TechRadar Verdict
TunnelBear doesn't have the largest network, or the most apps, or the longest of feature lists, but it does a good job of simplifying VPNs for novice users. Plus, WireGuard support has almost doubled speeds on Windows compared to other providers, and its annual audits are some of the most intensive in the business.TunnelBear is not for experts, but it's well worth a try for VPN newbies, casual, and less demanding regular users.
Pros
- +
Beginner-friendly
- +
Unlimited simultaneous connections
- +
Detailed annual security audits
- +
Unblocks Disney Plus, ITV, Channel 4 and more
- +
WireGuard now available on all apps
- +
Above average OpenVPN speeds
Cons
- -
Last audit report found a high number of security vulnerabilities
- -
Short on features
- -
Doesn't unblock Netflix, Amazon Prime Video
- -
Windows kill switch can fail in extreme situations
- -
No Bitcoin support
- -
No money-back guarantee
Why you can trust TechRadar
VPNs can seem like a complicated technology, packed with geeky features that not everyone understands, but TunnelBear is a provider that does does their best to keep things simple.
The Canadian-based, McAfee-owned company doesn't drown you in jargon. The website has little talk of protocols, no mention of encryption types, and barely any technical terms at all. Instead, the company focuses on the fundamentals, such as clearly explaining why you might want to use a VPN in the first place.
This approach won't work for everyone. If you're an experienced user and want to get down to the technical details of the service, for instance, you're likely to be disappointed. Search for DNS on the ExpressVPN support site, for instance, and right now you'll get 56 hits. Search at TunnelBear and you'll get three.
- Want to try TunnelBear? Check out the website here
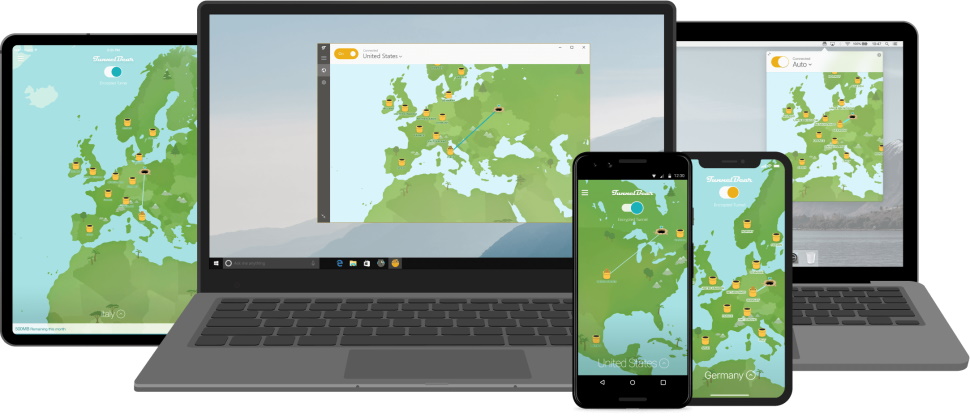
The service specs are fairly average. The network has a mid-sized 47 countries. There are apps for Windows, Mac, iOS, and Android, as well as extensions for Chrome and Firefox. But there’s little support for getting the service working on Linux, routers, game consoles, or other not-so-common devices.
TunnelBear does have a free plan, though, and it’s great to see the company finally lift its monthly allowance from a miserly 500MB to a more usable 2GB. Although, if that’s still not enough, PrivadoVPN and Windscribe offer 10GB, while Proton VPN has no data limit at all.
There’s more good news for paying customers. TunnelBear has dropped its ‘five simultaneous connections’ limit, and you can now install and use the service on as many devices as you like.
We noticed a surprising technical improvement in support for ECH (Encrypted Client Hello), a valuable feature that protects the initial key exchange between the app and VPN server to keep it safe from snoopers. That earns a big thumbs up from us. Many otherwise more technically advanced VPNs don't support ECH yet.
