What is Apple Private Relay and is it worse than a VPN?
Is Apple's shiny new privacy tool really a 'VPN killer'?
Sign up for breaking news, reviews, opinion, top tech deals, and more.
You are now subscribed
Your newsletter sign-up was successful
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
(Edit: This article has been updated with comments from various VPN providers)
Apple has announced several important new privacy features at its annual development conference, WWDC 2021. By far the most significant - and controversial - is 'private relay', a technology which enables users to browse the web without revealing their real IP address, making it more difficult for sites to track their web browsing activities.
The feature is one of several additions to Apple's upcoming iCloud+ account. Despite the 'Plus', existing iCloud accounts will be upgraded at no extra cost, which means you could benefit from the private relay feature from as little as $0.99 a month with 50GB of cloud storage.
This doesn't necessarily mean it's time to ditch your VPN subscription; far from that. There are a number of reasons for that, and we'll get onto those later, but one of the most important is that private relay won't protect all your traffic: it covers Safari, Apple’s web browser, and insecure connections only (apps which use HTTP rather than HTTPS.)
More crucially, the technology has other issues, too, which become clearer when you look under the hood.
- These are the best iPhone VPN services available
How does Apple Private Relay work?
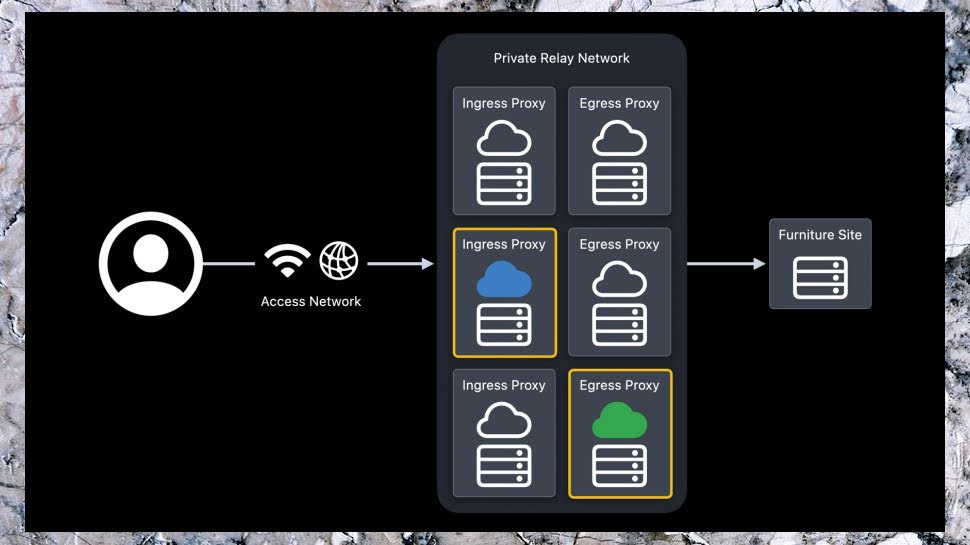
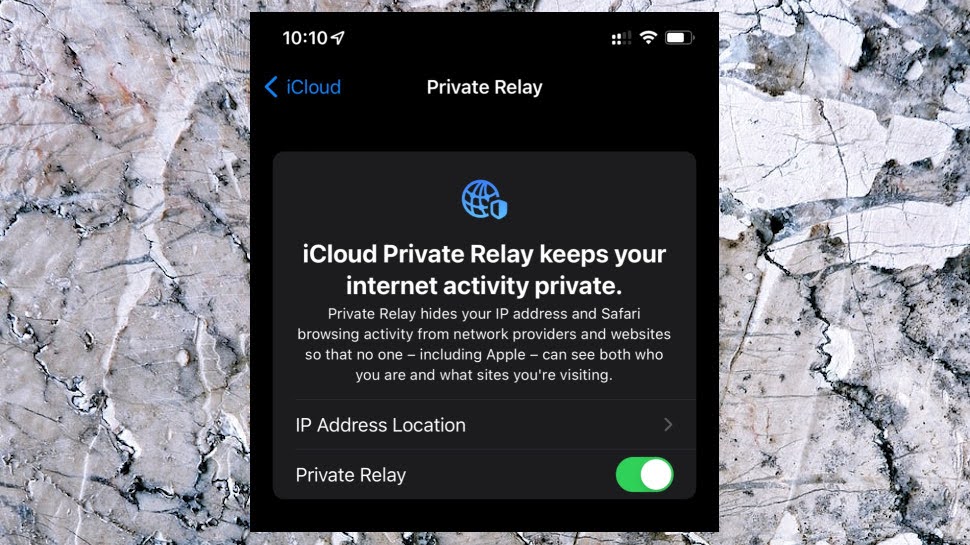
Private Relay is easy to use, with none of the app hassles you'll see with a regular VPN. Just sign into your iPhone, iPad or Mac with an iCloud+ subscription, enable Private Relay in your iCloud settings, and the technology starts shielding your Safari activities. When you next connect to a website, Private Relay randomly chooses two servers to handle your traffic.
