Best password generator of 2025
Making password generation easy

Most of us can admit that password hygiene isn't as much of a priority as it should be, and the best password generators are here to help. Whether you're a password repeater, a Password123 user, or if you're just not as cautious as you could be, these tools are designed to generate secure and hard-to-crack password options.
Ideally, every password should be completely unique, and contain lots of both upper and lowercase letters, as well as special characters if the site allows. Remembering all of these complex combinations can be a challenge, so the best password managers can help keep them securely in one place.
But you don't need a subscription to a password manager to generate strong passwords, and we've listed plenty of online tools to help you.
To test all these password generators, we set up accounts with each provider, and, you guessed it, asked it to generate us a range of passwords to test their strength. Some offer extra features, so we tested those out as well, and of course, considered the price.
All that considered, below is our recommendation for the best password generators available.
We've also featured the best business password manager software.
Reader Offer: Save 52% on NordPass Premium
NordPass provides an accessible, competent, easy-to-use solution that most people will love, according to TechRadar editors. Save 52% on NordPass Premium plus 1 month extra with code TECHRADARPASS.
Preferred partner (What does this mean?)
The best password generators of 2026 in full:
Why you can trust TechRadar
Best password generator overall
Reasons to buy
Reasons to avoid
With the NordPass password generator, you can quickly create new passwords both online and within the NordPass password management app. It supports the generation of passwords up to 60 characters long.
You can also select between uppercase and lowercase letters, digits, symbols, or a combination of the four. On top of this, NordPass includes a checkbox that allows you to avoid ambiguous characters like 1 and I that could be confused.
The in-app generator is just as powerful and comes with the added benefit of being able to save your password immediately. In addition, the base version of the NordPass password manager is 100% free. For other versions, check out the NordPass promo codes currently available.
Read our full Nordpass review.
Best password generator for speed
Reasons to buy
Reasons to avoid
Dashlane is another powerful password management program offering a secure online and in-app password generator. It includes the standard password creation tools, allowing you to specify the length and character types for your new login.
You can create passwords from four to 40 characters long using the Dashlane generator. Specify whether you want it to include numbers, letters, symbols, or a combination of the three, and gauge the strength of your password through the interface’s background color—red for weak, orange for medium, and green for strong.
Those who need to manage and store numerous login details may also benefit from the Dashlane password manager.
Read our full Dashlane review.
Fin the best deals on Dashlane products with our Dashlane promo codes.
Reasons to buy
Reasons to avoid
KeePass is a free, open-source password management program with a built-in password generator. It is a little difficult to set up, but it’s extremely powerful and supports a selection of predefined password compositions.
You can create standard random passwords based on standard length and composition criteria. But, KeePass also enables the generation of passwords following specific rules. For example, if your password has to include upper and lowercase letters, numbers, and one special character, you can specify this with the click of a button.
Read our full KeePass review.
Best online password generator
4. Strong Password Generator
Reasons to buy
Reasons to avoid
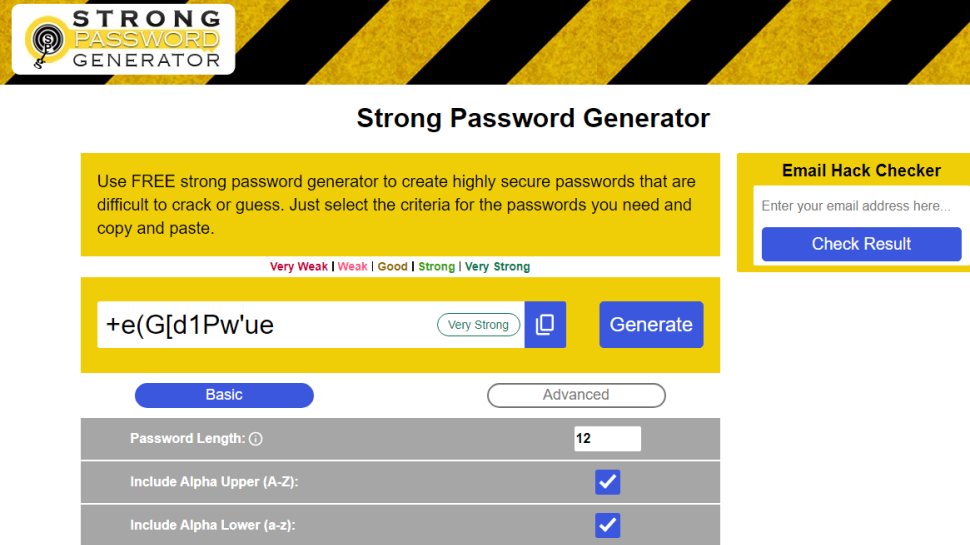
With the Strong Password Generator, the name says it all. This simple yet secure online program is designed to create unbreakable passwords at the click of a button. All new passwords are created locally on your computer, which means they aren’t ever stored online or on the program’s servers.
On top of this, the Strong Password Generator allows you to specify the length and composition of your new login. In theory, you can create passwords that are as long as you want. During our testing, we were able to easily generate a random string up to a million characters long in a matter of seconds—not that you would ever need one of this length.
In addition, you can specify what type of characters you want your password to include. Choices include alpha upper (A–Z), alpha lower (a–z), numbers (0-9), and symbols. Each new password comes with a unique QR code so you can transfer it to a phone or tablet as required.
Best free password generator
We've also featured the best password recovery solutions.
The best password generator FAQs
How to choose the best password generator
When you're looking for the best password generator to use, the first thought should be about what your needs are. If you just need just the basics for generating solid passwords to use in your internet life, then you probably won't get much use out of the higher end, more expensive platforms with advanced tools. If you require a more powerful software with added features, then consider which you'd find most useful before choosing.
Password Cracking vs Password Recovery. What's the Difference?
Denis Gladysh, co-owner and head of Passcovery, a supplier of high-speed GPU-accelerated software solutions for recovering passwords of popular file formats, gave us his insight into the differences between password cracking and password recovery:
