Facebook ads for this fake AI image editor were just an excuse to infect your PC with malware
Popularity of AI image editors is an easy win for cybercriminals

Attackers have been abusing the popularity of AI image editing tools to trick users into installing applications that mimic legitimate tools that are loaded with malware.
The campaign uses hijacked Facebook accounts to push the applications on social media using paid advertising to spread the malware.
The attackers trick Facebook pages into surrendering their credentials with phishing messages that take users to fake account protection pages which then steal their password.
Facebook malvertising
Jaromir Horejsi, a threat researcher for Trend Micro who analyzed the campaign, said “We discovered a malvertising campaign involving a threat actor that steals social media pages, changing their names to make them seem connected to popular AI photo editors. The threat actor then creates malicious posts with links to fake websites made to resemble the actual website of the legitimate photo editor. To increase traffic, the perpetrator then boosts the malicious posts via paid ads” (via BleepingComputer).
The software package that the victims install is not the AI image editor, and is instead the Itarian remote desktop tool which then launches a downloader on the victims device that installs the Lumma Stealer malware. This malware covertly sniffs through the victims files in search of valuable data, such as cryptocurrency wallet files, credentials, password manager files, and browser data.
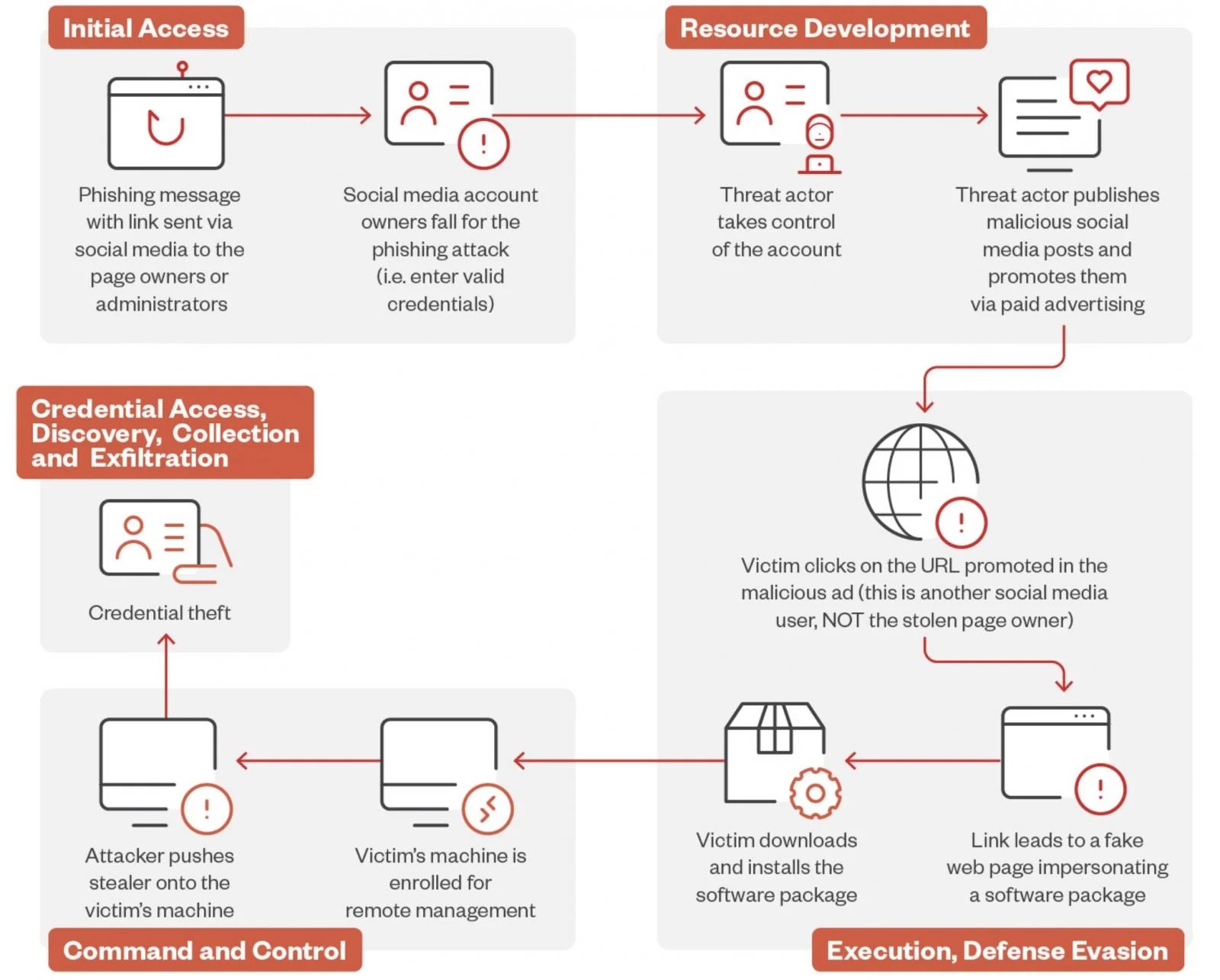
This data is then sold on the dark web, or used to take over other accounts using compromised credentials in order to promote more scams.
In response to the campaign, Horejsi provided some ways to stay safe from the campaign, stating, “Users should enable multi-factor authentication (MFA) on all social media accounts to add an extra layer of protection against unauthorized access. Organizations should educate their employees on the dangers of phishing attacks and how to recognize suspicious messages and links. Users should always verify the legitimacy of links, especially those asking for personal information or login credentials.”
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
More from TechRadar Pro
- Here is our guide to the best anonymous browsers
- Report finds macOS fares worse than Windows and Linux at preventing cyber attacks
- These are the best firewalls around right now

Benedict is a Senior Security Writer at TechRadar Pro, where he has specialized in covering the intersection of geopolitics, cyber-warfare, and business security.
Benedict provides detailed analysis on state-sponsored threat actors, APT groups, and the protection of critical national infrastructure, with his reporting bridging the gap between technical threat intelligence and B2B security strategy.
Benedict holds an MA (Distinction) in Security, Intelligence, and Diplomacy from the University of Buckingham Centre for Security and Intelligence Studies (BUCSIS), with his specialization providing him with a robust academic framework for deconstructing complex international conflicts and intelligence operations, and the ability to translate intricate security data into actionable insights.

 Become a TechRadar Insider
Become a TechRadar Insider







