your focus, stop you snoring, help you sleep, and more.
Some of this is through helping you change the way you breathe as standard – particularly if you’re inclined to breathe out of your mouth rather than your nose – while other things are exercises you can turn to just when you need them.
There’s quite a lot of free content here, but just as much is hidden behind a subscription, which at the time of writing costs $47.99 / £45.99 per year.
The best Android camera apps and photo editors
Our favorite Android apps for shooting, sorting and editing photos and videos.
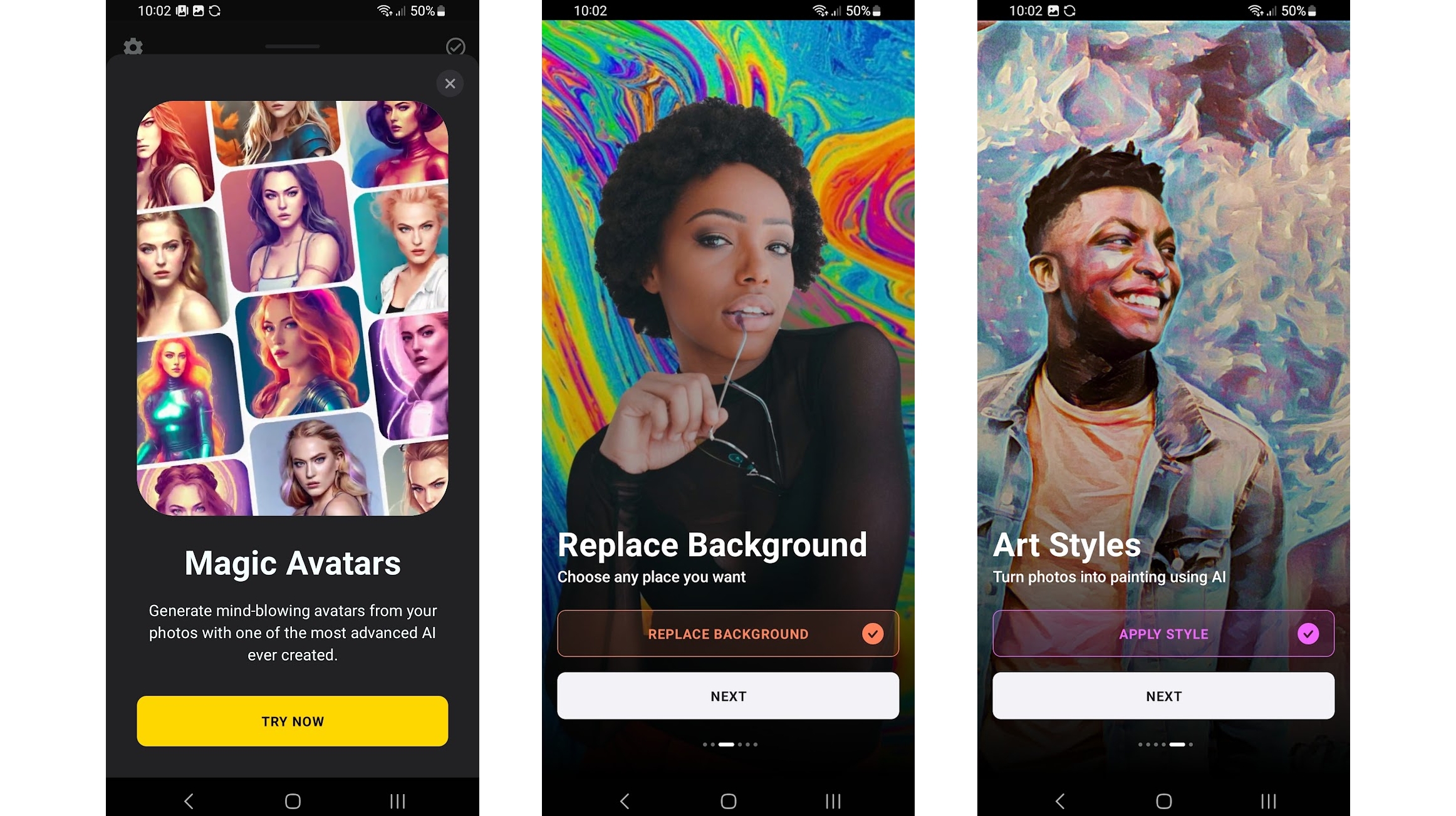
Lensa
Various IAP
Lensa is a controversial AI image app, which you may well have already read about. It’s capable of replacing backgrounds in photos and adding filters, among other things, but what it’s really famous for is creating AI-generated images, based on photos you feed it.
You simply upload 10-20 selfies, and it will return numerous AI takes on them, which have the appearance of digital portraits of you in various scenes, settings and outfits, such as playing a guitar or in a space suit.
These are generally high-quality, though the nature of AI images means they can sometimes look a bit weird or give you an extra arm. There are also questions around privacy and the sexualization of female portraits in the app. So be aware of the risks when going in.
It costs money as well, and its pricing isn’t clearly laid out when you first launch the app. It pushes you towards a subscription, but if you turn that down you’re then offered a batch of images for a one-off price, which for most people is probably the best option.