To date when breaking secure passwords, one uses password guessing attacks. It is as if you were actually entering all trial passwords one by one until you find the one that fits to open the file. Only in this case a program does it for you at a rate of tens-hundreds-thousands-millions-billions of passwords per second. Such a guessing technique is referred to as brute-force attack.
How long you'll have to wait depends on two factors: the number of words to test and the speed of brute-force attack. The longer the charset that may include the right password is, the more trial passwords there will be. As the password length is increased, the number of trial passwords will grow exponentially, for example:
number_of_passwords = charset_length^password_length
So, in order to guess a password of only 1 lowercase Latin letter 26^1=26 trial passwords will be generated. For a 2-character password - 26^2=676. 3-character password – 26^3=17576, etc.
Cracking a 1-character password of uppercase and lowercase Latin letters will require testing of 26*2=52^1=52 passwords, and in order to crack a 3-character password 52^3=140608 passwords will be generated and tested, etc.
Our programs give perfect visualization of these calculations when you configure a brute force attack. As you change input parameters, the program estimates in real time the number of generated passwords and approximate time to completion. Now that we have covered passwords settings and the range of trial passwords, it is time to crack the password. How long will it take?
Bad news. It's going to take a while. A pretty long time actually. Remember I said that data security vendors use their own methods to deal with password hacking attacks? For example, they slow down the rate of password checking.
More often than not, the delay will go unnoticed (or it may leave a positive impression: "it is taking so much time - the security level must be really high!") when you enter one correct password, but it does slow down the speed of searching during a brute force attack.
When you enter a password, a special algorithm called hashing algorithm converts the password into an encryption key, and passes the key on to the data encryption algorithm. A little too simple. And too fast. Inadequately fast. (the guys behind protection algorithms in Adobe Acrobat 9 should know what it's all about :)
That is why the hashing algorithm does not immediately release the encryption key. First, it hashes the key itself. Then hashes it again. And again. And again. And it goes on and on ... hundreds, thousands and even tens of thousands times. This trick is called key stretching; it is an easy way to make brute force search more time consuming by requiring repeated hashing.
One moment delay when checking one password turns into years of waiting when checking billions of passwords. For example, with the release of iOS 10.2 by Apple has ruled out the possibility of cracking iOS backup passwords by using 10,000,000 (ten million!) hashing iterations. Hence, the rate of brute-force search has almost dropped to zero, and GPU acceleration has become useless.
In this context, it becomes next to impossible to crack a random someone else's password that is completely unknown to the attacker. Especially when there is no high-performance hardware. Although it should be noted that there is always room for foolishly easy passwords that might be found in a dictionary.
Recovering your own password is a different story. You sure have been in a situation when you promised to do something and clean forgot about it. Or some may have experienced amnesia which returned their brain to a sort of a tabula rasa state. When it comes to forgetting passwords it is never the case.
The password or its structure or the words of the passphrase will still be revolving in your head. The correct password will be looming somewhere within reach. It will be flickering in the dark and feebly hovering over among similar ones. Just like those glittering winged keys in the underground chambers of Hogwarts School. Just reach out and grab the right one!
And that is the essence of password recovery and how it’s different from hacking: you don't need to try all the keys in the world. Just cut off the irrelevant and thus reduce the range to only the likely ones. This way you can quickly check them all and find recover the password.
How we tested the best password generators
To test for the best password generators we first set up an account with the relevant software platform, then we tested the service to see how the software performed when accessed by different devices, as well as testing any additional tools that were provided. The aim was to push each password generators platform to see how useful its basic tools were and also how easy it was to get to grips with any more advanced tools.
Read more on how we test, rate, and review products on TechRadar.
Get in touch
- Want to find out about commercial or marketing opportunities? Click here
- Out of date info, errors, complaints or broken links? Give us a nudge
- Got a suggestion for a product or service provider? Message us directly
- You've reached the end of the page. Jump back up to the top ^
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!

Benedict is a Senior Security Writer at TechRadar Pro, where he has specialized in covering the intersection of geopolitics, cyber-warfare, and business security.
Benedict provides detailed analysis on state-sponsored threat actors, APT groups, and the protection of critical national infrastructure, with his reporting bridging the gap between technical threat intelligence and B2B security strategy.
Benedict holds an MA (Distinction) in Security, Intelligence, and Diplomacy from the University of Buckingham Centre for Security and Intelligence Studies (BUCSIS), with his specialization providing him with a robust academic framework for deconstructing complex international conflicts and intelligence operations, and the ability to translate intricate security data into actionable insights.

 Become a TechRadar Insider
Become a TechRadar Insider