Best network monitoring tool of 2025
Advanced monitoring tools to handle complex IT environments

Network downtime costs enterprises an average of $5,600 per minute, making reliable monitoring not just a convenience but a business necessity. As IT infrastructures become increasingly complex with SD-WAN deployments, hybrid cloud environments, and distributed applications, traditional monitoring approaches fall short of providing the visibility teams need to prevent costly outages.
IT professionals now have to monitor diverse network environments spanning on-premises data centers, multiple cloud providers, and remote locations — all while maintaining security and compliance standards.
But, the right network monitoring tool can transform reactive firefighting into proactive issue prevention, giving teams the insights they need to minimize business disruption. Keep reading to learn about our top network monitoring picks for 2025, tools to help you enhance security without sacrificing performance.
What is the best network monitoring tool right now?
Why you can trust TechRadar
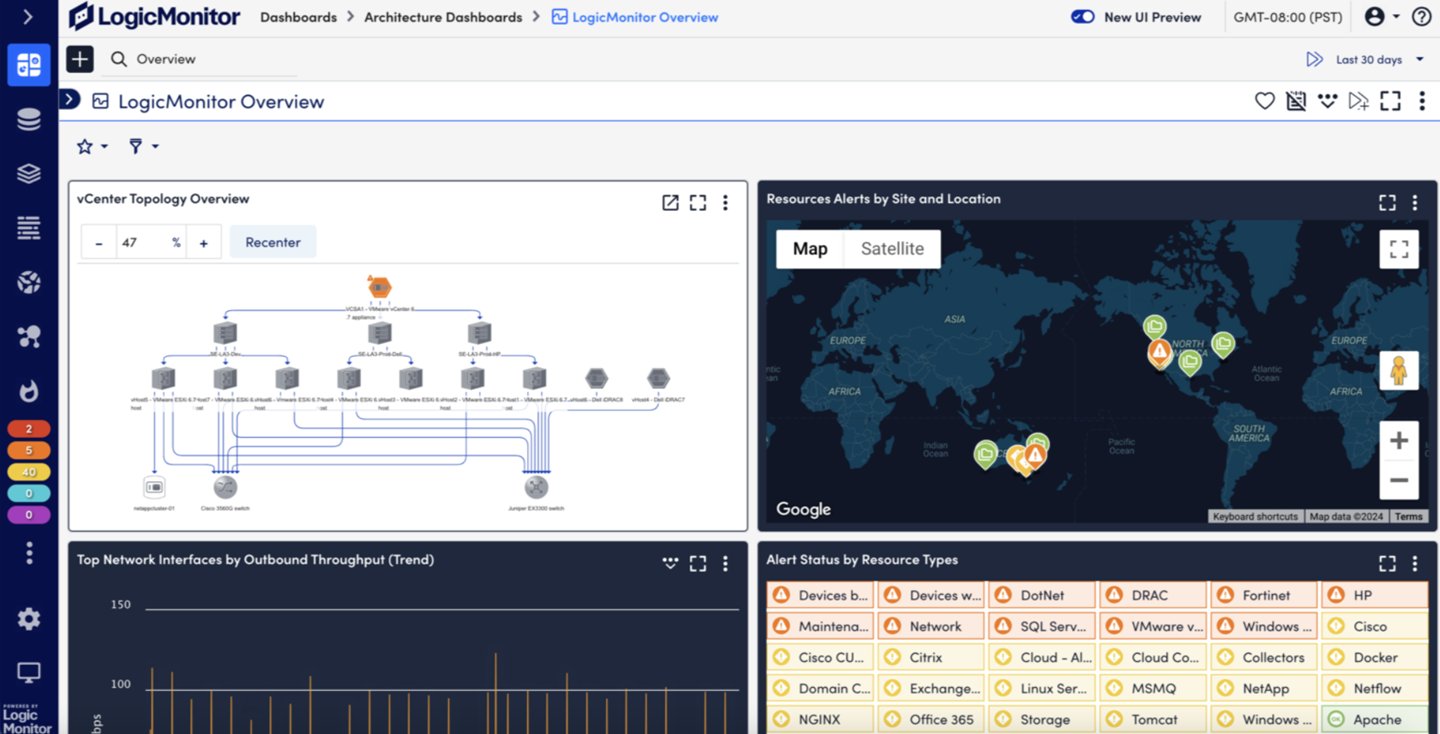
Our top pick for 2025 is LogicMonitor, for its comprehensive approach to network visibility across complex hybrid environments. This platform is built for automatic device discovery, real-time traffic analysis, and intelligent alerting. Plus, LogicMonitor's agentless architecture makes deployment exceptionally fast while supporting everything from traditional SNMP monitoring to modern flow-based traffic analysis.
Since 2008, TechRadar reviewers have spent weeks evaluating every major B2B software platform in the market, giving us unique insight into how these tools perform in real-world enterprise environments. We evaluated these network monitoring tools based on five critical factors: deployment speed, scalability, network visibility, analysis and reporting quality, as well as integration with existing IT ecosystems. Keep reading for the rest of our top picks.
We've also featured the best cloud storage.
The best network monitoring tools of 2025 in full:
Best network monitoring tool overall
Specifications
Reasons to buy
Reasons to avoid
LogicMonitor delivers comprehensive network monitoring through its unified SaaS platform that automatically discovers and monitors network devices across on-premises, cloud, and hybrid environments.
Its agentless collectors can be deployed in minutes and immediately begin discovering routers, switches, firewalls, and other network infrastructure using SNMP, NetFlow, sFlow, and other industry-standard protocols.
This eliminates the complexity of agent management while providing instant visibility into network performance and health.
Traffic analysis capabilities include real-time insights into bandwidth utilization, top talkers, and traffic patterns. LogicMonitor ingests flow data from NetFlow, sFlow, J-Flow, and IPFIX sources to identify bottlenecks, unusual traffic spikes, and potential security threats.