TunnelBear has been busily enhancing its apps, too. Recent welcome additions include a kill switch for iOS (something you won't often see elsewhere), more reliable split tunneling, and handy usability pluses such as a Search box for the location list.
TunnelBear pricing
TunnelBear's free account offers only 2GB of traffic a month. It’s better than it was, but only enough for very occasional use. This doesn't restrict the number of locations you can use, though, unlike most of the free competition. It's ideal if you're looking for a simple way to check out the apps before you buy.
Its monthly plan gives you unlimited data for a reasonable $9.99 a month. The price drops to an effective $4.99 a month on the annual plan, or $3.33 if you sign up for three years.
These are competitive prices that beat many providers, although there are some with cheaper deals. Private Internet Access asks $2.03 a month on the first term of its three-year plan, and opting for Ivacy's five-year plan cuts the cost to a supercheap $1. To put that in perspective, handing $59.88 to TunnelBear gets you one year of coverage. Hand $60 to Ivacy and you're protected for five.
If you do sign up for TunnelBear, keep in mind that there's no money-back guarantee. The small print says: "While all amounts paid are non-refundable, certain refund requests for subscriptions may be considered by TunnelBear on a case-by-case basis." Presumably, you might get a refund if you've had really bad service, but it's entirely up to the company to decide. Not quite as friendly as the cuddly cartoon bears suggest, then.
TunnelBear used to support Bitcoin payments for its annual plan, but no more. With no PayPal, either, it’s now strictly card-only.
Privacy and logging
TunnelBear's privacy policy is one of the most thorough we've seen from any VPN provider, with in-depth information on everything the service collects, and everything it doesn't. We do mean thorough, too – the details go right down to the names, purposes, and expiry dates of the cookies used by TunnelBear.com.
The logging policy is clearly described, with TunnelBear explaining that it does not collect IP addresses visiting their website, IP addresses upon service connection, DNS Queries while connected, or any information about the applications, services, or websites users use while connected to the Service. As a result, the company says, it can't link any of its users to an action carried out by a specific IP address. Sounds good to us.
The service does record 'operational data', updating this when you connect. That includes the OS version of your device, TunnelBear app version, whether you've been active this month, and the bandwidth you've used. Not quite zero logging, then, but it's far less than we've seen elsewhere, and there's nothing here that could link you to any online action.
These aren’t just words either, TunnelBear backs up its claims with ultra-comprehensive annual audits of its apps, browser extensions, service infrastructure, backend and frontend systems, and the public website. Auditors Cure53 spent 42 days drilling down into the detail, one of the largest projects we've seen.
Unfortunately, the results weren't great. Cure53 found 32 issues in total, including two critical and eight high-severity security vulnerabilities. Cure53 described this as worrisome, but it's better to discover these from an expert auditor than after you've been hacked. And unlike some VPNs, TunnelBear hasn't hidden its audit report from potential customers. Anyone interested can access it directly from the company's blog post.
Overall, we must applaud TunnelBear for its level of transparency. Most VPNs have never had any form of security audit, and the providers who have actually made some movement in this direction typically have one-off audits with a far narrower scope. That's just not good enough, and it's great to see TunnelBear leading the way on this front.
But we'd still like to see less unpleasant discoveries in next year's report, please.

Torrents
TunnelBear doesn’t say much about torrenting on its website – in fact, it barely mentions the topic at all – but the support team explained that it’s available in all locations.
Some may be more reliable than others, apparently. The company recommended we try Canada, US, UK, Romania, Netherlands, Germany, or Sweden if we had problems elsewhere.
How likely is it that you might have problems elsewhere, then? To get an idea, we tried downloading torrents from three of the other locations: Greece, Portugal, and Brazil. Despite not being on TunnelBear's 'recommended' list, they all completed without any issues, suggesting that you really should be able to use torrents right across the network.

Windows app
TunnelBear's Windows app opens with all its locations highlighted on a gray world map. This has one or two nice visual touches, with cartoon palm trees in tropical areas, and snow-covered Christmas trees if you head further north. But it’s also very basic, with little map detail, and not even a zoom option to help find the locations you need.

