TechRadar Verdict
An amazingly cheap way to unblock US Netflix and others, but VPNShazam has so many technical, security, privacy and usability issues that it's impossible to recommend.
Pros
- +
Unblocks iPlayer, Netflix
- +
Offer price of $1.17 a month during review
Cons
- -
Poor Windows client
- -
Below par speeds
- -
No Mac, iOS apps
- -
Previous security vulnerability
Why you can trust TechRadar
Palestine-based VPNShazam doesn't exactly have the highest of profiles, and a quick scan of its website might leave you wondering why, because at first glance the service looks to be stuffed with appealing features.
Network size? An excellent 2,000 servers spread across 140 countries. (That seems unlikely for a small VPN, but it matches the network stats for PureVPN, and further lines with DNS and server names leaves us suspecting the two companies are using the same infrastructure.)
Encryption? Plenty of options with support for PPTP, L2TP, OpenVPN, SSTP and the IVEv2 protocols.
P2P support? Not on all servers, but it's available if you need it.
Dedicated IP plans get you a fixed IP address from one of six countries - USA, UK, Canada, Australia, Singapore, Germany - and should improve your chances of getting in to any geoblocked websites.
- Want to try VPNShazam? Check out the website here
Trustworthy? It's hard to say from a website, but the service has been around since 2009, suggesting it's delivering on at least some of its promises.
There's an obvious downside in VPNShazam's apps, as the company has Windows and Android offerings only - the better services around like ExpressVPN or NordVPN offer Mac, iOS, Linux and more besides.
VPNShazam's setup page explains how to configure the service on multiple platforms, though - Mac, iPhone, iPad, multiple versions of Windows, various router types, Chromebooks, even how to configure your VPN-enabled Windows device as a wireless hotspot which other devices can use.
Once you're up and running, VPNShazam supports up to five simultaneous connections.
Sounds good to us, but if any of this doesn't work as it should, VPNShazam promises 24/7/365 support for via ticket (not live chat.)
Signing up
VPNShazam's pricing looks fair, ranging from $8.99 billed monthly to $2.25 on the annual plan for the regular VPN plan, $10.95 (monthly) to $4.50 (over two years) for a dedicated IP.
Oddly, a separate 'Best Offer' page apparently gets you a full year of the same plan for a one-off $13.99, or an equivalent $1.17 a month. Why would you spend $8.99 on a one-off month, or $34 on the annual plan, if you can sign up for the $13.99 a year 'best offer', instead? Maybe it'll have disappeared by the time you read this, but if not, it looks exceptionally cheap.
Whatever you choose, VPNShazam supports a long list of payment methods: card, PayPal, Alipay, Perfect Money, Coinbase, Paymentwall, Coins Payment, Skrill and WebMoney (which means you're able to pay via Bitcoin and multiple other cryptocurrencies.)
We stuck to our very average and ordinary PayPal option, completed the transaction as usual, and only moments later an email arrived acknowledging the payment and including our login details.
VPNShazam's billing and account management system is powered by WHMCS, the same platform used by many web hosts. If you recognize it from a web host you've used, that'll be a small plus, as you'll immediately know how to find your way around.
Looking for information on your VPN account, for instance? Click Services, click the plan, you'll get information on your account, and options to change your password or request a cancellation on the same screen. Easy.
Security alert
VPNShazam's Windows app got off to an unusually poor start when Windows SmartScreen raised an alert, warning that this file wasn't often run. We launched it manually, and Panda Antivirus killed and quarantined the file, calling it a virus.
Could this be true? We uploaded it to VirusTotal and it wasn't flagged by a single engine (even Panda's, oddly.)
We checked out the results of both a static and dynamic analysis of the file (how the file is structured, and what it does when it runs), and saw nothing suspicious.
As SmartScreen flagged the file purely on the basis that it's brand new, we suspect Panda's alert also took that into account, and the fact that it's an installer - which means it's set up to do lots of low-level system things - pushed it over Panda's 'this might be dangerous' threshold.
We're going to treat this as a false alarm, then, and not count it as a mark against VPNShazam.
