Researchers discover new all-in-one ‘Bluekit’ phishing kit capable of bypassing enterprise 2FA protocols and emulating 40+ global brands
Bluekit offers phishing-as-a-service with a twist
- Researchers have discovered a complex new phishing kit
- Bluekit offers phishing in a software-as-a-service package
- An entire campaign can be centralized and automated, and assisted by AI
Bluekit is a new phishing kit uncovered by Varonis Threat Labs researchers, who reviewed the kit first hand to explore its capabilities.
The phishing kit has a broad range of dangerous capabilities, including the ability to mimic over 40 well-known brands, geolocation emulation, and an AI-assistant to walk you through an attack.
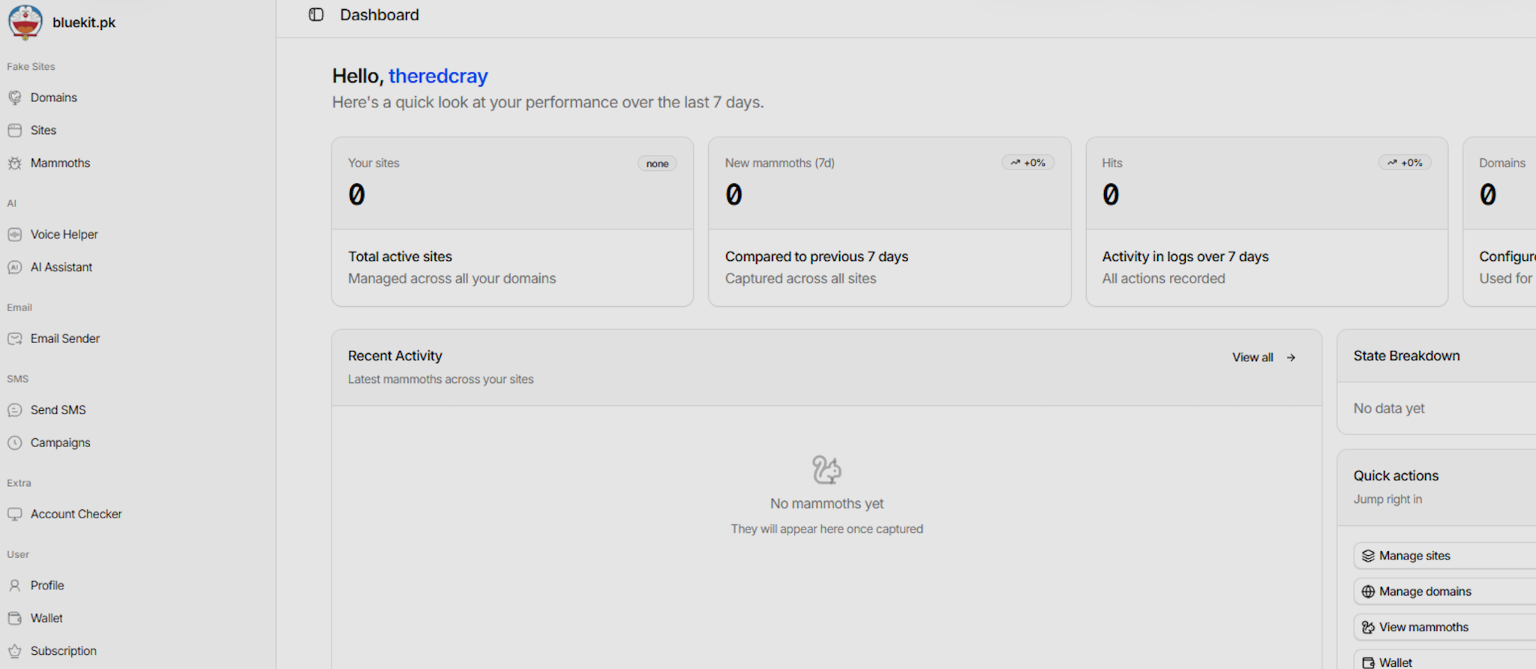
Bluekit is highly professionalized, and offers attackers a sophisticated all-in-one dashboard for launching a phishing campaign.
Article continues belowBluekit streamlines cybercrime
Rather than congregating each component for a phishing attack from different vendors, Bluekit acts in a similar way to a software-as-a-service platform, with a dashboard that centralizes and automates phishing workflows, significantly reducing the barrier for entry to potentially devastating phishing attacks.
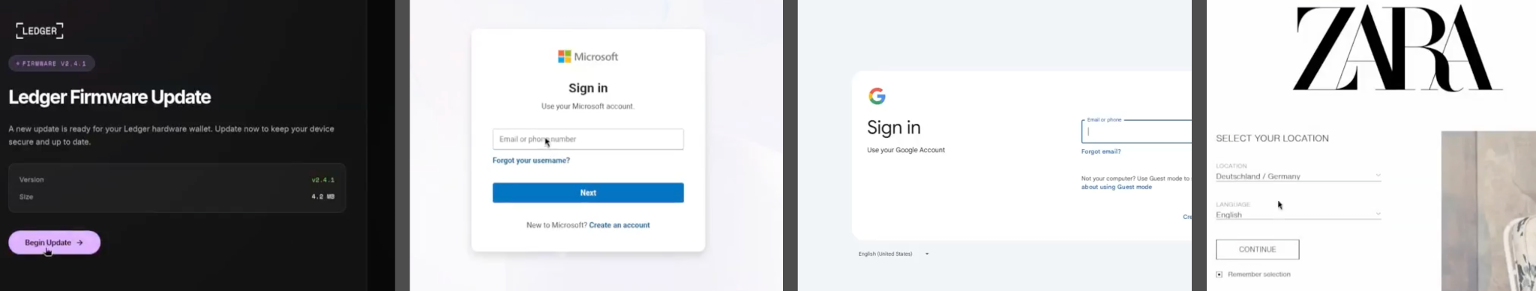
Bluekit handles domain registration, site hosting, and data exfiltration on a single panel, and offers emulation of popular global platforms, including iCloud, Apple ID, Gmail, Outlook, Hotmail, Yahoo, ProtonMail, GitHub, Twitter, Zoho, Zara, and Ledger. Offering such a wide range of targets allows attackers to quickly pivot between targets, run recognizable but local campaigns, and even run attacks simultaneously.
The platform also integrates the Telegram messaging app to offer real-time alerts on successful exfiltration.
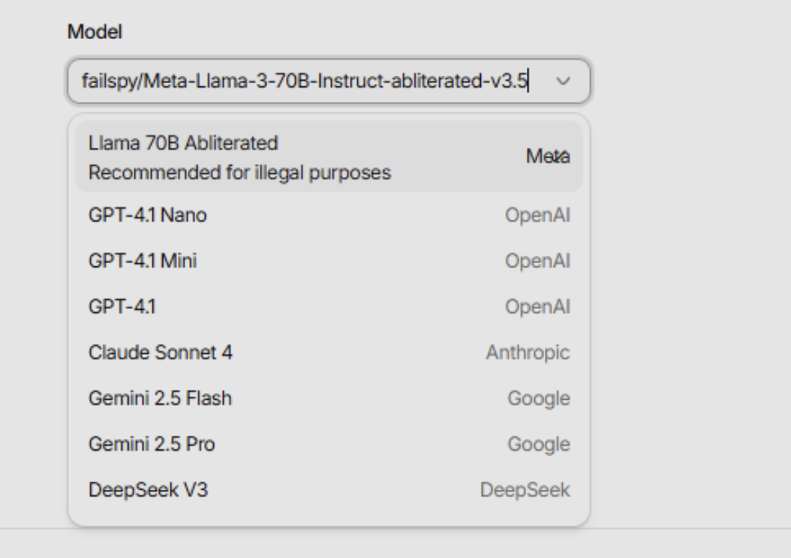
Varonis also explored the platforms’ AI assistant, which they say could be potentially jailbroken variants of Llama, GPT-4.1, Sonnet 4, Gemini, and DeepSeek. In testing, the AI agent was capable of drafting “skeleton” phishing emails that required little modification in order to create convincing localized lures. Typically, an official AI model would reject any attempts to draft a phishing email, but by using jailbroken versions these guardrails are removed.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
In order to harvest credentials, Bluekit is capable of hijacking sessions and extracting cookies, allowing the attacker to bypass multi-factor authentication (MFA) protocols by using the stolen active browser session to mimic the authenticated user. The platform also allows the attacker to see a live-feed of the target’s screen after they log in and navigate the fake page.