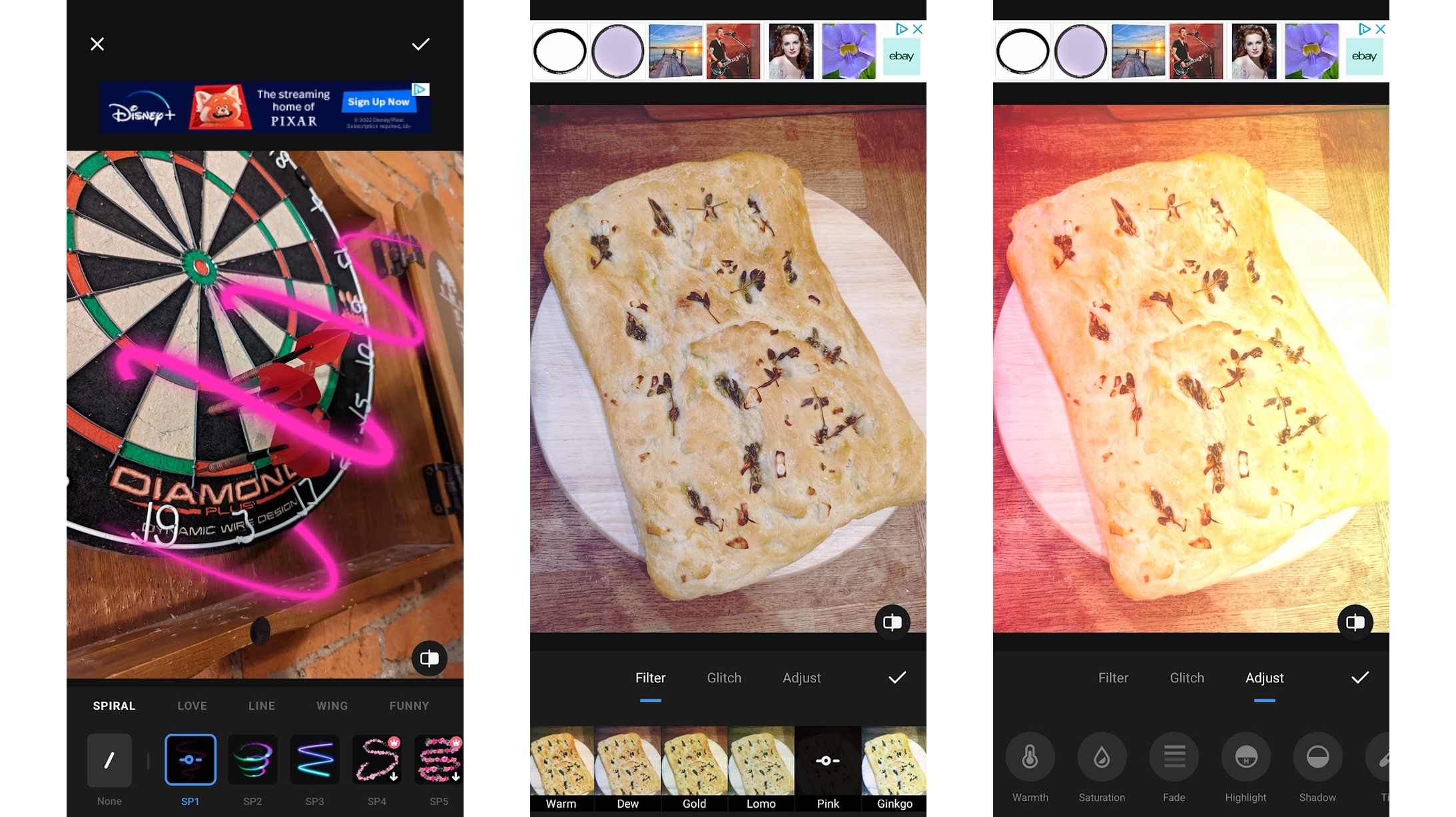
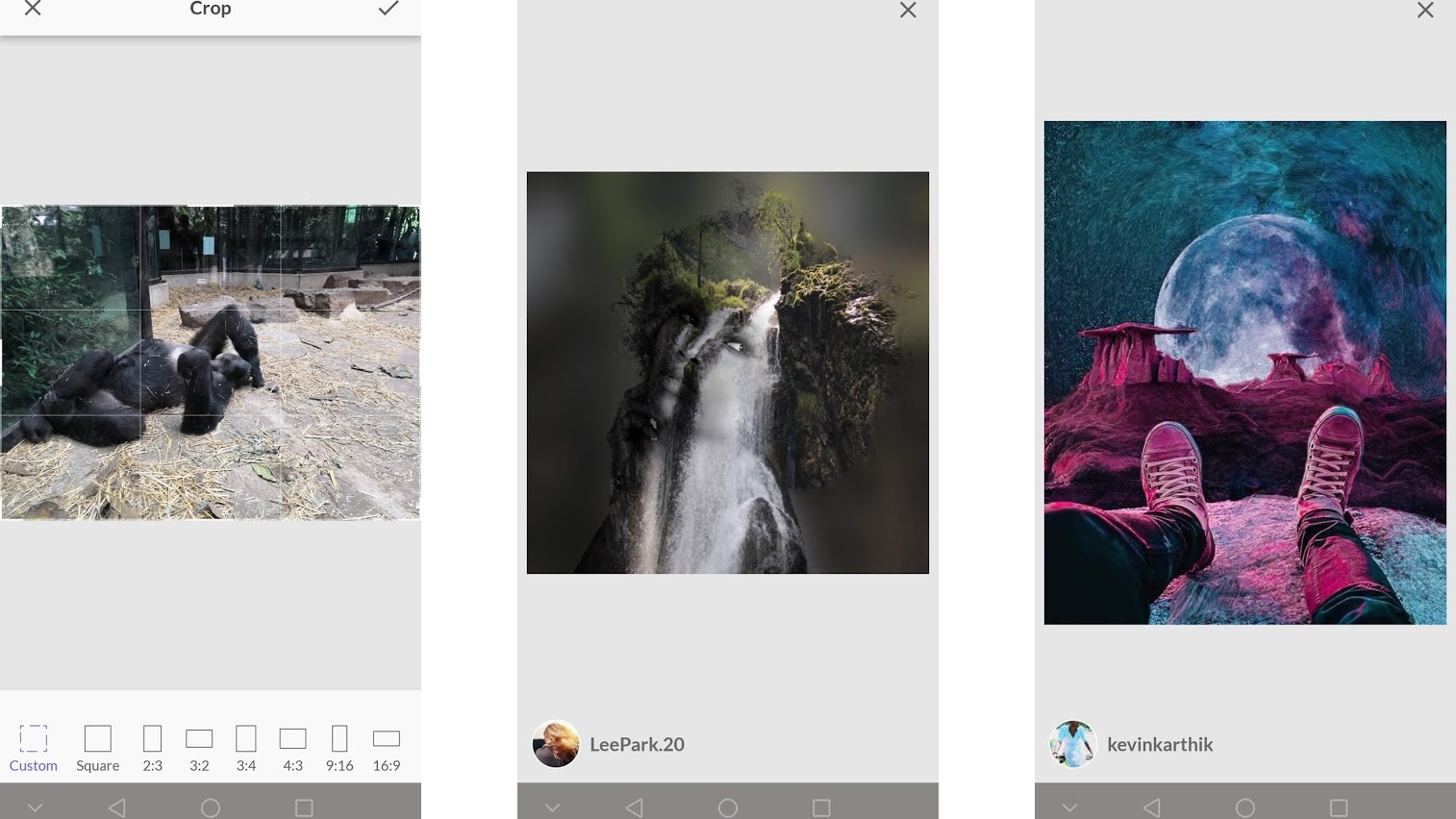
Photo Editor Pro
Free or various IAP
Photo Editor Pro is an extremely powerful photo editor, and one which you can use many of the features for no charge at all.
These features include filters, effects, an object remover similar to the Pixel 7’s Magic Eraser, tools to adjust things like the brightness, saturation and contrast, the ability to add stickers or text, or draw on the image, beautifying tools, and a whole lot more.
