TechRadar Verdict
A horribly basic and broken service, and no sign that the company knows or even cares just how many problems it has. Run in the other direction, as fast as you possibly can.
Pros
- +
Unblocks US Netflix
- +
Torrents supported
- +
Speedy email support
- +
30-day money-back guarantee
Cons
- -
Weak encryption
- -
Small, slow network with frequent connection failures
- -
Broken website
- -
Buggy apps not updated for years
Why you can trust TechRadar
If you like a VPN website to get straight to the point, clearly highlighting its main features, proXPN will be a big disappointment. It's a cluttered text-heavy mass which has twice as many words as usual, yet somehow tells you almost nothing about the service.
There's a degree of scaremongering, too. 'Anyone can intercept your passwords or banking details if they're on the same Wi-Fi network with you (coffee shop, airport)', says the website. Not if you're using a secure connection, which you usually will be.
We browsed the technically confused and occasionally misleading content, and eventually found some fragments of information in a FAQ.
- Want to try proXPN? Check out the website here
ProXPN has torrent-friendly servers in 11 countries. There are apps for Windows and Mac, and the site has setup guides for iOS, Android, Linux and Chromebooks. A kill switch aims to keep you safe if the VPN drops. And the service supports OpenVPN, L2TP and PPTP, which means you should be able to get it running on most other devices and platforms.
With no monthly billing, proXPN requires you to sign up for a minimum of three months, costing the equivalent of $9.98 a month, payable via card, PayPal or Bitcoin. Buying a full year subscription cuts the cost to a more average $6.25, but if you're willing to sign up for two or years, NordVPN, Private Internet Access, Surfshark and many others offer plans in the $2.50-$4 range.
The company tried to win us back with a free plan, although it's very basic, with very few locations and a minimal allowance of just 500MB data a month.
Privacy
ProXPN's privacy policy is shorter than most at under 200 words, and that's often a problem, as there's just not the space to properly explain what a company is doing.
In this case, proXPN just might get away with it, as the company claims it doesn't log anything, at all. This is the relevant section:
"proXPN, B.V. only collects your sign-up information, email, and password. We do not keep logs of connection times, activity, or origin IPs. What we don’t collect cannot be requested."
While that sounds good, as usual with small VPNs, there's no way for anyone to tell whether the company lives up to its promises. You're left to take these claims on trust.
We have no reason to doubt proXPN, but the dates on the policy are a concern. The Canary Policy states that "as of 2016-09-26 we've not had any gag orders relating to our users or our IP's", for instance, while the document was otherwise dated "July 20th, 2015." If the company has 'forgotten' to update its Canary statement for years, it seems at least possible that other updates might also have been missed.
Getting started
Signing up for proXPN was easy enough, and within a few seconds the website redirected us to its Member Area, just about as unimpressive an account page as we've ever seen.
There are no obvious setup guides or installation instructions, for instance. We noticed 'Knowledgebase', 'Support Ticket' or 'Help Center' links, but they all took us to a page saying, 'requests to the server have been blocked by an extension.' On investigation, it looks like the links pointed to a domain previously used by proXPN, which has since expired, presumably been registered by someone else, and now hosts VPN and other ads.
Or, in other words, you've trusted proXPN with your security, and without your knowledge (and maybe even its own), it's redirected you from its site, to a domain controlled by someone else, where (through ad servers) you could be exposed to, well, your guess is as good as ours.
