How to get secret service grade security
So Wi-Fi is iffy – what about the phone? Sadly, no self-respecting spy should consider it. In the UK, the Regulation of Investigatory Power Act (RIPA) and the Data Retention Directive force phone companies to keep records of calls and texts for a year, and give wire-tapping rights to dozens of government departments.
In the US, the Windows-based DCS-5000 system combines point-and-click monitoring of voice calls with location-tracking via mobile phone towers, plus DVR-like recording and playback. It can be set up to eavesdrop and track any landline or mobile phone in the country within seconds.
Don't think you can rely on new smartphone security apps, either. Philip Zimmermann is a computer security guru and the creator of PGP (Pretty Good Privacy), the world's most widely used email encryption algorithm. He says, "Mobile phone encryption only works up until the point where it hands over to the voice network. At some point, there's a gateway between the data and voice parts of the phone network, where a wiretap becomes possible."
Using voice over IP (VoIP) services may be more secure, but Stephen Bellovin says it depends on which service you use: "A lot of VoIP products don't encrypt, even though it's in the [widely used] SIP standard. However, Skype uses very strong cryptography and the best thing is that people don't have to worry about it – it just works."
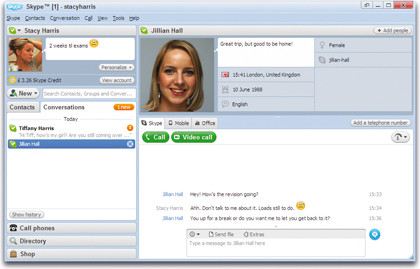
Zimmermann is more sceptical. "Skype encrypts, but we don't know how, so it's hard to evaluate the quality of the encryption," he told PC Plus. "I don't hear a lot of complaints from governments about their citizens using Skype. The oppressive governments around the world seem fairly happy with it." Which is as good a reason as any for spies to avoid it.
Zimmerman has his own solution: an open source voice and video encryption protocol called Zfone that works with SIP VoIP systems such as Google Talk and Apple iChat. When Zfone is running on two computers, they negotiate a strong encryption key in a peer-to-peer fashion. This means there are no public keys, certificate authorities or trust models. When the call ends, the key is destroyed. A new version of the (free) Zfone software will be released shortly.
Digital forest
Sign up for breaking news, reviews, opinion, top tech deals, and more.
Secure phone calls can be handy for arranging to meet 'the swift hawk by the silent pond at midnight' (pre-arranged pass-phrases help confirm who you're talking to), but they're less useful for passing on gigabytes of data. And if you're venturing into the digital world, the smart spy knows that the best place to hide a tree is in a forest.
Every day, three billion email accounts send and receive over 300 billion messages. Surprisingly, email is fairly secure according to Philip Zimmermann. "Even if you don't encrypt your mail, your mail server might encrypt it when it sends it to another mail server. The two servers can have an SSL (secure socket layer) connection between them – the same protocol your bank uses to communicate with your web browser."
You'll want to bump up security, perhaps with Zimmermann's own PGP, although this can be tricky to use. Hushmail removes the hassle, enabling you to send private emails via SSL to other Hushmail users – or even to normal email addresses using a question and answer combination.
"The best public scientific knowledge suggests that it would be impossible to decrypt our emails with current technology," explains Ben Cutler, CEO of Hush Communications. "However, it's likely that Hushmail messages have been intercepted by other means. For example, a customer doing human rights work in Eastern Europe reported certificate warnings when accessing our website. We determined that someone was trying to eavesdrop on the connection between his computer and Hushmail by proxying his computer's network traffic. Fortunately, he heeded the warning and avoided the attempt."
Of equal concern to secret agents should be Hushmail's willingness to deal with law enforcement. Hushmail has been forced on several occasions to hand over plain-text copies of emails, including those of US National Security Agency (NSA) whistleblower Thomas Drake. Ironically, Drake was intending to show reporters details of two failed NSA programmes, code-named Trail Blazer and Thin Thread, designed to check billions of phone calls, emails and chats for potential espionage and terrorist threats.
Another problem with encrypted emails is that they stick out like sore thumbs amid the sea of spam, automated messages and Facebook updates that comprise most email traffic. Professor Bellovin sums it up:
"If the FBI or MI6 see encrypted messages going from the US or the UK to known addresses in Moscow, they'll get suspicious and start investigating."
Hiding in plain sight
What a shy spy needs is a way of communicating with handlers without it even looking as though a message is being sent. And here's where things get really interesting, because the Russian illegals in America were all supplied with custom steganography software.
Steganography is the art of hiding not just the content of a message, but the existence of a message itself. The Russian software enabled the agents to insert a hidden file into an innocuous-looking image, such as a photo of Anna Chapman in a bikini. That image could then be attached to a normal, unencrypted email or even posted on a website for the world to see. Only its intended recipient would be able to extract and decrypt its payload.
However, image steganography has its limitations. Steganographic communication only works as long as no one suspects its existence, and sending a large batch of stolen documents could mean a conspicuous series of photos flying back and forth to Moscow.
Forward-thinking spies should consider network steganography, where secret data is concealed in the ebb and flow of data online.
Elzbieta Zielinska is a researcher in the Network Security Group at the Warsaw University of Technology. Her team has succeeded in using VoIP services to hide a stream of steganographic secrets. "We've tested it and proved it to work," says Zielinska. "You can modify the delays between packets so that certain packets are dropped at the receiver. This might escape the attention of the people talking, but those dropped packets can carry just about anything."
The Warsaw researchers have found ways to inject steganographic information into everyday web traffic, potentially turning Flickr and Facebook into ultra-secure data channels. They even have a system called HICCUPs (Hidden Communication System for Corrupted Networks) that can embed concealed files in Wi-Fi networks by modifying wireless packets' check sum data.
Underground video
Surely tinkering with individual packets results in glacially slow bit-rates? Not so, says Zielinska. "We came up with the idea of using steganography at the physical layer of an Ethernet network, where packets are often padded out with zeroes," she says. "Introducing network steganography here gives data rates sufficient for a decent quality MPEG-4 video stream. There are no limitations." If only that were true.
The truth is that all 'secure' communications systems have one major limitation: you and your fellow secret agents. Any encryption technology is only ever as strong as its weakest user.
As Steven Bellovin says, "You don't go through strong cryptography – you go around it. If I want to read someone's email, I'm not going to try to break strong cryptography, I'm going to hack into their desktop and wait until they decrypt it."
Cutler admits that Hushmail users are rarely as reliable as his algorithms. "We've had people getting their passphrases stolen by Trojan horse programs, installed by users who are unaware of what they are or by computer viruses," he says.
Philip Zimmerman agrees. "Once a computer is compromised, all bets are off," he says. "Spyware can capture keystrokes while you type your pass-phrase or decrypt your key and send it to the mother ship. As long as you're using general purpose computers that can be used to download games, open attachments and visit porn sites, you're going to have this problem."
There's only one thing for it. Spies like us – and the hapless Russian illegals – are just going to have to disconnect from the grid, unplug our computers, break out the invisible ink and start studying cipher books. The condor will see you at the queen's castle.

 Become a TechRadar Insider
Become a TechRadar Insider