The layout is intuitive too, and you can undo any edits with a tap, so it’s easy to fix any errors you make in the editing process.
If you do choose to pay then you’ll get rid of the ads, and unlock even more filters and effects, with more added weekly, plus a few additional features.
The free version of Photo Editor Pro is so generous that you might be disinclined to pay, especially since it’s charged either yearly or as a one-time purchase, which in either case is quite a hefty outlay. But if you do choose to pay then you’ll be upgrading one of the better photo editors on Android to one of the very best.
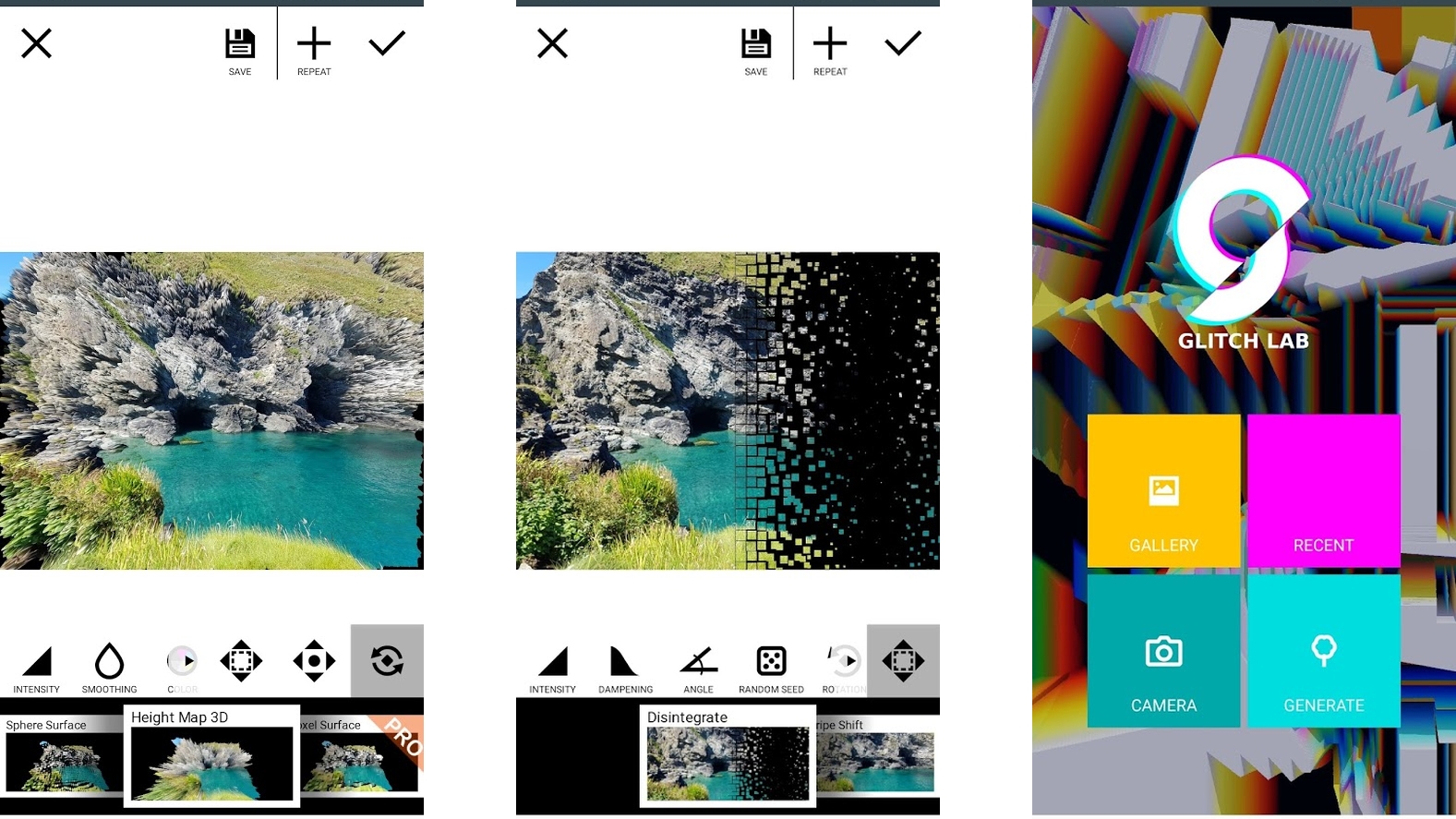
Glitch Lab
Free + $6.49/£5.99 IAP
Glitch Lab is a photo editor packed full of digital glitch effects. You’ve probably seen apps like this before, and the style of effects offered won’t appeal to everyone, but if you like making your pictures look a bit glitchy or retro, this is one of the most capable and versatile ways to do it.
There are over 100 effects in this Android app, and many of them are customizable, ensuring that your glitches won’t look like anyone else’s.
As if to demonstrate the power, it’s even possible to generate an image from scratch, building it up through a number of effects and tweaks.
There’s plenty here even for free, but to get the absolute most out of Glitch Lab you’ll need to grab the Pro IAP for $6.49/£5.99. This, at the time of writing, adds 42 extra effects, 37 new parameters for the free effects, increases the output quality, and more.
