Perfect Forward Secrecy explained: everything you need to know
With hackers refining their tactics, encryption gets smarter

You're probably already familiar with the concept of encryption. Messaging apps, VPN services and most websites constantly scramble your data in transit so that just you and the receiver can access that information - whether it's a message, call or webpage.
However, for encryption to be effective, these private keys must remain secret at all times. Otherwise, if cybercriminals get hold of them, they will be able to access or modify your data in transit.
That's where Perfect Forward Secrecy (PFS) comes into play: to minimize the risk in the rare situation that your encryption keys do get compromised. This technology is a way to fortify encryption, and prevent hackers from accessing your whole stack of data.
Secure messaging apps like Signal and many of the best VPN providers have implemented PFS technology in their software to ensure their users stay safe, even in a worst-case scenario.
Here, we'll explain everything you need to know about Perfect Forward Secrecy: how it works, its pros and cons, and on which occasions it is implemented.

What is Perfect Forward Secrecy?
Perfect Forward Secrecy minimizes the risk posed to your personal information in the event of an encryption key breach by regularly changing your keys. The amount of time between changes varies by implementation - some are hourly, and others change every time you access a new message or load a new page.
This means that if malicious actors manage to intercept one of these keys, they will be able to access just a small portion of the information you shared online.
These keys are randomly generated so that, even in case they get intercepted, hackers won't be able to use them to get hold of your past nor your future data.
In the case of VPN traffic, these sets of keys are regenerated for each session. Some providers like ExpressVPN use new keys every time your device switches network, after a connection is terminated, as well as every 15 minutes to better protect longer sessions.
How does Perfect Forward Secrecy work?
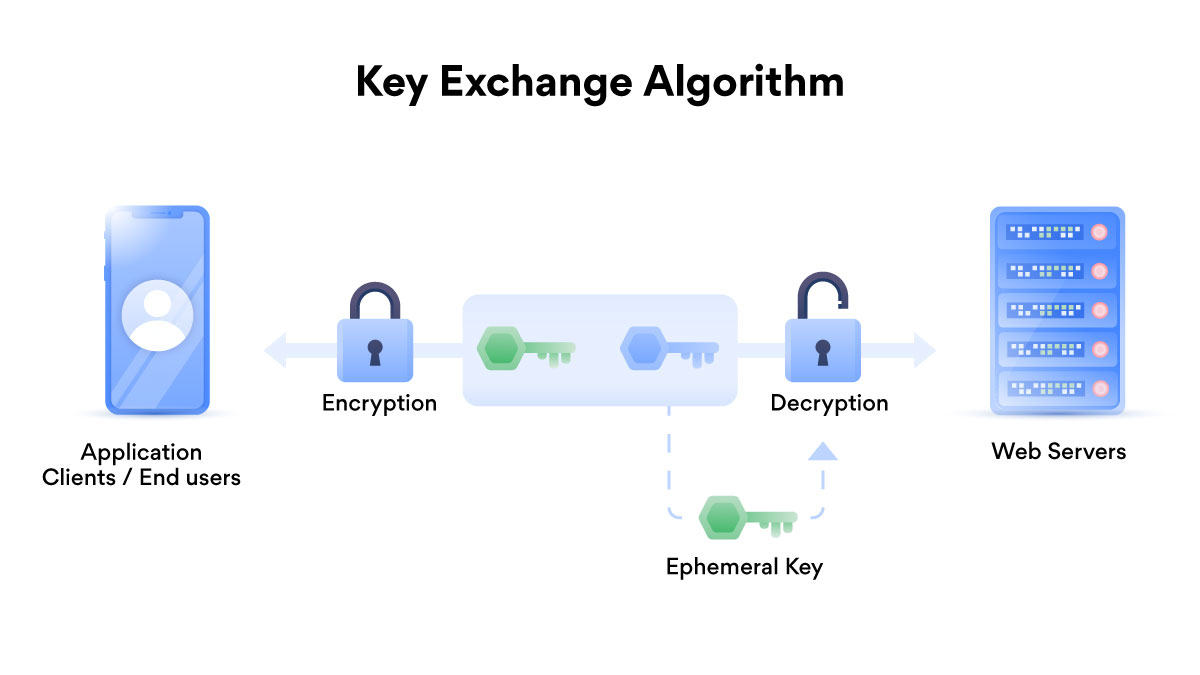
So, PFS generates new sets of keys to minimize the users' risk, but how exactly does this process work?
The infrastructure of apps, services and websites supporting Perfect Forward Secrecy relies on the Diffie-Hellman key exchange (DH) to generate ephemeral keys without sharing them over the internet. Using prime numbers and complex mathematical formulas, DH allows two parties without prior knowledge of each other to establish a shared secret key over an insecure connection channel.
In simple terms, as soon as these decryption keys have been used, they disappear. And the process is repeated for each data exchange happening between the two parties - whether that's you and your mate chatting via Telegram Secret Chats, or your device and the web server rerouting you on a chosen site.
All this makes it quite difficult for hackers to get hold of your data in transit and, in the virtually impossible case that they manage to do so, only the information you shared via that single key will be revealed.
What are the benefits of Perfect Forward Secrecy?
Perfect Forward Secrecy has several advantages compared with traditional encryption systems. That's not to say that normal encryption isn't secure, but adding an extra layer of protection makes your crypto-lock way more difficult to crack.
First of all, with endlessly changing encryption keys, your past activities will be protected from any intruders in case future sessions get compromised.
Your overall data security will improve as, even if a leak does happen, third parties will manage to see only a tiny portion of your encrypted data.
On top of that, hackers would probably be less inclined to target PFS-based services. That's mainly because it wouldn't be worth the effort to access only a very limited stack of data.
And the disadvantages?
As every time a double encryption occurs - similarly to NordVPN's Double VPN - your connection might slow down. That's because the system requires more processing power. However, if your device is powerful enough you are unlikely to even realize it.
From a developing perspective, PFS is harder to troubleshoot as its infrastructure is more complex.
Plus, although all modern browsers support Perfect Forward Secrecy on HTTPS-encrypted sites, there are still some web servers that unfortunately do not.
It is also worth noting that, even though both the popular OpenVPN and WireGuard protocols support PFS technology, even the most secure VPN services usually do not enable this by default.
Who's using Perfect Forward Secrecy?
With cyber attacks continuing to grow everywhere around the world, Perfect Forward Secrecy is becoming increasingly popular for protecting modern communications.
In 2011, Google started integrating PFS in its TLS infrastructure to secure all its services - from Gmail and Google Docs to encrypted search. Two years later, Twitter did the same.
Now, almost every website implements Perfect Forward Secrecy technology. As Atlas VPN reported, SSL Labs found out that only a tiny 0,9% of sites do not support PFS at all.
Many of the most private VPN services have implemented this secure technology, too. These include ExpressVPN, Proton VPN, NordVPN and Private Internet Access (PIA).
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!

Chiara is a multimedia journalist committed to covering stories to help promote the rights and denounce the abuses of the digital side of life – wherever cybersecurity, markets, and politics tangle up. She believes an open, uncensored, and private internet is a basic human need and wants to use her knowledge of VPNs to help readers take back control. She writes news, interviews, and analysis on data privacy, online censorship, digital rights, tech policies, and security software, with a special focus on VPNs, for TechRadar and TechRadar Pro. Got a story, tip-off, or something tech-interesting to say? Reach out to chiara.castro@futurenet.com

 Become a TechRadar Insider
Become a TechRadar Insider






