Why isn’t a VPN hiding my real location?
Website not fooled by your VPN? Here's what to do

Using a VPN brings all kinds of benefits. One of the most important is that it gives you a new virtual location, maybe helping you access geoblocked websites.
This is largely automatic. Connect to a server in the UK, US or anywhere else your VPN offers, and your regular IP address will be shielded – websites should treat you as though you're visiting from your chosen country.
Unfortunately, it doesn't always work that way. You might have connected to a US server, but some websites may still know you're in the UK, while others think you're somewhere else entirely, or just refuse to work as you'd expect.
Article continues below 
This could be a major issue, especially if accessing this website is the reason you're using the VPN in the first place, but sometimes there's little you can do to solve the problem. Netflix makes huge efforts to block VPNs and proxies, for instance, and does this very effectively. Your only option is to try and find another service which allows access, but even then, there's no guarantee it will stay working for long.
Many VPN location issues are simpler to address, though, so don't give up just yet. Following our guide may help you to identify the cause of your problems, and get the VPN working just as you'd expect.
- It’s also worth bearing in mind the good reasons why a VPN isn't enough
Verify your VPN location
The first step in diagnosing VPN location issues is to confirm what your client software is telling you. There are two issues to think about here.
Sometimes a VPN client will say it has allocated an IP address from one country, but actually use somewhere else entirely. For example, one VPN we tested gave us German and US IPs when we connected to its two UK servers. As a result, although we thought we were connected to the UK, BBC iPlayer wouldn't play as we appeared to be from another country.
The second problem is that some poorly programmed VPN clients don't properly monitor your connection state. They might show you as connected, even if the VPN drops. In that case it might look like you're using a VPN server far away, but any website will just see your regular IP.
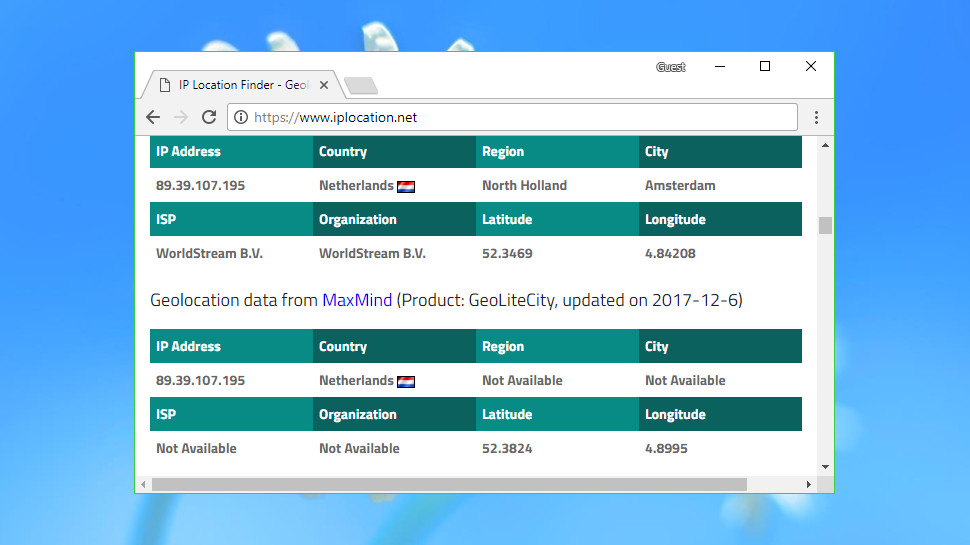
To check this for yourself, point your browser at IP Location immediately after you've had any location problems. The site runs your IP address through several web services and displays the city and country where it thinks you're located. Note that geolocation isn't a precise science, so don't worry if there are several suggested cities – the country is what matters.
If the report shows your home country and ISP, the VPN connection may have dropped or stopped working. Reboot and try again.
If the IP address is from another country, but not the one you selected, your VPN may be at fault. Close and restart your client, connect to several servers and verify their location with the iplocation.net site. Report any variations to your VPN.
