Best endpoint protection software of 2025
Protect and manage security on mobile devices as well as desktops

Sign up for breaking news, reviews, opinion, top tech deals, and more.
You are now subscribed
Your newsletter sign-up was successful
We feature the best endpoint protection software, to make it simple and easy to protect and manage security on mobile devices as well as desktops.
Endpoint detection and response works by monitoring all of the devices connected to your business' network, known as 'endpoints' which can include computers, mobile devices, routers, and even internet enabled smart devices such as lightbulbs and fridges (yes, really).
If an intrusion or suspicious activity is detected, the endpoint protection will notify your security team or IT admins, helping them narrow down the threat's location and respond to an attack faster.
Our experts have tested 20 of the best endpoint protection services from brands such as Avast, Cisco, and Malwarebytes, looking at how well they perform across a range of platforms and operating systems and how easily they can be customized to add additional devices, while also factoring in additional features such as extra security tools, customer support, ease of use, and value for money.
To make the most of an endpoint protection service, it may also be worthwhile investing in other business protection software. To help you out, we have also listed the best business VPNs, and the best SMB firewalls for your convenience.
If you're looking for extra protection, we've also featured the best identity management software.
Quick list

As one of the oldest names in the cybersecurity industry, Avast's endpoint protection offering is expectedly solid. It utilizes the company's Cloud Protection to deploy across all endpoints upon threat detection. A firewall, VPN, antivirus, and USB protection are all included.

A solution from another titan of the industry, the main selling point of Cisco Secure Endpoint is its resilience, with the company claiming it can block more threats than any other. It also has great cross-platform support, but the lack of clear pricing, while common for EPP solutions, is still a shame.

Malwarebytes Endpoint Protection is well priced, undercutting the competition and allowing many devices on a single plan. It's also quick and easy to setup, and puts hardly any strain on your resources. It might not be as proactive in its protection as others, though.
Load the next 6 products ↓

With one of the best interfaces we've used, Vipre EDR is also another very well priced product. It comes with AI-powered threat detection, as well as anti-spam tools, intrusion protection, and other typical endpoint protection features. Linux and mobile devices don't get agent software, though.

Made for SMBs, ESET PROTECT can cover mobile and desktop endpoints, including Macs and Linux (although the latter is somewhat limited). It comes with various useful features, such as a tool that can scan Microsoft OneDrive, Exchange Online, and virtual machines on Azure. The interface is also good to use.

Although the pricing can be obscure, Trend Micro's Vision One has a lot of security features, including one that allows you to simulate attacks on endpoints. It is modular in nature, so can be extended by downloading various add-on apps if required. There are also tutorials to help with deployment too.

If you're looking for supreme detection rates, then Bitdefender's offering is worth your attention. There are also many features here at a good price, and we welcomed the granular control over policy settings. Unfortunately, there is no mobile device coverage.
WatchGuard offers a number of endpoint protection services, and again it adopts a modular model, allowing users to pick and choose what they want. The EPP is compatible with more platforms than any other rival we've reviewed, but our installation on a basic machine wasn't plain sailing.

With a feature-set that's very impressive, Threatlocker is a generous service. The Ringfencing feature, for instance, allows you to set boundaries for how apps interact, and Network Control can open ports automatically based on an endpoint's location. The interface is very basic, though.
The best endpoint protection for business of 2026 in full:
Why you can trust TechRadar
Best endpoint protection for business overall
1. Avast Business Security
Our expert review:
Reasons to buy
Reasons to avoid
✅ You want ease of use: Avast was easy and quick to setup according to our tests, and the central dashboard is user friendly, making it a breeze to navigate your way around.
✅ You want good email protection: Avast's offering comes with a feature called 'Mail Shield', which is compatible with popular clients like Microsoft's Outlook. It scans for threats and has a sandbox to safely run apps you're not sure about.
❌ You want mobile protection: Perhaps the most glaring omission from Avast Business Security is the lack of mobile protection, so if your firm has company devices, you might want to opt for another service.
🔒 Avast Business Security is a comprehensive endpoint solution that includes a firewall, antivirus, VPN, email and USB protection, all controlled from an intuitive central hub. It also responded well to our virus tests. The only downside is the lack of mobile protection. ★★★★★
For over 35 years Avast has been researching and developing security software, so when they say they have a solution for endpoint protection we should all pay attention.
