Everything you need to know about the pros and cons of VPNs on Linux
Explore the pros and cons of VPNs on Linux

Sign up for breaking news, reviews, opinion, top tech deals, and more.
You are now subscribed
Your newsletter sign-up was successful
If you use your Linux machine to access the internet, whether it’s at home or particularly on the road, then it’s worth learning about the pros and cons of Virtual Private Networks or VPNs
We’ve looked at everything you need to know about VPNs before - but the upshot is this: paid-for and free VPNs allows you to secure traffic between two locations – the first being your own machine, the other being either a commercial VPN provider or a VPN system that you have deployed yourself, either in the cloud or perhaps at another location of your own, such as in the office.
Through VPN protocols, traffic is encrypted at the host end and decrypted at the server end, ensuring that information cannot be snooped on by a middleman on the way to its destination.
Article continues belowWhen using a VPN, there are a number of different options related to how data is routed. The typical scenario is to route all traffic over the VPN connection, but you can also use the concept of split tunneling, where some traffic passes over the VPN connection and some passes over the regular internet connection, based on routing rules.
The advantage of doing things this way is you can use one app to access certain services. For example viewing Netflix films in another country via your browser while leaving other applications unaffected. This is particularly important if you have work-related apps on your machine, as you may not have permission to use them with a VPN. Still, this is not as private as sending all your internet traffic via a VPN server, as anyone with access to your ISP’s records can monitor any apps not connected to your VPN.
- 5 of the most popular Raspberry Pi distros
- 10 of the best Linux distros for privacy fiends and security buffs
- 5 of the most popular Linux gaming distros
- 10 of the most popular lightweight Linux distros
Why go virtual?
VPNs are often touted as an essential tool for those worried about persecution for their online activities, but VPNs are useful to more than just dissidents living in dictatorships. They can offer peace of mind and stability for a number of lawful online activities.
So, let’s take a moment to more thoroughly explore the reasons why you might want to use a VPN. Although privacy and security concerns are the most common reasons for setting up private networks, they are not the only ones.
Whether you’re using a home broadband connection or roaming mobile data in a foreign country, there’s a good chance that you’ll be subject to traffic shaping. Traffic shaping is employed by service providers to limit the speed of certain types of traffic in order to prioritize content across their network.
For example, many of the UK’s service providers like T-Mobile use shaping to throttle down music and video streaming services when users are out of the country, in order to discourage customers from using large amounts of data. Similarly, some UK broadband providers will do the same with file downloads at peak hours.
Using VPN obfuscation technology can help avoid this happening, as it encrypts all traffic going across your internet connection, meaning that your provider won’t be able to see exactly what type of data you’re downloading.
One slight caveat with this is that some providers may detect and throttle VPN traffic itself, although given the wealth of different VPNs and protocols available, this can be avoided by using a less common service (typically, not OpenVPN).
Hotspot hazards
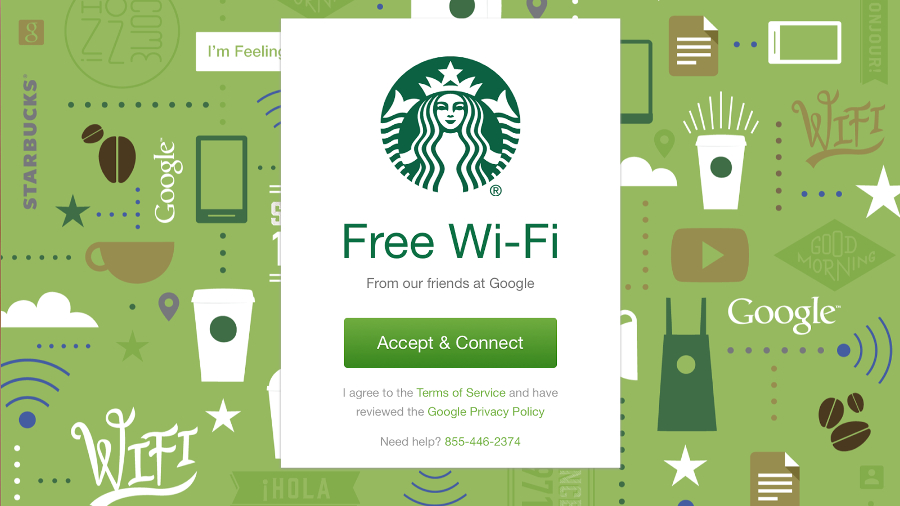
The classic use case of a VPN is with public Wi-Fi hotspots. If you are out and about with your Linux laptop (or your phone, or any other connected device), then you might want to take advantage of some free connectivity provided by your favorite library or coffee shop.
