7 ways to secure your home Wi-Fi
Make sure your wireless router is safe from hackers and other miscreants

These days, just about everyone has a broadband connection, and in a residential setup, it’s the job of the best wireless routers to facilitate that connection. The router connects to the cable modem – or optical network terminal for those fortunate enough to have fiber optic – and then routes traffic to client devices which are requesting data, such as for a web page or a video stream.
With gigabytes of data passing through a router every day, it’s wise to invest some effort in making sure your router is as secure as possible. Otherwise, you could be in danger of folks logging on to your network wirelessly and stealing bandwidth, which is commonly known as ‘poaching W-iFi’ or ‘Wi-Fi squatting’. Hackers sometimes roam around looking for Wi-Fi networks to exploit. This is known as ‘war driving’.
You need to be prepared for this. At the very least if someone hijacks your wireless network, you will end up with less bandwidth to work with.
In the worst case scenario, malicious parties might use your connection for illegal downloads which could subsequently be traced back to you. So before you become a victim, check out these seven recommended methods to better secure your home network.
Remember this list isn’t exhaustive and you should always check with your router manufacturer for the latest security updates. If a bad actor does compromise your network, you can also protect yourself by encrypting your connection before it leaves your device through using any of the best VPNs.

1. Strong password
A vital component of wireless network security is the Wi-Fi password. For starters, make sure your network has a password – an open Wi-Fi connection is the equivalent of leaving the front door to your house unlocked and wide open. Of course, these days every modern router has a wireless password enabled out of the box.
However, this is not enough. Attackers can discover and use these default passwords, so they should always be changed. Indeed, it’s good practice to change your password regularly, as if a hacker can ‘sniff’ data packets moving between devices with time they can work out your password.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
When choosing a password, you shouldn’t use predictable dictionary words or words familiar to you like the name of your pet or favourite baseball team. These can be broken using ‘brute force’ methods, which involves trying combinations of obvious letters and numbers. Hackers sometimes use word lists of common passwords to try and break in to your system : for obvious reasons this is known as a ‘dictionary attack’.
To be properly secure, a password should be a high degree of entropy. In other words, it should be as unpredictable as possible.
You can do this using a random combination of uppercase letters, lowercase letters, numbers, and special characters. If you do this make sure your password is at least 12 characters long.
While concocting these longer, random passwords with the correct combination of characters used to be tedious, there are now websites that can generate random passwords that will fulfill these specifications quickly and easily, such as this one provided by LastPass.
Unfortunately these kind of passwords aren’t very easy to remember. If you need to enter the password regularly and/or give it to others, you may want to consider using Diceware to generate a secure password. This uses a long list of dictionary words chosen truly at random using dice to create a password. As the words aren’t predictable in any way, any passwords you create will be incredibly strong.
Just four words chosen at random from a Diceware list e.g. “Flap Thinly Remindful Canned” offers around 159 bits of entropy and would take a computer over 200 trillion years to crack. That’s over twice the strength of a 12-digit password generated by Lastpass, for example, “m1Q24&zp9ZYL”. It’s also much easier to say and remember.

2. That other password
While we are on the subject of passwords, we shouldn’t forget that alongside the standard Wi-Fi access password, your wireless router is also protected with another password. Namely the router’s login credentials which consist of a username coupled with said password.
By default, this login could well be something painfully simple such as ‘admin’ for the username and ‘password’ for the password, and you should change that to something more secure for obvious reasons (head to your router’s settings page to do so).
Also, while it might seem convenient to reuse the same password you put in place for Wi-Fi access, this is bad practice in just the same way that it’s not a good idea to reuse the same password across multiple websites.
To do this, you’ll need to use a device already connected to your Wi-Fi network. Open your web browser and enter the IP address of your router. If you’re not sure what this is, you can check with your manufacturer.
The first time you log in, the router may prompt you to set a new password. If not, you’ll need to change this in the settings. Again, you should check with the manufacturer for help with this.
Some older routers and IoT devices have the passwords ‘baked in’ - in other words, you can’t change them. If this happens either replace your router altogether or disable Wi-Fi and connect another more modern router.
3. Disable WPS
WPS stands for Wi-Fi Protected Setup, and it was designed to make it easier to add new devices onto a wireless network. WPS gets used via two methods: the first is to enter an eight digit PIN code, which is often on a sticker on the bottom of the router, and the second is to physically push a button located on the side of the router.
Not all routers support WPS, and if yours doesn’t, consider yourself fortunate. There is a known security flaw from way back in 2011 that renders WPS insecure and potentially hackable.
Furthermore, the push button method is also insecure as while it requires physical access to the router, a visitor to your home can join your network with a simple push of a button, and subsequently be a part of your network forever going forward.
This sounds very convenient but can easily be exploited by hackers. For instance, Kali Linux has a built-in tool called ‘reaver’, which can just try different combinations of WPS pin numbers until it hits on the right one. This usually only takes a few minutes to break into your wireless network.
For those who have a router that supports WPS, the fix is quite simple – disable WPS in the router’s settings, and don’t give it a second thought. After all, it really isn’t much more effort to just join the Wi-Fi network via a good old-fashioned password.
If you do come across a device like a printer, which can only be connected via WPS (this is rare but does happen), you can always re-enable WPS just long enough to connect the device, then disable it again.