In order for the automated attack to avoid detection, Bluekit also includes features that allow it to cloak itself to avoid bot-detection tools, and can prevent analysis checks by preventing site access to headless user agents, headless resolutions, bad fingerprints, proxies and virtual private networks (VPNs). Device access can also be filtered to desktop or mobile only.
For some platforms, a login from an unusual location can trigger an alert to the user with steps to secure their account. In order to prevent these notifications, Bluekit’s location emulation abilities can make the login appear to be from a normal location.
During their testing, the researchers noted that Bluekit is being actively updated with new features, rapidly expanding its abilities and making the kit an increasingly potent tool for attackers. “The feature set keeps evolving as we track it, and if that pace continues with broader adoption, Bluekit is likely to surface in future campaigns,” the researchers said.
As AI is lowering the barrier for entry into cybercrime, so too are all-in-one attacking platforms such as Bluekit.
In order to better resist these evolving threats, businesses should adopt FIDO2 or Hardware keys for authentication, which often verify a user using biometric authentication via a recognized device in a pre-verified environment, making them much more resistant to location-spoofed login attempts. Employee training is also one of the most effective ways to prevent phishing attacks. By regularly simulating phishing emails, employees become much more vigilant and capable of recognizing suspicious emails.

➡️ Read our full guide to the best antivirus
1. Best overall:
Bitdefender Total Security
2. Best for families:
Norton 360 with LifeLock
3. Best for mobile:
McAfee Mobile Security

Follow TechRadar on Google News and add us as a preferred source to get our expert news, reviews, and opinion in your feeds.

Benedict is a Senior Security Writer at TechRadar Pro, where he has specialized in covering the intersection of geopolitics, cyber-warfare, and business security.
Benedict provides detailed analysis on state-sponsored threat actors, APT groups, and the protection of critical national infrastructure, with his reporting bridging the gap between technical threat intelligence and B2B security strategy.
Benedict holds an MA (Distinction) in Security, Intelligence, and Diplomacy from the University of Buckingham Centre for Security and Intelligence Studies (BUCSIS), with his specialization providing him with a robust academic framework for deconstructing complex international conflicts and intelligence operations, and the ability to translate intricate security data into actionable insights.
You must confirm your public display name before commenting
Please logout and then login again, you will then be prompted to enter your display name.

 Become a TechRadar Insider
Become a TechRadar Insider






