TechRadar Verdict
Cisco Umbrella is a robust security system that helps you detect, record, and block network threats and cyber undesirables while relying on AI and threat intelligence to keep your assets squeaky clean
Pros
- +
Robust security
- +
Threat intelligence
- +
Intuitive installation and use
- +
Trial available
Cons
- -
Can deny you access to secure websites
Why you can trust TechRadar
Cisco Umbrella is a cloud-focused security solution that aims to hold guard over your software perimeter before the attackers actually manage to cross its line. To achieve this, it relies on artificial intelligence (AI) that helps it track down the cyber threats and block them before they are capable of inflicting damage to your system.
Its living and beating heart is its browser-linked dashboard from which you can easily both ban IP addresses and get a full overview of what happens with your network at any moment.
Sounds fine, so far? Let’s get a look into the nitty-gritty of Cisco Umbrella’s security features to see if it can really shield you from all types of cybersecurity storms out there.
A TechRadar choice for top URL Filtering provider
Protect your employees and network from web-based threats with URL Filtering. Track web activity. Create custom filtering rules. Block malicious content. Secure your entire organization with just a few clicks with Perimeter 81. Radically simple. Get started today!
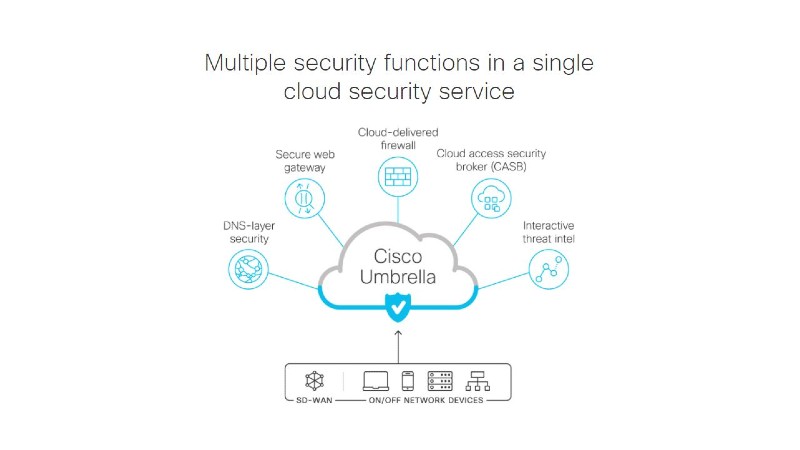
Security features
Cisco Umbrella operates on a software-as-a-service (SaaS) model in which the security threats are managed at the level of the IP and DNS. This means that the threats such as malware, trojans, and botnets can be blocked via ports and protocols prior to them getting in touch with your network.
With Cisco Umbrella, URL filtering is done via its web content filtering feature. It allows the user to manage internet access based on which sites are accessible or blocked for the user’s access.
Appropriate allow and block lists cover individual sites for URL filtering that is also supported by various filtering categories. These include the default setting such as “high”, “moderate”, or “low” as well as support for the creation of a custom list. You are given more granular control over the content your users can access with the help of the URL filtering feature that covers the likes of Google, Bing, or YouTube and cannot be turned off by the users themselves.
All of this is done from a web-based console that allows the user to bring about URL filtering at the level of an individual IP address, user, network, or device.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
To up its game, Umbrella relies on actionable threat intelligence and real-time security. Here, “actionable” means that Cisco Umbrella will rely on the threat intelligence models supplied by its globally renowned Cisco Talos team. Be it a dangerous IP, an undesirable domain, file, or link, Cisco Umbrella will keep an eye over all of your network activities to counter any threat and, equally important, try to learn from dealing with it.
This is helped by having all of your internet activity recorded and categorized which assists your IT administrators with mapping out cyber security risks and plugging the holes based on Umbrella’s prior interaction with cyber threats.
