Adware apps still common on Google Play Store
Avast discovers 50 adware apps on the Play Store with over 30m installs
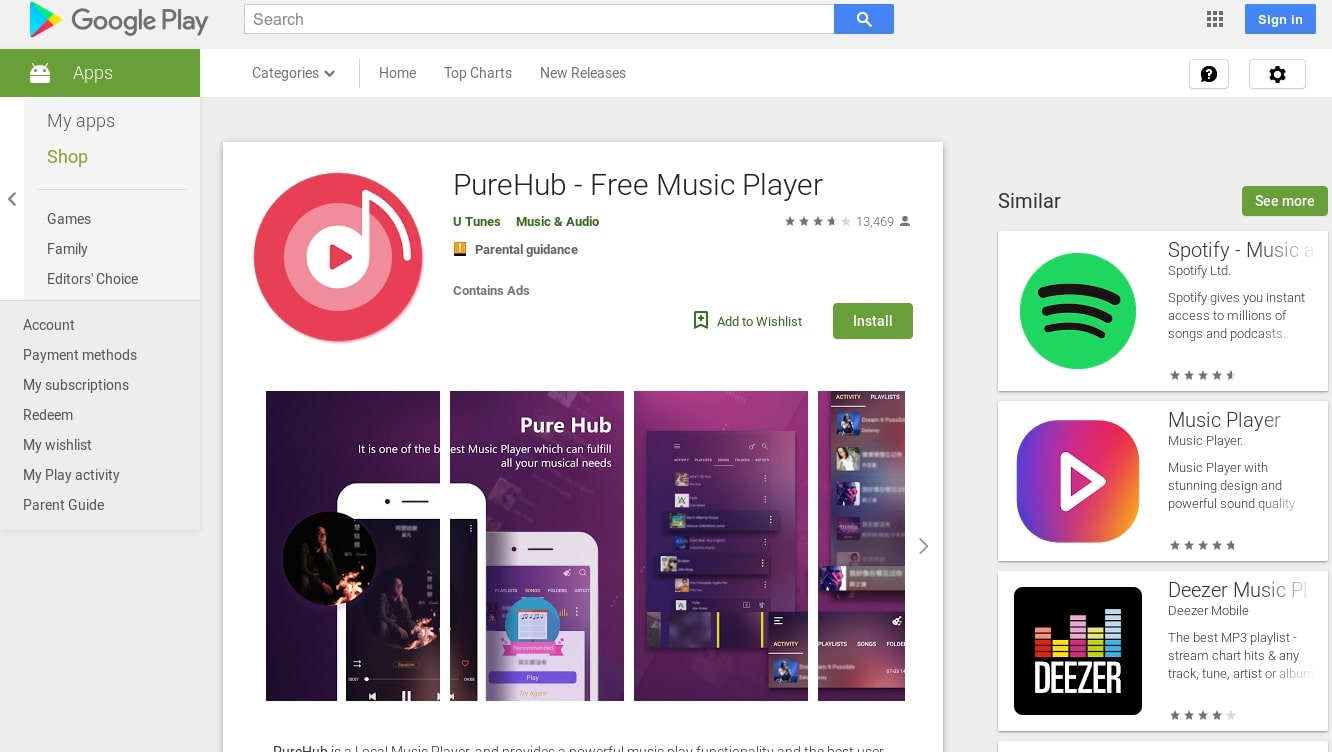
Through the use of its mobile threat intelligence platform apklab.io, Avast has discovered 50 adware apps on the Google Play Store that have been installed anywhere from 5k to 5m times.
The security firm has dubbed the adware TsSdk because the term was found in the first version of the malicious apps that persistently display full screen ads and even try to convince users to install further apps.
The adware applications Avast discovered are linked together by the use of third-party Android libraries that bypass the background service restrictions present in newer versions of Android. While bypassing itself is not explicitly forbidden on the Play Store, apklab.io detects it as Android:Agent-SEB [PUB] because these libraries waste user's battery life and make their devices slower.
- Android apps used in multimillion dollar ad fraud scheme
- Major mobile malware campaigns hit 250m downloads
- Google killed over two billion bad ads in 2018
The adware apps themselves, use the libraries to continuously display more and more ads to users which goes against the Play Store's rules.
TsSdk
Through apklab.io, Avast found two versions of TsSdk on the Play Store that were linked together by the same code. The older of the two versions has been installed 3.6m times and was contained in gaming, fitness and photo editing apps most often installed in India, Indonesia, the Philippines, Pakistan, Bangladesh and Nepal.
Once installed, the apps containing the older version worked as intended but also created shortcuts on user's home screen with full screen ads shown when the screen is turned on and periodically when a user interacts with their Android smartphone. Some of the apps also contained code capable of downloading further applications, prompting users to install them.
Additionally, most of the older samples also added a shortcut to a “Game center” on the infected device's home screen which opens a page advertising different games.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
The newer version of TsSdk has been installed almost 28m times through music and fitness apps. These apps were most installed in the Philippines, India, Indonesia, Malaysia, Brazil and the UK. The new version's code is encrypted using the Tencent packer and this makes it harder for analysts to unpack.
Several checks are also carried out before full-screen ads are displayed. The most important of which is the adware is only triggered if the user installs the app by clicking on a Facebook ad. The apps can detect this by using a Facebook SDK feature called “deferred deep linking”.
To avoid falling victim to adware, Avast recommends that users exercise caution when downloading apps, carefully check app permissions and install an antivirus app.
- Keep all of your devices protected with the best antivirus
After working with the TechRadar Pro team for the last several years, Anthony is now the security and networking editor at Tom’s Guide where he covers everything from data breaches and ransomware gangs to the best way to cover your whole home or business with Wi-Fi. When not writing, you can find him tinkering with PCs and game consoles, managing cables and upgrading his smart home.

 Become a TechRadar Insider
Become a TechRadar Insider