Avast 'Premium' Business Security involves using Avast 'Cloud Protection' to automatically deploy protection across the entire user base when a threat is detected. This protection not only includes antivirus but a VPN, firewall and USB protection.
The software also incorporates a 'Mail Shield' which works with email clients like Microsoft Outlook to scan for threats. The integrated 'Sandbox' also allows users to run applications safely.
During our tests we were very impressed to see the Avast agent aborted the download of our test computer virus. When we introduced a real trojan virus to the test machine, it was also immediately detected and quarantined. The Avast Business Hub also generated reports to confirm the suspect files had been sanitized.
Read our full Avast Premium Business Security Review.
Our EXCLUSIVE Avast business antivirus deal
Avast Ultimate Business Security | From $43.71 $34.97/ year
Save 20% This is Avast's biggest and best business endpoint protection. That means the usual standard of protection, with a lot more bells and whistles. If you want to be confident that your office infrastructure is as safe as possible, then hit that 'View Deal' button (or click here if you're in the UK).
Best flexible EPP
2. Cisco Secure Endpoint
Our expert review:
Reasons to buy
Reasons to avoid
✅ You want strong security: Cisco Secure Endpoint neutralized out test threats very quickly. It also offers a sandbox for in-depth analysis of threats, and it uses AI to spot threats based on their behavior, not just relying on signature detection.
✅ You want good platform support: Cisco Secure Endpoint is one of the few solutions that covers multiple platforms, supporting as it does Windows, Mac, and Linux systems, as well as Android and iOS devices.
❌ You want clear pricing: The main downside of Cisco's solution is that the pricing isn't made all that clear, with no plans listed on its website, so you will need to get a quote. This is fairly common in the endpoint space, though.
🔒 Cisco Secure Endpoint is another very competent and complete package, with intelligent threat detection that offers brilliant security across a wide variety of platforms. You'll have to get a quote for the cost, though. ★★★★½
For the past 40 years Cisco has been wowing consumers with its dazzling range of technology and software products.
In the company's own words, Cisco Secure Endpoint (formerly 'AMP for Endpoints') is 'built for resilience'. Cisco even makes the bold claim that the platform blocks more threats than any other security provider.
When it comes to brass tacks, we were unable find any specific pricing on Cisco's website but interested parties can contact one of their sales representatives. In fairness, this type of pricing model is quite common for the EPPs we've reviewed.
The good news is that unlike most EPPs we've reviewed, Cisco Secure Endpoint is truly cross-platform, supporting Windows, macOS, Linux, iOS and Android devices.
The platform maintains a database of every file it's scanned, allowing it to automatically block 'good' or 'bad' ones without intensive scanning through using a scoring system.
Cisco Secure Endpoint also employs machine learning analysis to identify malicious files based on their behavior. It supports detection of polymorphic malware to stop bad actors from making small changes to viruses to avoid signature detection. Once threats are detected, the platform is also capable of performing sandboxing and/or advanced forensics.
During our tests, when we tried to download a fake computer virus using the Microsoft Edge browser, the Cisco agent immediately detected it and blocked the download. We were impressed that the threat was prevented before it even gained a foothold on the test machine.
When we manually tried to copy a real trojan virus to the machine's 'Downloads' folder, the threat was also immediately detected and quarantined.
This means, aside from slightly vague pricing we found Cisco Secure Endpoint to be faultless.
Read the full Cisco Secure Endpoint review.
Best lightweight client
3. ThreatDown Endpoint Protection for Business
Our expert review:
Reasons to buy
Reasons to avoid
✅ You want lightweight protection: The advantage of Malwarebytes Endpoint protection is that it isn't very resource intensive, making it quick to setup and run - yet it still offers advanced threat protection.
✅ You want a good price: Malwarebytes Endpoint Protection is well priced, and offers coverage for many devices.
❌ You want proactive protection: During our tests, Malwarebytes only kicked into gear once we tried to download our dummy malicious payload - the 'BrowserGuard' extension failed to actually prevent the download itself.