This means network metrics, logs, and topology data are all available within a single interface, streamlining troubleshooting workflows.
LogicMonitor's auto-generated topology mapping provides visual representations of network relationships and dependencies, making it easier to understand the impact of issues across interconnected systems.
When problems occur, root cause analysis helps pinpoint the source, while intelligent alerting reduces noise by correlating events. It also includes forecasting to help teams plan for capacity needs and identify problems before they impact users.
Read out full LogicMonitor review.
Best network monitoring tool for advanced users
Specifications
Reasons to buy
Reasons to avoid
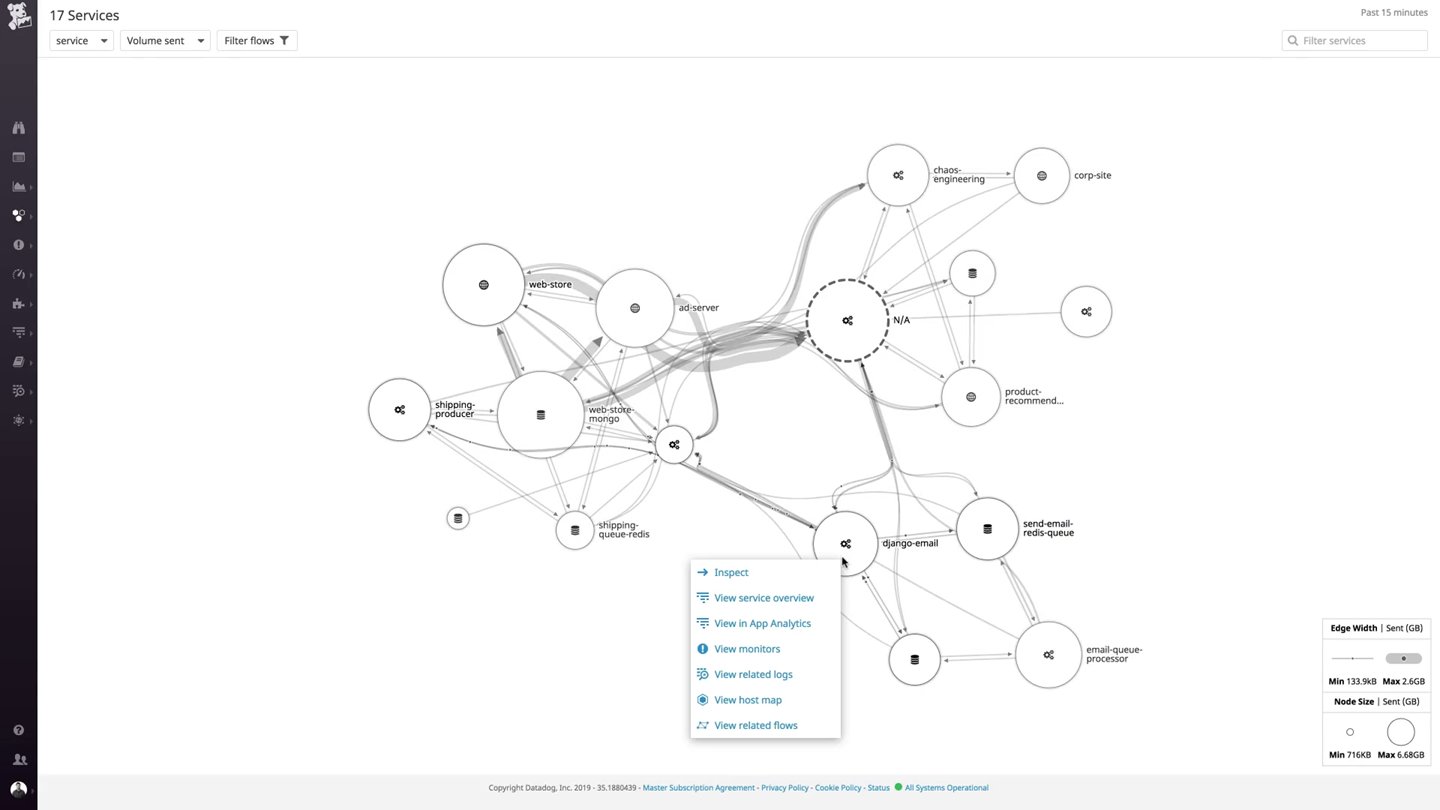
Datadog's network monitoring capabilities are part of its broader observability platform, making it a great fit for organizations that need to correlate network performance with application and infrastructure metrics.
The platform's Cloud Network Monitoring (CNM) provides real-time visibility into network topology across cloud environments, on-premises data centers, and hybrid deployments without relying on IP connection data alone.
This eliminates blind spots common in ephemeral cloud environments where traditional monitoring tools struggle.
Datadog automatically maps network dependencies and discovers managed cloud services, Kubernetes deployments, and other tagged objects without manual configuration. Its strength lies in its ability to analyze traffic efficiency between meaningful endpoints, from services to pods to availability zones.
Teams can quickly identify connectivity issues, analyze cross-zone traffic costs, and troubleshoot communication problems between microservices.
Network Device Monitoring (NDM) extends Datadog's capabilities to traditional network hardware, providing health and performance data from routers, switches, and firewalls alongside application observability data.
Its inventory-like view helps teams track all network-connected devices and filter connections between interfaces to identify upstream issues affecting performance.
Integration with Datadog's APM capabilities also means you can pivot from application performance issues to network analysis seamlessly when troubleshooting.
Read out full Datadog review.