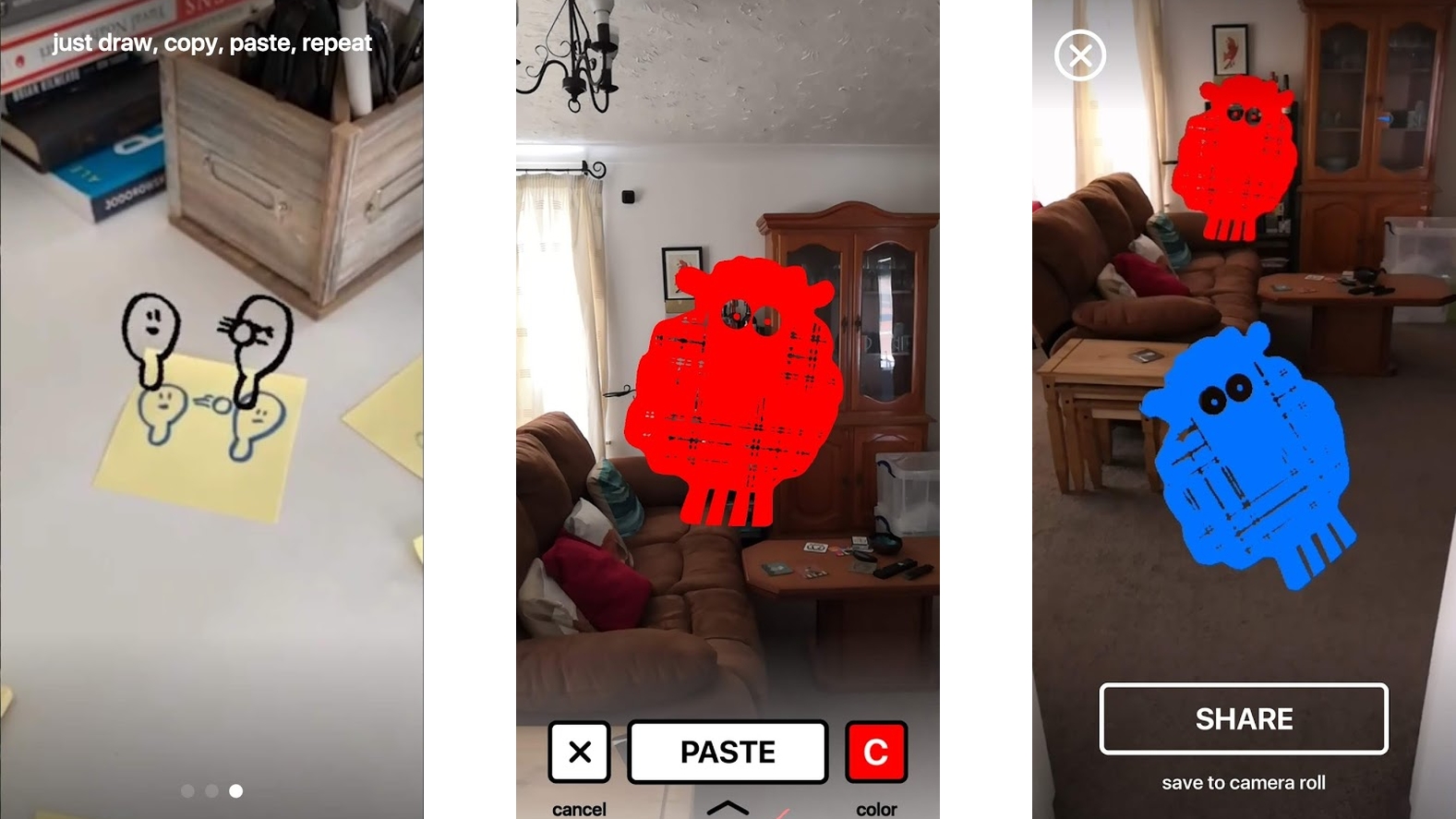
DoodleLens
$1.99/£1.89
DoodleLens is perhaps a bit of a gimmick, but it’s a fun one. Simply doodle something, then point your phone’s camera at the doodle from within the app, and you can copy it and paste it on top of the world around you in augmented reality.
You can also change the color of the doodle and even make very basic animations by copying multiple doodles and having the app cycle through them. You can then record and save the results.
DoodleLens probably isn’t an Android app you’ll use often, and we found it a bit hit and miss at recognizing our doodles, but when it works it raises a smile, which is all you can really ask for at $1.99/£1.89.
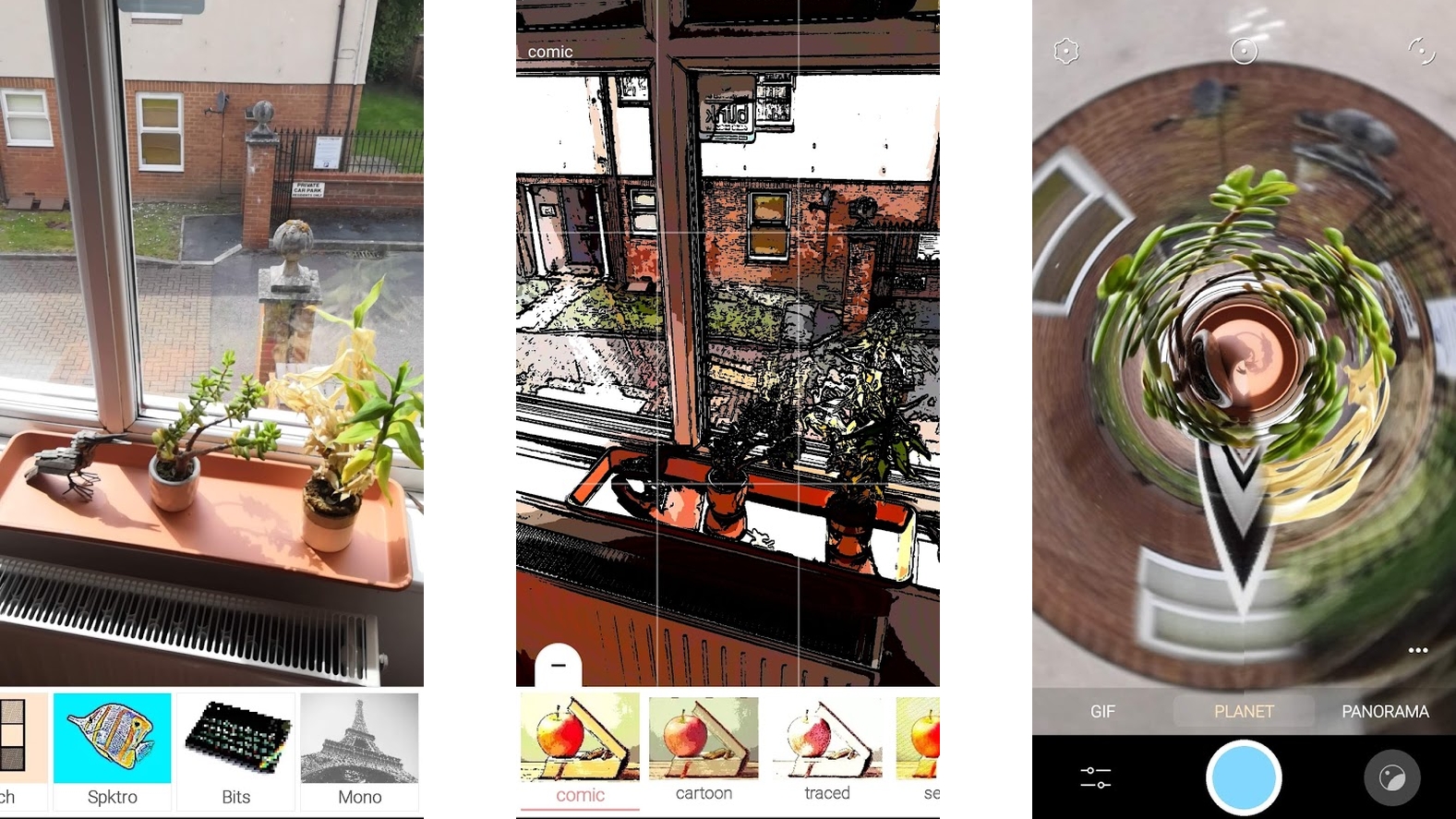
Pixtica
Free + various subscriptions
Pixtica is one of many tools hoping to replace your phone’s default camera app. Camera apps vary a lot, and their success largely depends on your phone make and model, but Pixtica is a decent option if you’re looking for something new.
