Growing threat
It's not difficult to see the criminal appeal of botnets. Once the C&C servers (usually also hijacked) that each infected machine will contact to receive its orders are established, to make money, botmasters need to build, secure and maintain the biggest botnet possible.
The emergence of social networking has helped them immensely, aided by some specialised botnets. "Some botnets have particular purposes," says Ferguson. "Koobface is a great example of that. It's designed to be spread through social networks and is aimed purely at stealing social networking credentials."

Compromised social networking accounts are then made to post links to malicious websites. Each can result in hundreds of new infections as friends absent-mindedly take the bait.
But creating a new botnet also attracts the attention of botnet hunters, and so the overall structure of botnets has also had to quickly evolve in an ongoing game of cyber cat and mouse.
"Conficker is a prime example of how botnets now use peer-topeer communication channels to receive instructions, without requiring a communication channel that leads directly to the operators," reveals Jeff Horne, Director of Threat Research at Webroot. "Effective P2P botnet communication makes the operators more difficult to track, making it an obvious technique to be deployed in future botnets."
Electronic techniques aren't the only ones being employed, though. According to David Harley, Senior Research Fellow at ESET, techniques such as 'cutouts' (human go-betweens that break the electronic trail that links online criminals) betray the involvement of ex-spies.
Get daily insight, inspiration and deals in your inbox
Get the hottest deals available in your inbox plus news, reviews, opinion, analysis and more from the TechRadar team.
"There is some indication that organised crime ... especially in Eastern Europe, has indeed provided an opportunity for dishonest toil for ex-spooks. In China, too, there are indications of links between hacker groups and the military."
Botnets can also evolve at bewildering speed in order to take advantage of new online technologies. An example is the Twitter-based botnet discovered last year by Jose Nazario of Arbor Networks.
"Basically, what it does is use [Twitter] status messages to send out new links to contact," he says. "These contain new commands or executables to download and run."
With a shift in computing towards becoming more mobile, will the botnet menace also evolve in the same direction? "I think so," says David Emm of Kaspersky Lab. "We're seeing the beginnings of that threat, but I think the thing that's missing with mobiles is that people aren't routinely using them in the same way they would a laptop.
"I do online computing, but I don't use my smartphone to do it, so we're not in a position where people are reliant on them for moving money around and making financial transactions. I think when they are, that's when the floodgates will open."
However, Emm also believes that diversity will help slow the spread of mobile botnets. "There are also some braking factors involved," he says. "On the desktop and laptop platforms, Windows is king. Therefore, as a malware writer, I'd write for Windows and know I'd get a big hit. If I write something for Symbian, it won't work on Mac OS. If I write something for Mac OS, it's not going to affect Windows Mobile."
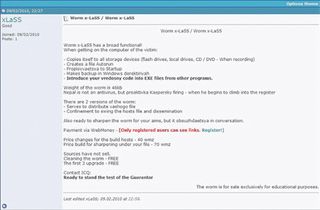
Building new botnets has also become easy for non-computer literate criminals. "Botnet creation kits and control consoles permit someone with little or no programming knowledge to create and control botnets," says Horne. So are these applications edging towards becoming products in their own right?
Ferguson says: "They are products, but how big the market is, it's difficult to say." An example of how easy it is to build a simple botnet is a new construction kit called TwitterNET Builder. "All in all, a very slick tool, and no doubt script kiddies everywhere are salivating over the prospect of hitting a website with a DDoS from their mobile phones," says Christopher Boyd of Sunbelt Software in a blog entry about TwitterNET Builder's existence.
With TwitterNET Builder, all the budding botmaster needs to do is enter the name of a Twitter account that infected machines must monitor for commands, and then press a button. The software creates a custom executable. The botmaster then sends the executable to victims to infect themselves. He then posts plain text commands such as 'Visit' to the Twitter account to have the zombies repeatedly visit a page for the purposes of click fraud, or 'Download', which makes them download new payloads.
Criminals who don't want to pay for state-of-the-art botnet software are increasingly pirating it. This has led to a curious situation, exemplified by the latest version of the Zeus botnet builder software.
"The author has gone to great lengths to protect this version," say Kevin Stevens and Don Jackson, Security Researchers at SecureWorks Counter Threat Unit, in their online analysis. "The author of Zeus has created a hardware-based licensing system for the Zeus Builder kit that you can only run on one computer.
"Once you run it, you get a code from the specific computer, and then the author gives you a key just for that computer. This is the first time we have seen this level of control for malware."
Botnet kit authors are also cashing in with secondary modules. For $1,500, you can add the Backconnect module to your growing Zeus botnet. This enables direct connection to an infected computer for the purpose of logging in, perhaps to empty stolen bank accounts. When the authorities raid the computer's owner, they find nothing more than a hapless householder with an infected PC.
Current page: Botnets: The growing threat
Prev Page Botnets: The scale of the problem Next Page Botnets: Money and motivationMost Popular





