Evaluate and improve your website security using these simple steps
Security is a major aspect of any website – particularly e-commerce operations

There was a time when people and companies chucked up websites with total abandon, simply hoping that nobody would hack the contents or install malware on the site.
Those days are long behind us, as the number and frequency of attacks mean there’s a constant threat – and the more successful a website is, the greater the danger.
So what are the ways in which you can protect your website (via your web hosting provider), and how can you reduce the possibility that the site is hacked and nefariously altered?
Before we get to that, though, we need to understand the most basic level of security that is responsible for many hacked sites – even those hosted on secure servers.
- We’ve chosen the best web hosting services right here
- These are the best free web hosting companies around
- And those are currently the best website builders

The first line of defense
Although some companies insist on hosting their own websites, most business domains are located on secure servers contracted for the purpose.
When you choose the hosting, you get to define what OS that system is running (Windows Server, Linux or Unix) and that dictates the security protocols which are required.
The person or people with the responsibility to administer the site have admin rights to alter the file structures on it, and nobody else.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
Where this can go wrong from the outset is if too many people know the admin account details, and the password isn’t changed on a regular basis. And it only takes a keylogger to be installed on one of the machines used to do the admin, and the password is revealed to exactly the sort of people you would least want to have it.
But being honest, how many people work in an office where passwords are regularly remembered with post-it notes? A few hands went up there, doubtless.
Securing these passwords is the first line of defense, and without that, whatever else you do can be easily undone.
So, there are two initial lessons to be learned about website security, namely that:
- It’s only as good as the network where the website was constructed
- Security is rarely made better by writing passwords down, and placing them in a highly visible location
Security audit
Performing a security audit on a site is a relatively simple exercise that can be done by IT staff using a selection of software tools. Or alternatively you can contract a third-party to perform the scan for you, and provide a list of potential weaknesses to shore up.
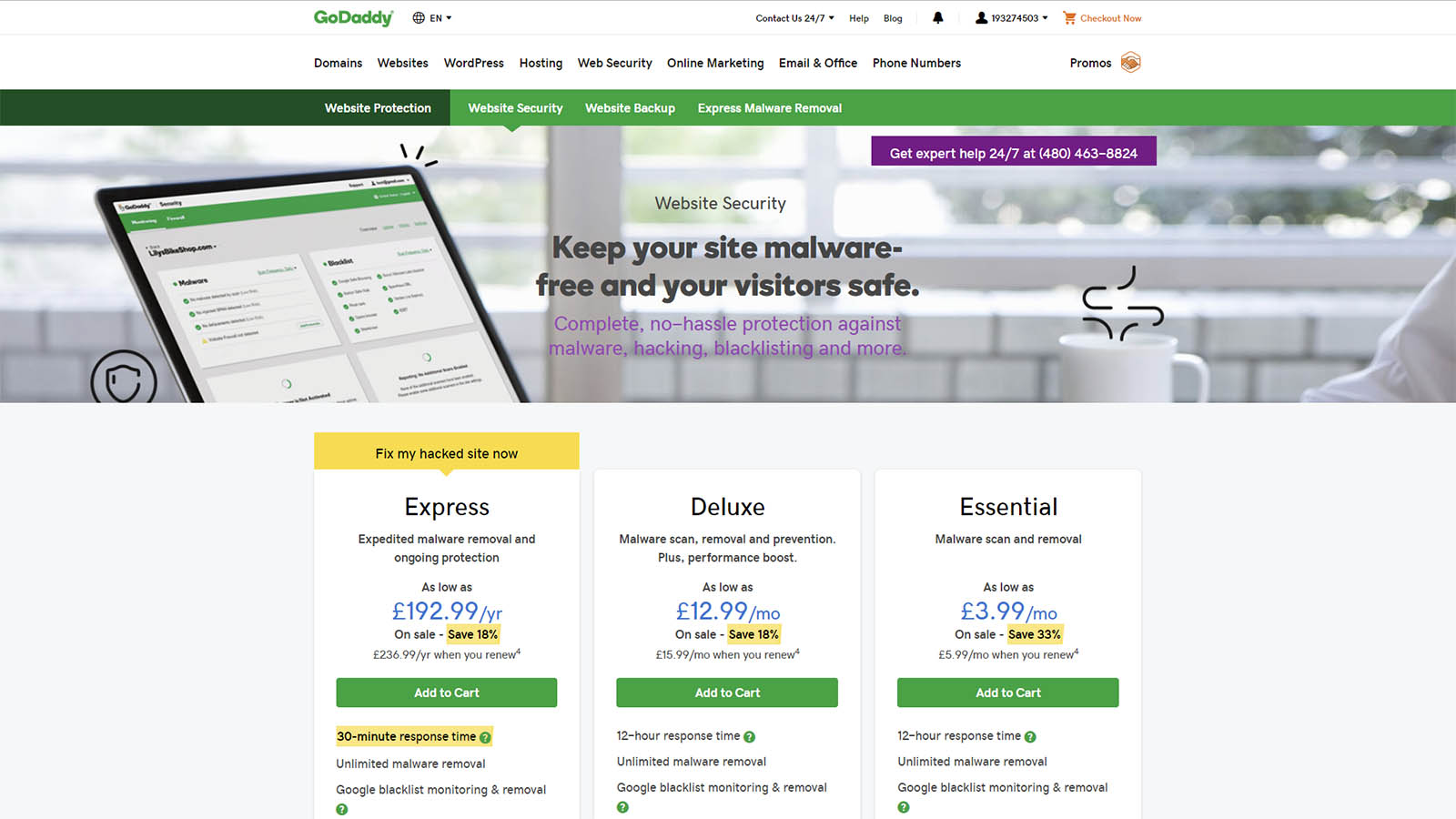
If you are buying a web hosting service, the provider might also bundle a security tool to make sure that you are reasonably secure from the outset – but not usually on an ongoing basis.
Beyond that, many providers also offer a website security package, where they promise a rapid response to threats and mitigation of service denial assaults. Unless you have just a small personal blog, these are a sound investment.
The price of these services isn’t much when you consider how costly having a site offline for any period of time might be, especially for those offering e-commerce.
Whatever approach you take, it’s important that security scans are performed on a regular basis, to identify possible new threats as they emerge, and address them immediately.

