
Sign up for breaking news, reviews, opinion, top tech deals, and more.
You are now subscribed
Your newsletter sign-up was successful
With everyone from government and world-wide corporations to websites including TechRadar falling foul of industrial hacking attacks, scrutiny of security has never been so high.
If you're still using PASSWORD or 123456 to protect your email, it's time for a radical rethink of your password security.
Recent attacks, such as the one against LinkedIn, highlight how important having a strong password is.
Article continues below 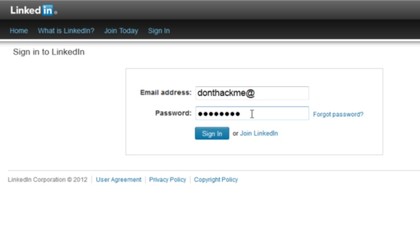
Hackers haven't targeted individual accounts but rather stolen a site's entire password database. This can then be cracked and potentially the hackers have a huge list of users' emails and associated passwords.
If this list hasn't been salted – a process that increases encryption complexity – a short or common password can easily and quickly be cracked via look-up tables and brute-force attacks.
We could explain, but XKCD have already done that very eloquently; basically a long, memorable password is more secure than a short and complex one involving symbols and numbers.
It's kind of contrary to what everyone is told, but the recent LinkedIn database theft had short passwords cracked within days, and modern GPU hash-crackers can pump out a billion hashes a second or more.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
This does ignore the issue that the LinkedIn database lacked the salting that would have increased the hash complexity and stopped them being cracked so quickly in the first place.
As a user, there's nothing you can do about your passwords being stolen directly from services and websites. However, you do have a duty to create strong passwords in the first place, along with protecting those passwords and not using duplicate passwords across sites.
Better passwords
As we've already covered, you can try and do all the right things and it's still possible to have your account compromised, be it by sheer bad luck, a weak password or malware like a key logger.
What's left to do?
This is where a one-time password system steps in, more commonly known as two-factor authentication or TFA.

Here, a bank or service provides a second route to prove who you are. Many banks now insist on a keycard that generates a one-time passcode.
Google, PayPal, Blizzard and Facebook provide similar systems, but these systems use a smartphone to generate the code, either locally via an app or delivered in a text message.
An alternative approach is SteamGuard for Steam, which uses your PC's IP address as the second TFA factor, clever old Valve.
While there are scenarios where a TFA system can be circumvented, the window of opportunity is vastly reduced, even if the attacker knows your password.
This technology currently represents the best protection for financially-sensitive services and accounts.
Top tips
Want to boost your password security? Here are our top-five tips for improved passwords.
1. Get Two Factor Authentication
If a service offers TFA, take it. While they're not 100 per cent bullet-proof, TFA systems offer by far the most secure protection. Possible routes of compromise do exist, such as someone ringing you to check the TFA is working, or malware installed intercepting the code.
You might consider, say, Google TFA, to be troublesome, but you can request a 30-day gap for regularly used systems.
Other devices need to be activated with a unique Google-generated password for each app that accesses Google accounts.
You can also eliminate the need for a text message by generating the code locally from the Google Authenticator TFA app.
2. Get a password manager
You don't even need to buy one or install one: Firefox, Chrome and Internet Explorer will all gladly save passwords for your sites.
For added security, Firefox can protect these with a master password from the Security tab in its 'Options' dialogue.
Similarly, Chrome Sync will secure your history via your Google Account login and synchronise passwords across your Chrome-using devices.