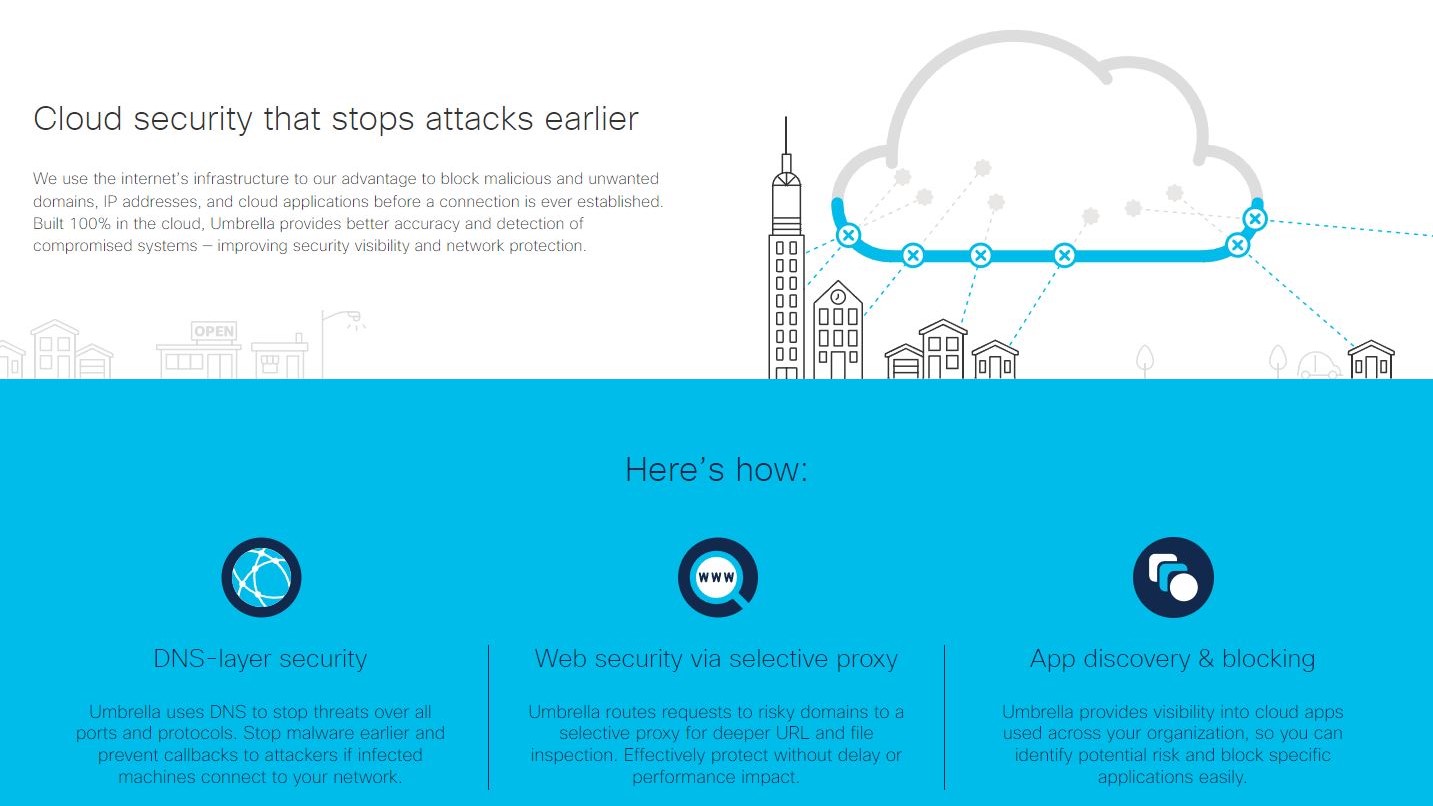
Thus, Umbrella’s DNS-layer security provides you with an easy detection of a breached sub-system by increasing your system’s overall security visibility. Umbrella’s secure web gateway will constantly log and control network traffic, applications controls, URLs, and encounters with malware.
It also relies on the cloud-based proxy that receives all forwarded web traffic with the help of IPsec tunnels and PAC files. Once forwarded, this traffic will be subjected to the existing security policies while countering all detected threats.
Umbrella’s Firewall will apply similar diligence in logging and blocking suspicious traffic that also gets forwarded via IPsec tunnels from all devices. As the tunneling is running, the unwanted traffic gets treatment in line with the valid security policies that can be easily defined and consistently enforced at all times.
Cloud Access Security Broker is yet another security feature that helps you stay vigilant of your collectively used cloud applications. All detected apps will be given a risk appraisal and blocked accordingly or set aside for monitoring for suspicious behaviors. Bear in mind that this level of agility comes with the nuisance of being denied access to otherwise secure sites. Thankfully, this happens infrequently.