🔒 ThreatDown Endpoint Protection is lightweight and well priced, but still provides advanced threat protection. It didn't block threats straight away, though - but it still stopped our test virus from actually running. ★★★★½
From 2016 onwards the cybersecurity experts at Malwarebytes have been producing EPP products such as Malwarebytes Endpoint Protection, which has now been rebranded as ThreatDown Endpoint Protection.
Pricing is extremely competitive, and key features include a very lightweight client, which is quick to download and setup. Management of Endpoints takes place through Malwarebyte's 'Nebula' cloud portal, complete with introductory video.
The platform engages in application 'hardening' to reduce attack surfaces, as well as behavioral-based analysis and blocking. The company claims this is also combined with 'zero day' protection which uses payload analysis to proactively block threats.
ThreatDown also incorporates 'web protection' technology to protect endpoints from malicious URLs. When we contacted Malwarebytes to request a trial for this review, they also suggested installing their free 'BrowserGuard' browser extension on our test machine.
We decided to put the platform through its paces after setup and downloaded a fake computer virus in compressed (ZIP) format in Microsoft Edge. The 'BrowserGuard' extension seemed to raise no objection to us doing this.
After we extracted and tried to run the program, the Malwarebytes agent sprang to life and contained the threat. Similarly when we copied a real trojan virus to the test machine, the agent only blocked and quarantined it when we actually tried to run it.
Most other EPPs we've reviewed are able to block downloads of malicious files or proactively quarantine them before the user has a chance to to launch. Still, the fact that threat detection works differently doesn't mean it's any less effective.
Read the full Malwarebytes Endpoint Protection Review.
Best UI
4. Vipre Endpoint Security
Our expert review:
Reasons to buy
Reasons to avoid
✅ You want a clear interface: One of the best aspects of Vipre Endpoint Security is its user friendly interface, which is vibrant and helpful at the same time.
✅ You want good and clear pricing: There is an annual subscription for $60 per seat, supporting up to 10 seats. This makes it one of the better priced endpoint protection services out there.
❌ You want strong agent software: Unfortunately, there is no agent software for mobiles or for Linux, and our setup on Windows proved to be more troublesome than we expected (although the company assured us this was only because we were using a beta version provided to us).
🔒 Vipre Endpoint Security is a well-priced solution with a great interface and plenty of advanced features, including AI malware detection and anti-spam. However, the agent software was only available on Windows and Mac, although there is still a console app for mobile. ★★★★½
Vipre Security Group was originally founded in 1994 and Vipre Endpoint Security - formerly Vipre EDR - is one of their flagship products.
There's a basic pricing model of $60 per seat, for up to 10 seats, billed annually via automatic subscription, unless you email to cancel. This makes Vipre Endpoint Security one of the most competitively priced platforms we've reviewed.
The platform supports AI-driven malware detection, deploying agents with firewall, email scanning, network intrusion detection, DNS protection, web exploit detection, and anti-spam engines.
Vipre also claims the platform has additional security measures, including correlation engines that combine raw events, security events, and contextual data to identify zero-day, "living-off-the-land", and gray zone threats not detectable by regular antivirus.
Agent software is available for both Windows (from Windows 7 SP1 onwards) and macOS. We were sorry to see that Linux and mobile devices weren't listed, though the console itself has an excellent mobile interface.
During our tests it took three tries before we could install the agent software and update it successfully. VIPRE were keen to point out that this was because the trial account that they set up for us was on the beta version of the platform. These issues don't exist in VIPRE's main production environment.
Once the agent was running it was immediately able to detect the fake computer virus we'd downloaded to our test machine in ZIP format, immediately quarantining the threat.
We next tried to copy a real trojan virus to the test machine's 'Downloads' folder, only for the agent to immediately detect and quarantine it too.
This combined with a colorful and helpful UI definitely make Vipre Endpoint Security a platform to consider.
Read the full Vipre EDR Review.
Best endpoint protection for a quick start
5. Acronis
Our expert review:
Reasons to buy
Reasons to avoid
✅ You want extra features: Apart from being an endpoint management software, Acronis Cyber Protect Cloud also includes anti-malware, antivirus, and several other features.