You can also select your server from a more conventional location list. That’s probably easier, but if anything, it’s even more basic, with no ping times, server load figures, or Favorites system to save your most commonly-used servers.
Once you've chosen a location, clicking 'On' gets you connected, and the app displays a 'connection' animation, panning the screen and plotting a line across the map to your destination. It’s a cute visual effect the first time of viewing, but it began to annoy us by the 100th (unfortunately, there’s no way to turn it off).
WireGuard connection times were a little disappointing at 3-4 seconds, even for our nearest server (the best VPNs take around a second). But this didn’t change much over distance – even connecting from the UK to New Zealand took only 5-6 seconds – and times were reasonable overall.
The app displays notifications when it connects or disconnects, too, ensuring you always know when you're protected, and when you're not.
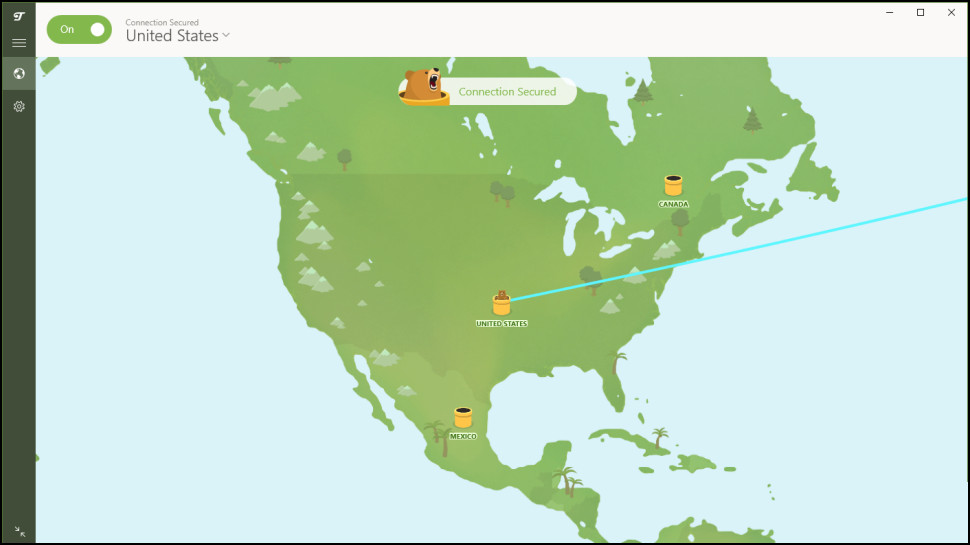
The app doesn't have many settings, but the few you get are very useful. You can have it load when Windows starts, for instance, then automatically activate the VPN whenever you access an untrusted Wi-Fi network (everywhere but home and work, say).
The Obfsproxy-based GhostBear attempts to make your activities look more like regular internet traffic, perhaps helping you connect in countries like China which try to detect and block the use of VPNs.
A VigilantBear setting is essentially a kill switch, blocking all internet traffic if the VPN drops to prevent any identity leaks. We found this had some issues in extreme situations – the kill switch could fail if the app crashed and it was restarted, for instance, but it performed well in simpler tests.
