The 10 most common cybersecurity scams uncovered
If it's too good to be true, it probably isn't

Some day your prince will come…
In the beginning there was the internet, and shortly after that came the internet scammers. Online scams include everything from the now-legendary Nigerian prince meme to the less-well-known but infinitely more devious fake shopping websites.
If you were curious about the origins of these deceitful hoaxes, we’ve got you covered. On the other hand, should you be worried about the repercussions of falling victim to one of these fraudulent schemes, we’ll also touch on that.
Online scams are typically malware disguised as rewards or charitable gestures. After all, what is the Nigerian prince scam other than an attempt to get you to care about getting someone else out of a rut, and providing you with a huge payout for doing so?
All the examples below are designed to prick our consciences, or play on our greed or vanity in one way or another. Some of these cyber-scams are actually pretty ingenious, but ultimately malicious – others are just plain malicious.
- Be more secure online with the best password manager.

1. Phishing
You may not recognize it by name – 65% of US and 72% of UK respondents in a Wombat Security report certainly didn’t – but a phishing scam is nothing to take lightly. Phishing is a play on 'fishing' for a good reason – it’s an attempt by criminals to lure you into giving them personal information by appearing to be a legitimate company.
Most phishing scams are found on social networks or delivered via email to multiple users. Those who are unwise enough hand over their personal information, such as account IDs and passwords, can then fall victim to identity theft.
The first known instance of phishing was recorded on January 2, 1996. It was contained within the Windows application known as AOHell, a multifaceted program frequently used for stealing AOL passwords. Today, phishing emails often purport to be from the tech support branch of companies such as Microsoft and Apple.
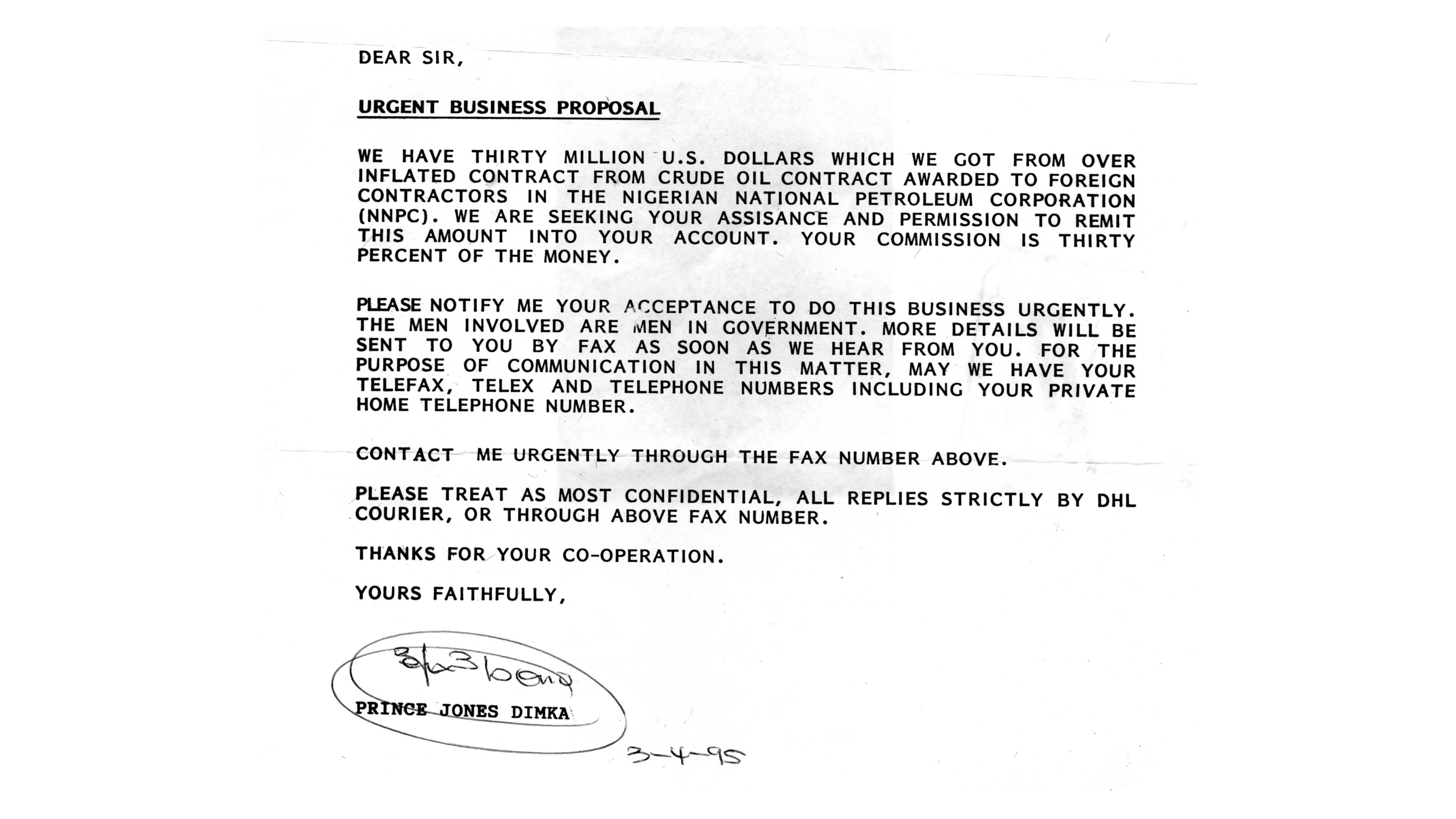
2. The Nigerian 419
The aforementioned Nigerian prince scam is the most notorious of all phishing scams. It’s made its way into pop culture like no other internet scam, being referenced on TV shows and in the worst kind of internet memes from the mid-2000s that used the Impact font, and which we thought were funny for some reason.
Officially dubbed 'Nigerian 419', this scam traces back all the way to the 19th century, when it was said that a 'Spanish prisoner' needed money. This morphed into a postal scam in the late 1970s and early 1980s, during the nefarious years of the Second Nigerian Republic.
In the late 1990s the now-ubiquitous Nigerian prince started asking email recipients to transfer funds to their bank, in return for which they'd be rewarded with a far greater sum of money at an unspecified date in the future. The exact nature of the scam varies, but the results are consistent: over $1.5 billion has been lost around the world to a scam that we now make a mockery of.