✅ You want a fast setup: The setup is a breeze, with only a few clicks and you’re already at the Acronis Cyber Protect Cloud console. After that, you only need a few minutes to get everything up and running.
❌ You want fixed pricing: For this particular solution, there is no fixed pricing, and you’ll need to register and use their pricing calculator to get an estimate.
🔒 Acronis Cyber Protect Cloud is a powerful endpoint management solution with lots of features thrown in the mix. Fast setup, great threat detection, and ease of use are just some of the main points of this great software. ★★★★½
Acronis is a Swiss company that’s been in the business for over 20 years. While they have more services, the one to focus on for this purpose is Acronis Cyber Protect Cloud. This software contains several products in one, like anti-malware, antivirus, and endpoint management.
As an endpoint security platform, the software has an “Acronis Active Protection” feature which is an AI-based detection routine and analysis tool to detect and prevent malware and ransomware. One can also perform backups of an entire endpoint to the cloud via its agent software.
A very interesting thing to note is that in addition to all the features, for instance, real-time threat detection, the software has add-ons that you can purchase to upgrade it even more. Add-ons like "Advanced Email Security" with anti-phishing and anti-spoofing engines.
As soon as you fill out the registration form an activation link will be sent to you which automatically leads you to the software’s cloud console. This makes the actual setup very fast. The interface itself is simple, with navigation being quick and easy.
Depending on your needs, Acronis has different pricing packages for several of its products. However, for “Acronis Cyber Protect Cloud” specifically, there is no fixed price, and you’ll have to use their calculator for a rough estimate. That said, you can expect to pay either “per workload” or “per GB”. The former means that you pay per number of devices or workloads protected, while the latter means you pay based on the volume of data being protected.
Read the full Acronis review.
Best endpoint protection for remote deployment
6. ESET PROTECT Advanced
Our expert review:
Reasons to buy
Reasons to avoid
✅ You want to operate remotely: One of the advantages of ESET PROTECT is that you can deploy and manage endpoints remotely from any device, thanks to its cloud interface.
✅ You want a Linux client: ESET's solution offers a client that you can install on Linux machines, which is something of a rarity in the endpoint protection world.
❌ You want remote control over those Linux endpoints: Despite having Linux clients, ESET can't offer the same level of remote admin features that it does for Windows and Mac systems.
🔒 ESET PROTECT offers protection for numerous platforms, both desktop and mobile, and allows for remote deployment and management via its cloud interface. Although Linux is covered, the amount of control you have over them isn't as comprehensive as you get over Windows and Mac machines. ★★★★
ESET PROTECT is pitched at small and medium-sized businesses and covers Windows, and macOS, and with certain conditions also extends to Linux, Android and iOS endpoints as well.
The security product brings with it a software firewall, the ability to detect malicious communications over the Internet and then block the offending process that initiated it. You also get a Host-based Intrusion Prevention System (HIPS) that uses a predefined set of rules to identify and stop dubious behavior.
ESET monitors and evaluates all executed applications on the endpoints and based on their reputation and behavior will block any processes that act like ransomware. It keeps an eye on typically exploitable applications such as browsers, document readers, email clients, Flash, Java, and such, to look for identifiable exploitation techniques.
The endpoint bundle also includes the File Security product for Windows Servers and Microsoft Azure that can scan and monitor a connected OneDrive storage and VMs.
During our tests, we found ESET failed to quarantine our fake computer virus in compressed (ZIP) format but as soon as we extracted the file it was detected and deleted.
We also enabled the 'Web Control' feature and tried to visit The Pirate Bay to search for some (legal) downloads of Ubuntu Linux. Although we found we could search torrents, downloading was blocked.
When we logged into the ESET cloud console after running these tests, the 'Detections' section displayed all security alerts.
Read our full ESET PROTECT review.
Best endpoint protection for modules
7. Trend Vision One
Our expert review:
Reasons to buy
Reasons to avoid
✅ You want lots of features: There are many security features within the Trend Vision One platform, including the ability to integrate with third-party services.
✅ You want a modular service: Trend Vision One works on the basis of credits, and you use them to buy licenses for certain modules in the platform, so you only take what you need.
❌ You want clear pricing: Because of Trend's modular approach, we found it difficult to ascertain how much on average a typical customer would likely spend on Vision One.
