QR code phishing surges 146% as Microsoft detects and analyzes 8.3 billion phishing threats in Q1 2026 – attackers are changing tactics to bypass security
Security tools are struggling against quishing-based attacks

- Microsoft detected 8.3 billion phishing emails in Q1 2026
- Attackers are favoring QR-code based attacks
- PhaaS group Tycoon2FA saw a drop in attacks following disruption, but is rehosting infrastructure elsewhere
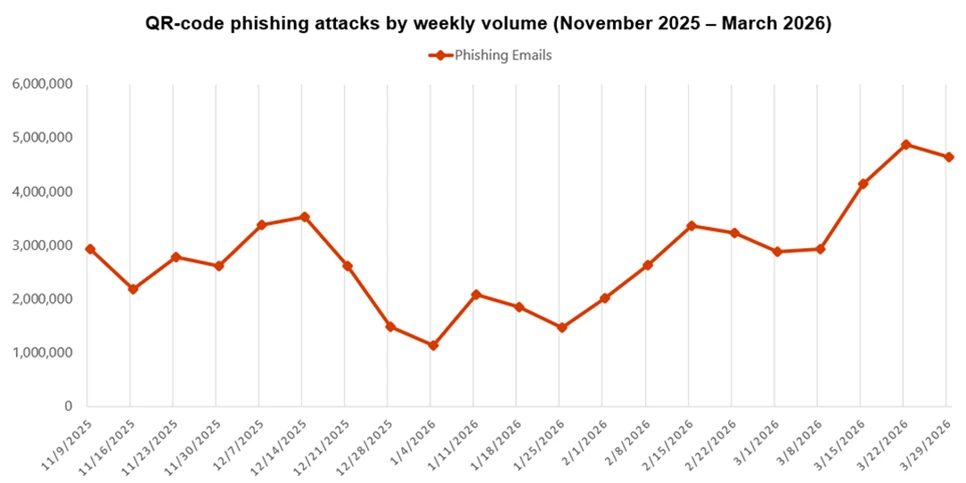
Microsoft has warned of a 146% rise in QR code phishing (quishing) as attackers change tactics to get through defenses.
These stats come from Microsoft’s latest Email threat landscape report, generated after analyzing over 8.3 billion email-based phishing threats in Q1 2026.
Other than the notable shift in tactics, Microsoft has also warned of increases in business email compromise (BEC), CAPTCHA pages to avoid detection, and credential phishing malicious payloads.
Article continues below8.3 billion reasons to enhance your security
While the overall volume of monthly phishing threats fluctuated between January and March, Microsoft noted a clear shift in tactics throughout Q1 2026.
Attackers have adapted to improved defender security by increasing phishing attacks via QR codes, with quishing attacks reaching their highest point in the last year.
While scan-based security defenses can quickly identify the typical text-based phishing attempts, they struggle to handle embedded QR-codes.
Moreover, the recipient of a QR-code-based attack is likely to use a mobile device to scan the code, taking the victim out of the protected environment on their workstation and thereby bypassing enterprise security tools - especially if they use a personal mobile device.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
Attackers are also shifting tactics in terms of how they deliver QR codes to their victims. While PDF files were the preferred delivery method throughout Q1, there was a 336% surge in March of QR codes being delivered directly in emails, avoiding the need for attachments altogether.
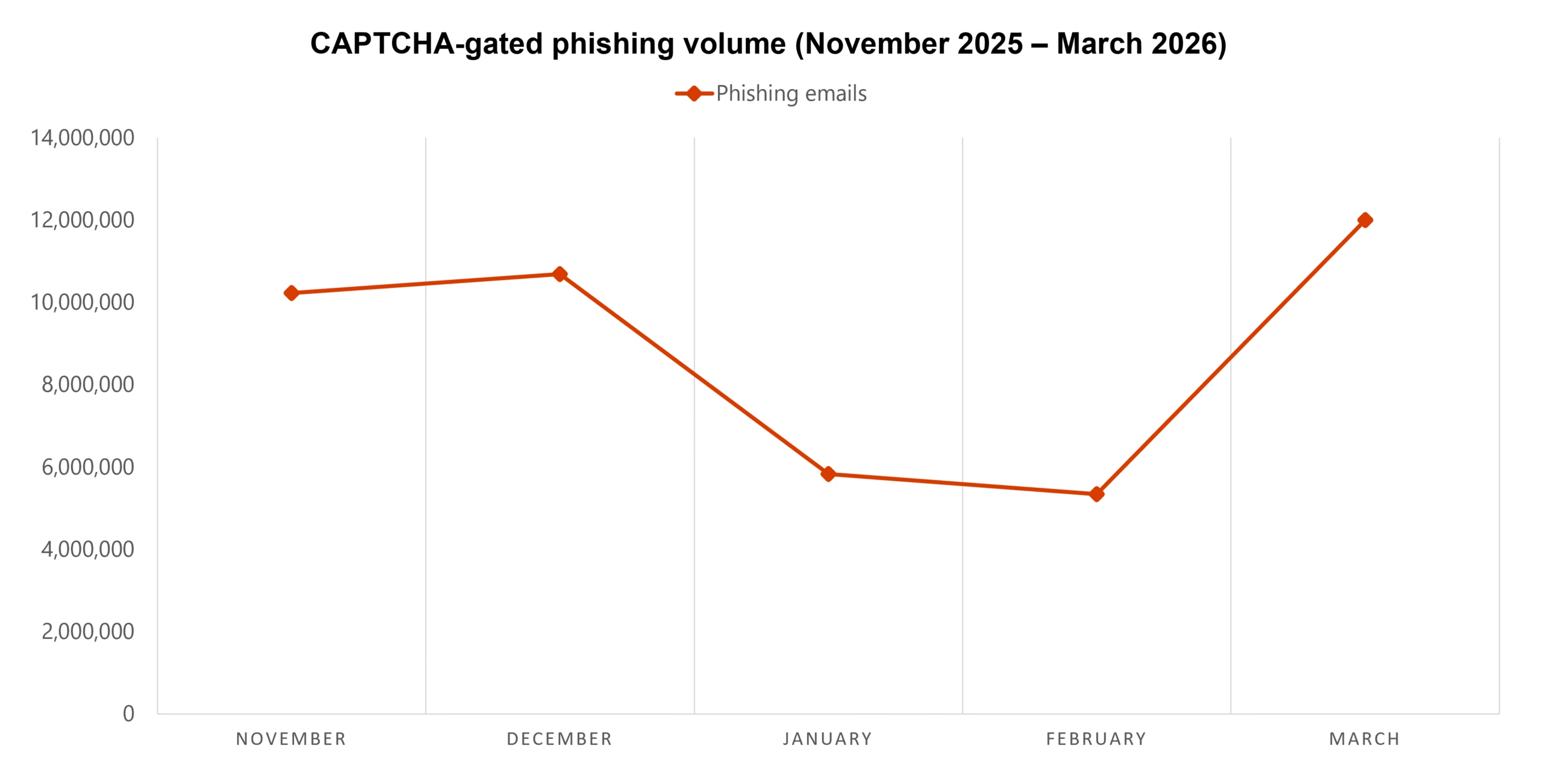
Microsoft recorded a downward trend in CAPTCHA-based attacks in the first two months of Q1, before attempts exploded by more than 125% in March.
CAPTCHA pages help attackers avoid detection by forcing victims to interact with the page before accessing the final payload. In some cases, the attackers use the CAPTCHA page to deliver the payload by having the victim believe they are verifying the CAPTCHA, but instead are copying and executing malicious commands.
Microsoft noted that attackers using the CAPTCHA method don’t seem to have a single preferred delivery mechanism for the payload, with groups experimenting in the use of HTML attachments, SVG files, PDF files, DOC/DOCX files, and Email-embedded URLs.
