New research reveals Surfshark, TurboVPN, VyprVPN are installing risky root certificates
Security design flaw paves the way for surveillance or man-in-the-middle attacks

Update: Surfshark and Atlas VPN sent us statements explaining the rationale behind the inclusion of their own CA certs and what is being done to remediate the current situation, click here to read.
Several well-known VPN providers - including Surfshark, TurboVPN and VyprVPN - are among six brands called out for a risky practice that potentially undermines user security.
As part of its Deceptor programme, security research firm AppEsteem found that providers’ apps install a trusted root certificate authority (CA) cert on users’ devices and some providers even fail to obtain users’ consent for doing so.
Article continues belowAppEsteem recently expanded its programme to include VPN providers, researching VPN apps to look for deceptive and risky behavior that could harm consumers.
Share your thoughts on Cybersecurity and get a free copy of the Hacker's Manual 2022. Help us find how businesses are preparing for the post-Covid world and the implications of these activities on their cybersecurity plans. Enter your email at the end of this survey to get the bookazine, worth $10.99/£10.99.
Not good practice
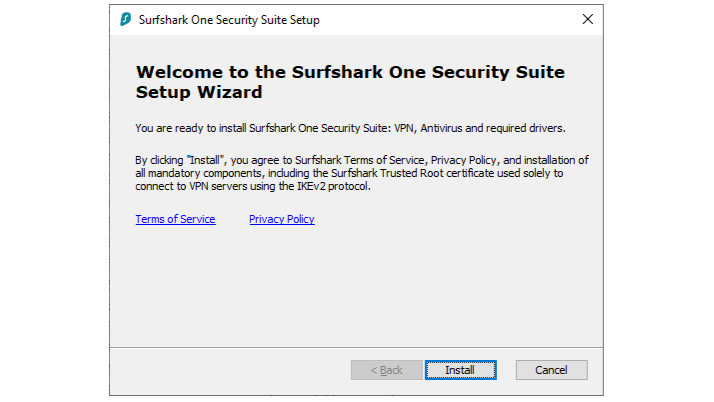
AppEsteem also pointed out that popular VPN provider Surfshark installs its root CA cert on the user’s device even when the user cancels the installation. Surfshark clearly mentions the use of its own trusted root certificate “solely to connect to VPN servers using the IKEv2 protocol”.
TechRadar Pro’s security expert, Mike Williams, stated “Installing trusted root certificates isn’t good practice. ‘If it’s compromised, it could allow an attacker to forge more certificates, impersonate other domains and intercept your communications.”
What are the risks of installing an additional trusted root certificate?
Root CA certs are the cornerstone of authentication and security in software and on the Internet. They’re issued by a certified authority (CA) and, essentially, verify that the software/website owner is who they say they are.
The installation of an additional root CA cert potentially undermines the security of all your software and communications. When you include a new trusted root certificate on your device, you enable the third-party to gather almost any piece of data transmitted to or from your device.
Plus, an attacker who gets hold of the private key that belongs to a trusted root certificate authority can generate certificates for his own purposes and sign them with the private key.
This applies to software applications, websites or even email. Anything from a man-in-the-middle attack to installing malware is possible, as illustrated by hacks in 2021 in Mongolia and in 2020 in Vietnam where CAs were compromised.
The power that Root CA certs have over a user’s device is why state actors like Russia have been pushing citizens to install their new root CA, a move that EFF describes as “paving the way for a decade of digital surveillance”.
The six VPN providers that were found to install root CA certs on user devices are Surfshark, Atlas VPN, VyprVPN, VPN Proxy Master, Sumrando VPN and Turbo VPN. Two of the better known providers on the list, Surfshark and Atlas VPN, both recently joined NordVPN’s parent company Nord Security. However, NordVPN was not among the named providers.
Why would a VPN company want to install a trusted root certificate?
We don’t believe that’s necessary even for IKEv2 compatibility, and most top-rated VPNs do not do this.
When an additional root CA cert is installed by a VPN provider, you are relying only on the provider’s encryption and authenticity checks, as the trusted root certificate can overwrite the encryption and authenticity checks of the actual service you’re using (e.g. Mozilla Firefox, WhatsApp).
This makes it possible for the VPN provider to intercept and monitor essentially all your traffic, in a worst case scenario. We’ve reached out to Surfshark, Atlas VPN and VyprVPN and will update the article when we hear back.
The official statement we received from Surfshark and AtlasVPN
Surfshark
When using the Surfshark root certificate, customers put their trust only in a VPN provider and not a third-party agency that can be compromised. Over the past years, we’ve seen numerous cases where third-party CAs were discredited. Surfshark is a trusted cybersecurity company and ensuring the security of our products and the privacy of our customers is our core goal. Building that trust is paramount to us. As for AppEsteem’s evaluation, we’ve closely cooperated with the company in quickly fixing the highlighted issues. All of them have already been fixed and all Windows users should soon receive an updated version of the app. Also, we’ve been working on turning off the no longer popular IKEv2 protocol and focusing all our efforts on supporting Wireguard and OpenVPN protocols. This will eliminate the need to install the certificate.
AtlasVPN
At Atlas VPN, our priority is to ensure security and privacy across all aspects of our services. Differently from most of the VPN providers, we decided to build our Windows client around the IKEv2/IPSec protocol instead of an older OpenVPN protocol. We chose IKEv2/IPSec as a more modern, more efficient, and faster alternative, which is also natively supported by many OSes. In order for the IKEv2-based client to work properly and to be secure, we had to issue our own certificate instead of relying on a third party.
MiTM attack would only be possible if private keys of our root certificate are compromised, this applies to every issuer of certificates around the world, and we trust in our ability to safeguard it. In the end, having Atlas VPN will significantly reduce the risk of MiTM attack compared to browsing without a VPN at all. We’re actively cooperating with independent reviewers, including AppEsteem, and we’ve always considered such cooperation crucial for improving our service. When it comes to AppEsteem’s analysis, we’re working on adjustments to provide more transparency and information regarding the functioning of our application, and the updated Windows app will be released soon.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!

Désiré has been musing and writing about technology during a career spanning four decades. He dabbled in website builders and web hosting when DHTML and frames were in vogue and started narrating about the impact of technology on society just before the start of the Y2K hysteria at the turn of the last millennium.

 Become a TechRadar Insider
Become a TechRadar Insider







