Sinbad crypto mixer used by North Korean Lazarus Group seized by US government
Cryptomixer seized in international effort to sanction Lazarus Group.
The Sinbad cryptocurrency mixing service has been sanctioned by the US government in an effort to restrict the money laundering abilities of the North Korean Lazarus group.
The Lazarus group, a cybercriminal enterprise sponsored by the North Korean regime, is responsible for a number of malicious cyber attacks, including the 2017 WannaCry ransomware attack, and the 2022 Horizon Bridge attack that saw $100 million stolen.
Cryptocurrency mixers are used for money laundering by cyber criminals, and allow people to ‘mix’ their deposited cryptocurrency between a number of virtual wallets in order to obscure its source.
Lazarus funds DPRK weapons of mass destruction
According to a press statement released by the US Department of the Treasury, “Due to the pressure of robust U.S. and United Nations sanctions, the DPRK has resorted to using illicit tactics, such as heists perpetrated by the Lazarus Group, to generate revenue for its unlawful weapons of mass destruction and ballistic missile programs.”
Crypto mixing sites like Sinbad generate revenue by taking commission on deposited cryptocurrencies, and are “used by cybercriminals to obfuscate transactions linked to malign activities such as sanctions evasion, drug trafficking, the purchase of child sexual abuse materials, and additional illicit sales on darknet marketplaces."
According to the US Treasury Department, funds seized by Lazarus in a number of recent high-profile attacks were ‘mixed’ using the Sinbad service. This is not the first crypto mixing site to be targeted by similar sanctions, with the Blender.io site previously used by the Lazarus group being similarly seized by the US treasury in 2022.
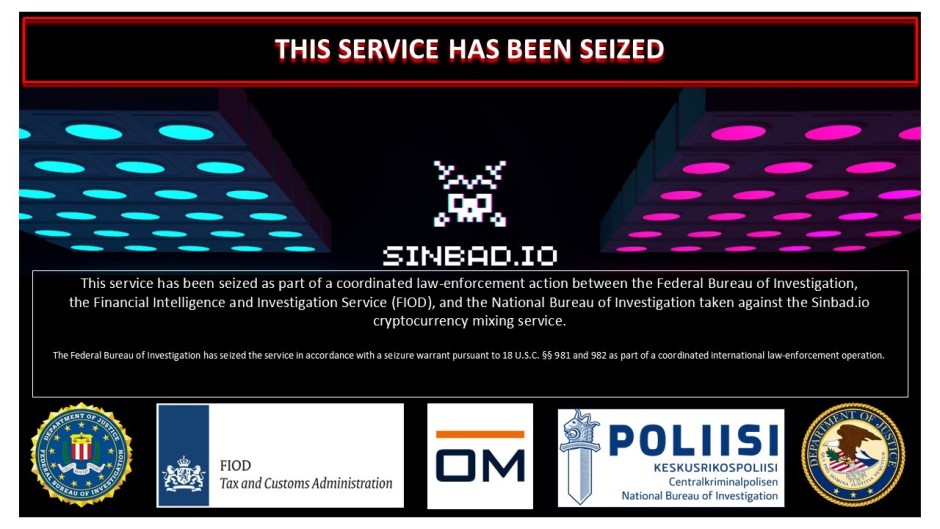
The Sinbad site now displays a message that states, “"This service has been seized as part of a coordinated law-enforcement action between the Federal Bureau of Investigation, the Financial Intelligence and Investigation Service (FIOD), and the National Bureau of Investigation taken against the Sinbad.io cryptocurrency mixing service."
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
Via BleepingComputer
More from TechRadar Pro
- IBM is teaming up with NASA to combat climate change with geospatial AI
- Best online cybersecurity courses: Free and paid certification programs, degrees and masters
- Malicious links are dominating emails all over the world

Benedict is a Senior Security Writer at TechRadar Pro, where he has specialized in covering the intersection of geopolitics, cyber-warfare, and business security.
Benedict provides detailed analysis on state-sponsored threat actors, APT groups, and the protection of critical national infrastructure, with his reporting bridging the gap between technical threat intelligence and B2B security strategy.
Benedict holds an MA (Distinction) in Security, Intelligence, and Diplomacy from the University of Buckingham Centre for Security and Intelligence Studies (BUCSIS), with his specialization providing him with a robust academic framework for deconstructing complex international conflicts and intelligence operations, and the ability to translate intricate security data into actionable insights.

 Become a TechRadar Insider
Become a TechRadar Insider







