How to make your email more secure
Keep your messages safe from prying eyes
While instant messaging apps are becoming an increasingly popular means of electronic communication, email isn’t going anywhere soon. Approximately 270 billion emails were sent in 2017, and this number is predicted to hit around 320 billion by the year 2021.
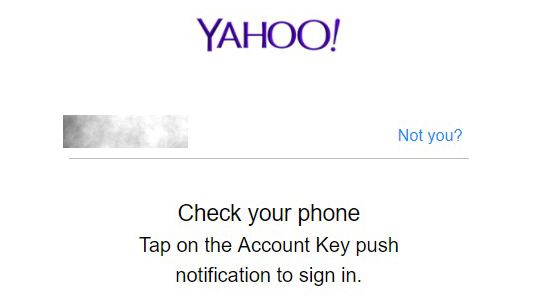
Despite the fact that in order to access your email account you’re required to supply your username and password (although Yahoo has attempted to increase security by allowing users replacing the conventional password with an app-based account key), email remains one of the least secure means of communication, and has been likened to sending a postcard – basically anyone along the way who’s interested can read the contents of a message.
In fact, email accounts have been hacked so many times at this point that scarily, there’s even a website you can check out to see if you appear on a list of compromised accounts.
Hacking aside, emails accounts in general are quite the opposite of private. This stems from the fact that an email is not a direct communication, but rather goes via several intermediaries. A single email message gets passed through multiple servers, including the ISPs involved as well as the email client’s, with multiple copies of the message stored at each server, and further copies on both the sender and recipient’s computer; so even when a email is deleted, there are still plenty of copies out there.
Finally, according the FindLaw, email accounts are among the easiest to access by both employers and law enforcement agencies – in the US they lose their status as protected communication after 180 days, allowing them to be produced on demand with a simple subpoena.
Email is starting to show its age – the first email was sent back in 1971 – and its various security shortcomings are enough to send users to more modern, alternative means of communication. However, with a few adjustments, your email can be more secure.
1. Password protection
The first weak point is, of course, the password, and with examples including ‘1’, ‘P@ssw0rd’ and ‘x’ featuring on a list of 10 common passwords it’s no surprise that some accounts are easily breached. Users also fall into the trap of using the same usernames and passwords for multiple accounts, and this can result in one hack being able to breach multiple accounts. We need to step up our game.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
Be sure to choose longer, and much stronger passwords – utilizing password software that can automatically generate these can help. Also, accept that relying on passwords alone is inherently insecure, and be sure to enable two-factor authentication. This should ideally be done via an app, and not just via SMS to avoid falling victim to SIM card spoofing. As mentioned above, Yahoo gives users the option to drop the password completely, and now provides a one-time-use passwords on demand via its mobile app for enhanced security.
2. General measures
Users need to understand that email is simply not a private communication. This goes double for work emails, which belong to your employer, and which can be inspected as they make their way through a company’s network and servers.
Be sure to always confirm that a reply is going to a genuine email address, and not to a spam variant. Also make sure to correctly choose between ‘Reply’ and ‘Reply to all’ when responding to a group email.
While email is convenient, cross-platform, and used by just about everyone, it’s worth considering if another method of communication might be more secure. Some instant messaging apps have addressed the issue of message privacy – options include TextSecure for Android, and Signal for the iOS camp.
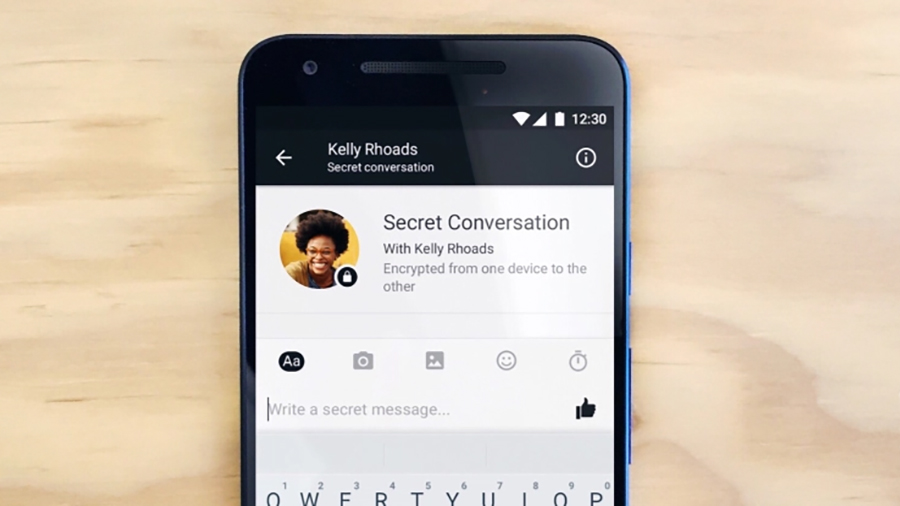
However, even with encrypted apps, there can be issues; the popular messaging app, Telegram, which uses 256-bit encryption, was recently taken off Apple’s App Store due to concerns over child pornography distribution, although it was subsequently reinstated. Even Facebook Messenger allows encrypted messages to be sent, and they’re also permanently deleted so as not to leave any trace.
3. Use a VPN
Another option to consider is a VPN, which creates an encrypted ‘tunnel’ to another server, where the data is decrypted before being sent on to the internet. However, while the primary reason for a VPN is privacy, and while it may keep your emails secure from your ISP, your email client will still have an unencrypted copy, so it only offers limited security.
4. Email encryption
The best strategy to keep your email private is to encrypt it directly – in some cases, the email client you already use may be doing this behind the scenes.
Gmail has been offering encryption as the default setting since 2014 for users emailing through Google apps, or on its Chrome browser. However emails aren’t encrypted if another browser is used, or if the recipient has any address other than Gmail, so this method does have its limitations. Then again, Google has become the Big Brother of the internet, and is known for reading user’s messages, all in the name of targeting them with more relevant ads; there’s privacy, and there’s Google’s idea of privacy.
Microsoft’s email client, Outlook, also offers an encryption option. Both the sender and the recipient need to exchange digital signatures, which include the certificate and the public key. The digital signature also includes a digital ID, which confirms the authenticity of the sender. However, this doesn’t work on Outlook.com, nor on the Windows Mail app.

There are some email services that have been designed to offer encryption. An example of a free one is the open source Tutanota, which offers mobile apps for iOS and Android as well as browser-based email. The downside is that people you send emails to will either need to have an email account on the same platform, or will have to provide a password to decrypt each email.
Another privacy strategy is to not actually use a permanent email address, and instead use a disposable one. Email provider MailDrop offers free addresses for exactly this purpose. Users have the choice of either creating their address, or allowing MailDrop to give them a random one – we got startingsibilation@maildrop.cc on a recent visit. There’s no sign-up or password involved, making it ideal for sending an email to an insecure recipient, although not for receiving mail.
Security Week by TechRadar Pro is brought to you in association with CyberGhost.
Jonas P. DeMuro is a freelance reviewer covering wireless networking hardware.

 Become a TechRadar Insider
Become a TechRadar Insider






