1. Laptop protection
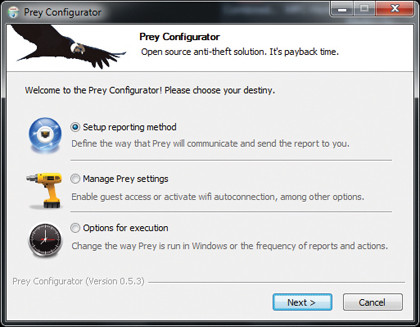
Prey works on a centralised service basis. It's installed on multiple devices and managed via its web control panel. There's an alternative mode but we'll choose this option. Download the laptop client from preyproject.com, install it, choose Prey + Control Panel and create a new user name with password.
2. Control Panel

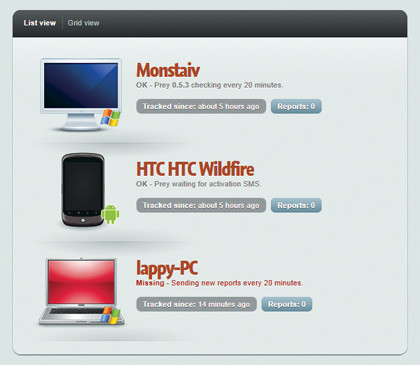
Log into the preyproject.com website and you'll have access to the Control Panel. The opening page shows you all the devices you have registered. The free service has a limit of three, with 10 reports, but that's enough to provide security. Click the icon to confi gure this further.
3. You are the Quarry
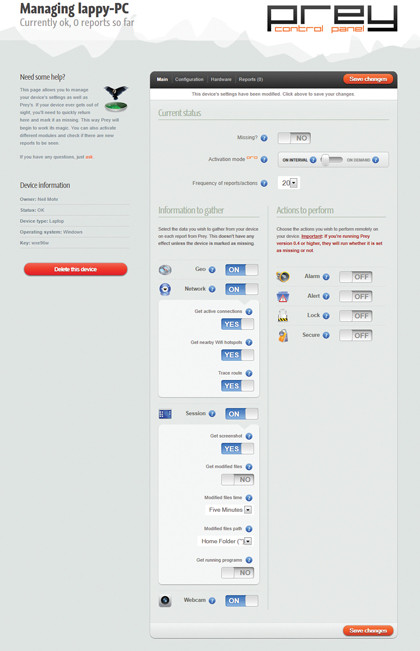
The main page is where you can set all the juicy bits. Geo and Networking enables you to pin down a rough locality for the device; the Session section will take screenshots of activity and monitor files; while the webcam will grab images of the perp.
4. It's gone
Sign up for breaking news, reviews, opinion, top tech deals, and more.
If a device is lost, setting the Missing switch to On will send an email to you the instant the Prey system detects the device is online and is in a state it has been able to run the client-side Prey app. The default setting sends updates every 20 minutes.
5. We've got one!
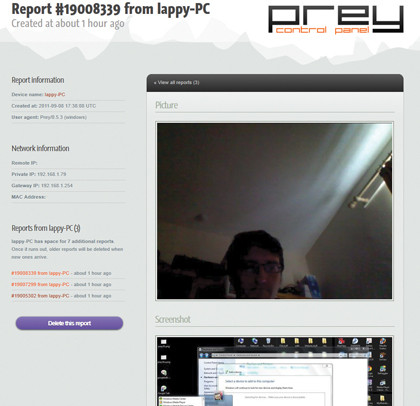
So how did it do? We initially had problems getting the webcam to work but it finally activated, was taking screengrabs and logging IP traces. It'd be better if it took targeted grabs and browser log-ins but it's certainly a very good step in the right direction.
6. Mobile protection
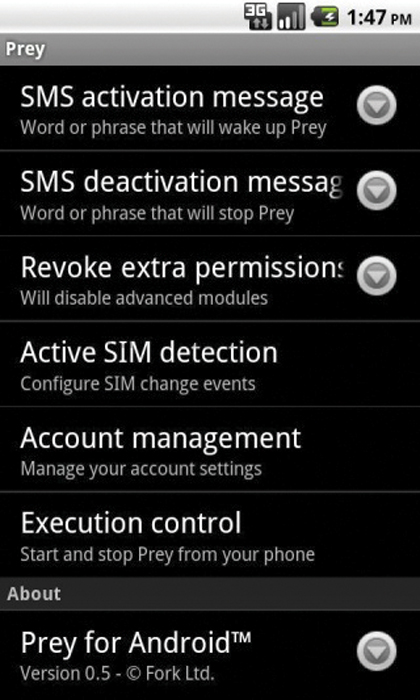
Prey works on more than just PCs, Macs or Linux: it also supports Android devices, including phones and tablets. A version for iOS devices, such as the iPhone, is apparently in the works. Phone devices are activated and controlled via SMS and it can play a loud sound if you've misplaced them.
- 1
- 2
Current page: How to track a stolen laptop with Prey
Prev Page How to protect your laptop from data theft
 Become a TechRadar Insider
Become a TechRadar Insider







