Best identity management solution of 2025
Prevent company data breaches

We list the best identity management software, to make it simple and easy to limit user access on your business network such as through Single Sign-On (SSO) authentication.
Identity management works by restricting employee access to tools, apps, and business environments to ensure they only have access to the things essential to their job. Therefore, in the event that their account is compromised, the attackers do not have excessive access to your business environment, reducing the risk of a data breach or ransomware attack.
The best identity management solutions should provide an easy way to manage your organization's credentials, while not introducing additional friction to employee login. Many of the solutions on this list provide Single Sign On (SSO) authentication as well as password management tools to help your employees get access to the systems they need with ease.
To test the identity management software on this list, we checked how easy it is to set up new credentials, delete expired credentials, restrict access to certain apps and environments while also considering the ease of use, customer support, and cost. These are the best that passed the test:
We've also featured the best employee background check services.
The best identity management software of 2025 in full:
Why you can trust TechRadar
Best identity management software overall
Reasons to buy
LogMeIn offers a range of identity protection and SSO authentication solutions depending on your business size and needs.
LogMeIn Pro is focused on remote working, allowing employees to sign in securely regardless of location. This enables them to work on their own documents and files, either by themselves or in collaboration with teams, without comprising data access to the rest of the business.
LogMeIn Central is a remote monitoring and management solution for IT teams, to ensure that only the right people access the right data, and correct issues and update security policies as and when necessary.
LogMeIn Rescue is a remote assistance platform that allows you to more easily manage worker and customer interactions.
Each LogMeIn solution is a multi-platform solution for Windows, macOS, iOS, and Android, and come with enterprise-grade security features such as TLS 1.2 transport security with AES-256-bit encryption.
To find out more, read our full LogMeIn Pro review.
Best identity management software for customers
Reasons to buy
Okta offers a range of identity management solutions for both your workforce and customers, allowing you to build secure environments and experiences that protect and enable both.
Identity services include SSO that helps reduce support loads while making it easier for users to access and login to apps. There are also universal directory and adaptive MFA, as well as API access management options, to make it easier to integrate IT infrastructure.
Identity management is customizable in real-time according to business policies, and two-factor authentication is also provided along with a user password reset functionality. Lifecycle management offers the ability to automate workflows and includes a range of B2B integrations to help with the process.
Centralized user management also means the service can adapt easily to new apps and other software development within your business, meaning that identity management can continue without interruption.
Read our full Okta Identity Cloud review.
Best identity management software for businesses
Reasons to buy
Reasons to avoid
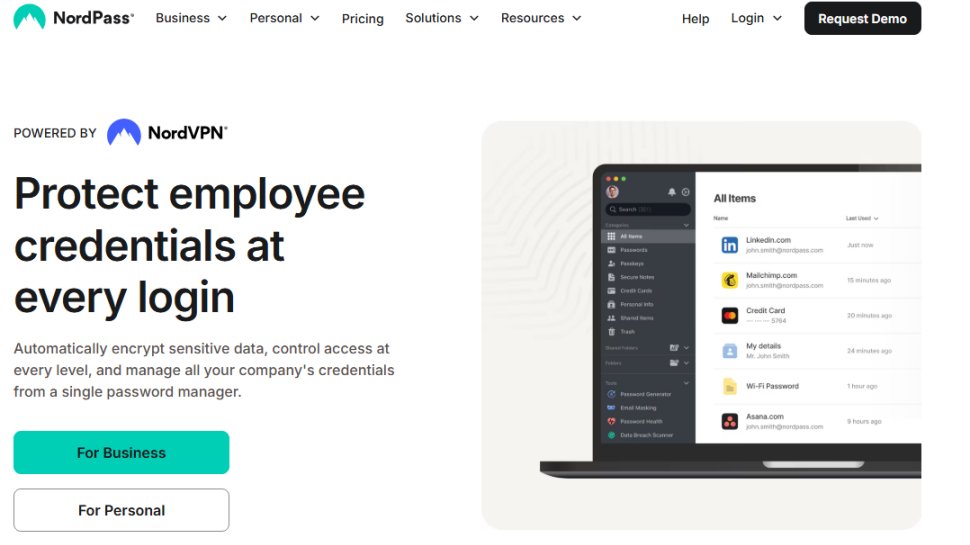
NordPass Business serves as a password management tool tailored for small and medium-sized businesses as well as larger enterprises. It assists in organizing and securing your organization's passwords, financial details, shipping information, and other sensitive data. This platform simplifies the processes of onboarding and offboarding employees and facilitates easy sharing of access among teams, enhancing collaboration.
Nordpass offers a very clean design and intuitive navigation with excellent customer support. There are numerous pricing plans to choose from, with the pricing depending on either the 1-year or 2-year options you get to choose from. The Teams starts at $1.99 per user per month, Business $3.99, and Enterprise $5.99.
Thanks to its proprietary encryption algorithm (XChaCha20), you can be sure that your data is secure and that the protection is future-proof. NordPass employs a zero-knowledge architecture, ensuring that your data is encrypted on your local device instead of being stored on NordPass’s servers.
NordPass fulfills all the standard functions one would expect from a password manager. Its apps and browser extensions are user-friendly, and it comes with beneficial security features, all at a cost that is reasonable even at the highest service tier.
Read our full NordPass review.
Best identity management software for features
4. OneLogin
Reasons to buy
