How Linux can help you protect your privacy online
The Web is the greatest system for sharing information but how do you stop it sharing too much?
Sign up for breaking news, reviews, opinion, top tech deals, and more.
You are now subscribed
Your newsletter sign-up was successful
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
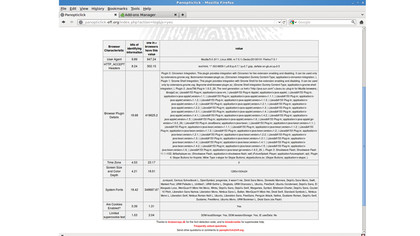
There is one, slightly more devious, technique that websites can use to identify you. This is by amalgamating all information about the capabilities of your browser and system into a digital fingerprint.
Because of the amount of information that your browser will, if asked, reveal about you, this fingerprint can often be used to uniquely identify you to a site. Once again, the EFF is active in this area, and hosts a website to help you understand what your fingerprint is.
Point your browser to panopticlick.eff.org to see how unique you are. At the time of writing, more than two million people had used the site to check their browsers, and we still found that most of our machines could be uniquely identified. This means any website could track us even without cookies, LSOs or any of the other storage techniques.
Article continues belowAt the moment, this is a theoretical vulnerability, and there have been no known cases of browser fingerprinting in the wild. If you're concerned about being tracked this way, the best way to prevent it is to stop scripts from running. This reduces massively the amount of information that a website can use to form the fingerprint.
The NoScript extension for Firefox provides an easy way to control which scripts run on a site. However, this will severely limit the function of many interactive websites. Web pages are made up of a number of different elements that your browser reassembles to make a single document. These elements may come from many different places, organisations and servers.
Any of these could contain some degree of monitoring using a technique called web bugging (also known as web beacons or pixel tags). These use images to generate HTTP requests that log your activities with a different server to one hosting the website. These potentially could be able to track you using browser fingerprinting, but they're also used more widely. They're not restricted to web pages, and can be used in any HTML document.
Most commonly, they're used by spammers to identify active email addresses. If you open an email containing one of these images, the spammer will be able to identify that you're checking the address, and can be persuaded to open spam emails. Fortunately, most email clients and web mail providers disable image loading by default.
Sign up for breaking news, reviews, opinion, top tech deals, and more.
Locating
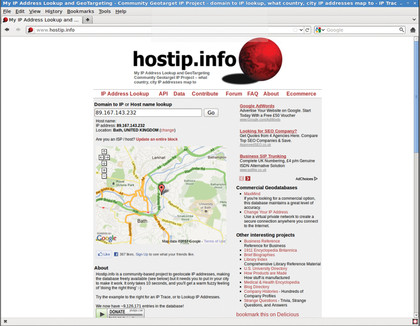
When you connect to the internet, your service provider assigns you an IP (Internet Protocol) address. This tells web servers and other computers you communicate with where to send the information. Any computer you interact with online can tell which IP address you use.
From this, they can find out some information, mainly your service provider and approximate location. Check out www.hostip.info to find out what you're transmitting to the world. Since IP addresses change periodically, web servers can't get closer to you than this. However, government agencies can force your service provider to reveal which subscriber was allocated to which IP address at what time. In short, they can link an online act with a physical computer.
For example, in April 2004 Shi Tao, a Chinese journalist, emailed the Asia Democracy Foundation with details of the Chinese Government's attempts to stifle news reports on the 15th anniversary of the Tiananmen Square massacre via Yahoo web mail. His government got the IP address he used from Yahoo, and since the ISP was state-controlled, could find out exactly where it was sent from. In November, he was arrested, and in March 2005 he was sentenced to ten years in prison.
To protect yourself from this level of scrutiny, you need to make sure that there's no link between you (and your IP) and the server you're communicating with. Simply encrypting your communication isn't enough, because it still allows the server to know who sent it - it just prevents eavesdroppers.
You can achieve the necessary privacy by passing your data through a series of encrypted relays. This technique is called onion routing, and has been implemented by the Tor Project
Step one: Communicate with the Tor directory server, which will reply with three random relays.
Step two: Encrypt your data with keys for each of the relays.
Step three: Send this encrypted package to the first relay. This server knows your IP address, but doesn't know what you're doing, since your data is encrypted with the keys to the other relays. The only piece of information they can access is the location of the second relay.
Step four: The first relay sends the encrypted package to the second relay, that can only decrypt the location of the third relay. This computer knows the location of the other two relays, but not your IP or what you are trying to communicate with.
Step five: The second relay sends the encrypted package to the third. This computer can decrypt your message and send it out of the Tor network on to the intended recipient. The third relay can see the final recipient of your data (and if you're using an unencrypted protocol, the actual data), and the location of the second relay, but he doesn't know your identity.
Step six: The recipient gets your request as though it had come from the third relay. They don't know your identity, or even that there is someone hidden behind the third relay. They respond to the third relay.
Step seven: The third relay passes the information back to you through the Tor network in the same manner as you sent it. No one on the network knows both the identity of the original sender, and the recipient.