It’s packed full of features, including numerous filters, a GIF recorder, panorama, hyperlapse, manual controls, and oddities such as a ‘Planet’ mode, which warps images into a sphere-like shape using Pixtica’s “advanced stereographic projection algorithm”.
There are all sorts of other modes too, whether you’re taking photos or shooting video, and the app is laid out intuitively. However, while many of the functions are free, you have to pay to unlock higher resolutions and to remove watermarks when using filters.
The payment gets you other things too, but those are the main things that make the purchase close to essential if you plan to use Pixtica. And that would be fine, except the app opts for a subscription fee (of $1.25/£1.25 for one month with discounts for six months or a year) rather than being available as a one-off purchase. We’re not fans of paying a subscription for a camera app, but if any such app is worth it, it’s Pixtica.
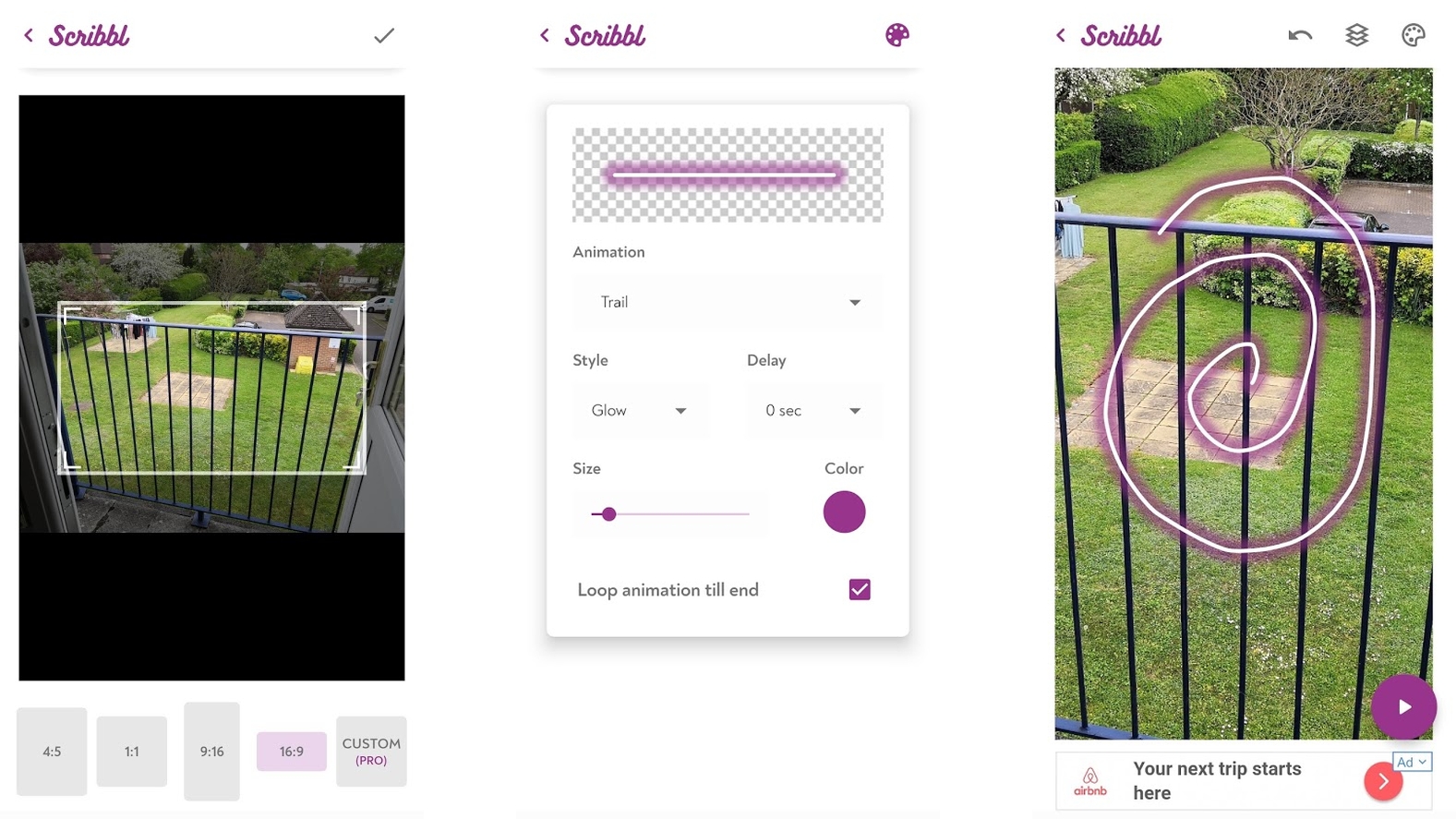
Scribbl
Free + $5.49/£5.49
Scribbl is a photo editor that lets you add animations to your pictures. By ‘animations’ we mean basically light trails, but there are various different ways they can be animated, numerous colors you can choose, and you can pick exactly where they appear on images and how large they are.
Essentially, it’s an app that does one thing but does it quite well. Once you’ve added an animation you can save the result to your phone’s gallery, ready for sharing.
The basic app is free, but for either a one-off fee or a monthly subscription you can remove adverts and unlock additional customization options, as well as unlocking the ability to remove the Scribbl watermark from your creations. If you like the app this is worth paying for, but you can get a good taste of it without spending anything.