Common concerns
The most common forms of attack that websites encounter are these:
- Distributed Denial of Service (DDoS) – Many remote computers, usually infected with a Trojan, act in unison demanding web pages repeatedly to the point where the servers can’t handle the amount of requests.
- Malware infection – Somehow files that contain some nefarious code are placed on the site with the intention to upload it to anyone who visits.
- SQL injection – Malicious code inserted in a form or input that is then executed by the SQL Database on the server. This code could enable customer data to be accessed, or open the machine to external access.
- Brute force – Often a flaw in the OS allows a repeat attack to cause a reset that opens a port briefly for a secondary assault. Given the complexity of modern operating systems, new vulnerabilities are found on a regular basis.
- Cross-site scripting – A hacking method where a browser can be redirected to another site, or replace content on the victim site without the visitor being aware.
- The ‘zero day’ hack – These are new and difficult to stop attacks that use a weakness that isn’t public knowledge. The time between the vulnerability being discovered and patched is critical, and may require some server features being temporarily disabled until a fix is found.
Weaknesses by design
While many sites operate with the following features active, they are the source of many security issues for numerous reasons:
- Forms – Anything that processes input on the server is a potential entry point for malicious code, and it can also be exploited to extract user data.
- Forums – The placing of scripts and redirecting users to websites that dispense malware are just a few of the potential issues with user-generated forums.
- Social media sign-in – Using your Facebook or Google account to log into a site is quick and easy, but it could also be a way that these accounts get hacked.
- E-commerce – Crime follows the money, and hackers will expend much more effort to hack an e-commerce site.
- Unregulated content – If you source news stories and articles from other sites, you are dependent on their security measures, whatever they might be.
Obviously, removing all these functions from a website would make it a much less inviting place for visitors. A judgement call needs to be made about what elements you are prepared to use, and how you intend to mitigate the possible security problems associated with them.
Appropriate protection
There is only one way to guarantee that your website is never hacked, and that’s not to have one. Ultimately, website security is a mitigation exercise where you do enough to make it much less worthwhile to try and hack your site, and also ensure that it’s quicker to recover from any incident.
The exact level of security effort made is a choice that all companies must wrestle with, but for those involved in online selling, the commitment must be 100% to secure the personal and financial details of those who trade with you.
Numerous companies and organizations have had all their customer data stolen and then subsequently used for identity theft scams, with expensive consequences.
Whatever level of protection and monitoring you choose, it needs to be fit for purpose. Finally, consider that having better security than you need has a minimal cost implication, but having less could have huge legal and commercial ramifications.
Mark is an expert on 3D printers, drones and phones. He also covers storage, including SSDs, NAS drives and portable hard drives. He started writing in 1986 and has contributed to MicroMart, PC Format, 3D World, among others.

 Become a TechRadar Insider
Become a TechRadar Insider