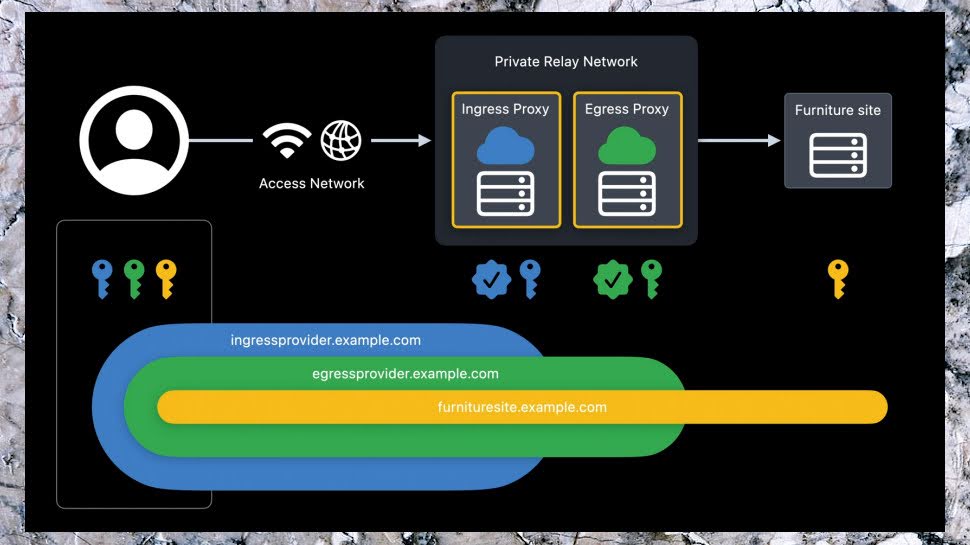
Your device makes a speedy and secure QUIC/ HTTP3 connection from the internet to the first server, the Ingress, run by Apple. The connection is authenticated via a technique called RSA Blinded Signatures, which allows you access without having to transmit a username, password, or any account details at all - no need to have the best password manager here. The Ingress Proxy doesn't even know which website you're visiting, as that information is encrypted on your device. Read our primer on proxy servers.
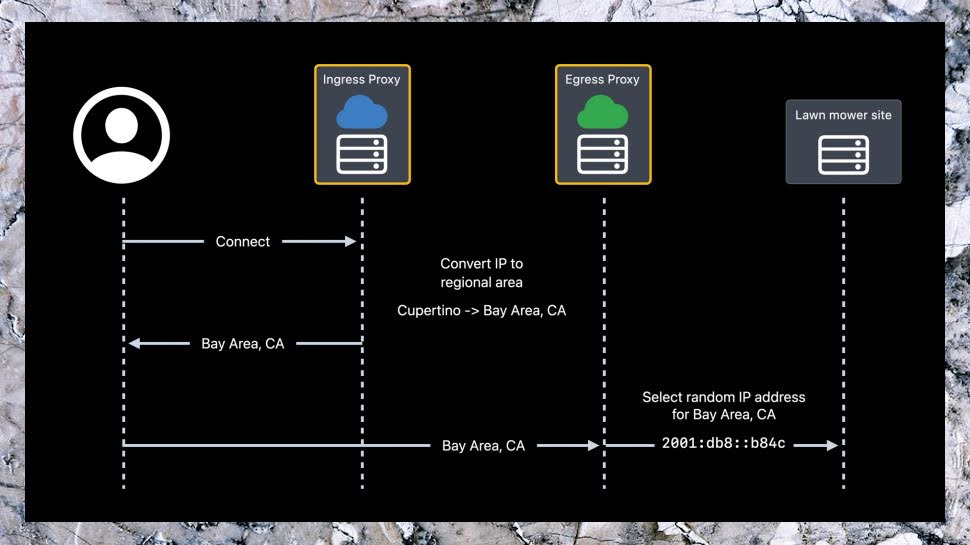
You could still be identified by your IP address, so the Ingress Proxy replaces it with an approximate geographical location. If you've a Staten Island IP address, for instance, it might simply use 'New York. (You can alternatively tell Private Relay to choose an IP from your country and time zone, giving it a much wider pool of IPs to choose from.)