3. Greetings card scams
These days, you’ll more than likely see them from a hacked account on Facebook. However, it used to be that greetings card scams were universally distributed over email. They use pathos by pretending to be a friend or relative, yet in reality they’re coming from a scammer.
It’s not clear where they came from originally, but you’ll want to probably want to peruse some of the best antivirus around if you click any of the links found in a greeting card scam.

4. Lottery scams
Remember when you last bought a lottery ticket? No? Well, the lottery scam isn’t going to work very well on you then.
This variation on the ‘advance-fee fraud’, wherein an email tells you that you’ve won the lottery, but you have to first have to pay a small fee in order to collect your earnings, seems completely unbelievable, even by email scam standards. And yet, people have fallen for it, leaving them needing to win a real lottery to make up their losses.

5. Guaranteed loan/credit card
This is a scam that shamelessly preys on poor people, which makes it particularly unpleasant. It takes the form of an email or on-site advert that tells you that you’ve been pre-approved for a credit card or a loan that you haven’t applied for, in an effort to trick you into handing over bank details or other personal information.
Since there’s no way a genuine financial institution would hand you a credit card without taking a look at your credit history, if you get one of these you can safely assume it’s fake news.

6. Fake antivirus software
There’s something particularly brazen about this one – someone sends you a message while you’re online telling you that your computer is infected with a virus, and that you’re in dire need of an antivirus in order to clean up your system… in order to actually infect your computer with a virus.
The key thing here is not to click on the message – and, of course, to make sure that you have (real) antivirus software installed to thwart such attacks.

7. Travel scams
As much as we appreciate how difficult it can be to turn down a free vacation, hear us out: 100% of these offers have a catch. Normally, that catch is a trojan is planted on your computer, or your identity is stolen if you provide the necessary information.
These travel scams usually arrive via email, and caution you that they’re limited-time offers you can’t miss out on. However, if you click on any of the links such emails inevitably include you’ll realize that you not only have to stump up some cash to acquire the offer, but you’ll also have to pay hidden fees on top.

8. Facebook impersonation
It’s not uncommon to see people you know get their user accounts ‘hacked’ on Facebook. Oftentimes you’ll receive a message purporting to be from a friend saying something like ‘Did you see this video of you?’ with a link that you’re invited to click. After that, you’ll probably have to ‘sign-in’ to see the video, which, we can assure you, you definitely weren’t in.
To make sure your Facebook account doesn’t get hijacked you’ll want to enable two-step authentication, number 12 on our advanced Facebook privacy and security tips list.

9. Job offer scams
Chances are that you’re not going to receive a job offer for a position that you didn’t apply for. So, if you receive such an offer, you’ll want take it with a few grains of salt. In most cases, these scams will be attempted by phone, or on LinkedIn to make them vaguely believable.
When you’ve been hooked, the scammer will try to reel you in by asking for funds in order to take your ‘application’ to the next step – at this point you should tell them that you quit.

10. Fake shopping websites
Fake shopping sites aren’t as common as some of the other examples we’ve listed here, but they can be a pain for website administrators who don’t have sophisticated security measures safeguarding their content.
That’s because, while these sites act as actual retailers, offering normally expensive merchandise for a remarkably low cost, they also overtake vulnerable domains to do so. This makes for a double-whammy in terms of scamming people.
To identify these threats, all you need is an eye for spotting malicious links, and a general idea of how much products are worth (although we know how tempting a $70 pair of Yeezys can be).
Securing your digital lifestyle doesn’t have to be a tedious or expensive process. You can achieve that in the next 60 seconds by downloading a trial of CyberGhost VPN here, risk-free.

 Become a TechRadar Insider
Become a TechRadar Insider