Finally, the integration involving Cisco Umbrella and Cisco SD‑WAN can be deployed across the network as a source of umbrella coverage against cybersecurity threats. This includes dealing with the risks posed by the remote workforce, networked devices, and all apps in use.
If you are relying on the use of other Cisco products, you are good to go. You will have a slightly harder time integrating Cisco Umbrella with third-party products which marginally hampers its out-of-box functionality.
Management features
Even beginner users will be happy to know that Cisco Umbrella is a walk in the park when it comes to setup.
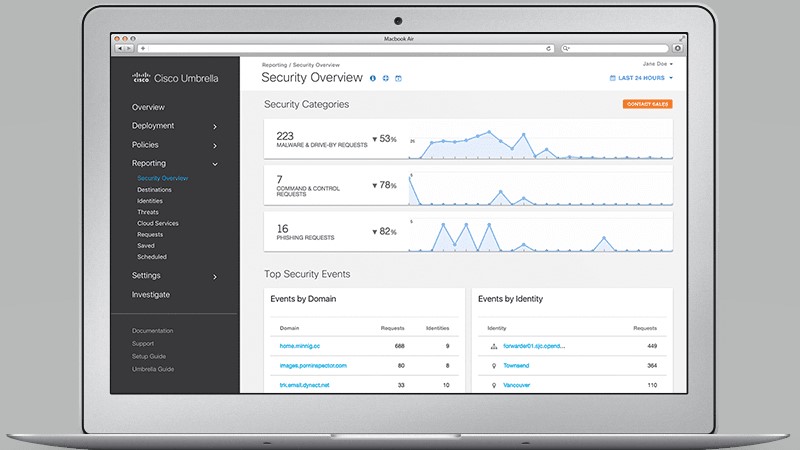
Its intuitive dashboard plays the centerpiece role in fine-tuning your security system and logging all of its activities. First of all, you have the Security Categories around which you get to organize your threat defenses. They range from the standard malware to newly seen domains and crypto mining. The categories help you define appropriate security policies and make sense of the reports on blocked threats.
A more recent addition to the Umbrella Dashboard is the Investigate feature that allows you to keep track of the Umbrella’s threat intelligence. Its Domain Summary feature, for example, will give you information about all applications related to a particular domain, together with the domain’s creation date, IP-related data, country of origin, etc.
Next, A Unique Visitors Score serves as a measure of a domain’s popularity and its changing use patterns.
Usability
While the use cases for Cisco Umbrella will ultimately depend on your specific situation, an ideal implementation involves larger organizations that are facing contemporary challenges such as having to manage a sizable remote workforce.
Those working outside of your premises can easily expose your organization to the malware found on the websites they use. Cisco Umbrella aims to counter this with its remote device monitoring systems that can easily block access to these sites. The same goes for the applications used on your network that you consider a security risk.
Cisco Umbrella is an efficient web proxy system that also comes packaged with a cloud firewall. You can also block resources that do not necessarily act as active security risks at all times, such as your employees’ private email accounts. Apart from security, these resources often prove to be a source of productivity-hampering distractions which are easily blocked with Cisco Umbrella.