The Ingress Proxy now makes an encrypted connection to the Egress Proxy, passing it your request. This second server is run by an independent content provider, not Apple and likely to be a partnering CDN provider, ensuring it has no way to figure out who makes any particular request.
The Egress Proxy then decrypts your request, to find out which website you're visiting. This is the separation of knowledge which preserves your privacy: the Ingress Proxy knows a little about who you are (your IP address), but not what you're doing; the Egress Proxy knows what you're doing, but nothing about who you are.
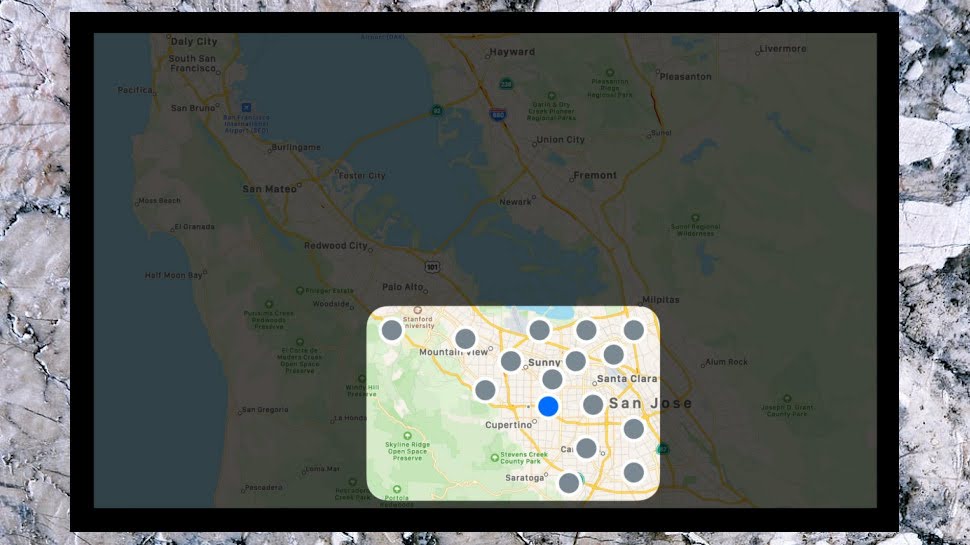
The Egress Proxy doesn't know your IP address, but it has to pass something to the website you're trying to visit, to ensure it can display localized content. To make this happen, the Egress Proxy looks at the approximate location it's received ('New York'), and allocates you a random IP address from a pool in your approximate area. 'Manhattan? That'll do.'
This approach allows websites to have enough of an idea of your location to display relevant content, but not to identify you. The IP address they see changes every time you visit, and your real IP is never revealed. All they know is the connection was made via the Egress Proxy, so they pass their content back in an encrypted form to that address, and it's routed back to the Ingress Proxy, and then to you.

The Private Relay network
Sign up for a VPN and you'll want to check out all kinds of details about the network: how many servers it has, how many locations, who runs them, and more. Unfortunately, Apple hasn't released any details at all, not even who is running the website-facing side of the network, but other sources provide some major clues.
Users running Private Relay on the iOS 15 beta have reported that they're allocated Cloudflare IP addresses, for instance, a strong indication of at least one provider.