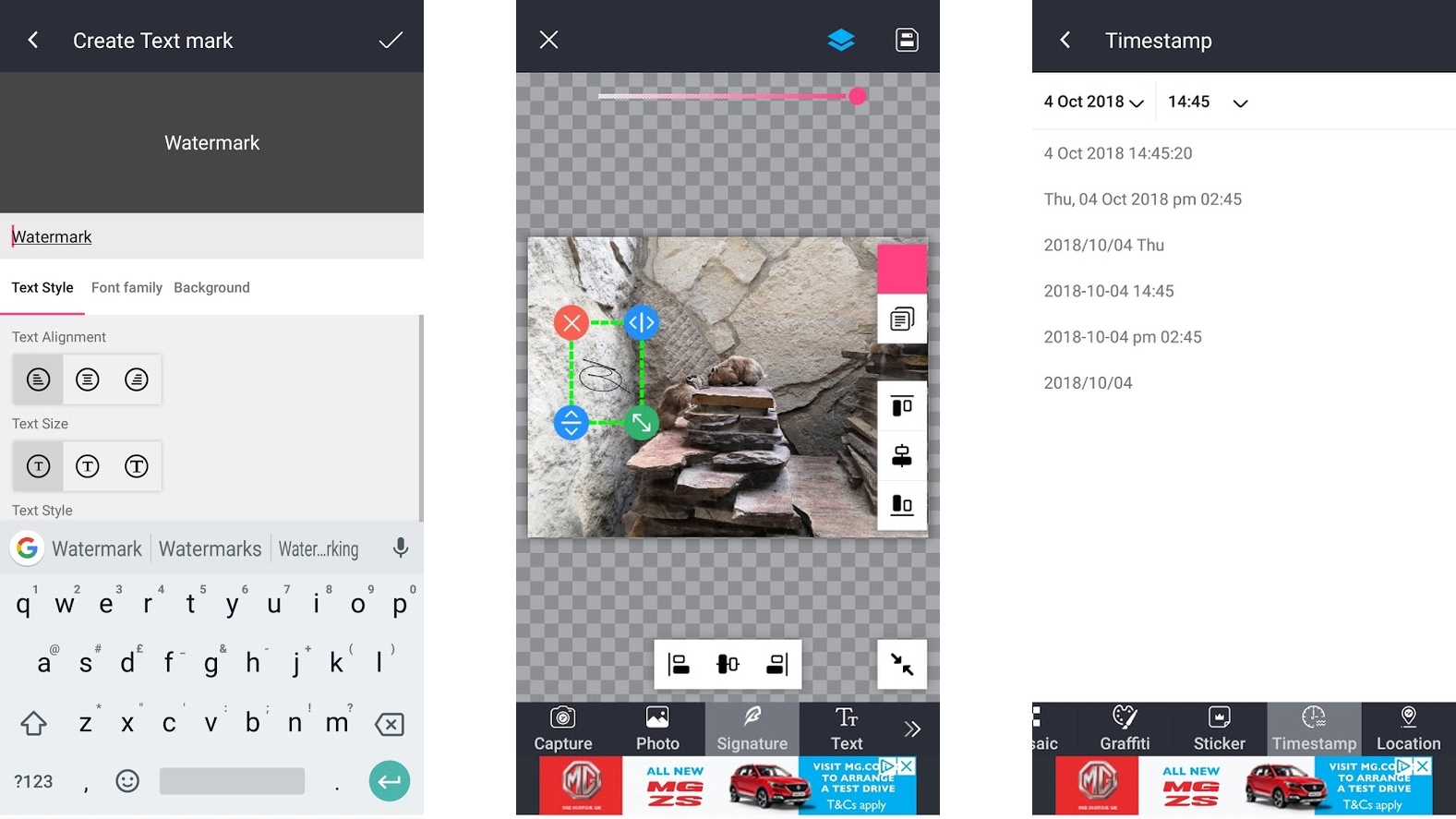
Photo Watermark
Free + $0.99/£0.89 monthly subscription
Photo Watermark does exactly what the name suggests – it lets you add watermarks to photos – but the types of watermarks you can add are quite varied.
Not only can you add custom text as a watermark (including changing the font, size and color), you can also use your signature (or any other hand-written text) as a watermark by writing on the screen.
You can also apply stickers, a timestamp, a location, a mosaic effect, or ‘graffiti’ (which basically just lets you go wild on your images with a digital paintbrush). Whether you want to protect your photo or just log when and where it was taken, there should be a tool here to suit.
Photo Watermark is free, but it’s quite heavy on adverts. For $0.99/£0.89 per month you can get rid of them, but unless you’re adding watermarks to a ton of images it’s probably not worth it.
StoryZ Photo Motion & Cinemagraph
Free + $1.99/£1.79 monthly subscription
StoryZ Photo Motion & Cinemagraph is a photo editing Android app in two parts. The first of these is ‘Ripple’, a mode which lets you add motion to a static image by drawing the area and direction that you want the motion to happen.
This can be an effective way to make it look like water or smoke is moving for example, or simply to add a slightly trippy effect to things that you might expect to be static.
The ‘Motion’ mode, which lets you blend a video with a photo, leaves you with an ‘image’ that’s partially static and partially in motion.
In both cases it can be hard to make the effect look convincing, but it’s doable, as evidenced by all the impressive public submissions shared on the app. StoryZ also holds contests with specific themes, such as ‘stairs’ or ‘sand’, which you can enter by submitting a relevant creation. The best ones will be featured on the home page and competition page of the app.
You can use StoryZ for free, but if you find that you have more of a talent for it than we do then there’s also StoryZ Premium, which for a monthly subscription removes adverts and watermarks, increases the allowable length of videos in Motion mode, improves the toolset in Ripple mode and lets you save and share in high resolution.