The problem with this is that you don’t really know what is happening to your data as it travels between your device and the service you want to use. It could be intercepted by other actors on the network or by a compromised Wi-Fi system in the cafe. If you are looking to send any data you care about, be it your social network posts or your online banking, you should really think twice.
Some users imagine that it’s safe to access certain websites on Public Wifi provided they use SSL or TLS. These are encryption protocols which can encrypt the connection between your device or a website. However, if you’re using public WIfi, you can’t be sure of the intentions of other people connected to the network.
In the first instance, whilst using public WIfi, your DNS requests (which are unencrypted) can be resolved through their server. This means you could be redirected to a scam ‘phishing’ website which will harvest your data.
Even if this doesn’t happen, as your DNS requests aren’t encrypted a bad actor connected to the same public Wifi network can discover which websites you’re accessing.
You may feel comfortable with others knowing which sites you access, provided they can’t actually access sensitive information like your password or credit card details. Using SSL/TLS websites is a great way to protect against this generally but if you choose to connect to an untrusted network, even this data could be put at risk through other hacking techniques such as SSL Stripping. This is where a rogue server sits between your device and a legitimate website as a “man in the middle” attack and tries to downgrade your connection from the secure https to regular http.
Some hackers will actually deliberately set up supposedly free Public Wi-Fi hotspots specifically to harvest naive people’s personal data.
Fortunately there’s a solution to all these problems. Using a reliable VPN will ensure that all traffic going over the public network is safely encrypted. You can stay extra safe by choosing a VPN service that routes all DNS requests through its servers too. This prevents what’s known as a DNS leak.
DIY VPN
The original purpose of VPNs was to provide external connectivity to office networks. Using this method means that opening machines up to the world completely can be avoided; instead, only a VPN server is configured. When users connect to the VPN, they will be able to browse as if they were actually in the office. Using split tunneling means that any internet access or local network access will still be possible, but addresses within the office IP range are routed over the VPN.
This concept can also be used in a similar way on your home network. By installing a VPN server at home (or using VPN functionality built into a number of popular routers), it is possible to connect when away from home and access machines on your home network as if you were actually there. This is particularly useful if you have content stored on a NAS drive, or perhaps want to remotely view business security cameras without opening them up completely to the world.
Many businesses now choose to deploy their infrastructure in the cloud, using providers such as Amazon Web Services. A common concept in cloud hosting is VPC, or Virtual Private Cloud. This allows companies to have a number of servers located in the cloud, but have them not generally accessible to the internet, instead allowing them only to communicate with each other. A good option is to deploy VPN access inside the VPC, so that again a minimal number of ports are exposed to the outside world, helping to enhance your overall security.
Location, location, location
One consideration when using VPNs is their location. If you are based in the UK, but connect to a VPN in another country – the US for example – then this will impact activities such as web browsing, as the destination server will see only your ‘exit IP’, that is the IP address of the server from where you are ultimately routing traffic.
This can be a negative thing – if you are using Google and everything comes up in another language, or content is geo-blocked – or a positive thing, if you’re using a Netflix VPN in order to access content that is similarly restricted (Netflix and BBC iPlayer are great examples).
When choosing a VPN Provider, you should also consider where they’re registered and the location of their servers. Some countries like the UK require ISPs to keep records of all connections. Others can require VPN providers to turn over data through a court order or by seizing the servers.
Consider choosing a reliable provider who is based in a jurisdiction where this is unlikely to happen. For instance, NordVPN is based in Panama and allows you to choose from almost 6,000 servers across 59 countries. NordVPN also claim that their servers run entirely in virtual ‘RAM’ memory so if they were seized it would be almost impossible to recover any useful information.

VPN versus VPS
So, that’s the basics of VPN covered, but you may have also heard of a VPS, and wondered what on earth that is. A VPS is a ‘virtual private server’ – a virtual server box in the cloud. Let’s explore the main points of difference between the two.
What’s a VPN?
- It’s typically provided by specialist VPN companies
- Also possible for tech-savvy people to deploy
- Varies widely in price, but start from free
- Typically, you get what you pay for
- If the encryption key is shared amongst users, data could still potentially be compromised
- Often available with ‘POPs’ (points of presence) in a range of countries across the world
- Speeds will often vary based on user location
What’s a VPS?
- Provides a set amount of CPU, RAM, storage and traffic for a monthly fee
- Is generally deployed with a basic OS build the user can then customise
- More commonly available with Linux than any other platform
- Ideal for deploying your own VPN solution
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!