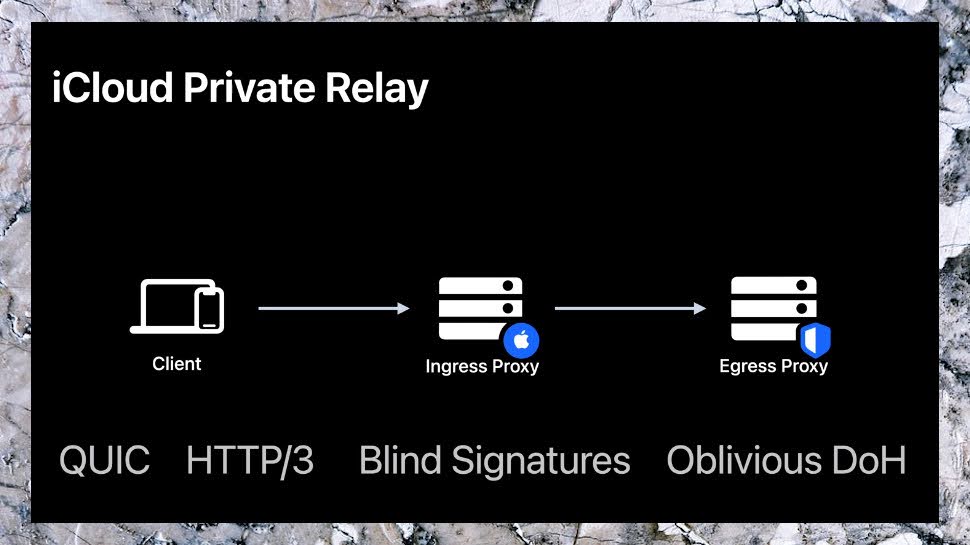
There's another clue in an Apple developer video, which explains that Private Relay uses 'Oblivious DoH' (ODoH.) This is a new DNS standard which encrypts requests to ensure that when you connect to Private Relay, the first server (the Ingress Proxy) can't see the website you're trying to access. It's a brand new technology developed by Apple, Cloudflare and Fastly, another big CDN provider who would make a lot of sense as a Private Relay partner.
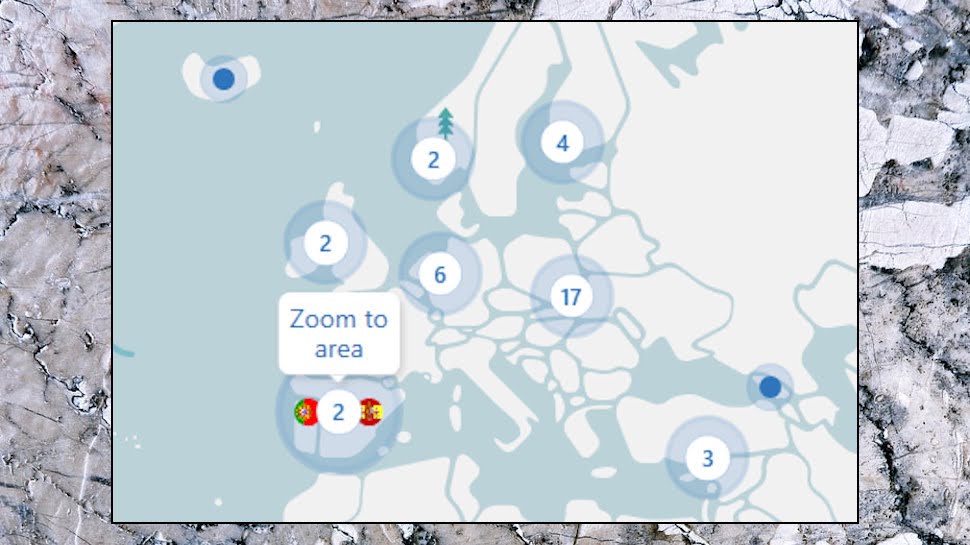
A recently published report speculates that Akamai is Apple's third provider, and suggests the Private Relay link is behind a rally in the share prices for all three companies. If this is true, it's good news.
These are CDN giants - Akamai alone has 300,000+ servers in more than 130 countries - and adding Cloudflare and Fastly to the mix should ensure you're never far from a Private Relay server. That’s one or two orders of magnitude higher than any VPN provider out there.
Can you trust Apple Private Relay?
Private Relay's design looks good to us, but is it good enough? Tor also uses a system where your connections are routed through multiple relays. But while Apple stops at two, Tor defaults to three, and there can be many more. These are all run by volunteers, too, greatly reducing the chance that any one person can track what you're doing, and we've seen arguments that this makes Tor safer than Private Relay.
