Sign up for breaking news, reviews, opinion, top tech deals, and more.
You are now subscribed
Your newsletter sign-up was successful
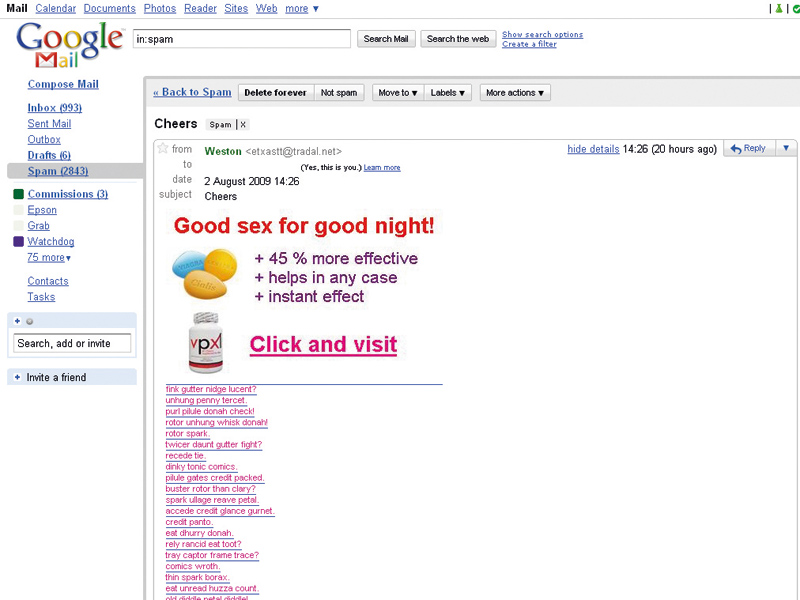
Your inbox is full of mail that casts aspersions on your man/ladyhood, wants you to buy prescription drugs online or promises to show you how to make money fast.
Latest figures from McAfee suggest that a massive 92 per cent of all email is spam. That's a lot of luncheon meat.
What's more, 67 per cent of American email users say that junk mail actively puts them off going online at all. Those aren't good statistics for 'email marketers'. So, who's doing it? There's no easy answer.
Article continues belowSpam is delivered by many dubious characters, from email harvesters to black-hat marketers. We've delved into the murky world of the spammers to find out more.
Taking names
Spam begins and ends with lists. First, there are the mailing lists that spammers use, which are culled from a variety of sources. These can be compiled in one of three basic ways.
When you're prompted to enter your email address into a form, the company behind it will be using that data to build a mailing list. Less-reputable outfits may sell that information on.
Sign up for breaking news, reviews, opinion, top tech deals, and more.
Then there are automated search spiders that crawl the web, harvesting email addresses from a variety of sources. They slurp up names from personal websites, forums and social networks – anywhere that email addresses are on display.
The third tactic is a more brute-force technique that's akin to the tactics hackers use to crack passwords. Lists are automatically generated for popular domains using word and number combinations. In any of the above examples, the populated lists may then be used by the spammer or sold on for profit.
There are companies that claim to sell 'opt-in' mailing lists – email addresses for folks who apparently enjoy a bit of spam with their eggs in the morning. Email marketing expert Mark Brownlow disputes the legitimacy of such outfits.
"With very, very few exceptions, purchasing a bulk list like this is a shortcut to email marketing hell," says Brownlow, webmaster at www.email-marketing-reports.com. "If somebody offers to sell and send you a bulk list of email addresses, 99 times out of 100 you're getting a spam list."
Spammers even have tactics to refine the targeting and accuracy of these lists. For example, a marketer will buy a list of email addresses from the kind of dodgy source we've already discussed.
WATCHING THE SPAMMERS: The Spamhaus Project tracks spam activity and provides a blacklist for the internet community
At the bottom of the spam advertising message there'll be a paragraph of legal-sounding jargon saying that the sender is acting within the law because you opted to receive their advertising – even if you didn't. Below that will be a link enabling you to 'opt out' of receiving messages in future.
However, when you reply using that link, you're simply confirming to the spammer that your email address is live. If your mail client previews HTML messages, you may not even need to click a link to confirm your existence. A 'web bug' – an embedded bit of code in the email – can do that automatically.
An even sneakier technique used to confirm that an address is active is when the spammer sends a blank or nonsense message. How do the spammers use these to confirm that addresses are live? Non-functioning email addresses generate bounce messages.
In this case, the same automated program used to send out messages also collates bounced replies and strikes unsuccessful attempts off the list. The result is a more valuable commodity: a list of guaranteed live addresses.
The fight against spam is similarly replete with lists: lists of the countries that generate the most spam, lists of websites that spam directs its victims to, lists of banned IP addresses from which junk mail originates, lists of those responsible. These lists – the black lists banning senders and the white lists that allow them – are all that really stands between us and them.