Researcher reveals official White House app is one command away from tracking your precise location every 4.5 minutes – app can also inject code to dodge cookie consent, GDPR banners, and paywalls
An analysis of the app's APKs reveals some concerning features
- An analysis of the official White House app has revealed some concerning features
- The app is capable of blocking cookie consent options, GDPR banners, and paywalls
- The app can track user's precise location every 4.5 minutes, and sends user data to non-governmental infrastructure
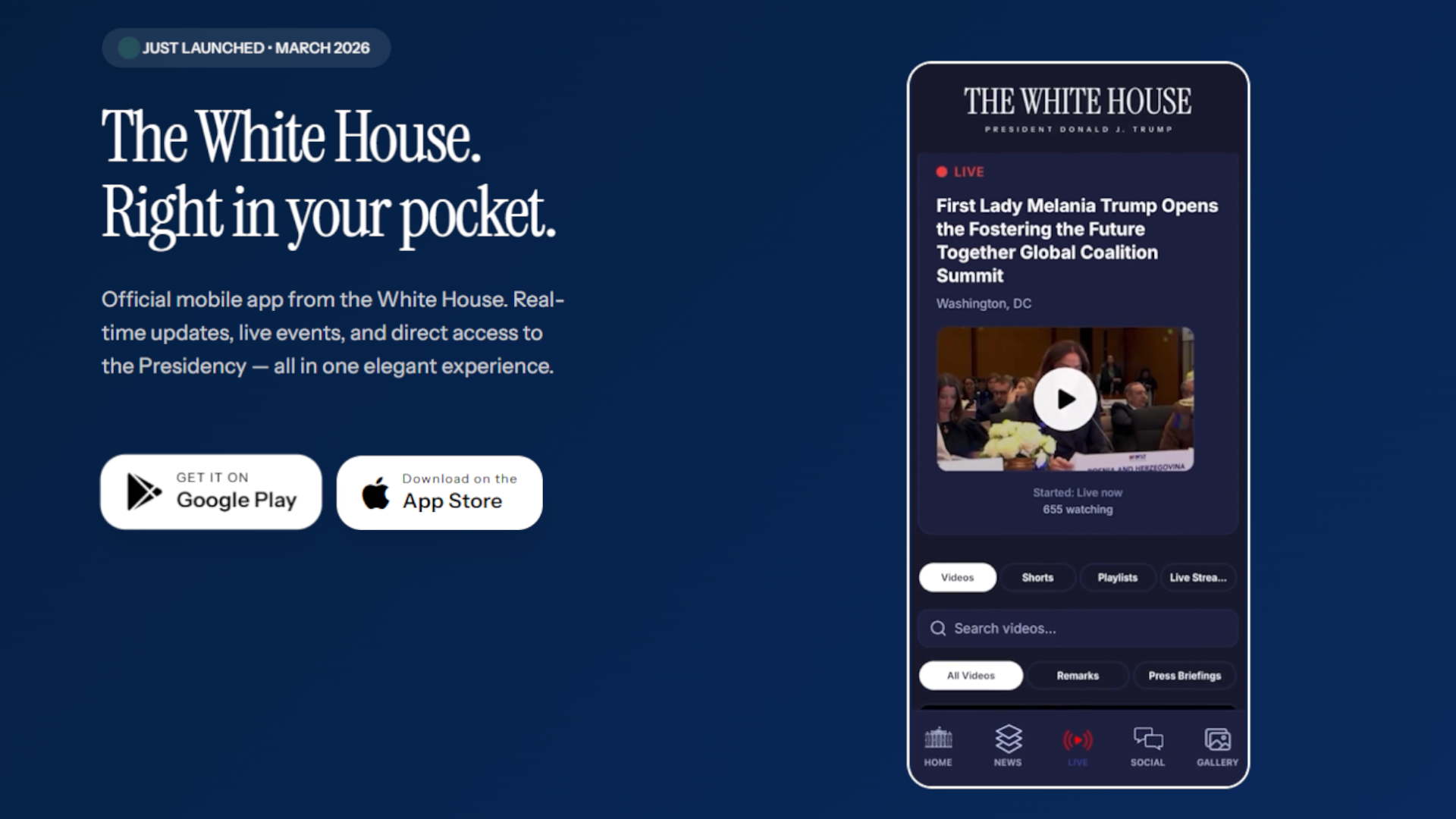
A security researcher has decompiled the new official White House app for Android that was released in March 2026, and has found some concerning features hidden inside.
Web developer Thereallo analyzed the app’s APK in a blog post and found it is capable of injecting code into third-party websites to hide cookie consent popups, GDPR banners, paywalls, and more.
It can also track your accurate GPS location every 4.5 minutes, pulls code from unsecured non-government infrastructure, and provides highly invasive profiling of every user.
Article continues below'A direct line to the White House'
When the White House released the new app, it said it “offers Americans a direct line to the White House,” but it looks more likely that the reverse is true.
Hidden inside the WebView used for opening external websites is a JavaScript snippet that has the ability to hide some fairly vital information typically displayed when you visit a website.
“An official United States government app is injecting CSS and JavaScript into third-party websites to strip away their cookie consent dialogs, GDPR banners, login gates, and paywalls,” Thereallo explained.
Blocking these core website functions means that users subject to GDPR or state-level privacy laws cannot exercise their legal right to opt-out of tracking. Furthermore, by circumventing paywalls, the US government is providing users with the ability to access content that is typically protected with a paywall.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
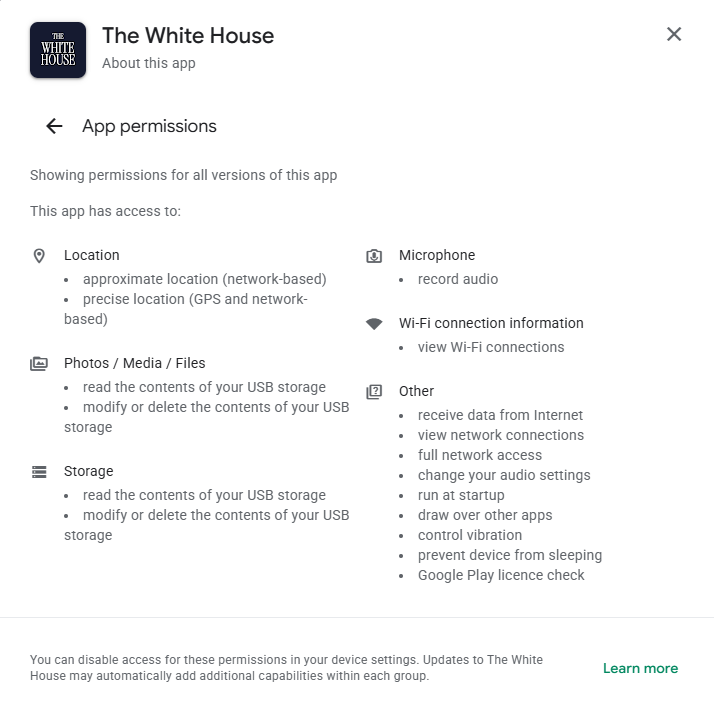
The Google Play Store listing states that the app can request approximate and precise location data, with Thereallo noting that the app requests location permission at runtime, and that the app contains an Expo plugin intended to strip location tracking. But the app instead relies on OneSignal SDK’s location tracking code.
The app can therefore collect accurate location tracking information every 4.5 minutes when the app is active, and every 9.5 minutes when the app is running in the background. While this tracking isn’t active by default, the entire process can be activated with a single command.