Interface and features
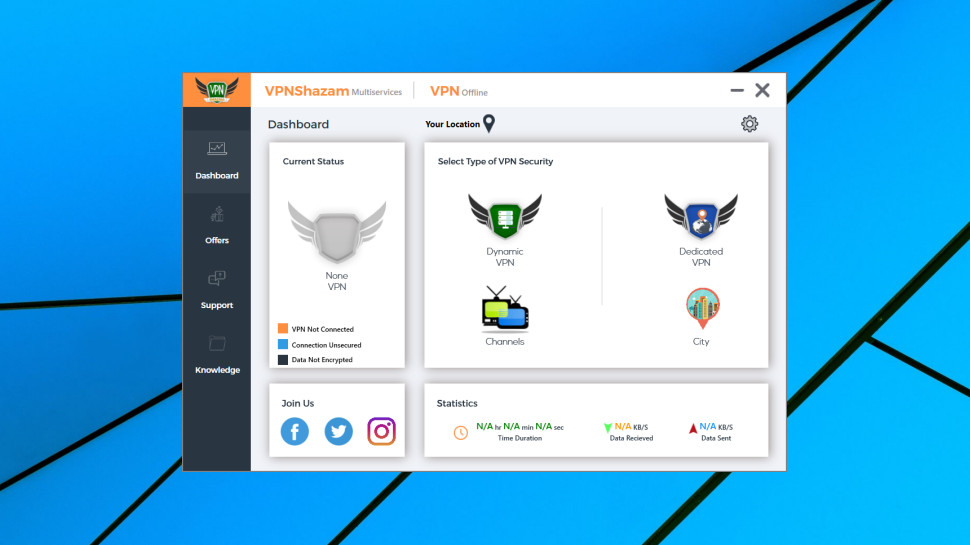
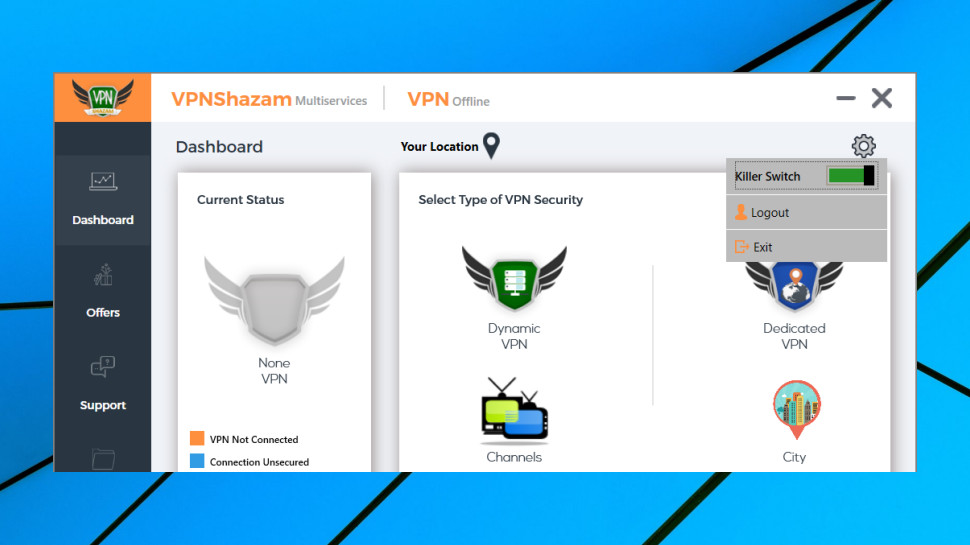
The VPNShazam Windows app has a bulky interface which wastes a huge amount of space on large graphics, a pointless sidebar, social media links and more.
It's all more complicated than it needs to be. A 'Select' panel asks you to choose from four options, for instance: Dynamic VPN, Dedicated VPN, Channels (a list of TV channels and streaming services) and 'City.' If you've bought a Dynamic VPN plan, should you choose that? Does 'Channels' apply to Dynamic and Dedicated plans? Does city-based selection really have to be an entirely separate panel?
The issues continued after connecting, when we found one panel took up as much space as some entire VPN apps, just to list some basic features of a VPN (our IP was hidden, we were browsing anonymously, we could access blocked sites, our connection was now encrypted.) We know, thanks, that's why we signed up-- no need to tell us this now.
There are plenty of other interface and usability annoyances. The app doesn't have an 'automatic' option to automatically choose the nearest server, for instance, and it doesn't remember the last server you chose, or include a Favorites system to quickly find commonly used locations. So, while other apps get you connected with a single click after launch, here we had to click Dynamic VPN, click 'Select Country', choose our preferred location, and then click Connect, each and every time.
The app plays an audio alert once the connection is complete. It's good to know when you're protected, but audio alerts can be annoying, and you may not want to announce to everyone nearby that 'I'm using my VPN now.' Unfortunately, there's no way to disable these.