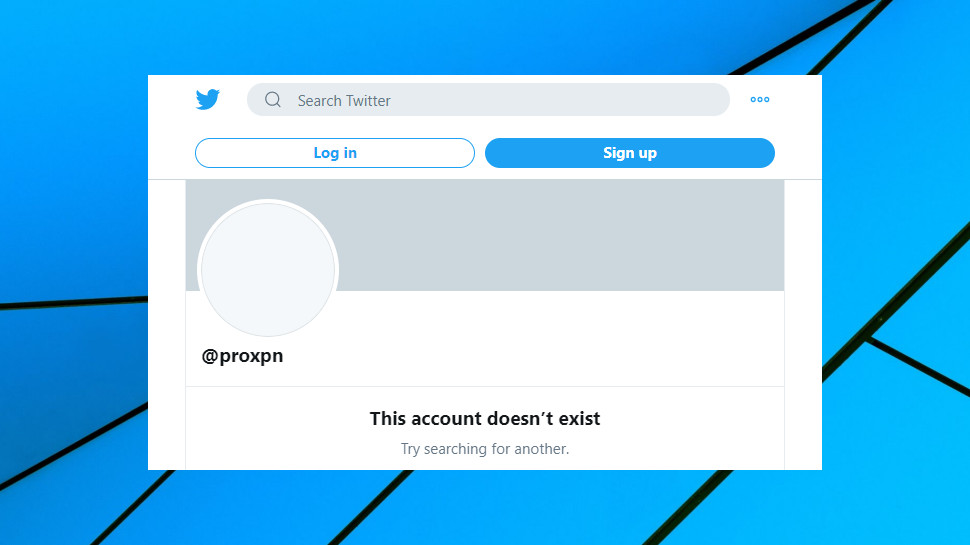
Just when we thought it couldn't get any worse, we clicked the Member's Area 'Announcements' link, and watched as our browser opened a Twitter page with the caption 'This account doesn't exist.'
So it looks like the company can't even make the effort to maintain a Twitter account, has closed it or failed to notice that it's been shut down, and then 'forgotten' to update its website.
We'd call this amateurish, except that's an insult to amateurs. This isn't so much a mistake, as an indicator of massive, industrial scale neglect. It looks to us like proXPN hasn't paid the tiniest bit of attention to its website for years, and if you're not worried about what that means for the rest of the service, then you really, really should be.
Apps
Most modern VPN clients open with a stripped-back console that makes it as easy as possible to use the service: choose a location, click a Connect button, and you're done. Easy.
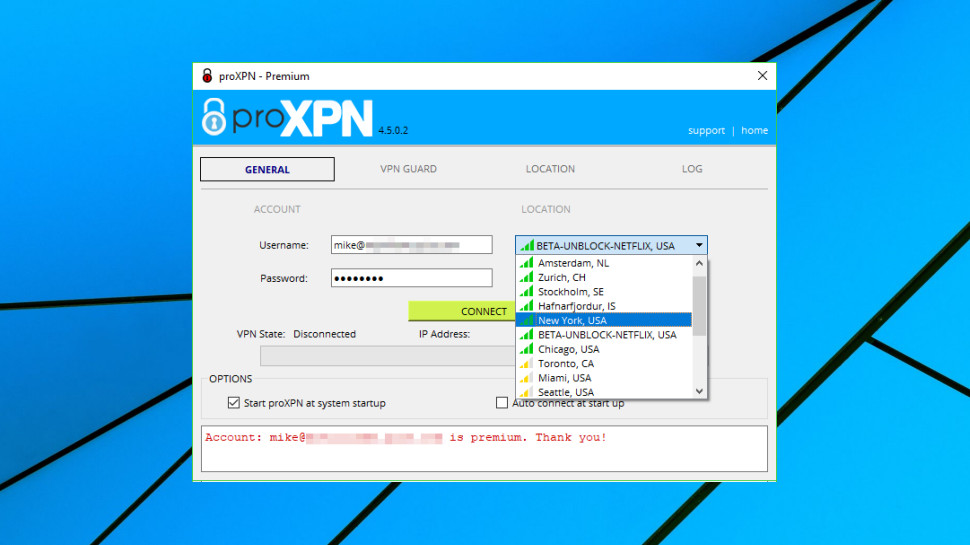
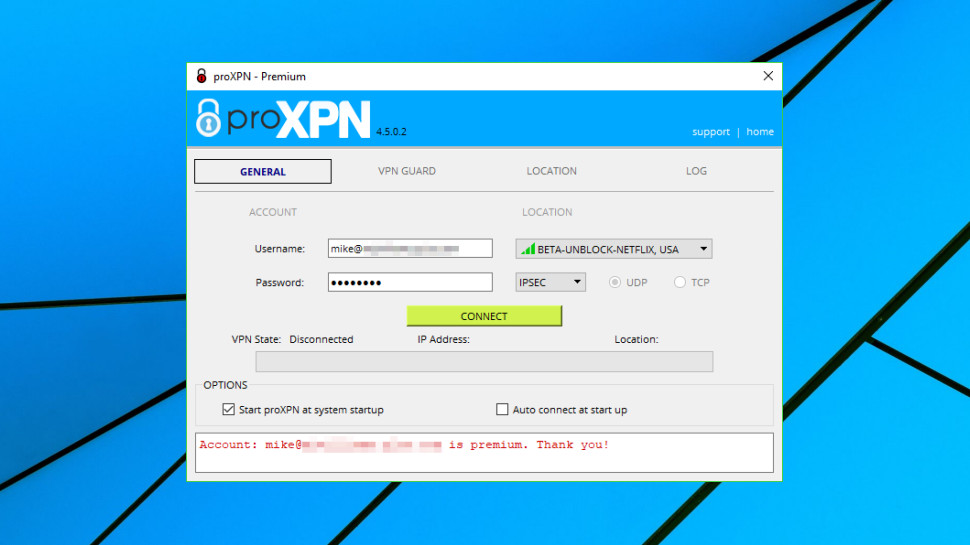
ProXPN's Windows client ignores all that, and crams its opening screen with unnecessary extras. There's your username and password, a choice of protocol (OpenVPN, L2TP, PPTP), UDP and TCP options, an Upgrade button, a couple of startup settings, and a text panel with a log of your OpenVPN connection status. These are all useful options, but there's no reason to have them visible all the time, and it would make much more sense to tuck them away on another tab.
It only got worse when the app told us we only had a limited free account, despite paying proXPN's inflated prices only moments earlier.
We tried to use the app, but with little success. First, it wouldn't connect. We reinstalled, it apparently connected, but the VPN dropped after around 30 seconds. This happened repeatedly.
When the app did say up for a while, we opened a browser to run some tests, but weren't able to access any websites. A DNS issue, maybe. After disconnecting and reconnecting a few times, the client warned its 'VPN service is not installed or not running' and refused to do anything at all until we relaunched.
We took a look under the hood, and proXPN proved as unimpressive as ever. The bulk of the client hadn't been updated for almost three years, for instance. That applies to the bundled version of OpenVPN, too (forget security patches here.)