🔒 Trend Vision One takes a different approach to endpoint solutions, by operating a credit system to purchase modules in the platform. There are also many security features, but working out how much you'll end up paying may take some effort. ★★★★
Trend Micro's Vision One debuted in 2021. It's touted as an XDR (Extended Detection and Response) platform to allow customers to detect and respond to threats from a single console. It uses a 'credits' system to buy licenses for individual products, though in our research we had trouble finding out how much on average it costs to use Vision One specifically.
The platform includes an 'Operations Dashboard' for quickly assessing risks such as user and device vulnerabilities. It even delivers a helpful 'risk index', though we found this was unaffected by detection of a fake virus on our test machine. Trend Vision One's features can be extended by adding various apps.
The 'Security Assessment' app is useful for executing quick scans on remote mailboxes and endpoints. The 'Workbench' app displays alerts in response to threats, while the 'Targeted Attack Detection' app uses threat intelligence from the Trend Micro Smart Protection Network to identify early indicators of attacks.
Another notable feature of Trend Vision One that impressed us is that it does allow you to run simulated attacks on endpoints. Ultimately though we decided to run our own tests in the interests of fairness.
The Agent software provided by the platform immediately detected and quarantined our test virus file, even though it was in compressed (ZIP) format. A short while later, we received an e-mail alert from Trend Micro alerting us to the detection and providing a link to view details in the aforementioned 'Workbench' app.
Read our full Trend Vision One.
Best endpoint protection for detection rates
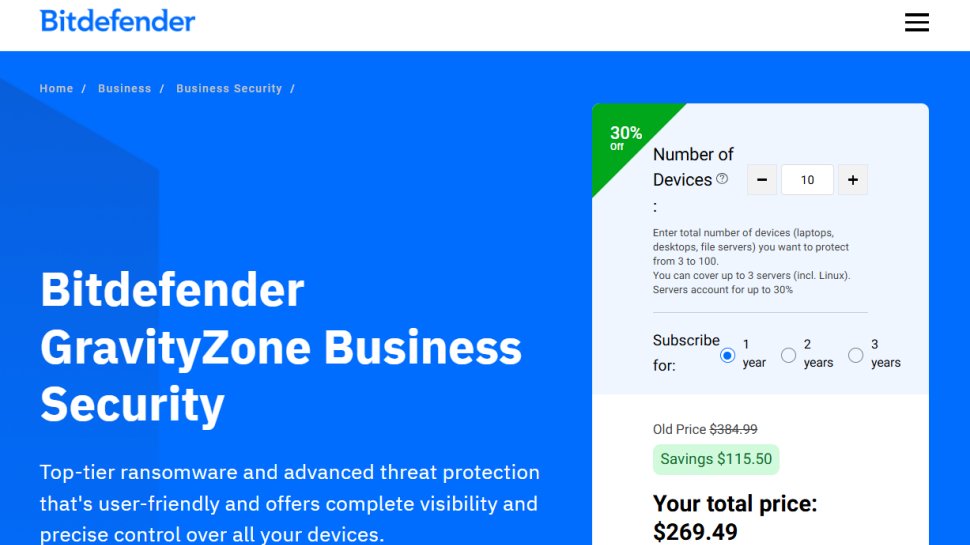
8. Bitdefender GravityZone Business Security
Our expert review:
Reasons to buy
Reasons to avoid
✅ You want to get going quickly: From our tests, Bitdefender's offering was one of the quickest and easiest setups we've experienced, kicking straight into action once downloaded.
✅ You want a great interface: From the welcome screen to the console management hub, GravityZone is helpful and easy to navigate, and the dashboard that offers summaries of your endpoints' security is also one of the best we've seen.
❌ You're on a budget: Bitdefender GravityZone is on the more expensive end of the spectrum, and beware that some features bundled with the trial version have to be bought separately when it comes time to parting with your cash.
❌ You want mobile coverage: This is sadly yet another endpoint protection solution that doesn't cover mobiles.
🔒 Bitdefender GravityZone Business Security offers some great features in a well-packaged outfit, making it very easy to setup and use. The pricing is a bit steep, though, and no mobile devices are covered. ★★★★
BitDefender GravityZone Business Security can command some high prices, placing it at the higher end of the spectrum for endpoint protection platforms. However, there are offers on to net some good savings.
