Telegram inadvertently hosts a thriving illegal marketplace
Want to rent a DDoS network to knock-off a website?

Sign up for breaking news, reviews, opinion, top tech deals, and more.
You are now subscribed
Your newsletter sign-up was successful
An investigation by security researchers has revealed that cybercriminals are exploiting Telegram’s encryption capabilities to sell illegal goods.
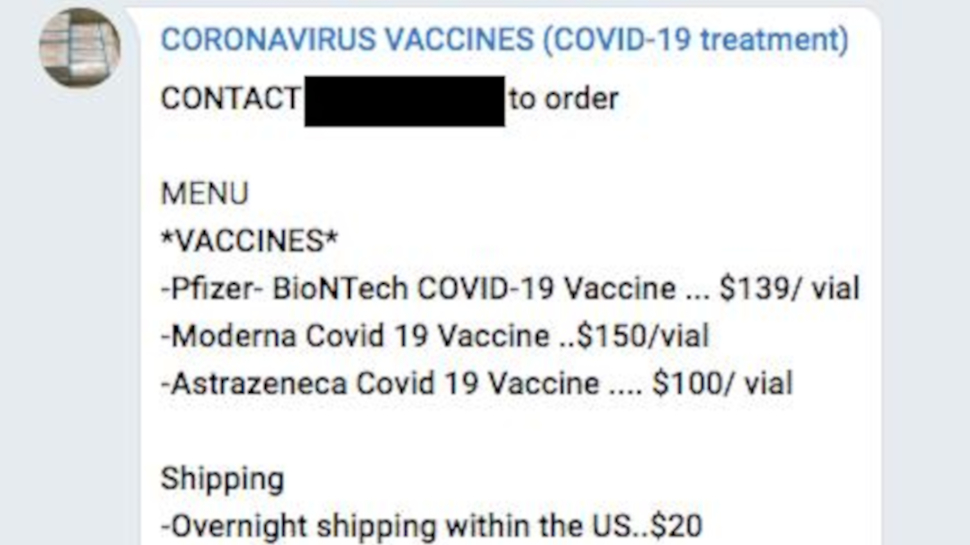
Cybersecurity experts from NortonLifeLock found evidence of a thriving illegal marketplace on Telegram where unscrupulous users hawk everything from Covid-19 vaccines and personal information, to pirated software and fake IDs.
Encrypted chat apps have gained popularity in recent times and are slowly entering the mainstream, displacing incumbents such as WhatsApp, as users warm up to their privacy-centric advantages.
Article continues belowWe're looking at how our readers use VPN for a forthcoming in-depth report. We'd love to hear your thoughts in the survey below. It won't take more than 60 seconds of your time.
- These are the best firewall apps and services
- We've put together a list of the best endpoint protection software
- Here's our choice of the best malware removal software on the market
“Scammers, fraudsters and hucksters of illegal goods are usually ahead of the curve on the latest technologies to provide a good experience for their customers. Therefore, we often see these actors as early adopters of popular technologies,” notes NortonLifeLock in a blog post sharing details of their investigation.
Illegal marketplace
The researchers argue that cybercriminals misuse Telegram’s strong anonymity protections to engage in such nefarious activities and communicate with customers without fear of law enforcement.
One of the most popular genres of illicit goods according to NortonLifeLock are fake documents and personal information, including social security numbers, home addresses, phone numbers, bank account numbers, and more.
Interestingly, they found that some miscreants even market their items for sale to coincide with newsworthy events. For instance, they found a vendor hawking hacked GameStop accounts right around the time of the GameStop stock trading frenzy.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
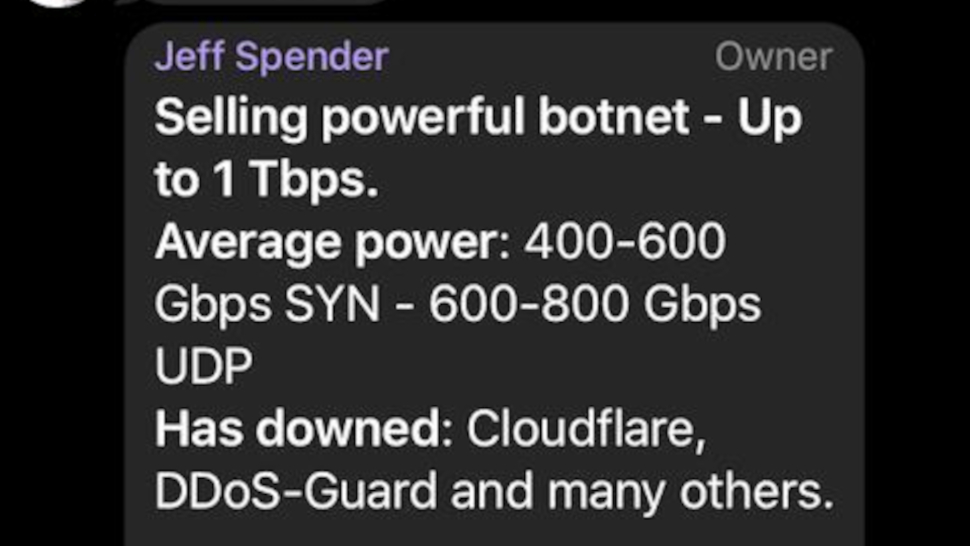
More worryingly though, in addition to illegal goods, the researchers also found criminals selling tools and services to facilitate cybercrime, including the rental of entire distributed denial-of-service (DDoS) infrastructure.
- Protect your devices with these best antivirus software
With almost two decades of writing and reporting on Linux, Mayank Sharma would like everyone to think he’s TechRadar Pro’s expert on the topic. Of course, he’s just as interested in other computing topics, particularly cybersecurity, cloud, containers, and coding.
