6 ways to protect your PC from rogue PDF files
PDF files can contain malware. Here's how to stay safe
Once they were just a convenient way to share documents with the widest possible audience. But PDF files have become increasingly popular as a way to distribute malware, according to a recent Microsoft security report, with attacks doubling almost every month in the second half of 2008.
Adobe has patched the vulnerabilities behind those particular problems, so if you're running the latest copy of Adobe Reader then you're not currently at risk. At least, that's the theory.
But what if there are other PDF security holes yet to be discovered? Just a few minutes spent tweaking your Adobe Reader settings could protect you from future attacks. Here's what you need to know.
1. Disable JavaScript
Some PDF files make use of Acrobat JavaScript to do smart things like perform calculations in form fields, change a documents appearance or work with a database. Unfortunately hackers sometimes use it to create exploits, so if your PDF files don't need that kind of power then it's worth turning JavaScript off. Click Edit > Preferences > JavaScript and clear the "Enable Acrobat JavaScript" box.
2. Block multimedia
PDF files may also include embedded audio or video content, a problem if that's been hacked to exploit a media player security flaw. If you don't need multimedia support in your PDF files then click Edit > Preferences > Multimedia Trust, and clear "Allow multimedia options" for both "Trusted documents" and "Other documents".
Sign up for breaking news, reviews, opinion, top tech deals, and more.
3. Beware file attachments
The authors of a PDF document can configure it to launch attachments embedded within the PDF file itself. There are obvious risks here, and so Adobe will always display an "are you sure you really want to do that"-type prompt - but that may not always be enough. If inexperienced users have access to your system, for instance, they may not fully understand the consequences of clicking "OK".
Even with the prompt, we think the dangers of this feature outweigh any benefits. If you agree, click Edit > Preferences > Trust Manager and clear the "Allow opening of non-PDF file attachments..." box.
4. Control your plug-ins
Adobe Reader comes with more than 20 standard plug-ins to handle everything from processing web links to playing videos or saving PDF files. Each one provides another potential attack point for a hacker, so removing unnecessary plug-ins should help make you more secure (and might help Adobe Reader boot more quickly, too).
Click Help > About Adobe Plug-Ins to get a feel for what's installed. If you scroll down to SaveAsRTF and decide you really don't need the ability to save PDF files in Rich Text Format, say, then make a note of the plug-in's file name: SaveAsRTF.api. Close Adobe Reader, navigate to the plug-ins folder (by default \Program Files\Adobe\Reader 8.0\Reader\plug_ins) and rename SaveAsRTF.api to SaveAsRTF.api.old. Restart Adobe Reader, click Help > About Adobe Plug-Ins again and you'll see SaveAsRTF has disappeared.
Repeat the process with other unwanted plug-ins, as required. And if you discover you need a particular plug-in, after all, then remove the .old from the file name and restart Adobe Reader to get it working again.
5. Tweak default settings
Adobe Reader has a few other security settings that are installed at their safest values by default, but it's wise to check your configuration occasionally to ensure they're still set correctly.
Click Edit > Preferences to begin, then choose the JavaScript category. The "Enable menu items JavaScript execution privileges" option here gives extra rights to scripts, so leave this off unless you've good reason to do otherwise.
Click Security and ensure "Verify signatures..." is checked, allowing Adobe Reader to check document signatures.
Then click Trust Manager > Change Settings to view the web sites that Adobe Reader is allowed to access. Make sure the program is not set up to use the riskiest "Allow all web sites" (unless you've set that yourself and understand the dangers), and that the My Web Sites list is either empty, or only contains sites that you trust.
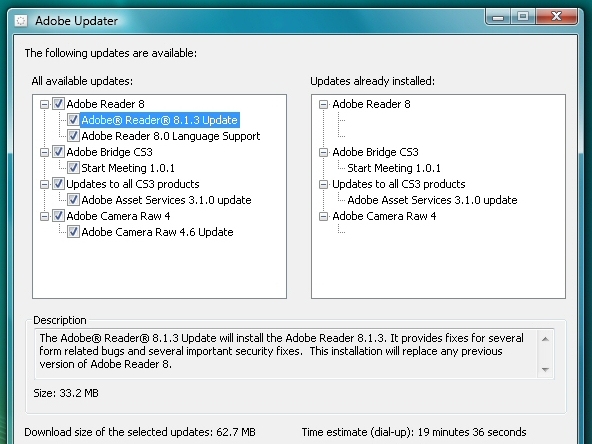
6. Stay up-to-date
The best protection of all? Never view PDF files from untrusted sources, particularly spam. And ensure Adobe Reader is kept up-to-date with all the latest security patches. Allow the program to download updates just as soon as it alerts you to them, and click Help > Check For Updates occasionally just to confirm that you have the latest version.

Mike is a lead security reviewer at Future, where he stress-tests VPNs, antivirus and more to find out which services are sure to keep you safe, and which are best avoided. Mike began his career as a lead software developer in the engineering world, where his creations were used by big-name companies from Rolls Royce to British Nuclear Fuels and British Aerospace. The early PC viruses caught Mike's attention, and he developed an interest in analyzing malware, and learning the low-level technical details of how Windows and network security work under the hood.

 Become a TechRadar Insider
Become a TechRadar Insider