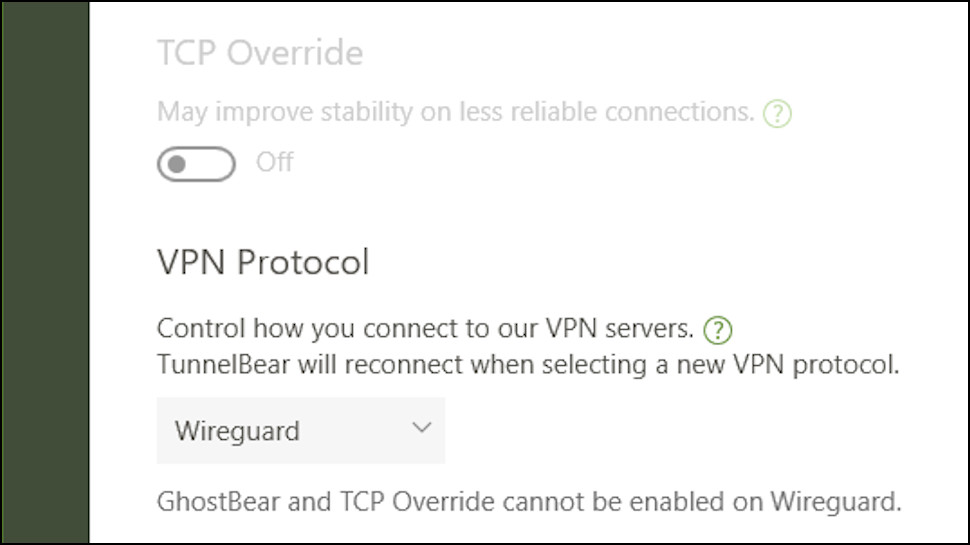
It’s great to see WireGuard supported in the Windows app, as well as OpenVPN and IKEv2. By default the app selects the most appropriate protocol for your network, but you can now also choose your preferred option.
Overall, TunnelBear's Windows app is easy to use, and the arrival of WireGuard is a major plus. There’s clearly scope for improvement in every part of the app, though, and the basic feature list could disappoint experienced users.

Mac and mobile apps
TunnelBear's Mac and mobile offerings all feature essentially the same colorful map and location list as Windows, along with WireGuard, OpenVPN, and IKEv2 support. That's good news, but what's less welcome is they also have odd variations, which could be confusing if you use more than one platform.
The Mac app is relatively basic, for instance, with no VigilantBear kill switch, automatic connection when you access untrusted Wi-Fi, or GhostBear to bypass VPN blocking.

The Android app includes a kill switch, and SplitBear, which is TunnelBear's take on split tunneling. If an app can’t connect when the VPN is running or it's too slow and doesn't require extra security, SplitBear allows it to bypass the tunnel and use your regular unencrypted connection, instead.
The Android app did have an odd technical issue at review time. The ability to switch protocols wasn't available on our Android 12 test system. TunnelBear told us this had been removed from 'newer operating systems' temporarily, while it diagnosed some reported problems, but the feature will return soon.

Unlike the Mac app, the iOS app does support the VigilantBear kill switch. However, you don't get GhostBear, and although there's the SplitBear feature, it's for websites rather than apps. So, if LocalTV.com refuses to stream when you're using the VPN, for instance, you can use SplitBear to have it connect via your normal connection.
Overall, these are all decent apps and the mobile offerings in particular outperform many competitors. But we'd like them to be more consistent across platforms, where possible, with features like SplitBear available across all platforms.
Browser extensions
Installing TunnelBear's browser extensions can make the service easier to operate, by allowing you to choose a location, connect and disconnect from inside your browser. The extensions work as proxies and so only protect your browser traffic, but if that's all you need, the extra convenience could make them worth a try.
The Chrome extension added an icon to our address bar, and tapping this enabled choosing new locations from a drop-down list.
Hit the 'Connect' button and, as usual with proxies, you're connected instantly. A tiny map updates to show your location, similar to the regular apps.
There are no extra features, no WebRTC or tracker blocking or anything else. But the extension does have a small usability plus in its keyboard shortcut support. If you want to keep your hands off the mouse, pressing Ctrl+Shift+U connects you to the VPN, and pressing it again will toggle the connection off when you're done. (A separate Alt+Shift+N shortcut toggles the connection on and off in Incognito mode.)
We checked the Firefox extension to see if it had any more options, but no, it looked and worked much the same as the Chrome version.
The browser extensions follow a very similar pattern to the apps, then – they are short on features, but relatively simple, and fine for the target audience of casual users.