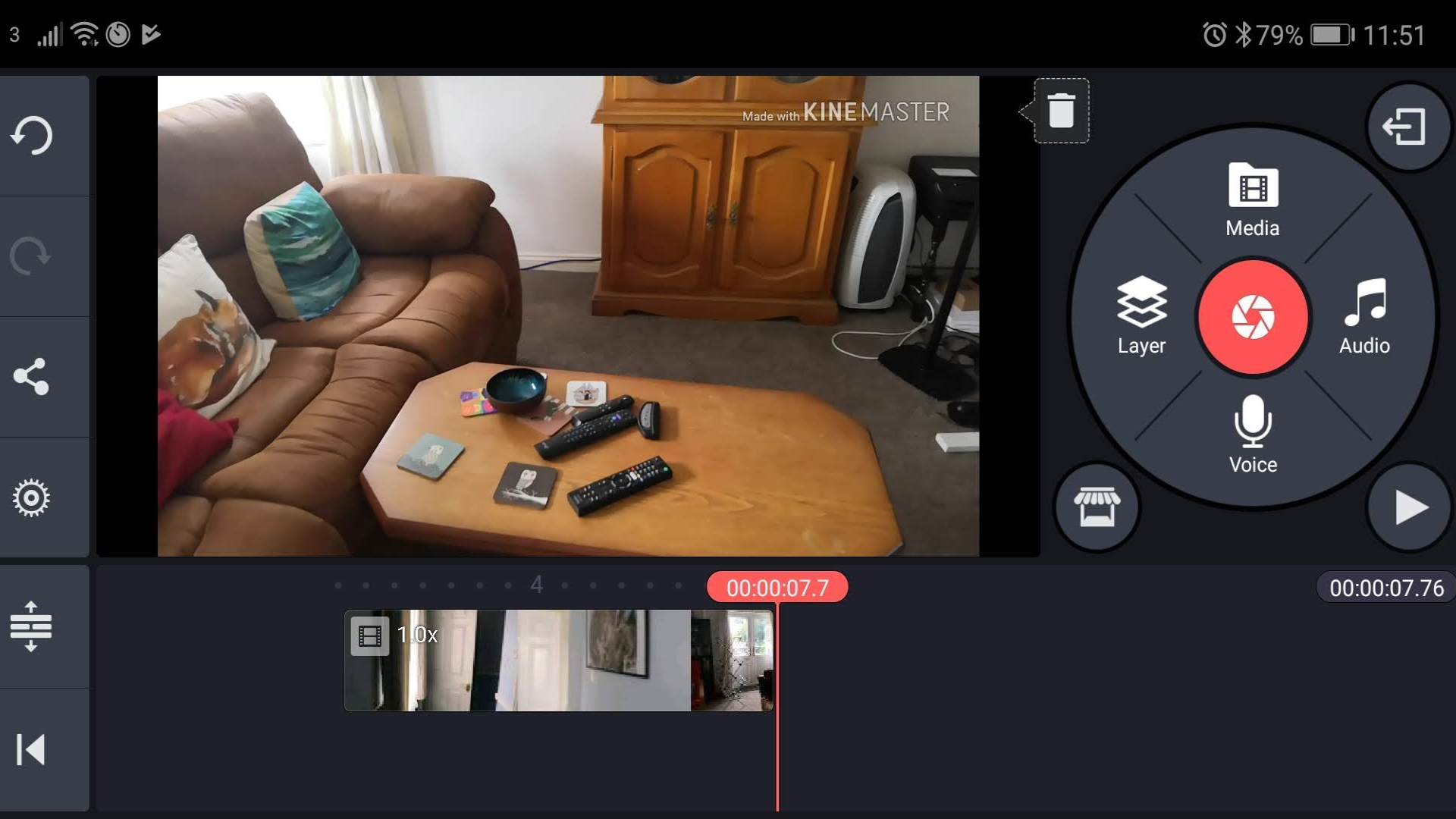
KineMaster
Free + £2.91 (roughly $3.70) monthly subscription
KineMaster is probably one of the most powerful video editors on Android, but it’s also intuitive enough that anyone could enjoy using it.
The app lets you add audio and visual filters to footage, add text, stickers and other overlays, alter and trim videos frame-by-frame, adjust the speed, add transition effects and a whole lot more. You can also record videos straight from the KineMaster app. It can feel a little cramped on a phone screen, but otherwise everything works well.
You can use the KineMaster Android app for free, but all your videos will have a KineMaster watermark and you can’t use them commercially. To remove the watermarks, allow commercial use and unlock additional assets (such as effects and overlays) you have to pay a subscription, but at £2.91 (roughly $3.70) per month it remains affordable.
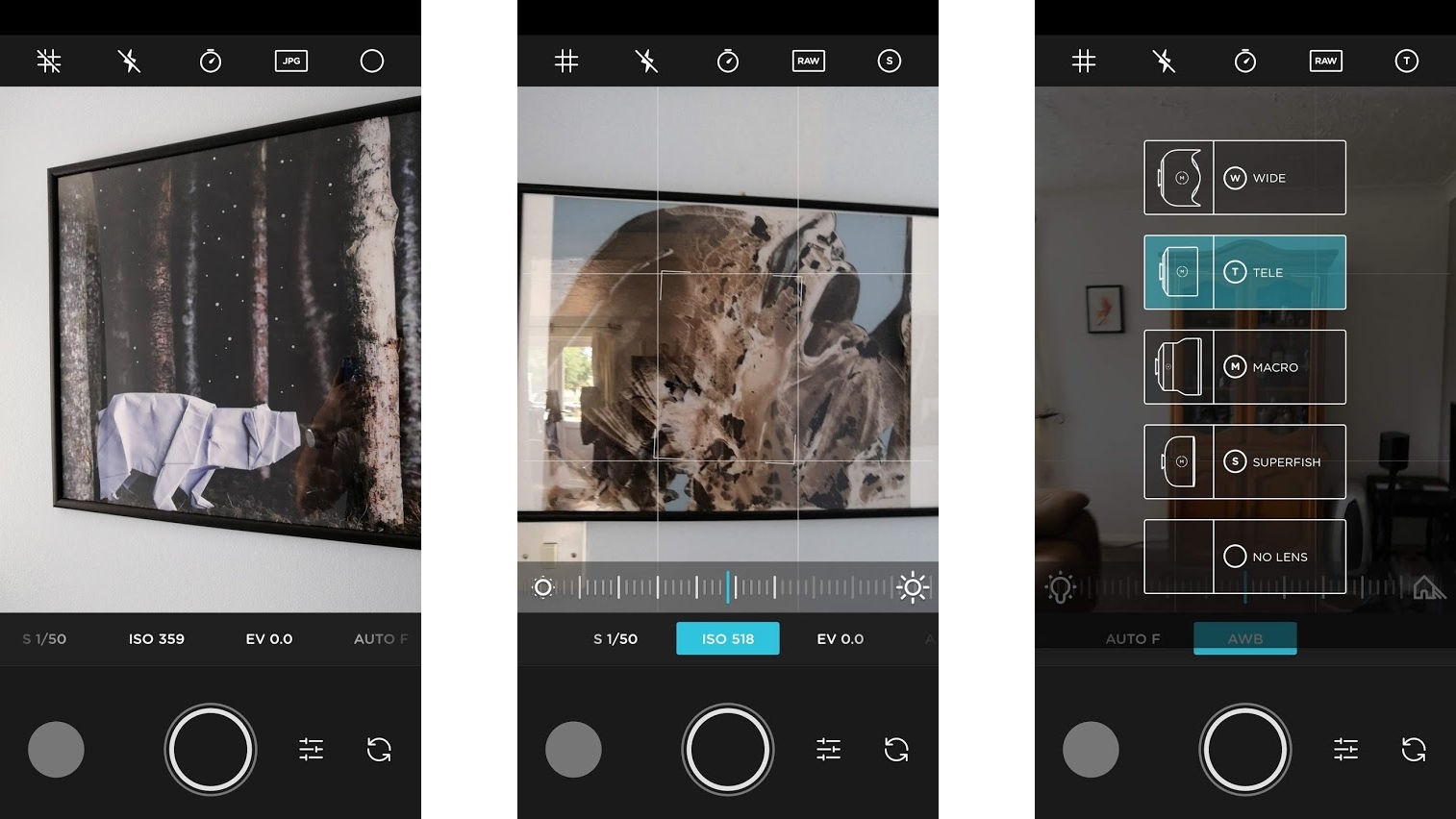
Moment – Pro Camera
$1.99/£1.79
A truly great camera app arguably needs to both avoid clutter and be packed full of manual controls, so you can capture an image exactly as you want it, but that’s a tough balance to strike, and few manage. Moment – Pro Cameraarguably does though.