Best network monitoring tool for ease of use
Specifications
Reasons to buy
Reasons to avoid
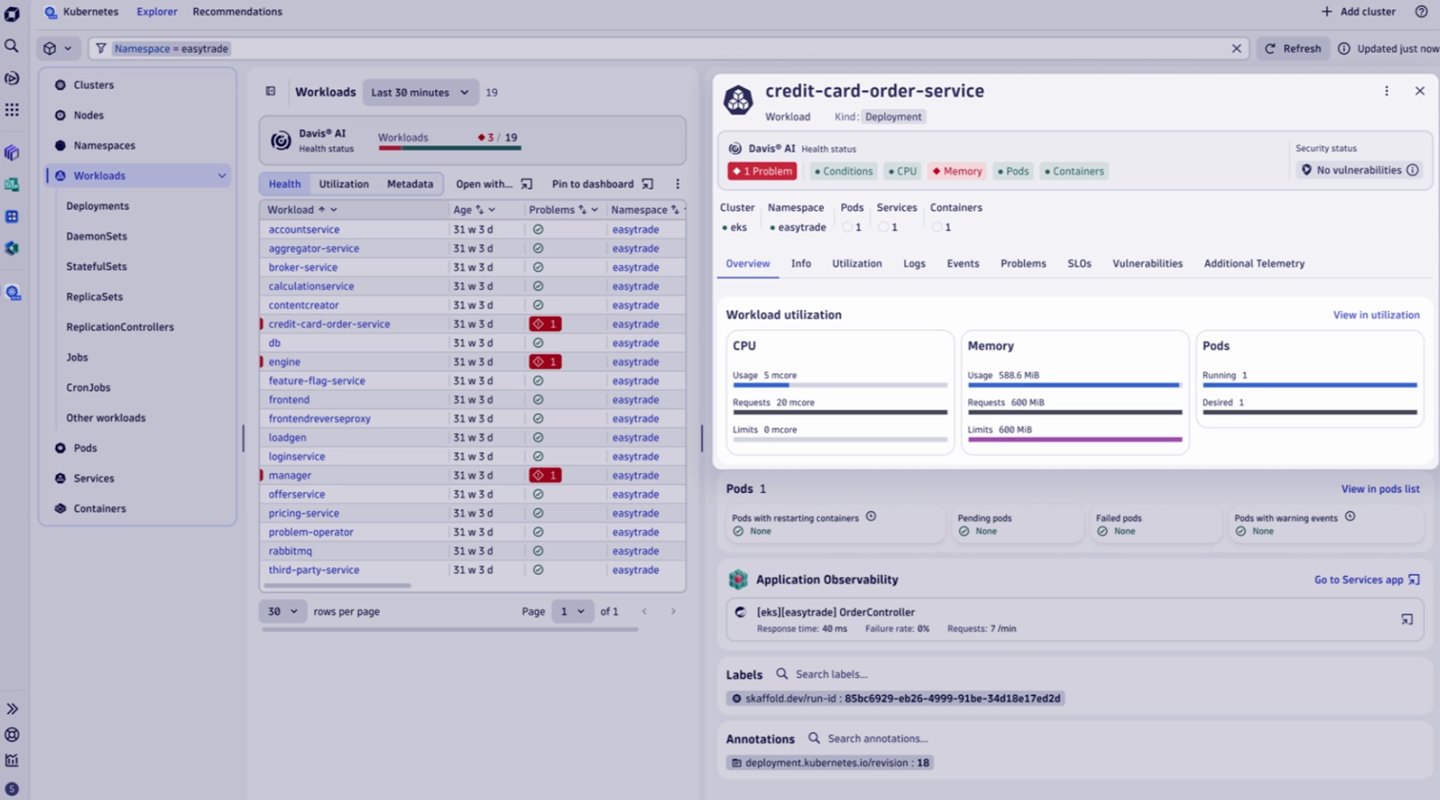
Dynatrace takes a full-stack approach to network monitoring, automatically correlating network performance with application and user experience data to provide comprehensive visibility into how network issues impact business operations.
The platform's AI engine, Davis, continuously analyzes network communications between hosts and processes, establishing baselines and detecting anomalies that indicate performance or security threats. This reduces alert noise while ensuring teams are notified of issues that truly require attention.
The platform analyzes data packets exchanged between processes and hosts, providing insights into communication quality and resource consumption.
Dynatrace's network monitoring operates with negligible overhead and includes intelligent throttling, ensuring the monitoring solution doesn't impact the systems it's protecting. This makes it perfect for production environments where performance is critical.
Dynatrace can show the business impact of network issues through its real-time dependency mapping and end-user experience correlation. When network problems occur, teams can immediately see which applications and users are affected, enabling faster decision-making.
The platform supports traditional protocols like SNMP while also ingesting modern telemetry data through OpenTelemetry, making it adaptable to diverse network architectures.
Read out full Dynatrace review.