Once connected, the app won't minimize to your system tray, unlike just about every other VPN app we've ever seen. Not the biggest of deals, but it means the app button is constantly taking up space on your taskbar.
Click Disconnect and the app asks, 'Are you sure?' That's great as a default option, but the app doesn't allow it to be disabled, which means an extra click every time you close a VPN session.
Wherever you look, there are very few configuration options. They're essentially limited to a choice of protocol (PPTP, L2TP, IKEv2, SSTP, OpenVPN TCP and OpenVPN UDP, and an optional 'Killer Switch' (a more scarily named version of a kill switch, which in theory disables your internet connection to prevent data leaks if the VPN drops.)
Windows app tests
VPNShazam's Windows app connected quickly, at least with our first attempts, getting online in under two seconds when using IKEv2.
When we chose OpenVPN, though, the app took more than a minute to get connected.
Investigating this, we found the app had failed to connect via OpenVPN, but not displayed any alert, and simply switched to another protocol (IKEv2 in our case) without telling the user.
That's bad news about the connection failure, but it's also poor practice to allow a user to think they're using one protocol, when in reality they're using another. Keep in mind that the app uses the ancient PPTP protocol, so insecure some VPNs have now dropped it entirely. Might the app have switched to that if its IKEv2 connection had failed? We don't know, but the app doesn't display the current protocol, so there's no obvious way for users to find out.
The native Windows connections (IKEv2, PPTP, L2TP) were at least sensibly configured, requiring encryption and disabling IPv6 to reduce the chance of data leaks.
The app replaced our regular DNS servers with its own, reducing the chance of data leaks.
We tried forcibly closing the VPN connection, to see what would happen. The app updated its interface, but, unfortunately, didn't display any notification or audio alert. Unless the app window was visible, we would think our data was protected, even when the VPN was down, and we were using our regular connection.
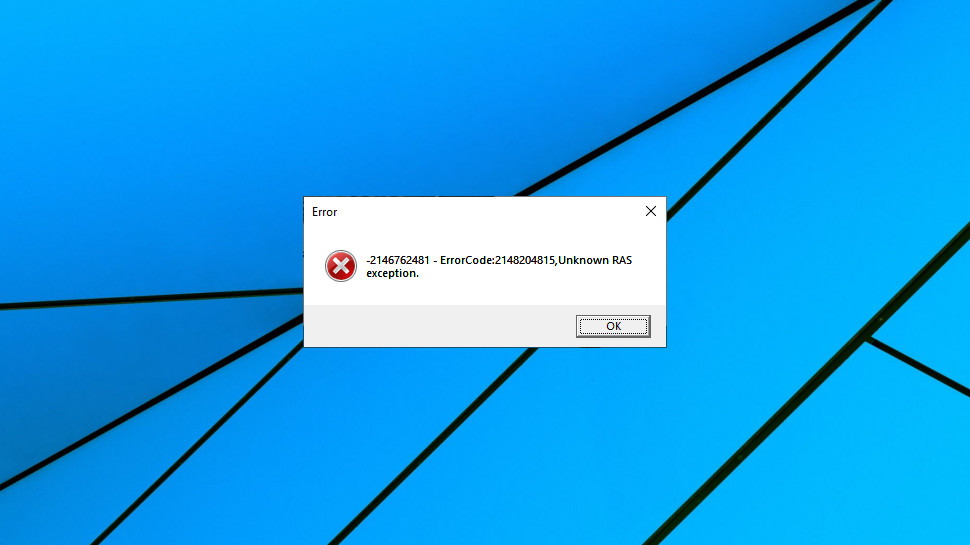
The app received a major update during the review, so we tried this test again. There some improvements - we got an audio alert once, the app reconnected at another time - but results were very inconsistent, and the display of raw and very cryptic .NET error messages ('ErrorCode:2148204815, Unknown RAS exception') suggested its error handling 'needs a little work.'
This didn't give us much hope for the app's kill switch, but we checked it out anyway.
We turned the kill switch on, tried again, and once more got very mixed results.
Sometimes the app would reconnect and play an audio alert to warn you something had happened.
But on other occasions it just displayed an error message, failed to reconnect, and didn't block our internet connection, either. If we didn't see the alert, perhaps because we were running a full-screen application, we would have no way to know our connection was no longer protected.
Investigating further, we found the app had set up some Windows firewall rules, suggesting it does have the basis of a kill switch mechanism. Maybe it will work properly in some situations. But it didn't do much for us, and that's a notably worse performance than we see with most VPNs.