As Thereallo notes, “the infrastructure is there, ready to go, and the JS API to enable it is referenced in the bundle.” So while the app may not necessarily be tracking you today, it has the potential to be activated at any point in the future.
OneSignal is also used to collect profiling data on every user. “Your location, your notification interactions, your in-app message clicks, your phone number if you provide it, your tags, your state changes. All going to OneSignal's servers,” Thereallo notes.
Additionally, the app also relies on code from a random GitHub account to embed YouTube videos. Thereallo points out that if this account is ever compromised, the perpetrator could “serve arbitrary HTML and JavaScript to every user of this app.”
The app also loads third-party code without adequate security infrastructure, sends your data to non-governmental infrastructure, and has no certificate pinning.
“Is any of this illegal? Probably not. Is it what you'd expect from an official government app? Probably not either,” Thereallo concludes.
An app advertised as a one-stop-shop for news and media direct from the White House is instead functioning as a highly granular user profiling, tracking and marketing tool. It is important to note that Thereallo’s analysis was conducted immediately after the app’s release, and therefore features may have been modified, added or removed.
TechRadar Pro reached out to the White House for comment, but did not immediately receive a response.

➡️ Read our full guide to the best identity theft protection
1. Best overall:
Aura
2. Best for families:
IdentityForce
3. Best for credit beginners:
Experian IdentityWorks

Follow TechRadar on Google News and add us as a preferred source to get our expert news, reviews, and opinion in your feeds.

Benedict is a Senior Security Writer at TechRadar Pro, where he has specialized in covering the intersection of geopolitics, cyber-warfare, and business security.
Benedict provides detailed analysis on state-sponsored threat actors, APT groups, and the protection of critical national infrastructure, with his reporting bridging the gap between technical threat intelligence and B2B security strategy.
Benedict holds an MA (Distinction) in Security, Intelligence, and Diplomacy from the University of Buckingham Centre for Security and Intelligence Studies (BUCSIS), with his specialization providing him with a robust academic framework for deconstructing complex international conflicts and intelligence operations, and the ability to translate intricate security data into actionable insights.
You must confirm your public display name before commenting
Please logout and then login again, you will then be prompted to enter your display name.

 Become a TechRadar Insider
Become a TechRadar Insider