Best network monitoring tool for hybrid clouds
Specifications
Reasons to buy
Reasons to avoid
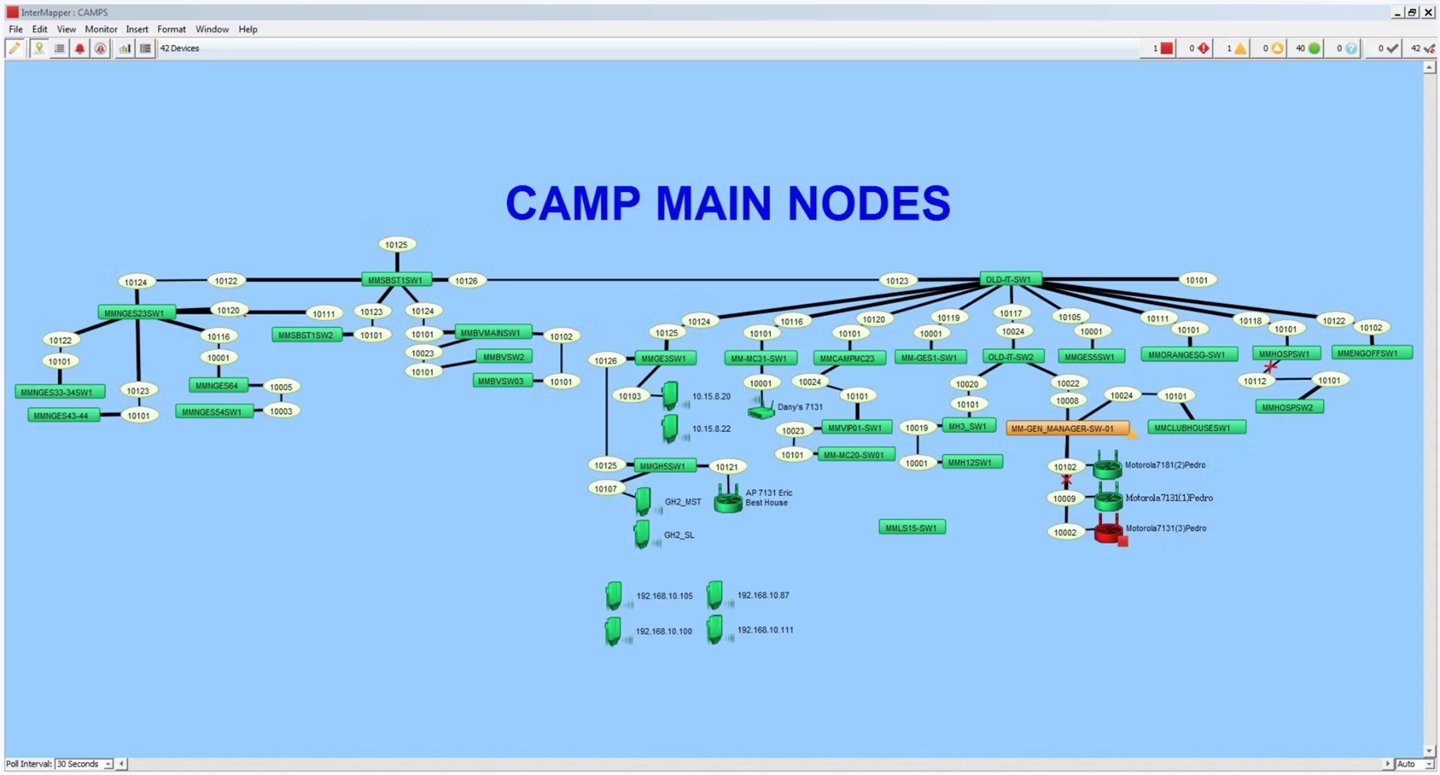
Intermapper specializes in creating visual network maps that provide live color-coded views of network infrastructure status. The platform automatically discovers and documents every IP-enabled device within minutes using SNMP and other protocols, then presents this information through customizable maps.
This makes it very effective for teams that need to quickly understand network topology and identify problem areas at a glance. It continuously polls device status 24/7, updating network maps in real-time with color-coded indicators that show what's operational and what's experiencing issues.
Teams can spot problems across distributed environments in seconds rather than hours, which is valuable for organizations with limited IT staff managing geographically dispersed networks.
Also the hierarchical mapping feature allows users to create sub-maps for specific areas like building floors or network closets, providing both high-level and detailed views as needed.
Smart alerting capabilities notify teams through multiple channels including email, text, and sound when performance thresholds are exceeded. The platform supports customizable alert schedules and escalation procedures to ensure critical issues receive timely attention.
Intermapper may not offer the advanced analytics of enterprise platforms, but its straightforward approach to network visualization makes it valuable for organizations that prioritize clear visual feedback.
Read our full Intermapper review.
Best comprehensive network monitoring tool
Specifications
Reasons to buy
Reasons to avoid
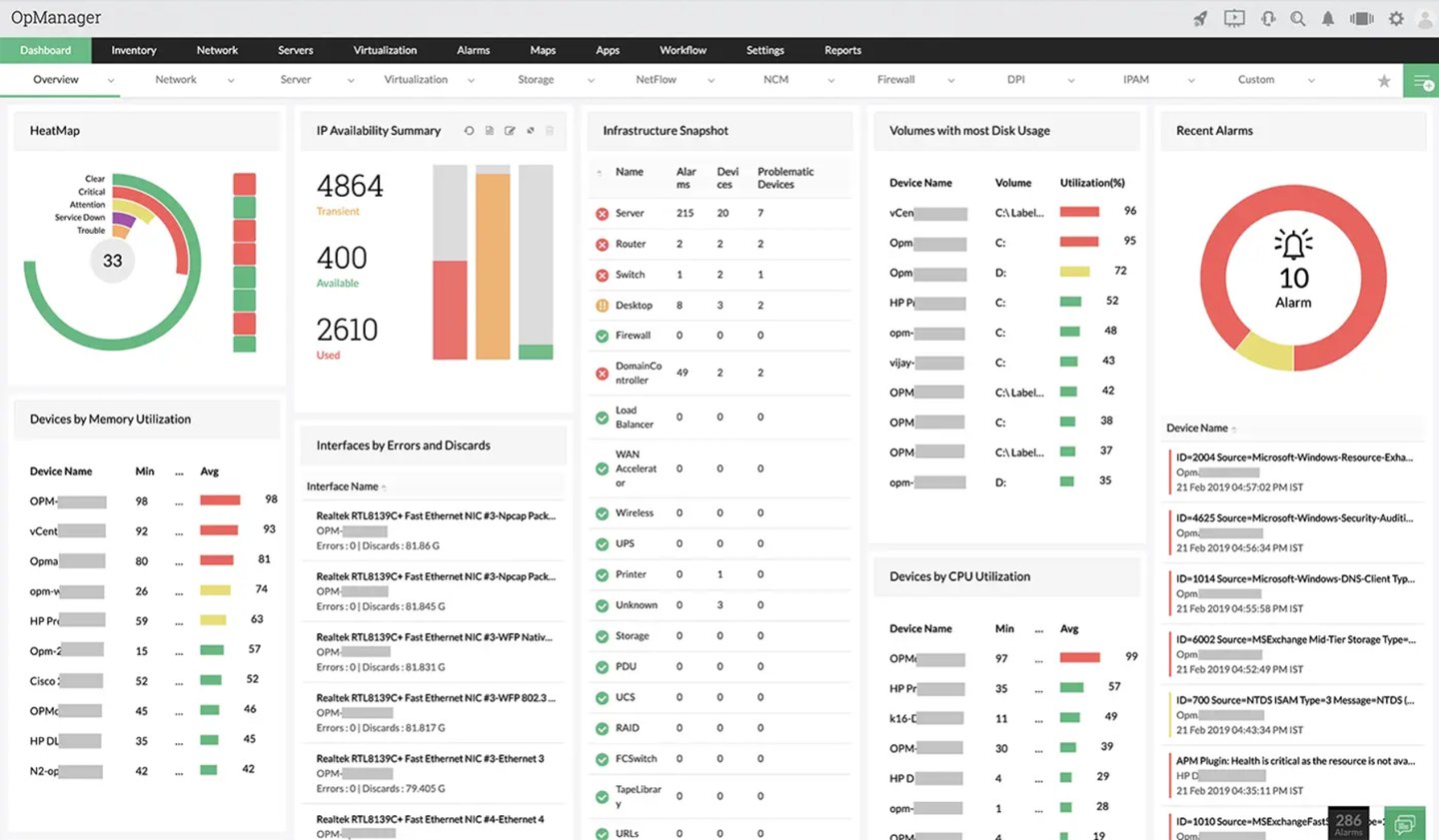
ManageEngine OpManager provides network monitoring with deep visibility into routers, switches, firewalls, load balancers, wireless controllers, servers, and storage devices.