OneLogin is a cloud-based authentication system that makes it easier for firms to secure their digital assets and users. It can handle multiple applications at once and has single sign-on capabilities.
The system is perfect for all businesses, regardless of industry sector, and it can work with both internal and public applications. Features include access request management, account management, compliance regulation, password management, user monitoring and role management.
There's a free trial you can use to try out the software. If you do purchase a solution, the support doesn’t stop. You can access documentation, webinars and online chats to better understand and get the most out of OneLogin. There’s also 24/7 tech support through the company website, so you can always ask a question if you get stuck.
Best identity management software for simplicity
5. PortalGuard
Reasons to buy
Reasons to avoid
PortalGuard combines important authentication procedures and password management capabilities within one convenient portal.
The software is compatible with Mac, Windows, iOS, cloud tools and web browsers, and it places a premium on ease-of-use. While it’s not the most powerful system out there by any means, many users will appreciate having things kept simple, and benefiting from their own custom-branded login portal.
What’s also neat is that when it comes to trying out the service before you commit to purchasing, you can avail yourself of a free interactive trial, or alternatively request a live demo from the company.
Best identity management software for flexibility
6. HID Global
Reasons to buy
Reasons to avoid
If you run a large-scale enterprise with a ton of digital assets, then you ought to check out HID Global. Used widely across the globe and adopted by companies such as Airbus, Citibank, HP, Nissan, and Verizon, this system lets you set smart authentication procedures for users.
The software analyses risks posed to your company and aims to give you a tailored approach to cybersecurity. There are multiple authentication methods to choose from, such as advanced multi-factor authentication, secure physical and logical access, credentialing, as well as analytics and reporting for appraising risk. Any of these can involve biometrics, tokens, pins, SAML and phones.
What’s also nifty is the fact that you can add more applications and changes over time, so you don’t have to worry about finding the perfect method straight away. As well as this, the software offers added protection for privileged and important users. This is sophisticated technology and is targeted at firms with significant security budgets.
Check out more in our full HID Access Control Systems review.
Additionally, we’ve chosen the best identity theft protection solutions.
Best identity management software FAQs
How to choose the best identity management software
When deciding which identity management software to use, first consider what your actual needs are, as budget software may only provide basic options, so if you need to use advanced tools you may find a more expensive platform is much more worthwhile. Additionally, higher-end software can usually cater for every need, so do ensure you have a good idea of which features you think you may require from your identity management software.
How we tested the best identity management software
To test for the best identity management software we first set up an account with the relevant software platform, then we tested the service to see how the software could be used for different purposes and in different situations. The aim was to push each identity management platform to see how useful its basic tools were and also how easy it was to get to grips with any more advanced tools.
Read more on how we test, rate, and review products on TechRadar.
Get in touch
- Want to find out about commercial or marketing opportunities? Click here
- Out of date info, errors, complaints or broken links? Give us a nudge
- Got a suggestion for a product or service provider? Message us directly
- You've reached the end of the page. Jump back up to the top ^
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!

Benedict is a Senior Security Writer at TechRadar Pro, where he has specialized in covering the intersection of geopolitics, cyber-warfare, and business security.
Benedict provides detailed analysis on state-sponsored threat actors, APT groups, and the protection of critical national infrastructure, with his reporting bridging the gap between technical threat intelligence and B2B security strategy.
Benedict holds an MA (Distinction) in Security, Intelligence, and Diplomacy from the University of Buckingham Centre for Security and Intelligence Studies (BUCSIS), with his specialization providing him with a robust academic framework for deconstructing complex international conflicts and intelligence operations, and the ability to translate intricate security data into actionable insights.

 Become a TechRadar Insider
Become a TechRadar Insider