4. Enable guest network
Most folks run a single SSID, with their router broadcasting a single wireless network name. A guest network allows the router to broadcast an additional SSID, thereby segregating network traffic off the main wireless network and onto a separate one. This guest network also needs to have a secure password as explained above, which should be different to the one you use for your own Wi-Fi network.
The guest network can help to secure the entire network. For example, if visitors are on your guest network, they aren’t gaining access to the main network that could have PCs with file sharing enabled – which could be a potential vulnerability.
Another possibility for a guest network is to use this for your smart home devices, as these Internet of Things gadgets are often not kept as up-to-date as computers, and can suffer from more security issues. Therefore by keeping these gadgets segregated from your main network, you’re in less danger from said potential security vulnerabilities.
Once your guest network is set up, there’s no need for anyone else to see your own Wi-Fi network. Check your router settings to see if you can hide your SSID i.e. your Wi-Fi network name.
This means if anyone comes to your place, they’ll only see the guest network as an available Wi-Fi option. Your other Wi-Fi network will stop broadcasting its identity to anyone that comes along. You can still connect other devices to your own hidden Wi-Fi network by entering both its name and the password in the connection settings.
This also avoids confusion for guests visiting your property. There’s no harm in writing the guest Wi-Fi password down and displaying it somewhere prominent inside your home e.g. on the refrigerator as it can’t be used to access your own devices, which are connected to a separate Wi-Fi network.
5. Turn your router off
Hiding your wireless network name won’t stop a skilled and determined hacker, as they can use specialist tools to scan for routers that aren’t broadcasting their name. If you’ve set up a guest network, this also could be detected.
It stands to reason though, that if your router is switched off, there is no wireless signal. As such the wireless network can’t be hacked as for all practical purposes, it doesn’t exist!
It isn’t ideal to have to keep switching off or unplugging your router, of course, but some routers allow you to schedule on/off times. Many mainstream routers like TP-Link devices also allow you to switch off wireless connectivity at certain times without powering off the device altogether.
If you’re an experienced network administrator, you could also consider beating hackers at their own game by setting up an obvious ‘honeypot’ network separate to your main one, with a few dummy files on it. It may not necessarily fool a determined attacker but it will slow them down. If you do this, make sure to use a separate router and device to set up the fake Wi-Fi network, as otherwise you could be making your data more vulnerable, not less.