A multi-protocol discovery engine leverages SNMP, WMI, ICMP, and CLI protocols to automatically discover and classify network infrastructure, creating both Layer 2 and Layer 3 topology maps that visualize physical and logical connectivity.
Its extensive device support makes OpManager particularly suitable for organizations with multi-vendor network environments.
OpManager is great at monitoring traditional network hardware, with specialized modules for wireless networks, WAN links, and storage systems.
Wireless monitoring provides comprehensive statistics for access points, wireless routers, and WiFi systems, while WAN monitoring leverages Cisco IPSLA technology to visualize link availability and troubleshoot performance issues.
Storage monitoring capabilities extend to fiber channel switches, storage arrays, and tape libraries with capacity utilization tracking and growth trend analysis.
OpManager's business-centric approach allows teams to group devices by geographical location, business service, or department. It replaces tool sprawl with a unified console that transforms raw performance data into actionable intelligence.
While the interface may feel dated compared to modern SaaS platforms, OpManager's feature set and competitive pricing make it attractive for organizations looking for comprehensive network management without premium pricing.
Read our full ManageEngine OpManager review.
Best network monitoring tool for small business

Specifications
Reasons to buy
Reasons to avoid
Paessler PRTG uses a sensor-based approach where each monitored element becomes an individual sensor, making it easy to understand what you're monitoring and how much it costs.
It automatically discovers network devices and creates sensors for switches, routers, servers, and applications using protocols like SNMP, NetFlow, WMI, and REST APIs.
You typically need 5-10 sensors per device, which makes capacity planning straightforward compared to tools with complex licensing models.
PRTG offers lots of out-of-the-box functionality with over 200 predefined sensors covering everything from basic ping monitoring to complex application performance metrics.
The AJAX-based web interface provides real-time monitoring capabilities alongside a desktop client for Windows, Linux, and macOS environments.
This makes it accessible to both technical staff and business users who need quick network status updates through customizable maps and dashboards.
Recent updates include significant infrastructure improvements with a new PostgreSQL-based time-series database and NATS messaging system for better scalability.
They address previous limitations around handling large-scale environments while maintaining PRTG's signature ease of deployment. The platform also extends monitoring capabilities to operational technology (OT) and IoT environments.
Read our full Paessler PRTG review.
Best network monitoring tool for MSP
Specifications
Reasons to buy
Reasons to avoid
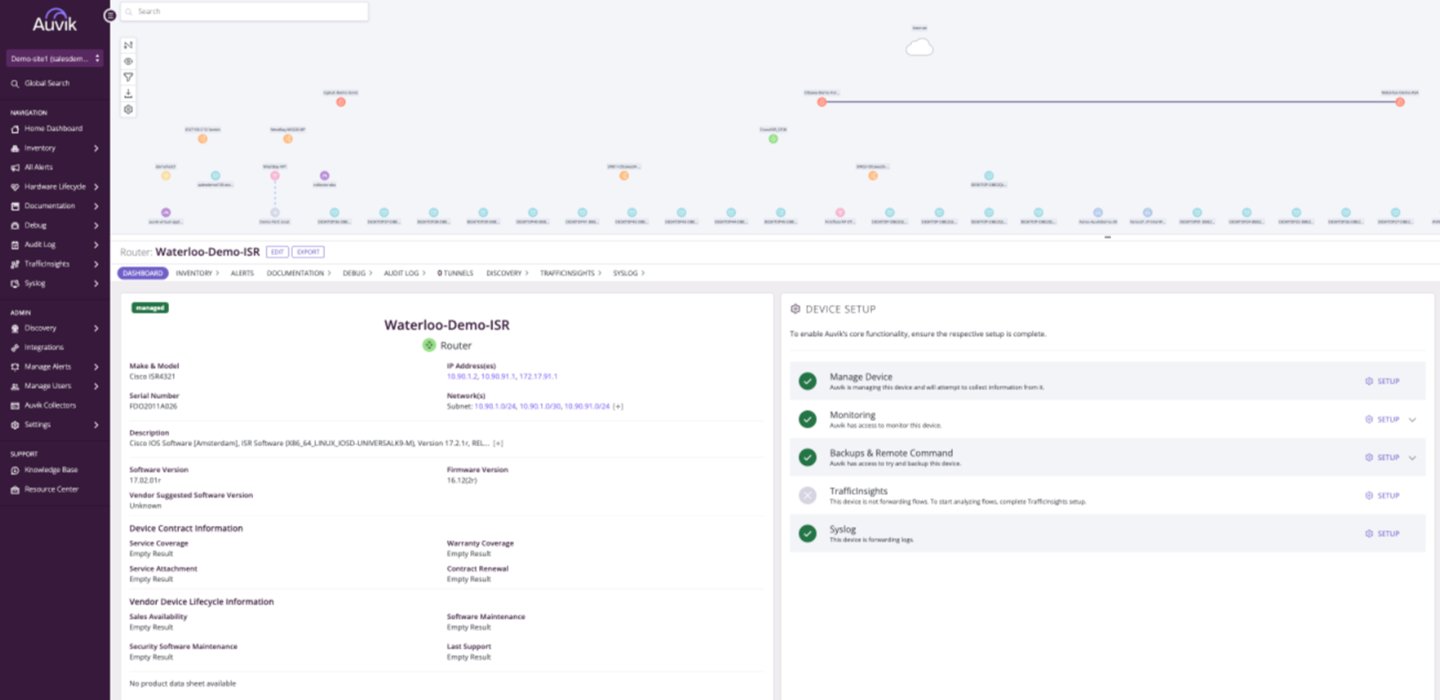
Auvik is great at providing instant network visibility through automated discovery and real-time topology mapping. It visualizes devices, connections, and traffic flows without any manual configuration.