Performance
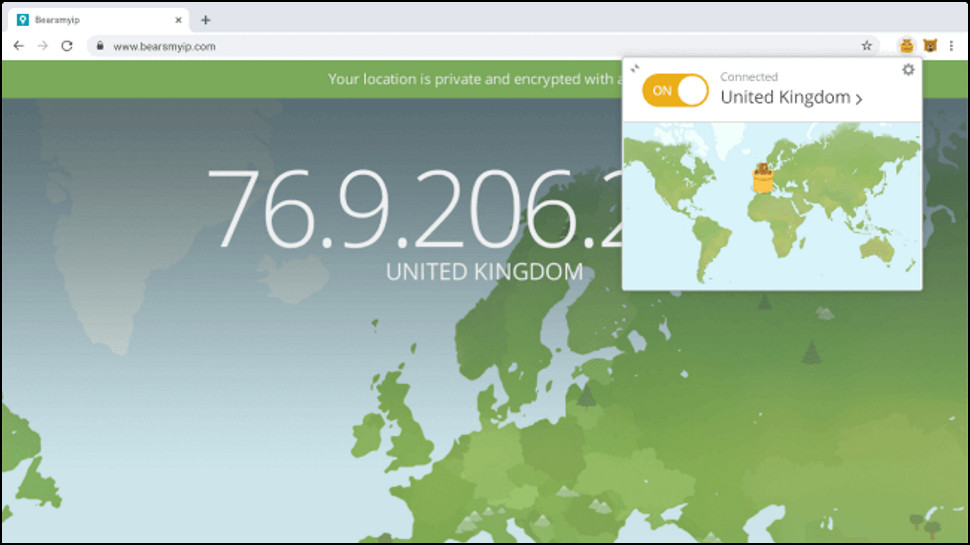
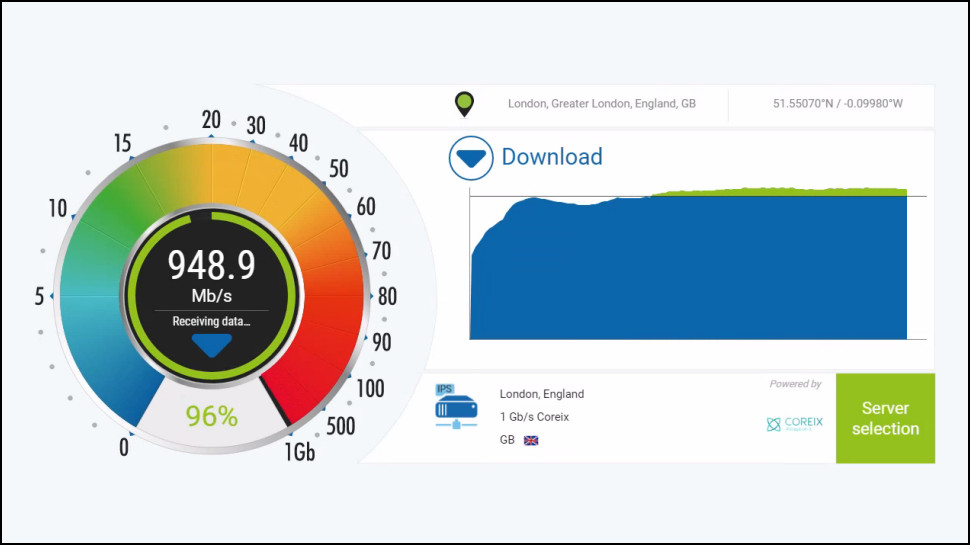
To check out TunnelBear's performance, we first connected to our nearest server from a UK data center and a US location, each with 1Gbps test connections.
We then measured our download speeds multiple times using several benchmarking services including SpeedTest's site and command line app, Cloudflare, and others. Then we repeated each test in an evening session.
TunnelBear’s US OpenVPN speeds were excellent at 270-310Mbps. That's two to three times as fast as some providers, although a handful have done better. Mullvad even beat 500Mbps in recent tests.
Switching to WireGuard accelerated our downloads to 500Mbps. That's far behind the likes of NordVPN, Surfshark, and Hide.me, all of which beat 950Mbps in our last checks. Still, TunnelBear delivers all the speed that most people need and are able to use.