6. Be vigilant about firmware
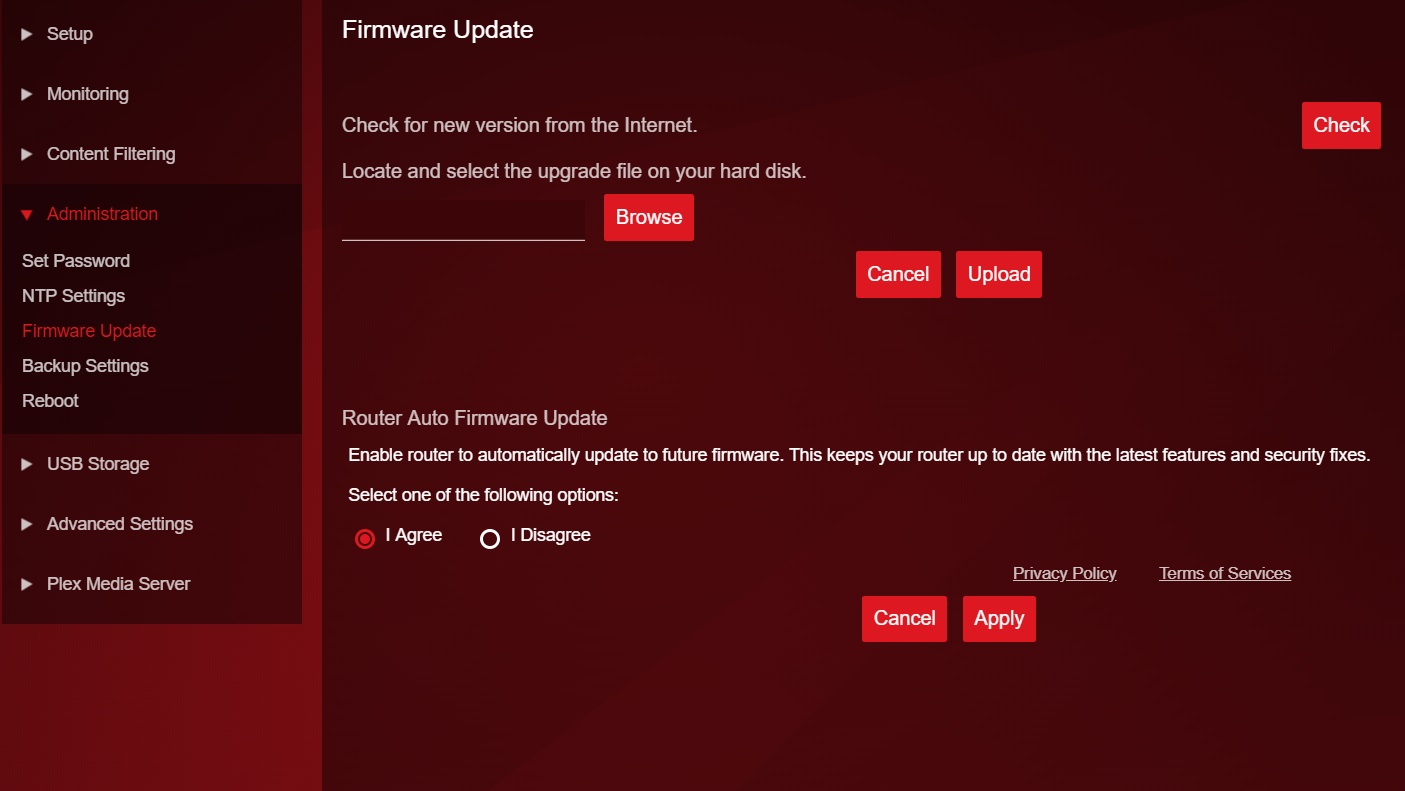
The manufacturer of your router will provide security fixes for the device, and these will be delivered via fresh firmware updates. Some routers update firmware on their own, while others need the user to trigger the upgrade via an app. Y
Unfortunately, some other routers hide the firmware upgrade option in the advanced settings, requiring a manual upgrade using the code from the manufacturer’s support site, where novices are unlikely to find it.
You can double check this with the manufacturer, as well as check which firmware version you’re running by accessing the router settings.
Whatever the process, you should make sure that your firmware always stays bang up-to-date, or your router may be vulnerable to known attacks.
One thorny issue is that really old routers may no longer be supported with firmware upgrades from the manufacturer. In this case, you should probably look at upgrading to a more current supported router. Alternatively, if you don’t want to spend money upgrading, you could turn to an open firmware such as DD-WRT assuming the router in question supports it.
If your router was supplied by your ISP, you may have to keep using it, as it also contains a modem to connect your network to the Internet. If this is the case, remember you can simply shut down Wi-Fi on your ISP’s router and then connect a more up to date router to it to manage your wireless network.
7. Upgrade your Wi-Fi encryption
Assuming you’re now using an up to date router, you should make sure that your wireless network operates on the Wi-Fi 6 standard.
This new standard, previously known as ‘802.11ax’ comes with a number of advantages : it’s more energy efficient and is designed to handle multiple devices and wireless channels. From a security point of view, it also supports WPA3 encryption.
If you aren’t the kind of person who gets excited by security protocols, you may not know that the previous versions, WEP and WPA2, are vulnerable to being ‘cracked’, even though WPA2 uses advanced ‘AES’ encryption.
WPA3 addresses these flaws by making ‘brute force’ attacks much harder, by using the ‘DragonFly Key Exchange’, also known as SAE (Simultaneous Authentication of Equals).
There have been some successful attacks against WPA3 but you’re making life much more difficult for bad actors, particularly if you combine this with the steps outlined above: use a strong password, change it regularly, hide your wireless network and deactivate Wi-Fi when not in use.
Jonas P. DeMuro is a freelance reviewer covering wireless networking hardware.

 Become a TechRadar Insider
Become a TechRadar Insider