The cloud-based platform uses protocols like CDP and LLDP to map network relationships automatically, making it valuable for teams managing multiple locations or clients. This eliminates the traditional setup time associated with network monitoring tools while providing immediate insights into structure and performance.
MSP-focused features include unlimited user access, global dashboards, and multi-tenant capabilities that let service providers manage multiple client networks from a single UI. Auvik's real-time alerting system overlays problems directly on network maps, making it easy to identify fault locations with a single click.
Bandwidth monitoring helps identify top talkers, applications, and protocols consuming network resources, supporting both troubleshooting and capacity planning activities. Auvik's configuration management module includes automatic backup of device configurations and change tracking that helps teams maintain network stability.
It provides complete lifecycle details for network assets, including support contracts, software versions, and security updates for budget and vulnerability management. This helps your organization identify devices approaching end-of-life or requiring updates before they become problems.
Read our full Auvik review.
Best network monitoring tool for Enterprises
Specifications
Reasons to buy
Reasons to avoid
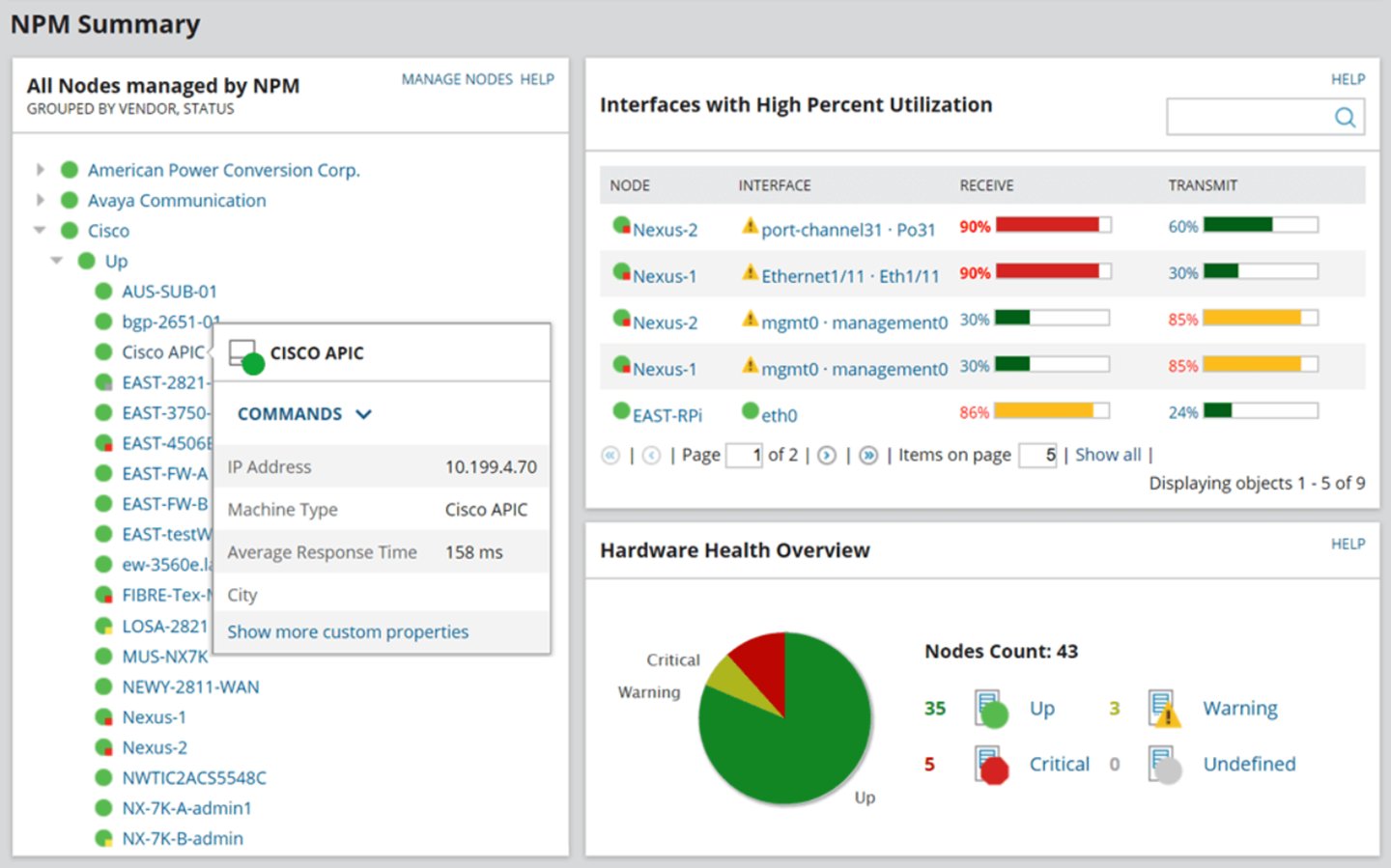
SolarWinds NPM provides enterprise-grade network monitoring with coverage of routers, switches, wireless access points, and load balancers through multiple protocols including SNMP, NetFlow, and WMI.