Speed can sometimes be affected if a VPN uses virtual locations. For example, you want to connect to Malta and get a Maltese IP address, but the servers are physically located in another country.
We tested some of TunnelBear's locations to get a feel for how the service works. The Brazil, Mexico, Nigeria, Peru, and Slovenia servers all turned out to be in or very close to their advertised countries. There seemed to be a few virtual locations, but the host countries were never too far away (the Indonesia servers may be based in Singapore, for instance, while the Kenya location may be closer to South Africa.) If it's important that your VPN locations are close to their advertised countries, TunnelBear is a reasonable choice.
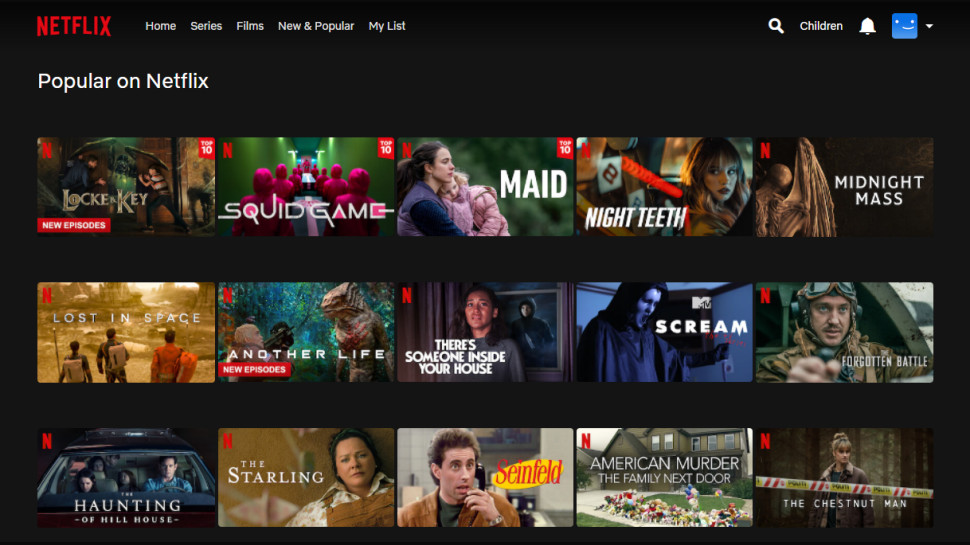
Netflix and streaming
One of the major selling points of a VPN is that it can make you appear to be visiting a website from another country, perhaps giving you access to content you wouldn't be able to view otherwise. Unfortunately, this doesn't always work, so we test all VPNs with Netflix and more to see if they can give us access to various streaming sites.
TunnelBear has a poor history in our unblocking tests, and this time was no different, as it failed with Netflix in the US, UK, Australia, Canada, and Japan.
There was some success elsewhere. TunnelBear failed with BBC iPlayer, but it got us into the UK's ITV and Channel 4. In Australia, the service was defeated by 10 play, but successfully unblocked 9Now.
TunnelBear couldn’t really redeem itself with our last two tests. It failed with Amazon Prime, but we were able to view US content on Disney Plus.
There's a faint chance TunnelBear might unblock one or two smaller streaming platforms, but if accessing geo-blocked content is a priority, ExpressVPN, NordVPN, Private Internet Access, ProtonVPN, PureVPN, and Surfshark all unblocked every one of our test streaming services in our latest round of reviews.