For our tests we used a fake computer virus, provided by the good people of EICAR. Our initial 'Quick Scan' failed to reveal it but this was unsurprising as these types of scan only seem to check the C:\Windows\System32 folder on our Windows 11.
We next ran a 'Custom' scan to check the 'Downloads' folder specifically where the virus was located. The Bitdefender Agent recognized the virus immediately and quarantined it.
For our final round of tests we tried to download the fake virus directly from the EICAR website several times as a compressed (ZIP) file. In each case the agent either deleted the virus or changed file permissions, so we couldn't access it.
Our only criticism was that we had to open up the agent software to see the detection alerts - other endpoint protection software we've reviewed usually shows a pop up notification as soon as a threat is detected.
Read our full Bitdefender GravityZone Business Security review.
Best endpoint protection cross-platform
9. WatchGuard Endpoint Security
Our expert review:
Reasons to buy
Reasons to avoid
✅ You want advanced threat protection: WatchGuard offers an antivirus that is next-gen, so it can detect more malicious files and programs than those based on signature detection alone. It can also suggest security updates for your endpoint.
✅ You want good compatibility: WatchGuard Endpoint Security works not only on Windows, Mac, Android and iOS devices, but also on Windows on ARM machines and Windows Server.
❌ You want an easy setup: WatchGuard proved to be quite troublesome when we tried to get it working, failing to install on Windows 11 on numerous occasions, and alerts only came when we manually synced with the Panda agent.
🔒 WatchGuard Endpoint Security offers advanced endpoint protection across 100 devices and supports numerous platforms. We did encounter setup issues during our testing, though, but there is at least a 30-day free trial for you to see for yourself how it performs. ★★★★
WatchGuard was first founded in 1996 and their flagship product was a single firewall program. Since then WatchGuard has created any number of security solutions, as well as acquiring Madrid-based Panda Security in 2020.
WatchGuard allows interested parties to secure up to 100 endpoint devices with a 30-day free trial. From accessing the free trial and examining the various licenses available, we were able to discover there are in fact a number of solutions: WatchGuard Advanced EPP, EDR, EPDR and 'Advanced' EPDR.
For the sake of simplicity we chose a trial of WatchGuard EPP, though this doesn't tell the full story: users can subscribe to additional 'security modules'. These handle tasks like patch management, full disk encryption and multi-factor authentication.
The platforms NGAV (Next-Gen Antivirus) provides detailed, real-time detection and reporting. The agent software (named 'Panda') is compatible with a huge range of devices including Windows, Windows Server, Windows for ARM devices, macOS, Android and iOS. This makes WatchGuard EPP by far the most cross-compatible platform we've ever reviewed.
During our tests we tried to download the agent software and install it to our test machine running Windows 11 but setup failed the first three times. Eventually we rest the test machine and were able to get the Panda agent running the fourth time.
We also tested the platform's malware detection features. We were able to download a fake computer virus in compressed (ZIP) format but as soon as we tried to extract, the agent software immediately detected and quarantined it. Next, we tried to copy a real trojan virus to the 'Downloads' folder of our test machine with the same result.
When we logged into the cloud console however, there were no reports of these threats until we manually clicked the 'sync' option on the Panda Agent. The console then displayed details of the threats in a helpful infographic.
Read the full WatchGuard EPP review.
Best endpoint protection for features
10. Threatlocker
Our expert review:
Reasons to buy
Reasons to avoid
✅ You want advanced features: In addition to the basics, ThreatLocker also offers unique features, from ringfencing application interactions and setting time slots for their access, to opening ports based on precise application conditions.
✅ You want good support: In our experience, we found the support team at ThreatLocker to be very helpful, even offering to help us setup the platform on our devices.
❌ You want a sleek interface: ThreatLocker's UI is about as basic as it comes, but it is at least well laid out and a beta version is available for something a bit more visually appealing.
🔒 ThreatLocker is a powerful endpoint solution with a great setup experience and plenty of interesting features. The UI is quite spartan, though, but there is at least an upgraded beta version for this. ★★★★
Threatlocker is a newcomer to the cybersecurity game - the Florida-based company was only founded in 2017, long after security giants like Symantec and Kaspersky. Still, the company's endpoint security platform has one of the most impressive array of features we've ever seen.