2025 updates focus on platform improvements including enhanced dashboard capabilities, intelligent maps parity, and recurring maintenance windows that reduce alert noise during planned activities. They address common enterprise needs for better visualization and more sophisticated alert management.
Scalability features support high-availability deployments with clustering and load balancing capabilities that ensure monitoring continuity even during hardware failures.
SolarWinds NPM also includes advanced capacity planning tools that help predict future resource needs based on historical trends and usage patterns. Its reporting engine provides both real-time dashboards and scheduled reports for compliance requirements and executive reporting.
Recent improvements include optimized wireless monitoring for environments with large numbers of access points, addressing performance issues that previously affected organizations with extensive Wi-Fi deployments.
Integration with other SolarWinds products create a unified observability stack, while third-party integrations support existing workflows and ticketing systems. However, the features that make NPM powerful for large enterprises can also make it overwhelming for SMEs with simpler monitoring needs.
Read our full SolarWinds NPM review.
Best open source network monitoring tool
Specifications
Reasons to buy
Reasons to avoid
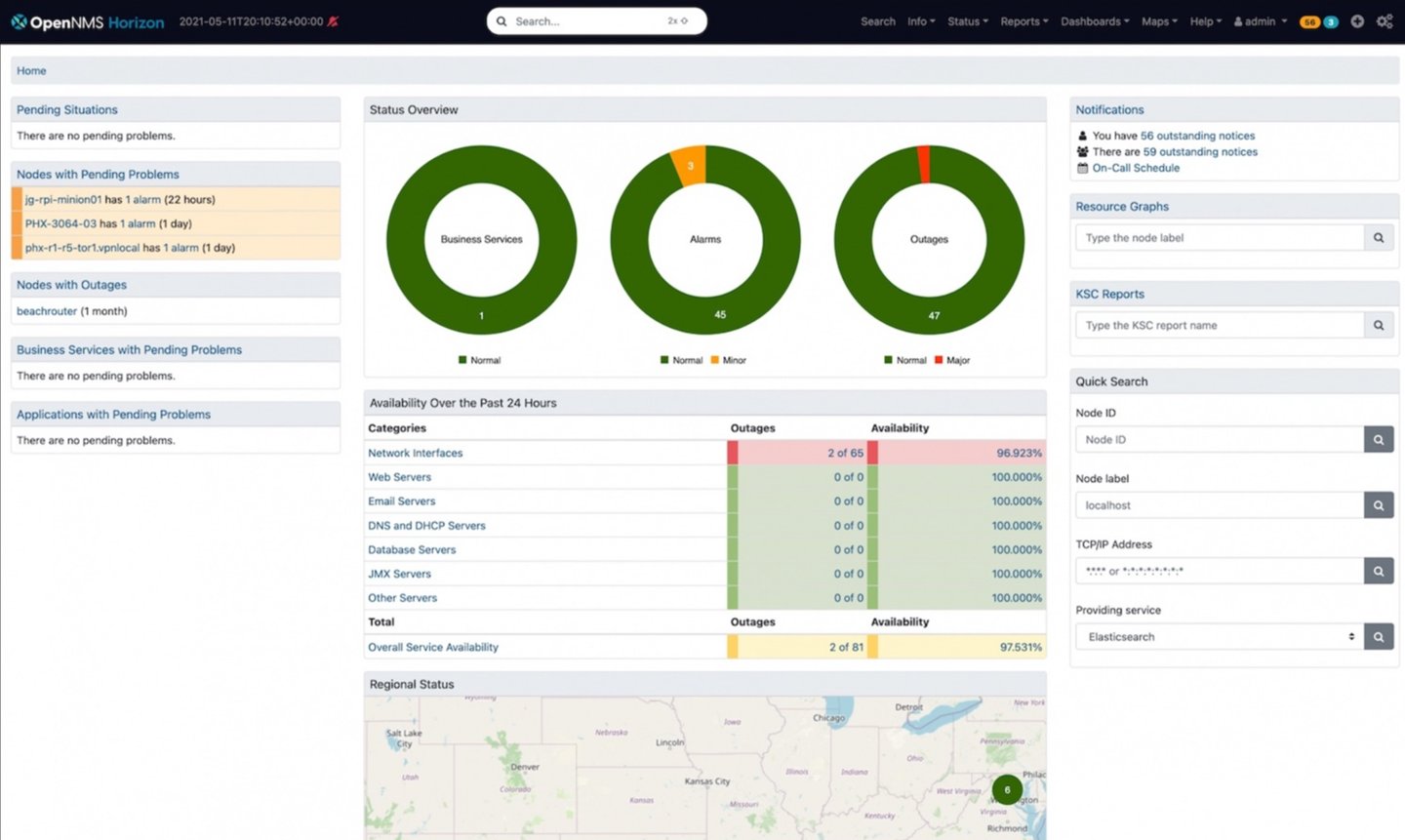
OpenNMS is an open-source network monitoring platform that provides enterprise-grade capabilities without licensing costs.
The platform supports extensive data collection protocols including SNMP, JSON, WinRM, XML, SQL, JMX, and modern standards like Prometheus without requiring third-party plugins.
This makes OpenNMS adaptable to diverse network environments and emerging technologies while avoiding vendor lock-in common with commercial solutions. The platform's traffic management capabilities handle over 300,000 flows per second across NetFlow v5/v9, IPFIX, and sFlow protocols.