If your VPN has given you an IP address exactly where you requested, then it seems to be working as it should. That's good news, but also means you'll have to dig a little deeper to find the source of your problems.

Try another server
Sometimes you'll be allocated a new IP address correctly, but a website might recognize that it belongs to a VPN address range, and block it or somehow limit your access.
This could mean that although you're connected to a UK, US or some other server, this won't allow you to unblock a streaming site in that country.
VPN providers will sometimes try to highlight the best servers for particular tasks. The client might have an icon to indicate which servers are best to use for Netflix, for example. Sometimes there will be a server list on the website with this information, or you could always email the company and ask.
Alternatively, if you can't properly access a website from one of your VPN's servers in that country, try each of the other servers in turn. There's no guarantee of success, but we've often found that's enough to solve the problem.
- Check out the best free VPN services
Cookie cutting and more
Replacing your IP address won't always be enough to persuade a website that you're in another location, particularly if you have an account at the site or have visited it before.
A website might use an IP and location from your initial visit, for instance. If you've logged in via a social media account, it may be able to obtain location-related profile details. It could use cookies to maintain location across sessions.
These tactics aren't used by everyone, but it's still a good idea to check whether these website state issues might be related to your VPN problems.
Start by logging out from a website account at the end of a normal session, then connect to your VPN and log in as normal.
Try removing any browser state information – delete your cookies, browser history and so on – before you log in.
Alternatively, launch an anonymous browsing session which won't have any previous website state information (in Chrome this is Menu > New Incognito Window, and in Firefox it’s Menu > New Private Window, or a similar option in other browsers).
Geolocation API
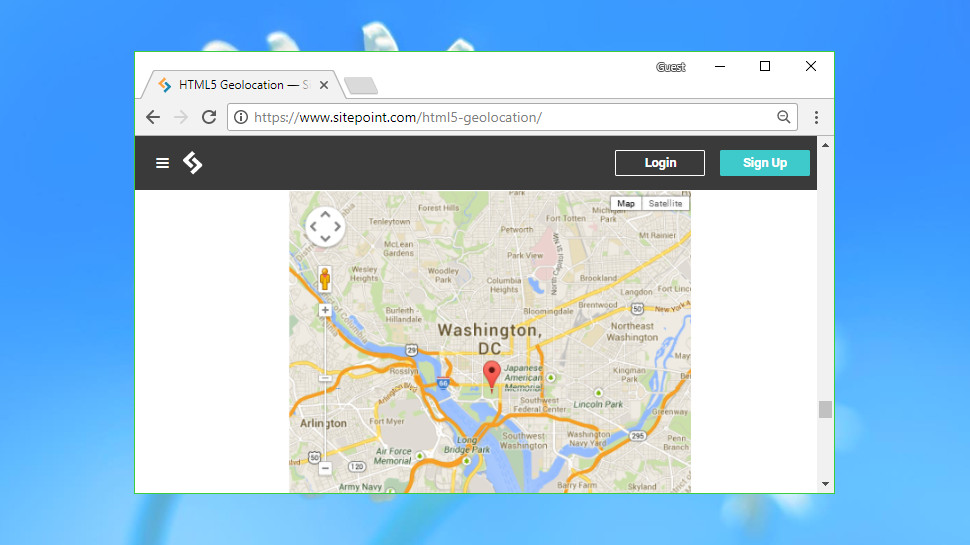
Websites and apps have several options available to try and find your location, but one of the simplest is the HTML Geolocation API. It's easy to use, often surprisingly accurate, and probably won't be affected by your VPN.
Test this by connecting to your VPN, then running the geolocation test on the BrowserLeaks site.
Normally your browser should ask if the site can access your location. Give it permission and a map will appear, most likely with your real location, and not the VPN server.
The main problem here is that if you give an app or website permission to access your location, that may be remembered next time, and the website will always be able to see where you are.
Check your browsers and apps for permissions you may have given previously, and delete any you don't need.
In Chrome, click Settings > Privacy and Security > Site Settings > Location to see the list of blocked and allowed sites.