That sounds reasonable in theory, but there's a problem. Having Tor's servers provided by volunteers rather than big business might sound appealing, that doesn't make them any more trustworthy. Security researcher nusenu has been tracking Tor relays since 2020, and a recent blog post reported that '25% of the Tor network’s exit capacity has been attacking Tor users' using various attacks.
Private Relay's two-server approach, where Apple always controls the Ingress Proxy, a second big corporation runs the other, could still be seen as a problem. If you don't trust either of them, you're probably not going to be impressed by Apple's privacy promises.
It's likely that everyone running Private Relay will be under US jurisdiction, too, and we've seen user concerns that any anonymity will disappear just as soon as the first warrant or subpoena arrives.
Is this realistic, though? Apple isn't just promising not to log, it's saying the design makes that impossible. The Ingress Proxy doesn't know who you are beyond an IP address, or which site you're trying to access, so there's no way for Apple to spy on you; the Egress Proxy knows the site, but nothing about you, not the IP. Only your device knows everything.
You don't have to automatically trust Apple to realise the impact on its reputation if this turns out to be wrong, and it really does hand over user data as soon as it's asked. It would be goodbye to any claims of privacy expertise, and the greatest gift to Google and Microsoft they could ever give. No-one can know for sure, but it seems to us that's a very big incentive for Apple to be very, very, very sure that Private Relay works as promised.
- Also check out the best Mac VPN
A look at the performance of Apple Private Relay
Using Private Relay requires more encryption and routes your traffic through two extra servers before it reaches its destination, which suggests there's going to be some performance hit. But Apple has said there will be minimal speed impact: can it be right?
If your ISP throttles some traffic types - video, say - then the extra encryption bypasses that, immediately improving speeds. Private Relay's use of the speedy UDP-based HTTP/3 is a plus, and should help compensate for the extra server hops.
And while passing your traffic through two extra servers must affect speeds, Private Relay isn't like a regular double-hop VPN, where maybe one cheap VPS server in a data center somewhere connects to another.
CDN providers like Cloudflare and Akamai use powerful hardware, smart routing and all kinds of other technologies to shave off milliseconds here and there, and that will keep any overheads to an absolute minimum. Delivering data securely and with as little lag as possible is what they do.
Put it all together and we expect to see some speed impact, though less than you'd get from a VPN. There are lots of factors to consider, though - your location, demand on nearby servers, your device and network - and we'll have to wait until release date to find out for sure.
What are the advantages of Apple Private Relay?
Private Relay improves on VPNs in a number of ways.
Building it into the operating system reduces any technical hassles. You don't need to run an app, figure out which settings work best, or remember to connect before you do anything sensitive. Sign up for iCloud+, check a box to turn the technology on, and it just works.
The two-server approach, each run by a different company, means you no longer have to trust that your provider is living up to their privacy promises. A VPN server gets your account details when you authenticate, and then gets to see everything you're doing online, making it very easy to log your activities.
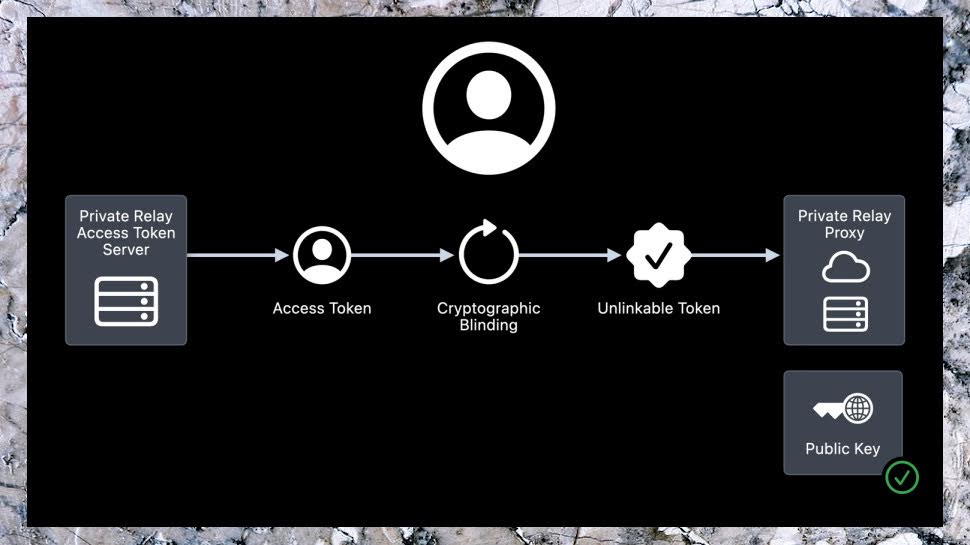
With Private Relay, Apple can't associate an internet action with an account, so it's unable to log what you're doing. And all your destination website sees is the randomly selected Egress Proxy IP address, leaving no way for any internet action to be connected back to you.
