How to lock your PC with a USB drive
Secure your PC quickly when you have to walk away from it
Sign up for breaking news, reviews, opinion, top tech deals, and more.
You are now subscribed
Your newsletter sign-up was successful
Part 1: Activating the Predator…
1. Get Predator
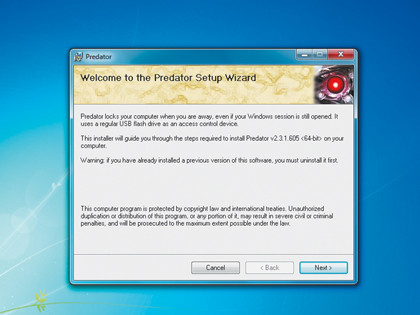
Download Predator from the website. The two editions are available for 32-bit and 64-bit versions of Windows XP, Windows Vista, Windows 7, Server 2003 and Server 2008.
2. Plug in USB
Article continues below 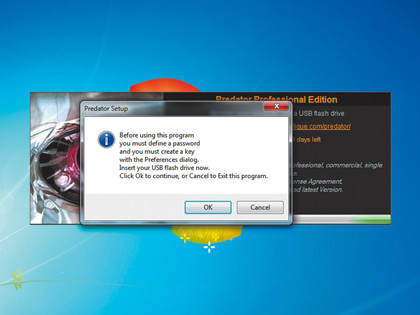
Install the software on the PC you want to protect. Once it's installed, Predator prompts you to insert a USB key before you launch it for the first time. You are then asked to enter a password.
3. Create key
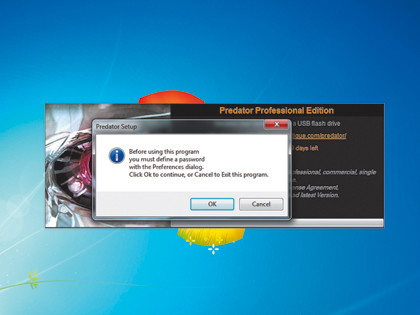
Once you've entered a suitable password, you'll see the Preferences window. Make sure that Predator points to your USB drive correctly in the 'Flash drives' section, then click 'Create key'.
Part 2: Maintaining the Predator
4. Remove to lock
Sign up for breaking news, reviews, opinion, top tech deals, and more.
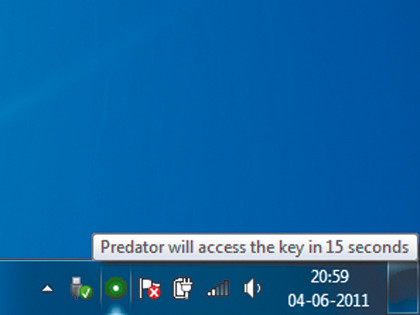
After the Predator key has been created, Predator will periodically monitor whether it's plugged in or not. To lock the computer remove the key when the green icon is flashing.
5. Check log
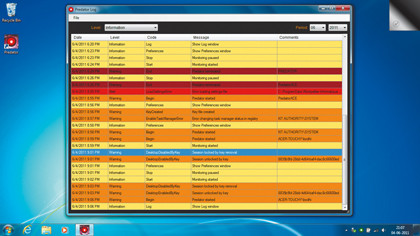
By default, Predator is configured to launch the log viewer if it notices an unsuccessful login attempt has been made while the USB key was removed and the session was locked.
6. Tweak settings
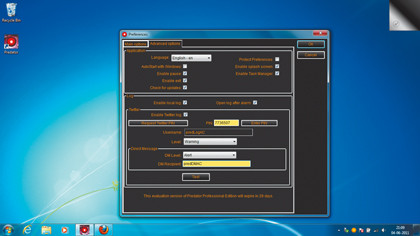
Predator's default settings will suit most users, but it has a comprehensive set of options to give you better control over its monitoring and reporting abilities, depending on how paranoid you are about security.

With almost two decades of writing and reporting on Linux, Mayank Sharma would like everyone to think he’s TechRadar Pro’s expert on the topic. Of course, he’s just as interested in other computing topics, particularly cybersecurity, cloud, containers, and coding.