However, Tor is an anonymisation system, not an encryption system. While the data is encrypted as it passes through the relays, once it leaves the network, it's no more or less secure than any other information on the internet. To keep your data private, you need to use the same precautions you would if you were not using Tor - ie use one of the encrypted protocols listed on the right of table one.
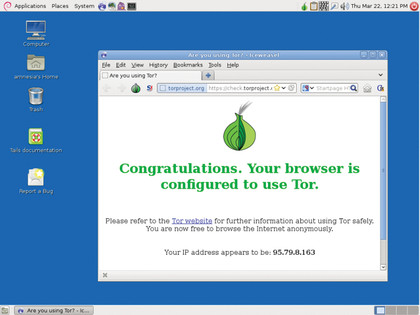
Sounds complicated? Fortunately, the Tor Project has put all the necessary tools in a single package with a secure version of Firefox. It's on the disk, or available from www.torproject.org - just unzip the file and run start-tor-browser. It will connect to the network and open a secure browser.
If you are on the run (in any sense of the phrase), you can browse securely via Orbot for Android or Covert Browser for iOS. There are potential statistical attacks against the network. For example, if an organisation can see all the data going into the network, and all the data coming out of it, the timing and quantities of packets may reveal which user sent what. However, due to the worldwide nature of the system, this would require co-ordinated and systematic monitoring across many countries.
You may think that using an internet account not linked to a physical location - such as mobile or satellite phones - will improve this situation, but it does the opposite. Mobile phone signals can be triangulated, and many satellite phones include the GPS co-ordinates of the phone in the connection to the service provider.
Polish firm TS2 sells a product that can pinpoint a satellite phone user: www.ts2.pl/en/News/1/151. It's possible that technology similar to this was used by the Syrian regime to target and kill journalists in Homs earlier this year.
Some regimes, most notably in China, appear to have taken steps to stop their citizens accessing Tor. The simplest way of doing this is to download a list of Tor relays and stop all connections to those machines.
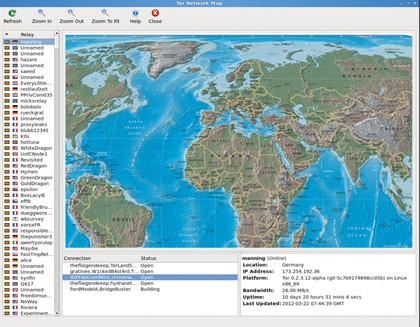
To allow users to bypass this, Tor has introduced a series of bridges. These are routes into the network that aren't published. A game of cat and mouse has now begun between the Tor Project and organisations trying to block access to the anonymisation service.
Like many community-based projects, Tor needs volunteers. However, unusually for a free software project, programmers are not the most needed people. Running a relay or bridge will help keep people anonymous.
Translators and people working in advocacy are also in demand. To see how you can help people maintain both their privacy and freedom of speech, check out www.torproject.com/getinvolved/volunteer
Disk encryption
If you're interested in privacy, then the chances are you use full disk encryption. If you don't then you may wish to consider it. It's easy to set up, usually just a tickbox during the distro install, and on a modern system the performance penalty should be minor for most purposes.
Note that partial disk encryption is considerably less secure - in issue 154 we showed one of many methods for circumventing it. Modern encryption methods using algorithms such as AES are unbreakable without the passphrase, provided a sufficiently long key is used (AES-128 should be considered a minimum. If the CIA is on your tail, then AES-256 is better).
There are a few methods a government agency can use to acquire this passphrase. Unfortunately, the easiest (for them) is torture. The second easiest is to try to guess your passphrase using a dictionary attack. However, let's assume that you've picked an unguessable passphrase, and managed to jump out of the window and flee when the knock at the door came. Your secrets will be safe, right?
Well, not quite. When you're using an encrypted drive, the computer stores the decryption keys in the memory. If they smash through the door just in time to see the computer shutting down, they could put a memory scrubbing tool in your computer and restart it.
Contrary to popular belief, the RAM in your computer isn't wiped when it's powered off, just very soon afterwards. Researchers at Princeton were able to steal encryption keys from the memory of restarted computers. The tools they created to do this are available from https://citp.princeton.edu/research/memory.
If you only locked or suspended your computer, then the situation's even worse. In these cases, the spooks will have time to freeze the memory before rebooting it (or transferring to a computer set up to scrub the memory).
At room temperature, memory typically becomes unusable after a few seconds. If it's frozen to around -50˚C (which is achievable using cheap aerosols), that time increases to several minutes. To avoid this style of attack, you need to stop them being able to access usable memory.
Don't leave your machine locked or suspended. If you have valuable information on it, turn it off. And prevent booting from devices other than the hard drive without a password. This will stop them booting straight into a tool such as the Princeton researchers' USB scrubbing tool. By the time they've managed to bypass your BIOS's security, the memory will be useless.
Using longer encryption keys will also help, since slight errors often creep in during the scrubbing process. The longer your key, the more of these errors it's likely to pick up.
If the men in black are really on your tail, then you could consider running your laptop without its battery. This means that you have only to pull out the power cable before running away.
 Become a TechRadar Insider
Become a TechRadar Insider