The service configures OpenVPN using the old BF-CBC encryption algorithm, too. That made the headlines in 2016 when two French computer scientists demonstrated SWEET32, an attack which could theoretically enable attackers to access BF-CBC-encrypted traffic. Top VPNs responded quickly, and for example Private Internet Access immediately alerted its users and made changes to block the attack. But years later, proXPN doesn't seem to have even noticed there's a problem.
Moving over to the mobile apps, we noticed their last updates were also in 2017. Investment, improvements, enhancements, security patches - you won't find the faintest interest in any of that, here.
The Android app looked better, thanks mostly to displaying the server locations on a Google Map. Functionality was much the same, though - the app didn't recognize we had a paid account, and it refused to connect.
Some weird local issue, nothing to do with proXPN at all? Can never rule that out, but a quick check of the app stores revealed horribly low scores (3.3, 2.8), lots of poor reviews, and no responses from the company after mid-2018.
Support
Tired of the app telling us our account was limited, we contacted support. And for the very first time, proXPN performed well, with a reply arriving within an hour.
The positive effect was spoiled a little by the content of the message. 'We're so sorry for the confusion', said the agent, explaining that we should disregard the website telling us we'd paid, because its own systems said we only had a freemium account.
We fired back a reply immediately with a screenshot of the transaction from our PayPal account, and a copy-and-paste of the PayPal email with every detail of the transaction, and a polite suggestion that the company fix this now, please.
The agent returned within minutes: 'Okay, the payment details were not forwarded to our backend. We will have our team look into this issue.' We doubt very much that there is a 'team' - or anyone else - who looks into anything for proXPN, but to its credit, the agent manually updated our account to Premium immediately. After logging out and back in again, the client refreshed its account details and finally recognized that we had a premium account.