It includes basic features we'd expect to see such as black and whitelisting of applications. We were much more intrigued though to read about Threatlocker's 'Ringfencing' feature, which allows managers to set boundaries for how certain applications interact.
Threatlocker also supports 'Dynamic Network Control' to regulate traffic, as well as open ports only for authorized applications using dynamic ACLs (Access Control Lists) or agent authentications. The Threatlocker website rightly points out that this is an often overlooked security gap for EPPs.
Users can also set time-based policies, so applications can only be accessed and/or perform certain functions at an allotted time during the day.
Threatlocker's extremely friendly and helpful support team, offered to contact us and set up a demo to walk us through the onboarding process. We appreciated the offer but decided to go it alone to see how easy the platform is to use.
Upon login, we found that the main interface is a little spartan. At times it feels more like editing a database rather than editing an online portal. That said, the left hand pane is logically laid out and it's easy to expand sections to see further options. There is, however, a a 'Beta' portal which offers a much more modern-looking UI.
During our tests, when we tried to extract the fake computer virus in compressed (ZIP) format, the Threatlocker Agent immediately changed file permissions to contain the threat. We next tried to copy a real trojan virus to our test machine's 'Downloads' folder, which was also immediately detected and quarantined.
A bare-bones interface is a small price to pay for a platform so powerful and versatile.
Read the full Threatlocker review.
Best endpoint protection software FAQs
What's the difference between consumer and business antivirus protection?
Consumer antivirus tools are designed to protect individual devices from cyber threats. It's suitable if you run your business from just one device that needs protection. On the other hand, business antivirus tools provide protection for a network of devices within an organization. They differ in several other ways including
Setting up consumer antivirus software is pretty easy. You just buy and install it on the device that needs protection. In contrast, business antivirus software works through a centralized management system; an IT administrator can install the software on multiple devices from their control panel. This panel can modify settings, deploy updates, and receive alerts about the devices connected to the organization’s network.
Business antivirus tools are called endpoint security because they protect multiple devices under a single network, and these devices are called endpoints. Any device connected to the network is automatically protected, while in the consumer sphere, you must manually install the software on each device that needs protection.
Another distinction between consumer and business cyber software is that the former is reactive and the latter is proactive. Consumer systems aim to prevent known malware from infecting your device, although some may slip through. If malware slips through, the antivirus software then mounts a defense to prevent it from corrupting the system.
Proactiveness, on the other hand, is more focused on preventing any attack from occurring in the first place than defending against one that has occurred. The software anticipates the threats and works to close any vector that the threat can come from.
Think of the reactive approach as security personnel guarding the door of a building and the proactive approach as a military battalion patrolling the perimeter of a building to identify and eliminate potential threats before they can strike.
Business antivirus software is much more sophisticated than consumer-level ones. Consumer software operates more simply; it scans files on your device for signatures associated with malware. The companies behind these tools have large databases of known malware signatures that their tool runs checks against. But, business cyber software goes more than that. They usually employ artificial intelligence and machine learning to detect threats whose signatures may not be known.
Business software also usually provides extra features outside endpoint protection. For instance, it can come with a virtual private network (VPN) service, a password manager, a registry scanning tool, etc. You may find these extra features on consumer software, but it will likely come at an additional cost, unlike business software where it‘s free.
Business software is more complex than consumer software, so it costs more to buy and maintain. Consumer software usually has a fixed annual or lifetime fee that you can pay for each device, while pricing for business software varies according to the number of devices on the network and other related factors.
Expect to pay much more for endpoint software covering an entire network than you would for consumer software installed on a few devices.
Do I need endpoint security software?
If you need protection for a personal device or just a few devices under your care, endpoint security is not cost-effective. You’re better off with basic cyber tools that safeguard your devices against threats.
However, if you run a business with a significant number of employees, think a few dozen, then it becomes worth it to get endpoint security software. Businesses, not individuals, are the primary targets for data leaks and ransomware operations, so it is worth it to invest in a sophisticated endpoint security solution if you run a large one.
Which endpoint protection software is best for you?
