Latest Pro News

Want to back up your iPhone securely without paying the Apple tax? There’s a hack for that, but it isn’t for everyone... yet
By Wayne Williams published
Want to back up an iPhone locally without iCloud fees? A small Linux-powered device offers encrypted USB backups but you've got to put in the work to set it up.
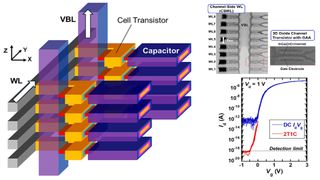
Crying over expensive RAM? Kioxia may have cracked the 3D RAM puzzle, paving the way for cheaper, faster memory — but it probably won't reach the market till the next decade
By Efosa Udinmwen published
Kioxia develops eight-layer stackable oxide-semiconductor transistors for 3D DRAM - yet commercial deployment remains years away.

World's smallest AI supercomputer achieves world record with 120B-parameter LLM support on-device — what I don't understand, though, is how it does OTA hardware upgrades
By Efosa Udinmwen published
Tiiny AI Pocket Lab is a pocket-sized Mini PC running large language models offline with optimized CPU and NPU performance.

Talk about a snappy attack - popular photo booth maker allegedly leaves user images at risk
By Sead Fadilpašić published
Photos taken at booths get uploaded on the internet where they can easily be downloaded.

A water-cooled AMD AI 14-inch tablet with 16 CPU cores, a 5060-class GPU, and 128GB RAM is exactly what I need for Christmas — I don't think it will cost less than $2000, though
By Efosa Udinmwen published
OneXPlayer’s Super X is a 14-inch hybrid tablet-laptop with AMD Ryzen AI Max+ 395, 128GB RAM, and liquid cooling.
Latest Pro How To's

Optimizing for online sales: Your insider guide to Black Friday success
By Owain Williams published
Want the best Black Friday/Cyber Monday ever? We asked these experts to share their strategies for online sale success this year.

How to pick a website builder for your agency: I asked 6 experts
By Owain Williams published
Picking the right website builder is a key factor in agency success. So, I asked the experts how you can find the right one for you.

How to create an online store
By Ritoban Mukherjee last updated
A comprehensive guide to help you research, create and launch your first online store.
Latest Pro Reviews

Idea Spectrum Realtime Landscaping Pro 2025 review
By Steve Paris published
Create a virtual garden from the comfort of your Windows PC

Boulies OP180 office chair review
By Steve Clark published
The OP180 sits neatly in Boulies' Office Professional line-up ideal for office spaces with multiple users.

Creatio CRM Review 2025
By Ritoban Mukherjee last updated
Highly customizable no-code CRM for specialized businesses

Doogee S200 Ultra rugged phone review
By Mark Pickavance published
The Doogee S200 Ultra is yet another evolution of its S200 line of rugged smartphones