Also, OpenNMS includes BGP monitoring support implementing OpenBMP standards for border gateway protocol messages and metrics, providing visibility into routing infrastructure that many commercial tools lack. Its scalability architecture uses Sentinels for flow persistence and Minions for distributed data collection, supporting geographically dispersed monitoring deployments.
OpenNMS provides digital experience monitoring through distributed Minions that can measure service latency and availability from multiple perspectives, helping teams understand user experience across different locations.
Enterprise reporting and visualization capabilities include customizable dashboards exportable as PDFs, resource graphs, and database reports that support compliance and executive reporting requirements.
While the open-source model provides significant cost advantages and customization flexibility, you should also consider the technical expertise required for deployment and ongoing management.
Read our full OpenNMS review.
Best network monitoring tool for clouds

Specifications
Reasons to buy
Reasons to avoid
Site24x7 provides cloud-based network monitoring with AI-driven analytics that predict issues before they impact business operations.
The platform employs predictive analysis to identify anomalies in response time and uses threshold alerts to help IT teams detect probable issues . This aligns with its 2025 trends toward AI-enhanced monitoring that reduces reactive troubleshooting and improves service reliability.
It also includes synthetic monitoring that simulates real-world network conditions to identify potential issues. Site24x7's 5G-ready monitoring capabilities handle the increased data flow and complexity of modern high-speed networks while providing latency monitoring and uptime assurance for businesses adopting 5G technology.
Security integration features provide real-time insights into suspicious traffic patterns alongside firmware vulnerability management and network compliance monitoring.Site24x7's 2025 roadmap focuses on unifying observability data with enterprise IT management, creating a more holistic view of infrastructure health and performance.
The platform supports sustainability initiatives through monitoring capabilities that help optimize energy consumption, addressing growing corporate focus on green IT practices. Its cloud-native architecture eliminates infrastructure maintenance requirements while providing global accessibility for distributed teams.
But, organizations with strict data sovereignty requirements may prefer on-premises alternatives.
Read our full Site24x7 review.
The best network monitoring tools of 2025: Compared
Platform | Starting cost | Key features | Easy to use? |
|---|---|---|---|
LogicMonitor | $22 per resource/month | Automated discovery | Real-time monitoring | Cloud-native architecture | Requires training |
Datadog | $15 per host/month | APM integration | Cloud monitoring | Custom dashboards | Complex setup |
Dynatrace | $0.08 per hour/host | AI-powered analytics | Full-stack observability | Automatic baselining | Complex initial setup |
Intermapper | $1,650 for 25 devices per year | Visual network mapping | Real-time status | Multi-platform support | Easy |
ManageEngine OpManager | $245 per month for 25 devices | Multi-protocol discovery | Device management | Configuration backup | Requires training |
Paessler PRTG | $179 per month for 50 devices | Sensor-based monitoring | Web interface | Custom dashboards | Easy to moderate |
Auvik | $35 per device/month | Cloud deployment | Automated topology | MSP features | Easy |
SolarWinds NPM | $12 per device/month | Enterprise scalability | Advanced reporting | High availability | Complex |
OpenNMS | Not disclosed | Flexible provisioning | Protocol support | Community-driven | Steep learning curve |
Site24x7 | $49 per month | AI analytics | Multi-cloud support | Synthetic monitoring | Easy |
We've also listed the best network switch.
Best network monitoring tool FAQs
What is network monitoring and why do I need it?
Network monitoring means continuously observing your network infrastructure to track performance, detect issues, and ensure optimal operation. Network downtime costs enterprises thousands of dollars per minute, making monitoring essential to prevent costly outages and customer complaints.
How do network monitoring tools improve security?
Network monitoring tools enhance security by providing visibility into network activity and detecting unusual traffic patterns that might indicate cyber threats. They can identify unauthorized access attempts, suspicious data flows, and security breaches, enabling rapid response to protect your infrastructure.
What's the difference between free and paid network monitoring tools?
Free tools typically offer basic monitoring capabilities with limited device support and community-based help, while paid solutions provide advanced features like enterprise scalability, priority support, and comprehensive reporting. Free versions are suitable for small networks, but growing businesses usually need paid tools for better functionality and professional support.
Which metrics should I monitor in my network?
Essential metrics include bandwidth utilization, latency, packet loss, device uptime, and error rates across your network infrastructure. You should also monitor application response times, security events, and capacity trends to maintain optimal performance and plan for future growth.
How often should I update my network monitoring software?
Network monitoring software should be updated regularly to maintain security and add new features, but many cloud-based solutions update themselves automatically. On-premises solutions typically require quarterly or bi-annual updates, while security patches should be applied immediately when available to protect against emerging threats.
How we test the best network monitoring tool
We test by evaluating numerous factors. To start with, we look at the feature set, the range of tools available, and what size of businesses this would be ideal for. We consider how easy the setup is, the simplicity of the interface, and whether there's sufficient documentation and tutorials for users to utilize necessary options optimally.
We assess how well the service integrates with other relevant apps, and check the overall scalability of the service. We also analyze whether there are collaboration features for multiple users, and lastly, we judge the quality of the customer service and the different pricing plans available.
Read more on how we test, rate, and review products on TechRadar.
Get in touch
- Want to find out about commercial or marketing opportunities? Click here
- Out of date info, errors, complaints or broken links? Give us a nudge
- Got a suggestion for a product or service provider? Message us directly
- You've reached the end of the page. Jump back up to the top ^
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!

Ritoban Mukherjee is a tech and innovations journalist from West Bengal, India. These days, most of his work revolves around B2B software, such as AI website builders, VoIP platforms, and CRMs, among other things. He has also been published on Tom's Guide, Creative Bloq, IT Pro, Gizmodo, Quartz, and Mental Floss.

 Become a TechRadar Insider
Become a TechRadar Insider