Vulnerability
While carrying out the VPNShazam review we discovered an unusual and worrying security issue.
The VPNShazam website included files listing details of its VPN servers. At least one of these was referenced from the Windows app. We discovered that it was possible for an attacker to replace that file, or upload an arbitrary file of their own, using nothing more than a web browser.
Our initial concern was that VPNShazam's lists could be compromised, perhaps redirecting users to malicious servers. We don't know how much of a risk that constituted - getting VPNShazam's clients to connect to the fake servers is a whole new task in itself - but the fact that this security hole existed at all is worrying.
A secondary issue is that attackers could have uploaded arbitrary files of their own, perhaps malware or a phishing page, which would then be served from the VPNShazam website. Files could only be uploaded to the same folder as the lists, greatly limiting the impact of any attack (it wouldn't be possible to replace the app installers or any existing web pages, for instance), but this is still a concern.
We asked VPNShazam about this, and the company responded:
'I would like to confirm that our users are secure, and no one uses those servers list anymore. We were using those servers lists for our old VPN applications 2 years ago and it's not useable anymore. We have discussed this internally and we decided to take this offline as it's not useful anymore and could cause problems or bad impressions about our services.
'...we thank you for pointing this out. We have taken the lists, JSON and the upload files offline. Our Current Android and Windows VPN applications are using very secure API to load the servers list and supported protocols beside local data file included in the apps to load from in-case the API is not reachable if the client has an internet problem.'
Checking this information, we found that the server data currently used by the app was different to the data in the lists, suggesting this wasn't a current vulnerability.
One of the server lists had a 'last modified' date of January 2019, presenting at least the possibility of usage this year. The file could have been changed since it was last used, though, and most files were dated 2016-2017, matching what the company told us.
While it's good to see that the current apps server lists are no longer at risk from this form of attack, it looks like they may have been in previous years. Even though we're unclear about the scope of the exploit, that's not exactly reassuring.
Worse, the second security issue, the ability for attackers to upload their own files to the VPNShazam site, was active right up to the time of our investigations.
VPNShazam took action following our report, as the company promised, removing the vulnerable files and blocking both exploits.
The poor website security which opened up these loopholes doesn't inspire much confidence, though, especially in a company which you're trusting with your most confidential web activities.
Netflix
As with many other providers, VPNShazam makes big claims about its unblocking abilities.
'Imagine a world without internet restrictions and barriers', the company explains, 'where you can surf whatever social media website that you want, stream all the movies and videos you want without any restrictions.' 'All' the movies and videos you want? Without 'any' restrictions?
Maybe the company is overdoing the marketing a little, but it got off to a good start in our tests, with the UK server getting us instant access to BBC iPlayer.
Connecting to the US enabled viewing some of the less well-defended sites, including US-only content on YouTube.
Best of all, we were able to access Netflix in the US and Japan. VPNShazam's record wasn't perfect - Netflix was blocked in UK and Canada - but it's better than you'll see with many providers.

Performance
To assess VPN performance, we use the benchmarking sites SpeedTest and TestMy to measure download speeds from UK and US locations.
Our UK results were a little inconsistent, ranging from 55-66Mbps on our 75Mbps test line. Most VPNs manage 64-66Mbps just about all the time. Still, 55Mbps isn't exactly slow, and overall VPNShazam had enough speed for most tasks.
Our US test connection is capable of more than 600Mbps, giving any VPN a big chance to show what it can do. But VPNShazam's results were only marginally better than we saw in the UK, with median speeds ranging from 70-96Mbps.
Performance might be 'good enough', then, depending on your device and connection and what you're hoping to do, but it's unlikely to blow you away.
Final verdict
VPNShazam has some major technical and usability issues, and we would never rely on it protecting our privacy. If you'll only ever use the service for unblocking sites like US Netflix or BBC iPlayer, its ultra-low $13.99 a year price might seem tempting, but it's not a gamble that we recommend you take. Bet on a dead cert like ExpressVPN instead.
- We've also highlighted the best VPN services

Mike is a lead security reviewer at Future, where he stress-tests VPNs, antivirus and more to find out which services are sure to keep you safe, and which are best avoided. Mike began his career as a lead software developer in the engineering world, where his creations were used by big-name companies from Rolls Royce to British Nuclear Fuels and British Aerospace. The early PC viruses caught Mike's attention, and he developed an interest in analyzing malware, and learning the low-level technical details of how Windows and network security work under the hood.