The joint Microsoft/Europol disruption of the Tycoon2FA phishing-as-a-service (PhaaS) group in March contributed to a marked 15% decline in attacks utilizing the groups chosen methods, however the disruption is unlikely to be permanent as the group changes its infrastructure to be hosted on second-level domains such as .RU. To that end, Microsoft has already seen 41% of all Tycoon2FA domains using a .RU TLD since the last week of March.
As for business emails, Microsoft highlighted that it detected 10.7 million phishing threats directed towards business emails, with attackers showing a clear preference for lure-based phishing emails. These emails typically include a generic message such as “Are you at your desk?” to establish a conversation with the recipient before delivering the payload.
Attackers are also moving away from targeting business emails with requests for gift cards, and instead took advantage of tax season to send payroll update requests, with this attack vector growing by 15% in February.
In order to protect against phishing attacks, Microsoft recommends taking the following actions:
- Check Exchange Online Protection and Microsoft Defender for Office 365 settings to ensure the recommended settings are turned on
- Provide phishing simulation training to employees
- If using Defender for Office 365, enable Zero-hour auto purge (ZAP)
- Enable safe links in Microsoft Defender for Office 365
- Enable network protection Microsoft Defender for Endpoint
- Use phishing-resistant multi-factor authentication (MFA) such as FIDO2 keys or biometric authentication.

➡️ Read our full guide to the best antivirus
1. Best overall:
Bitdefender Total Security
2. Best for families:
Norton 360 with LifeLock
3. Best for mobile:
McAfee Mobile Security

Follow TechRadar on Google News and add us as a preferred source to get our expert news, reviews, and opinion in your feeds.

Benedict is a Senior Security Writer at TechRadar Pro, where he has specialized in covering the intersection of geopolitics, cyber-warfare, and business security.
Benedict provides detailed analysis on state-sponsored threat actors, APT groups, and the protection of critical national infrastructure, with his reporting bridging the gap between technical threat intelligence and B2B security strategy.
Benedict holds an MA (Distinction) in Security, Intelligence, and Diplomacy from the University of Buckingham Centre for Security and Intelligence Studies (BUCSIS), with his specialization providing him with a robust academic framework for deconstructing complex international conflicts and intelligence operations, and the ability to translate intricate security data into actionable insights.
You must confirm your public display name before commenting
Please logout and then login again, you will then be prompted to enter your display name.

 Become a TechRadar Insider
Become a TechRadar Insider