It gives you full manual control, including RAW shooting, shutter speed, ISO, white balance, exposure compensation and focus. There’s also tap to focus, a timer, a grid and several different lenses. It’s an impressive toolkit, with the app focusing more on powerful utilities than gimmicky filters, but it all has a very clean, minimalist look.
And it’s designed with ease of use in mind. You can double tap any setting to return it to auto or double tap the viewfinder to turn everything back to auto and all the controls are within easy reach.
The main downside of this Android app is that it can’t currently shoot videos, but for photos there’s a good chance you’ll want to replace your current camera app with this, and video is apparently in the works.
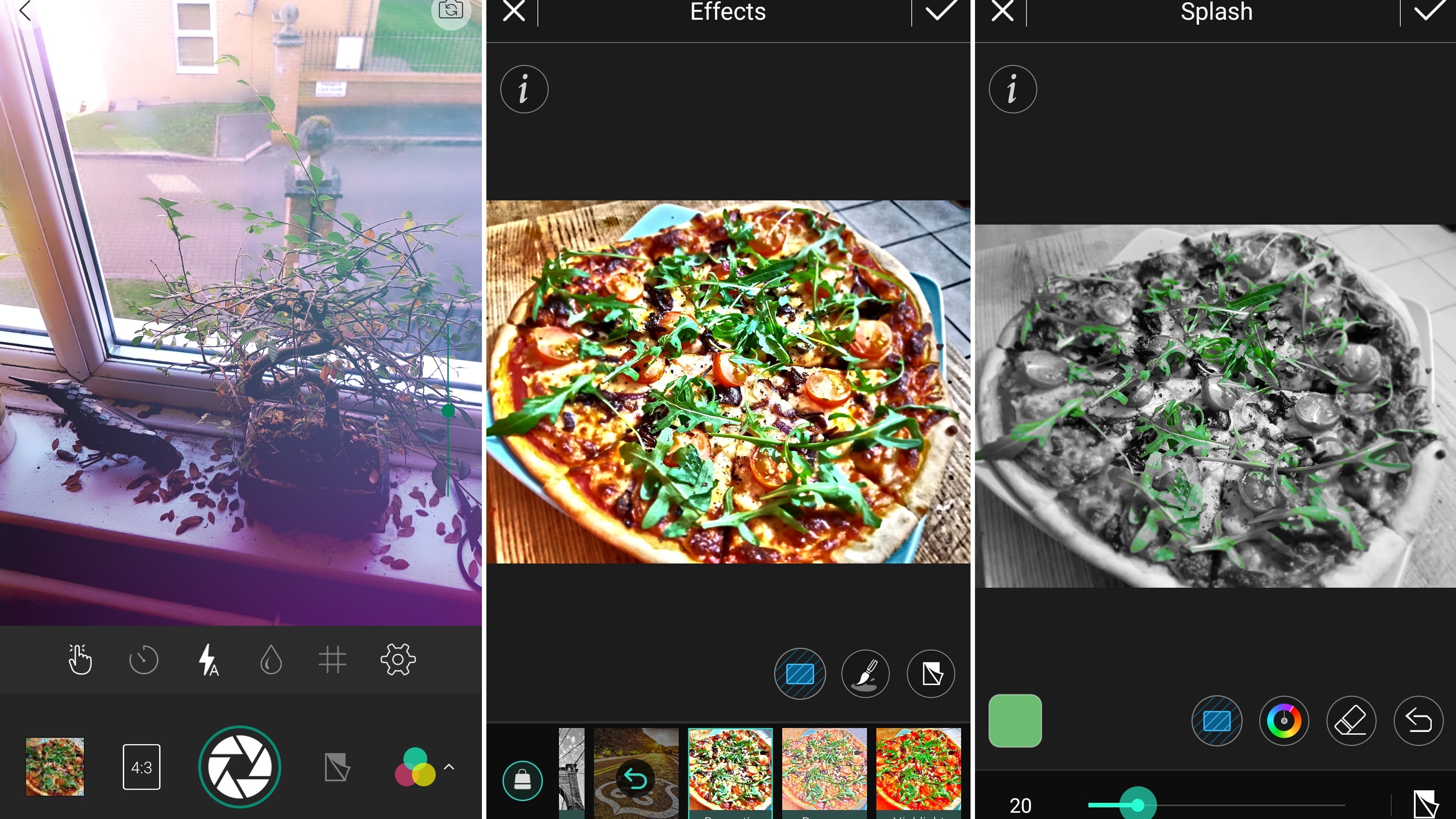
PhotoDirector
Free + optional subscription
Your phone might have a powerful camera, but chances are it doesn’t come with much in the way of photo editing tools. Fortunately, PhotoDirector is an Android app can fill in the gaps.
This app lets you adjust the tone, saturation, white balance and colors of photos you’ve previously taken, as well as adding filters and effects, which you can adjust the strength of and apply to all or just part of an image.
You can also add text, stickers, frames, change the perspective, mirror the image, cut sections and a whole lot more.
There are lots of tools, but PhotoDirector is easy to navigate and you can always undo your changes, so you’re safe to experiment.
And that’s just the editing part of the app. There’s also a built-in camera, which lets you shoot new photos with various effects and see live through the viewfinder how they will affect the image.
PhotoDirector is largely free, but if you want to direct to your best there’s a premium version that costs £2.59 (around US$3.70) per month, with discounts if you commit for three months or a year. This unlocks additional tools, boosts the output quality and removes adverts.
- These are the best photo editing apps you can download right now
Current page: Best new app / best Android camera apps and photo editors
Next Page The best art and design apps for AndroidSign up for breaking news, reviews, opinion, top tech deals, and more.
James is a freelance phones, tablets and wearables writer and sub-editor at TechRadar. He has a love for everything ‘smart’, from watches to lights, and can often be found arguing with AI assistants or drowning in the latest apps. James also contributes to 3G.co.uk, 4G.co.uk and 5G.co.uk and has written for T3, Digital Camera World, Clarity Media and others, with work on the web, in print and on TV.