We're glad to see Private Relay encrypt DNS and protect insecure HTTP connections by default. Most VPNs do the same, but it's good to know these potential data leaks will be plugged.
We can't describe Private Relay's Safari-only protection as anything other than a weakness, but it does have one positive side: it won't cause issues with banking, payment or other apps which might complain if you're using a VPN. (Safari traffic may still be blocked by PayPal and others, as they're looking to use IP addresses as a record of identity, but we'll have to wait and see if Private Relay is more or less affected than VPNs.)
You don't have to choose between using Private Relay or a VPN, though: you can run both. Apple explains that 'if your app provides a network extension to add VPN or app-proxying capabilities, your extension won't use Private Relay and neither will app traffic that uses your extension.' Proxy traffic also ignores Private Relay, and your apps work just as they did before.
What are the limitations of Apple Private Relay?
While Private Relay is technically very smart, it's all about security and privacy, and it's never going to fully compete with a commercial VPN.
There's no option to choose another location, for instance. And that's by design. Private Relay chooses the location of your Ingress and Egress Proxies, and it's those servers working together who get to decide your eventual IP address. There's no way to do that within the existing system.
It doesn't look like this will change in the future, either. An Apple developer session stated: 'Private Relay guarantees that users can't use the system to pretend to be from a different region, so you can continue to enforce region-based access restrictions.' An issue for users, but it makes sense for Apple.
The company wants to work with content providers, not alienate them by providing ways to bypass their regional blocking schemes. It is a major content producer itself and the last thing it would want to do is become the go to VPN for Netflix.
Reuters highlighted a similar issue at the country level, reporting that Apple's new service won't be available in Belarus, China, Colombia, Egypt, Kazakhstan, Saudi Arabia, South Africa, Turkmenistan, Uganda and the Philippines.
If you're hoping to use Private Relay to get online from some VPN-unfriendly country, be prepared for disappointment. Don't expect that to change in future, either - Apple isn't going to compromise its China revenue by encouraging the breaking of Chinese law.
Keep in mind, also, that although Private Relay shields your real IP address, a website or network can still check that IP and see it relates to a Private Relay hostname. If you currently use a VPN to bypass network-level blocking policies on public Wi-Fi, Private Relay may not help, at least not for long. All any network admin has to do is block Private Relay's hostnames, and Apple is already explaining how that's done.
If you think Private Relay might bypass parental control services, that's unlikely to work, either. The technology allows content filters to inspect traffic before it travels through Private Relay, so they'll block all the same content as before.
Even where Private Relay does match a regular VPN, for normal browsing, it can't protect you from all tracking. If you sign into a web account or just accept cookies, for instance, the site already knows who you are. Private Relay isn't a complete privacy solution, and you'll still need to use features like private browsing and optimise Safari's privacy settings to keep yourself safe online.
How does Private Relay compare to other privacy solutions?
Proxies are poor, rating perhaps a lowly 2 out of 10 on our made-up privacy scale. They hide your IP address by routing your traffic through another server, a welcome plus. But you must set them up on every app where you'd like to use them (if that's possible at all), they don't encrypt your traffic, and a malicious server operator can see a lot, maybe all of what you're doing.
Tor is significantly better, encrypting your traffic and routing it through multiple randomly selected relays to conceal your IP. But various Tor weaknesses - including slower speeds - and attack vectors have appeared over the years, and headlines like '25% of the Tor network’s exit capacity has been attacking Tor users' suggest you really shouldn't trust it entirely. We'd still rate it 5/10.
VPN works system-wide, encrypting all your traffic by default, and allowing you to choose an IP address from one of many countries around the world. But you're placing all your trust in a single provider, and if a VPN wanted to log your internet activities, it could do that. And even if a VPN proves it's completely trustworthy, there may be scope for a hacker to gain useful data on users. We'll score VPNs 7/10.