Pricing
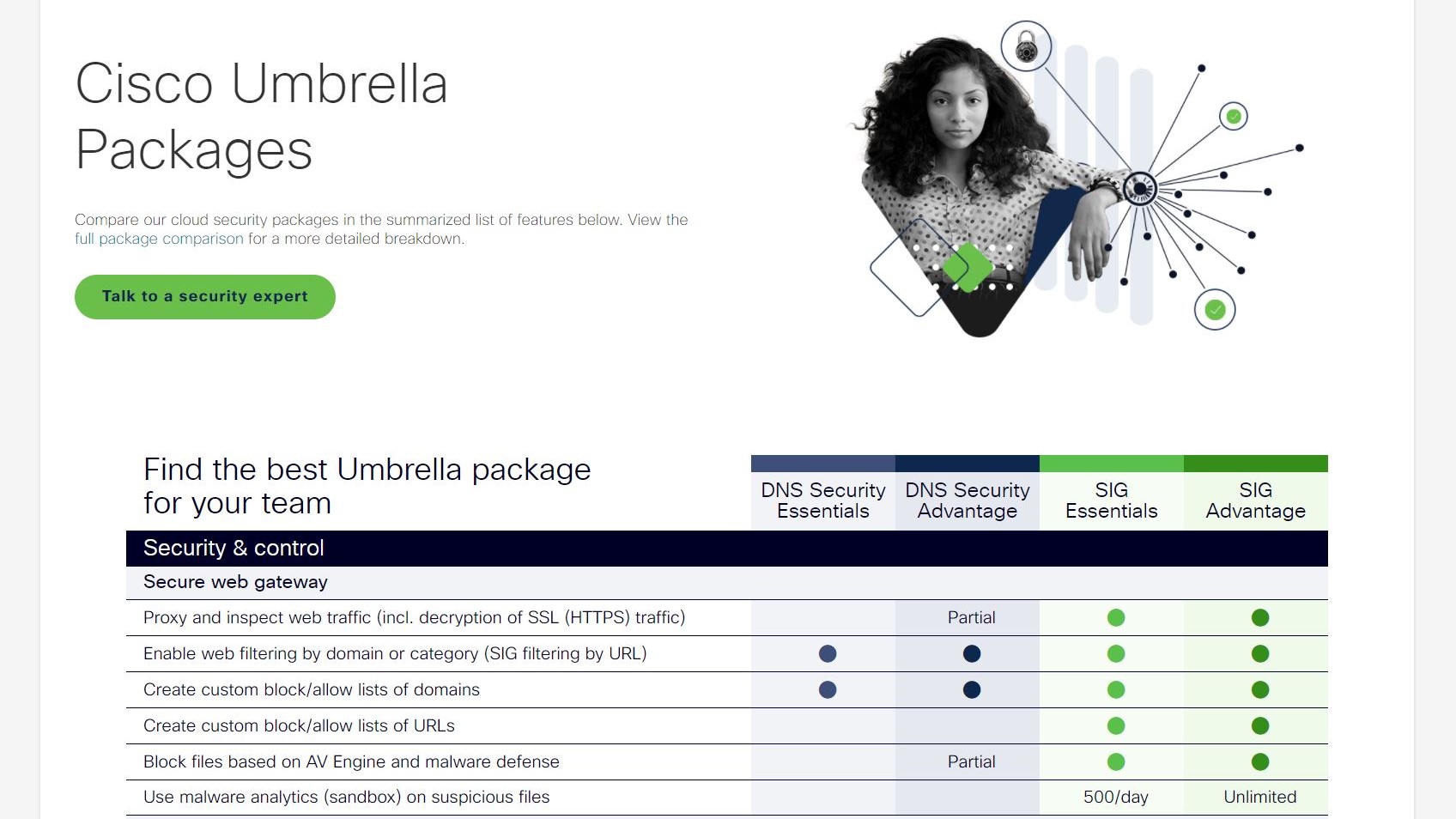
For starters, Cisco Umbrella will give you a fair 14-day free trial, which is a great way to give it a try before you opt for any of the four packages on offer.
The cheapest one, DNS Security Essentials will give you the basic threat-blocking functionality which you should be able to enjoy at the DNS layer and without latency.
DNS Security Advantage provides you with the same level of protection, with an added focus on threat and security insights for easier management of investigations.
More advanced security features and streamlined management are offered with the SIG Essentials package, while SIG Advantage is the flagship product with advanced protective features such as layer 7 firewall with IPS, etc.
Final verdict
Cisco Umbrella is a cloud-based cybersecurity powerhouse that does not rest on the laurels provided by its brand name. It is a robust security system that helps you detect, record, and block network threats and cyber undesirables while relying on AI and threat intelligence to keep your assets squeaky clean.
Paired with the intuitiveness of its setup and management features, you can hardly allow yourself to pass over at least giving its trial version a spin if you are in need of a SaaS-based security solution that can handle all of the modern-day security and workforce management challenges.
We've also highlighted the best firewall, best cloud firewall and best business VPN
Sead is a seasoned freelance journalist based in Sarajevo, Bosnia and Herzegovina. He writes about IT (cloud, IoT, 5G, VPN) and cybersecurity (ransomware, data breaches, laws and regulations). In his career, spanning more than a decade, he’s written for numerous media outlets, including Al Jazeera Balkans. He’s also held several modules on content writing for Represent Communications.