Cybersecurity threats are increasingly becoming sophisticated, some say too sophisticated to be detected by traditional methods. Many endpoint solutions now employ artificial intelligence and machine learning to identify threat patterns and stop them before they can cause issues. It isn’t compulsory for your solution to incorporate these tools but it’s preferable.
It's worth considering the size of your business when choosing an endpoint protection solution, as some services will have a set amount of devices that can be managed, so you may end up paying for a solution that offers protection for far more devices than you currently manage. While this does provide some wriggle room for growing businesses, its worth considering if the cost is worth it.
Its also important to consider if you need extra levels of protection for your business, as well as learning the differences between types of protection. To get you started, we have an article explaining the differences between endpoint protection and a business VPN.
If customer service is a priority for you, this is also an important factor to consider. Some services will provide around the clock support 7 days a week to keep you protected and help out with any queries you may have, as well as providing technical assistance and troubleshooting. For a budding small business this could be a priority, as some services can be difficult to navigate, customize, and set up.
You can read more about the essential features endpoint protection should have here.
The competition
The above Endpoint Protection solutions represent a handful of the products out there. Sadly in a number of cases when we filled in a form on the company website requesting a trial, we either received no response or a representative refused our request.
A number of platforms offered to showcase a product demo or provide marketing material but we felt that TechRadar readers would prefer to read reviews of products we'd tried for ourselves, not to mention the results of our malware detection tests.
Although we're not going to name names here, we encourage all software vendors to cooperate with requests from independent reviewers to try out their products. IT Managers often make a point of visiting websites like TechRadar to read assessments of your platforms before signing up for a trial.
How we test
To test for the best endpoint protection software we first set up an account with the relevant platform, logged in to the cloud console and downloaded the agent software to our test machine, which contains a clean install of Windows 11. No third-party software is installed besides the platform we're reviewing.
Our aim is always to push each endpoint protection software platform to see how useful its basic tools were and also how easy it was to get to grips with any more advanced tools.
To this end, we make a point of leaving each platform's default settings as is, to see how well it responds to potential threats.
When reviewing the EPPs, our first test is always to download a fake computer virus, provided by EICAR. This file is actually harmless but it's signature exists in almost all antivirus databases for testing purposes.
The file is downloadable from the EICAR website in compressed (ZIP) format. We used the Microsoft Edge browser on our test machine to begin the download. If the EPP offers any web filtering features, we also check to see how the agent reacts to our attempts to visit the website.
Once the fake virus is downloaded, we then try to extract it to the test machine's 'Downloads' folder. A hallmark of an effective EPP is if it can recognize the threat before the file is decompressed and quarantine it. But at the very least we expect the file to be isolated and sanitized after it's extracted.
Our next test is to try to copy a new, real computer virus (usually a trojan virus) to the test machine's 'Downloads' folder. We do this to check that an EPP can detect a threat based on suspicious behavior, not just by comparing file signatures to a database of known malware. If the EPP agent doesn't immediately quarantine the file, we then try to run it to see if the platform will block it or if the machine will be infected.
Our final test is always to log into the EPP's cloud console to see which threats (if any) have been reported. Even if a file has been quarantined, we'd expect to see a report in the main dashboard, ideally providing more information about the threat.
Read more on how we test, rate, and review products on TechRadar.
Get in touch
- Want to find out about commercial or marketing opportunities? Click here
- Out of date info, errors, complaints or broken links? Give us a nudge
- Got a suggestion for a product or service provider? Message us directly
- You've reached the end of the page. Jump back up to the top ^
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!

Benedict has been with TechRadar Pro for over two years, and has specialized in writing about cybersecurity, threat intelligence, and B2B security solutions. His coverage explores the critical areas of national security, including state-sponsored threat actors, APT groups, critical infrastructure, and social engineering.
Benedict holds an MA (Distinction) in Security, Intelligence, and Diplomacy from the Centre for Security and Intelligence Studies at the University of Buckingham, providing him with a strong academic foundation for his reporting on geopolitics, threat intelligence, and cyber-warfare.
Prior to his postgraduate studies, Benedict earned a BA in Politics with Journalism, providing him with the skills to translate complex political and security issues into comprehensible copy.