Firefox has a similar list at Options > Privacy and Security > Permissions > Location. Opera's is at Settings > Websites > Location. Internet Explorer can allow or block location checks from Tools > Internet Options > Privacy > Location.
Another option is to manage location permissions at device level, allowing you to control more apps at once.
In Android, click Settings > Locations to view recent location requests or turn off location access for everything.
In Windows 10, press Win+A and click All Settings > Privacy > Location.
You're able to see and control which apps have permission to access your precise location. A Clear button wipes Windows' recent location history, and you can optionally turn off the location service for all Windows apps at once. Keep in mind that this only works for system apps, like Cortana and Edge – it won't affect Chrome, Firefox or other third-party software.
IP leaks
A website could try to identify your real location by checking for IP address leaks, or other indicators that you're not where you say you are.
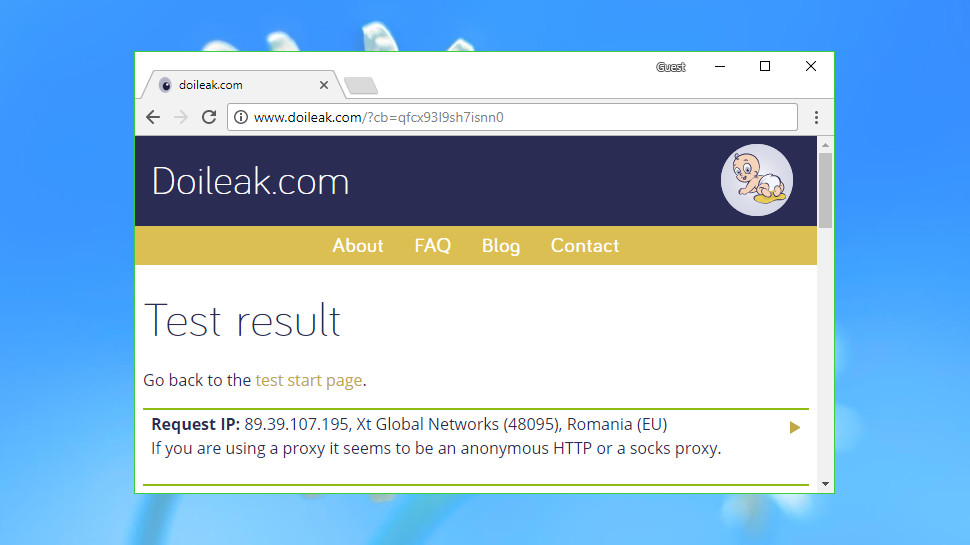
Visit Doileak.com and click Start Tests to see how this might work.
Check the WebRTC Leak and HTTP Request Leaks sections, in particular. If either of these contain your real external IP (not a local 192.168.x.x address), that could provide any website with a way to detect your real location.
The report might also list signs that suggest you're using a proxy or VPN. These could include an unusual connection type, multiple browser types or differences between your browser and IP address time zones.
The results you'll see might vary depending on your browser, so revisit the Doileak.com site with any other browsers or devices you might use, and look for any differences.
If you find one browser or device doesn't report a particular leak, try using that with your VPN to connect to any problem sites. And if they no longer seem to detect your location, maybe the address leak was the issue.
Fixing leaks is more difficult, as they're usually a function of how the service is set up, but there may still be things you can do. Check out your client Settings dialog for additional privacy features you might be able to turn on – smart DNS, multi-hop VPN, Tor support – or browse the VPN provider’s support pages to find out more.
- Check out our best VPN
- Discover how to change location with a VPN
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!

Mike is a lead security reviewer at Future, where he stress-tests VPNs, antivirus and more to find out which services are sure to keep you safe, and which are best avoided. Mike began his career as a lead software developer in the engineering world, where his creations were used by big-name companies from Rolls Royce to British Nuclear Fuels and British Aerospace. The early PC viruses caught Mike's attention, and he developed an interest in analyzing malware, and learning the low-level technical details of how Windows and network security work under the hood.

 Become a TechRadar Insider
Become a TechRadar Insider