Private Relay is (mostly) Safari only, but it does a great job of hiding your IP, and as no one entity knows who you are or what you're doing, there's no way for anyone to connect your account to any internet action. As our rating is about privacy more than features, we have to edge Private Relay in front with a score of 8/10. (Yes, VPNs can protect all your devices, but if they're all vulnerable to logging, that's not a big privacy plus.)
What would a 10/10 look like? Private Relay levels of protection for all your apps and devices would help, ensuring you're covered whatever you're doing. We'd like some transparency on the low-level details of how Private Relay works, too, so that others can take a view on how well the system works. The technology has only just been released, though, so there's likely a lot more information to come. We'll take a closer look when it arrives.
What comes next for Apple Private Relay?
Private Relay doesn't begin to deliver the features you'd get from a full VPN, but that's not what the system is designed to do. The technology is focused on improving your privacy, not breaking existing company and regional restrictions, and in many ways that's a plus. If Private Relay could be used to unblock various platforms, many companies would simply block its IPs, and that's no benefit to anybody. By living within the rules, rather than breaking them, Private Relay should stay working in more locations.
There's certainly scope for some improvement, though, most obviously in which traffic is protected. Making Private Relay a (mostly) Safari-only thing is a big plus for the browser, but it's hard to see it lasting long-term, and the service makes most sense as a technology that works system-wide.
Wherever Apple goes with Private Relay, it already outperforms the operating system competition. Right now, the best Google can offer is its VPN by Google One, for instance, a very standard US-only service which doesn't begin to match Private Relay for privacy. Google, Microsoft, maybe even Amazon are going to have to come up with some major privacy innovations of their own if they want to compete (leave Facebook out of the equation because… well, it didn’t go down well with Onavo).
In the long term, if the top operating systems and devices begin moving into the VPN space, that puts pressure on specialist providers to up their game.
The top VPNs have many more features, for instance, but if even a few users feel they don't need anything extra to protect their iDevices, that might leave them questioning whether it's worth buying a subscription to cover anything else. Providers may have to drop their prices to keep users on board.
The real issue is trust, though. With Private Relay designed to guarantee that no one provider can see what you're doing online, VPN website promises that 'we don't log, honest' look more unconvincing than ever. Will even no-log audits convince an ever more skeptical user base? It'll be interesting to find out. Watch this space.
So what do VPN Providers think of Apple's Private Relay?
NordVPN says : "Private Relay is part of Apple’s continued effort to foster a privacy-oriented operating system, but there will still be some caveats, and that is where solutions such as NordVPN will thrive.
Apple says Private Relay hides a user’s traffic from ISPs, advertisers, and even Apple itself. While there are similarities, when you turn on a VPN (Virtual Private Network) on your computer, smartphone, tablet, smart TV, or even router, it protects your data by putting everything you do online through a tunnel.
Private Relay is available only on Safari. This means Apple users who stick with Chrome or Firefox are not utilizing Private Relay whatsoever. Instead, these users will begin or continue to rely on VPNs like NordVPN. So unless you fully trust your data privacy, traditional VPNs such as NordVPN are still the go-to.
Although Apple does not appear to offer full-fledged VPN features, it will become the first step towards cybersecurity for many users who wouldn’t have considered taking action otherwise. I’d say that this will boost cybersecurity awareness in general, and this is a big win for the whole industry.
Additionally, big tech entering the VPN market suggests the solidity and importance of the industry. Tougher competition raises standards and this is something users will benefit from.
Finally, tech companies stopped treating digital privacy and cybersecurity in the narrow sense of the words. NordVPN is also taking a step forward by offering the password manager NordPass as well as the file encryption tool NordLocker, which also has a cloud storage add-on. In the future, we might offer additional antivirus-like features."
- Also check out our complete list of the best VPN services
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!

Mike is a lead security reviewer at Future, where he stress-tests VPNs, antivirus and more to find out which services are sure to keep you safe, and which are best avoided. Mike began his career as a lead software developer in the engineering world, where his creations were used by big-name companies from Rolls Royce to British Nuclear Fuels and British Aerospace. The early PC viruses caught Mike's attention, and he developed an interest in analyzing malware, and learning the low-level technical details of how Windows and network security work under the hood.
 Become a TechRadar Insider
Become a TechRadar Insider