Kill switch
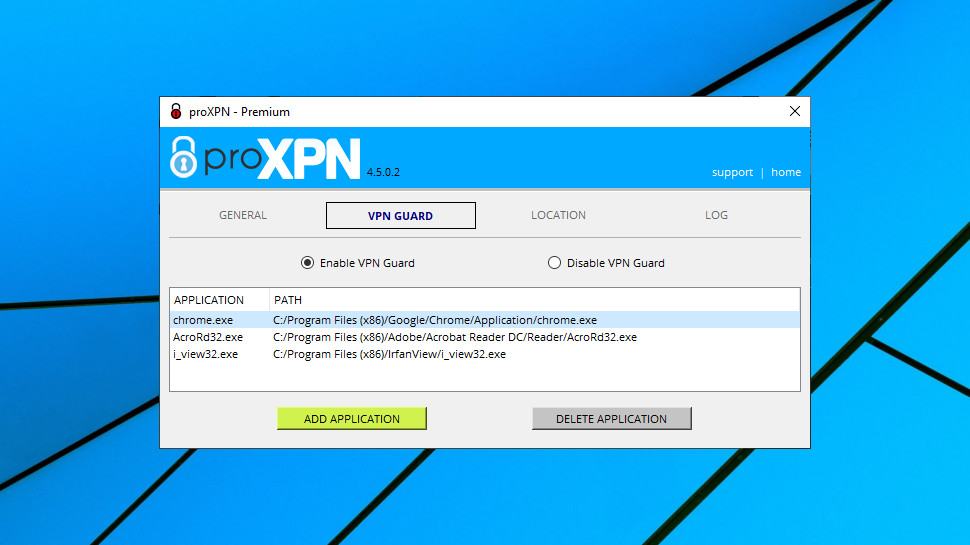
The Windows app has a sort-of kill switch called VPN Guard, which apparently enables telling the client to close specified apps if the VPN connection drops. Sounds useful, but, well...
The first issue is the client can't forcibly close an app. Instead it just does the equivalent of clicking the close button, or pressing Alt+F4, and that could leave an app open if it displays any prompt before it closes ('Are you sure?', 'Do you want to save?').
We also had a major issue in a previous review when we found VPN Guard disabled our internet access and wouldn't restore it. We turned it off, it turned itself back on. We closed the program, our internet remained dead. We uninstalled it, no change. We reinstalled it, tried turning it off again, no luck. There was no support on the website, so we tried raising a ticket, but no help materialized. Eventually, we solved the problem ourselves, but only by some very low-level Windows work.
Kill switches always have some level of risk, but most clients restore your internet access when you turn them off, and the worst we've experienced in the past is the need to reboot before normal access was restored. There's simply no reason or excuse to have even the possibility of failing as badly as this, especially when there's little support.

Performance
The proXPN website claims it 'allows you to access your favorite sites no matter where you live or travel to', but how does it really perform?
We started by logging into the UK server, but BBC iPlayer noticed an issue, telling us 'this content is not available in your location.'
The client offered two specialist Netflix locations, for instance - NETFLIX-UNBLOCK BETA, USA, and BETA-UNBLOCK-NETFLIX, USA - which seemed confusing. We tried the first and weren't able to access any websites; we tried the second and it wouldn't even connect; we manually connected to the New York server, and again, weren't able to access any websites. (Our Outlook installation was able to pick up emails, so we had some connectivity; just not quite enough.)
Switching protocol from OpenVPN to IPSEC, we tried New York again. This time it connected, and we were able to view US Netflix. At last. Okay, proXPN failed to get us into Amazon Prime Video or Disney+, but we were so happy that proXPN had succeeded at something, we barely noticed.
Our speed tests showed below average speeds, with even our local UK servers ranging from 30-45Mbps (top VPNs hit 65Mbps+), and UK-US connections horribly slow, often under 5Mbps. You might, just about get away with this for simple browsing and low-res streaming tasks, but why you would want to, when there are so many faster VPNs around?
Final verdict
Broken links, expired domains, weak encryption, basic apps and a pile of bugs, and a company which either doesn't know how poor its service is, or doesn't care. Don't just avoid proXPN, email everyone in your address book and tell them to avoid it, too.
- We've also highlighted the best VPN

Mike is a lead security reviewer at Future, where he stress-tests VPNs, antivirus and more to find out which services are sure to keep you safe, and which are best avoided. Mike began his career as a lead software developer in the engineering world, where his creations were used by big-name companies from Rolls Royce to British Nuclear Fuels and British Aerospace. The early PC viruses caught Mike's attention, and he developed an interest in analyzing malware, and learning the low-level technical details of how Windows and network security work under the hood.





 Become a TechRadar Insider
Become a TechRadar Insider