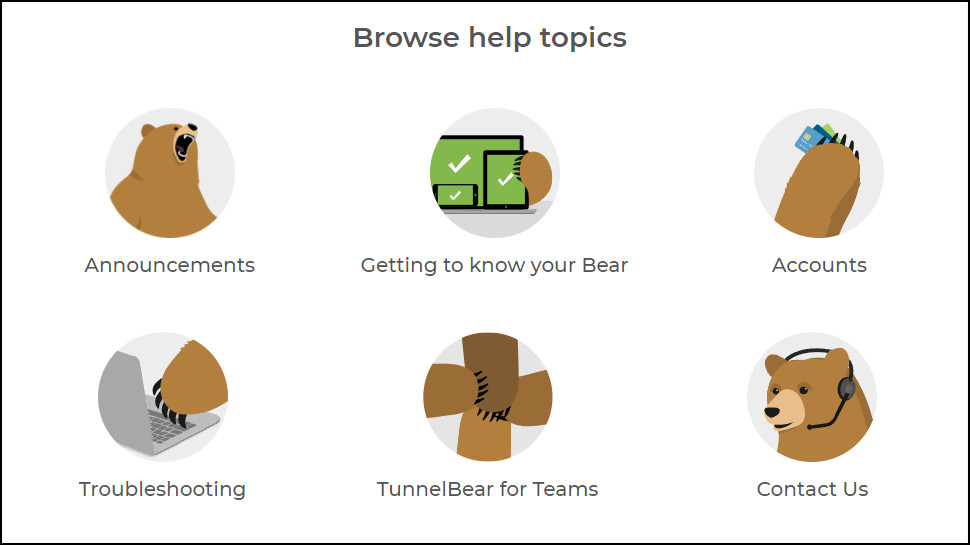
Support
TunnelBear support starts with its web-based help site. This is presented in a clear and simple way, with large icons pointing you to key areas (Getting Started, Troubleshooting, Accounts), and basic articles on the most common questions ('Why should I trust TunnelBear?', 'Why can't I access the content I want?', 'Does TunnelBear keep logs?').
Go searching for answers and you'll find TunnelBear's knowledgebase doesn't have a lot of content, but what you get is well presented and gives you a decent range of information. The Connection Issues page doesn't just offer generic 'reinstall'-type ideas, for instance. It links you to TunnelBear's Twitter page to look for service information, suggests trying out the service on another network, and points you to settings which might help.
Despite its beginner-oriented approach, there's also room for just a few more advanced tweaking ideas, with recommendations for ports which should be opened in some circumstances.
There's no live chat, but if you need more help, a Contact page allows you to send a message to the support team. We'd already noticed the Android app no longer had an option to change protocols, so fired off a question asking whether this was still supported. A reply arrived in less than an hour, and we quickly got into a conversation about the problem.
“Tap this, then this, and the option is there.” The support agent recommended. “It's not,” we replied.
“Uninstall and reinstall,” said reply two. We tried and installed it on two more devices. It made no difference
“What device and version of Android are you using?” Asked the agent.
We sent the details back immediately but had to wait a couple of hours before a reply finally explained that this was a known issue. It turned out that TunnelBear had removed the feature on later versions of Linux, and it wasn't available to anybody. All our troubleshooting efforts had been a complete waste of time.
There were some plus points to this exchange. The replies were quick, the agent was friendly, and he gave what would have been sensible advice (if the problem was on our system.) That's not unusual, TunnelBear's support has always generally delivered decent service.
This time, though, we're struggling to see how an issue as major as this, where a significant feature has been removed from an app in some situations, and support doesn't know about it.
Hopefully, we were just unlucky, but this doesn’t look good.
TunnelBear review: Final verdict
It's not the largest, fastest, or most powerful of VPNs but TunnelBear's ease of use and strong focus on opening up its systems to scrutiny deserve a lot of credit. If you're looking for a gentle start to VPNs, or are tired of apps that are crammed with features you never, ever use, then TunnelBear could be a smart choice.

Mike is a lead security reviewer at Future, where he stress-tests VPNs, antivirus and more to find out which services are sure to keep you safe, and which are best avoided. Mike began his career as a lead software developer in the engineering world, where his creations were used by big-name companies from Rolls Royce to British Nuclear Fuels and British Aerospace. The early PC viruses caught Mike's attention, and he developed an interest in analyzing malware, and learning the low-level technical details of how Windows and network security work under the hood.